Keep SSH keys safe
- Transfer

I want to tell you how to safely store SSH keys on the local machine, without fear that some application might steal or decrypt them.
The article will be useful to those who have not found an elegant solution after paranoia in 2018 and continue to keep the keys in $HOME/.ssh.
To solve this problem, I suggest using KeePassXC , which is one of the best password managers, it uses strong encryption algorithms, and also has a built-in SSH agent.
This makes it possible to safely store all keys directly in the password database and automatically add them to the system when it is opened. Once the database is closed, the use of SSH keys will also become impossible.
First of all, add the autostart of the SSH agent when you log in, to do this, open ~/.bashrcin your favorite editor and add to the very end:
SSH_ENV="$HOME/.ssh/environment"
function start_agent {
echo "Initialising new SSH agent..."
/usr/bin/ssh-agent | sed 's/^echo/#echo/' > "${SSH_ENV}"
echo succeeded
chmod 600 "${SSH_ENV}"
. "${SSH_ENV}" > /dev/null
}
# Source SSH settings, if applicable
if [ -f "${SSH_ENV}" ]; then
. "${SSH_ENV}" > /dev/null
#ps ${SSH_AGENT_PID} doesn't work under cywgin
ps -ef | grep ${SSH_AGENT_PID} | grep ssh-agent$ > /dev/null || {
start_agent;
}
else
start_agent;
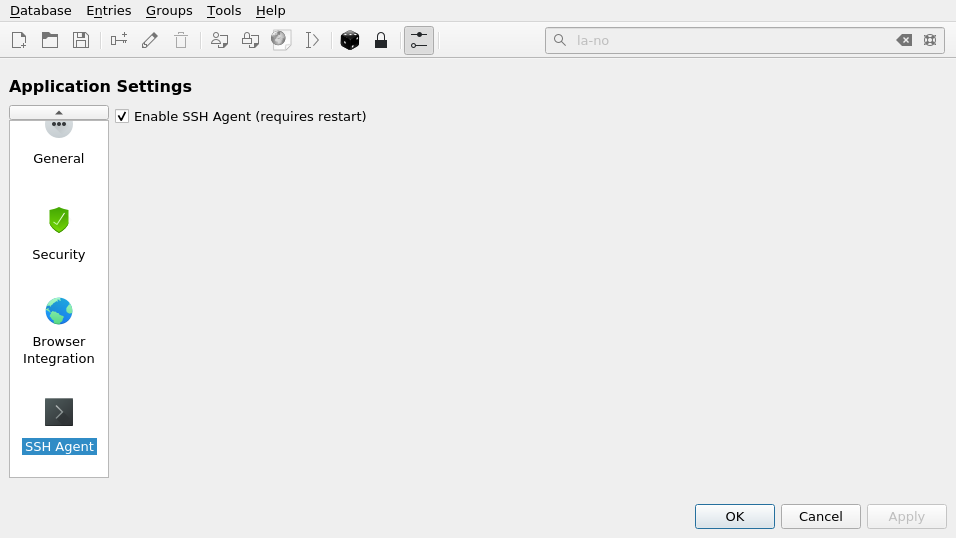
fiThen we need to enable support in KeePassXC:
Tools -> Options -> SSH Agent -> Enable SSH Agent
This completes the setup, now try adding a new SSH key to KeePassXC:
Click on the icon with the key, then fill in the data:

If the key is password protected, provide the same password
On the Advanced tab, load the attachment with our id_rsa :

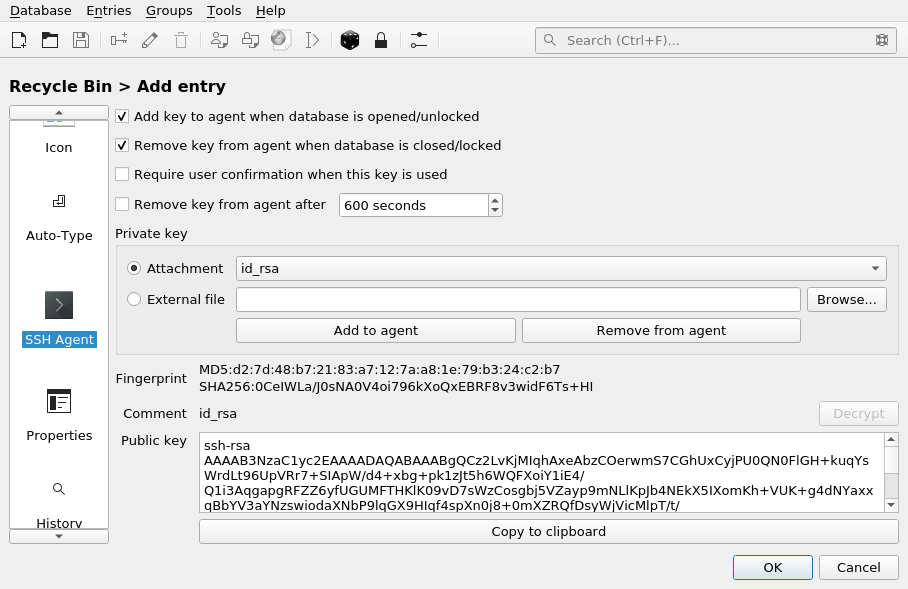
On the SSH agent tab , note:
- Add a key to the agent when opening / unlocking the database
- Remove a key from an agent when closing / locking a database
Next, select our key ( id_rsa ) in the attachment
And click the Add to Agent button :
Now when you start KeePassXC, the key will be automatically added to the SSH agent, so you can no longer store it on disk!
