Brian Krebs: a database of megapatch accounts containing hundreds of millions of records, 2-3 years

Today, a new post has appeared in the blog of Brian Krebs, a journalist and specialist in network security . In it, he talks about receiving hundreds of messages describing the “mega-leaky” that happened a couple of days ago . According to him, this is a truly large-scale event, but the accounts merged into the network are not new at all - the base is about three years old.
As for the dump called “Collection # 1”, the size of which is about 87 GB, it was analyzed in detail by Troy Hunt, the developer of the HaveIBeenPwned service. He believes that the dump was obtained by merging many smaller databases of accounts, perhaps there were thousands.
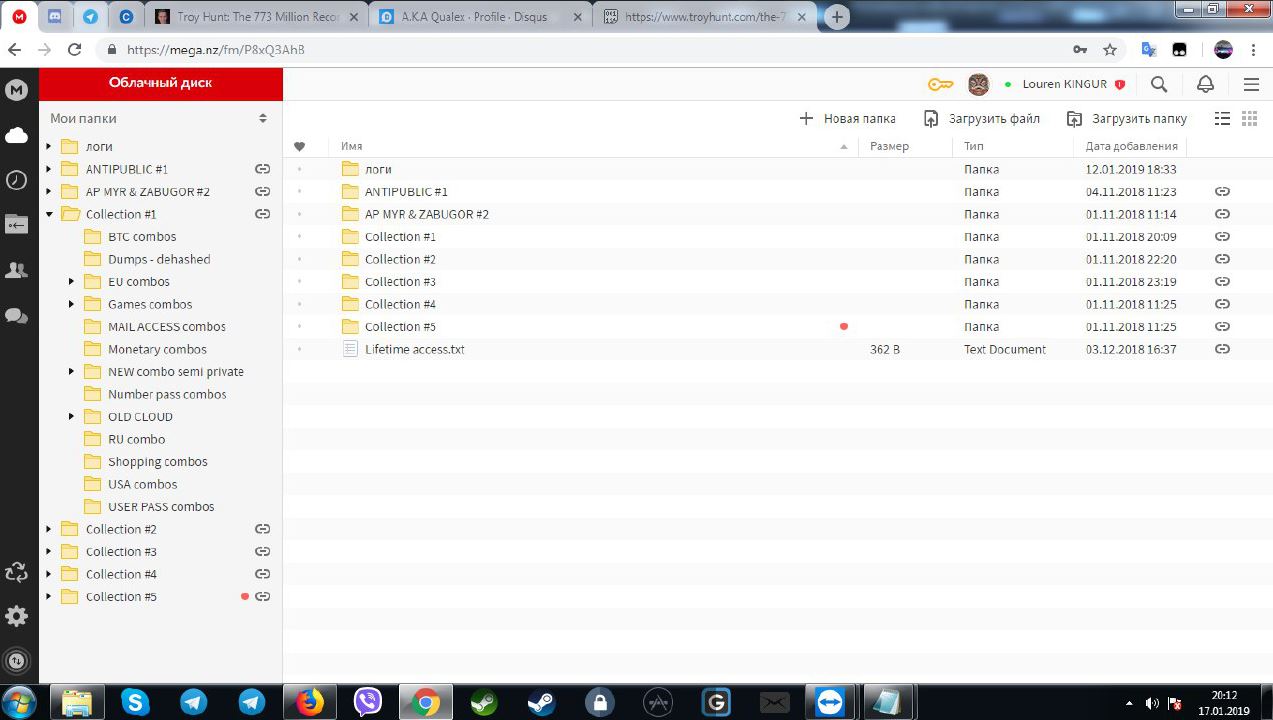
Previously, data that is part of the “mega-leakage” was published in various specialized closed forums. However, according to Alex Holden, a representative of the company Hold Security, the first publications appeared not three years ago, but in October 2018. Accounts can be even more, they are all sold on private resources. Below is a dump of almost 1 TB, containing a huge number of accounts.

The seller of all this information has a Telegram account, his nickname is Sanixer. Judging by the screenshot, Collection # 1 is exactly the dump that is now being discussed online. And it was sold for only $ 45.
The dump includes a huge number of accounts received as a result of hacking various resources. This is not a fresh offer. Most likely, the accounts included in the dump were stolen 2-3 years ago. But the other offers of the seller (not all of them are shown in the screenshot) are much more recent, they are less than a year old. The total amount of all data sold by Sanixer reaches 4 TB.
This "black entrepreneur" demonstrated the data stored on his personal account of the Mega service. The demonstrated base is impressive. By the way, the seller is clearly Russian-speaking (the Russian language is visible in the screenshot).
According to some information security experts, data that has been merged into the network can be used in phishing, spam, and other indirect attacks. Many accounts are already inactive, passwords are changed. But email can be used without any problems.
“Merged data was very popular among Russian hackers on the Darqube forums a few years ago. Since the data is obtained from many sources, mainly, these are old accounts, there is no direct threat to the web community. But the volume of the dump is, of course, impressive. ”
The main reason for the fact that such a large number of accounts is being led away by the attackers is due to the unpreparedness of network users. Most, despite the recommendations of experts, still uses simple passwords and logins. Few people establish two-factor identification or work with password managers. In addition, many users work with the same bunch of username / password on a large number of resources. And this is just dangerous, because the base can be used to select passwords for different accounts on resources that have not yet been affected by hacks.

The scheme of use of stolen data by hackers
It is worth noting that the cost of stolen data is constantly falling. The price of the account from the dump (for example, Collection # 1) is approximately 0.000002 cents.
Cybersecurity experts recommend using long phrases as a password, which the user can easily remember. This requires, of course, support for long passwords with resources. This is not always the case. In most cases, a long phrase is much more difficult to crack than a regular password, albeit a complicated one (of course, everything is relative here).
It is best to work with password managers that can generate both passwords (and very complex ones) and phrases. The main thing in this case is to remember the master password to the manager, otherwise you can lose all your data once and for all.
Plus, it helps and two-factor authentication. True, there may also be problems here, since not all resources use this opportunity in a proper way. Nevertheless, it is much better than the constant use of the same login / password bundle on a large number of different resources, especially if these resources contain vital user information (banks, public services, etc.).
