DEFCON 18. "How I met your girlfriend, or a new type of Internet attack." Samy Camcar
- Transfer
I will tell you about the development and implementation of a completely new type of hacker attacks that will help me meet your girlfriend. But first, a little about yourself.
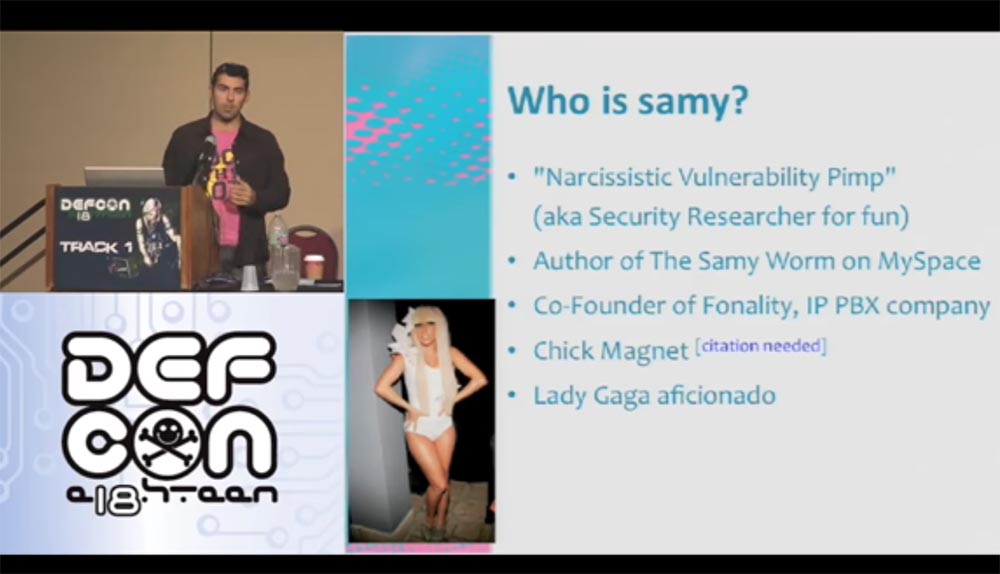
My name is Samy Kamkar, I am investigating security issues, but not professionally, but for my own pleasure, like most of those present here. I am known as the “Narcissistic Vulnerability Pimp,” or “narcissist of narcissistic vulnerabilities,” I am the author of the Samy Worm virus, created on MySpace several years ago, and one of the founders of IP PBX Fonality. I am also called Chick Magnet, a “chick magnet,” and I'm a fan of Lady Gaga. And I also love cash.
On this slide, you see guys who have done me a great service - they allowed me not to touch the computer at all for a while. A few years ago, representatives of the USSS, United States Secret Service Electronic Crimes Task Forces, the US Secret Service cybercrime investigation team, burst into my house. They seized all my computers, took my laptop, mobile phone, CD and DVD players, and even the Xbox game console. The case ended in a court that forbade me to touch computers for life, but a couple of years ago I was "unban", and now I'm with you again, but without access to MySpace.
I’ll tell you why I want to talk about the Internet today. The Internet is new, it's cool, you can use it! But a few years ago I was bored. Because the Internet is good, but security is much wider. It covers all areas of web technology, and DEFCON is at the forefront of Internet security. This includes hardware engineering, network security, web application security, hacking hardware, and other funny things. Some guys even learned to pump cash from ATMs, but you probably don’t know about it. But the Internet is cool not only because of this. There is another reason.

If you have a computer, then you have an operating system that necessarily has a web browser. It is part of the software that allows me to deliver you some code that you use. This is such a delivery mechanism, thanks to which I can attack any of those present on the Internet. This is similar to the way apps from the App Store get to your iPhone, and you can get any content you want. Of course, Apple protects its content and protects you from annoying porn. Browsers act in exactly the same way, but no one protects them. No one cares that the sites you are viewing can be malicious.
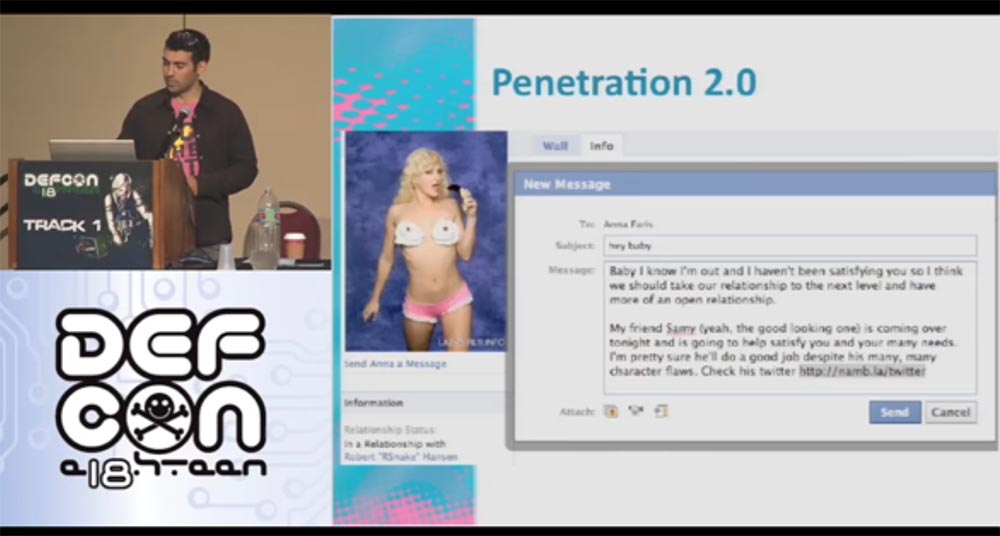
Now I will show you my page on Facebook. She is very popular because many people like Anna Faris, she is amazing.
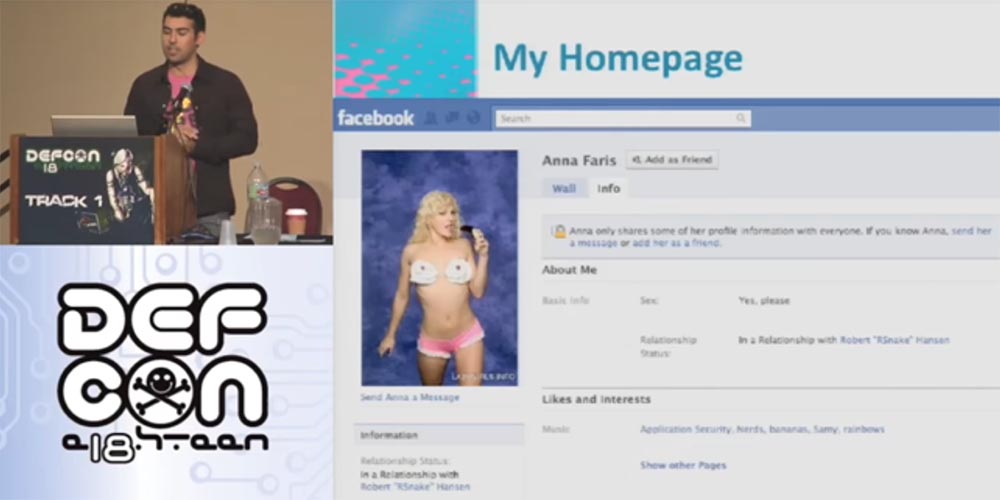
I usually post such a picture before creating a bunch of troubles. One guy wants to meet Anna. He studies her profile, looks at her photos, but cannot see everything, because he is not a friend of her. And then he had the idea to write to her through a messenger to establish a relationship. So who is this guy and how can I help him?
And then I find out a lot of interesting things!
The guy who will be the target of the attack is:
From the applause in the hall, I realized that you like my idea.
This is a very impressive resume. Now I will show you its author - this is Robert "RSnake" Hansen, Robert "Snake" Hansen. The problem is that I am going to attack this guy.
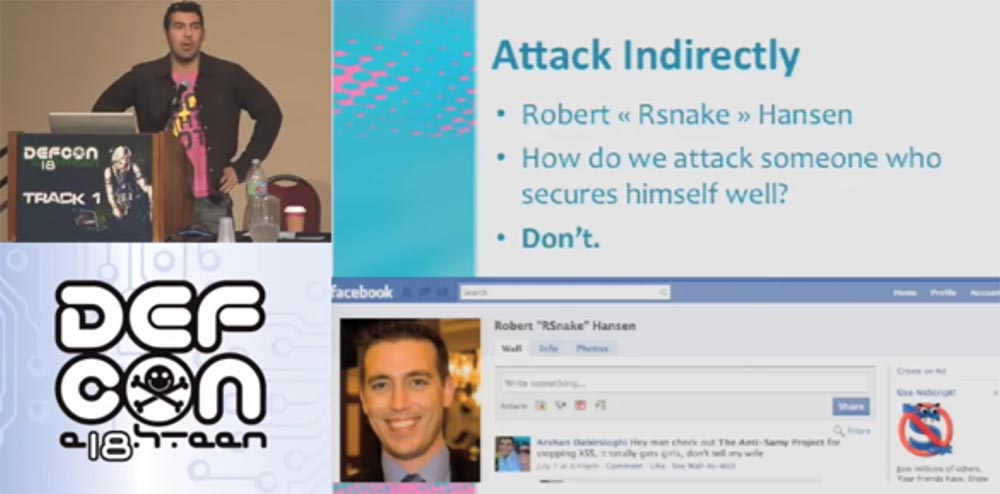
We can easily attack random people by sending them malware or forcing them to follow phishing links, but now I'm going to attack a specific person who understands security and uses many technologies to provide our own protection.
So how do I attack this person? Right - no way. I cannot do this, so I will act differently.
Our guy is registered on Facebook. Facebook is an amazing social network that has the properties inherent in all Internet resources. When authorizing on the main page at the end of the address bar, we see the symbols index.php. You probably think this is FIP, but no, it is just PHP, a general-purpose scripting language used to develop web applications. Surely many of you have heard about it or even programmed in this language. Its code is open source, so you can change the encoding and observe what it leads to. This is a great tool for managing Internet sessions that everyone can use for their needs. Everyone who uses PHP and sessions uses a session management system. They use software platforms, frameworks such as cakePHP, Kohana or Codelgniter.
A PHP session is a random string that is generated in URLs or cookies. Cookies are pieces of text that remain in your browser and contain session data.
When you go to any page of the site, the browser checks to see if its cookies are stored on the computer. When you go to Facebook and enter your username and password, a random line is generated from them. When you go to another Facebook page, she checks this line and says: “Oh, I know this guy, this is Samy!” That is, it performs your authentication and provides access.
Consider what PHP session code is.
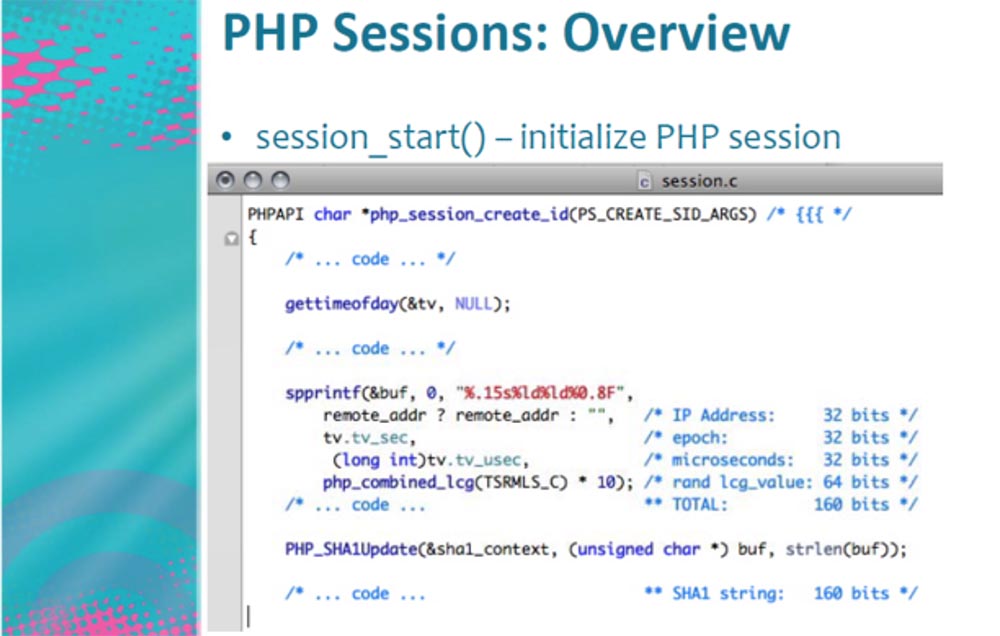
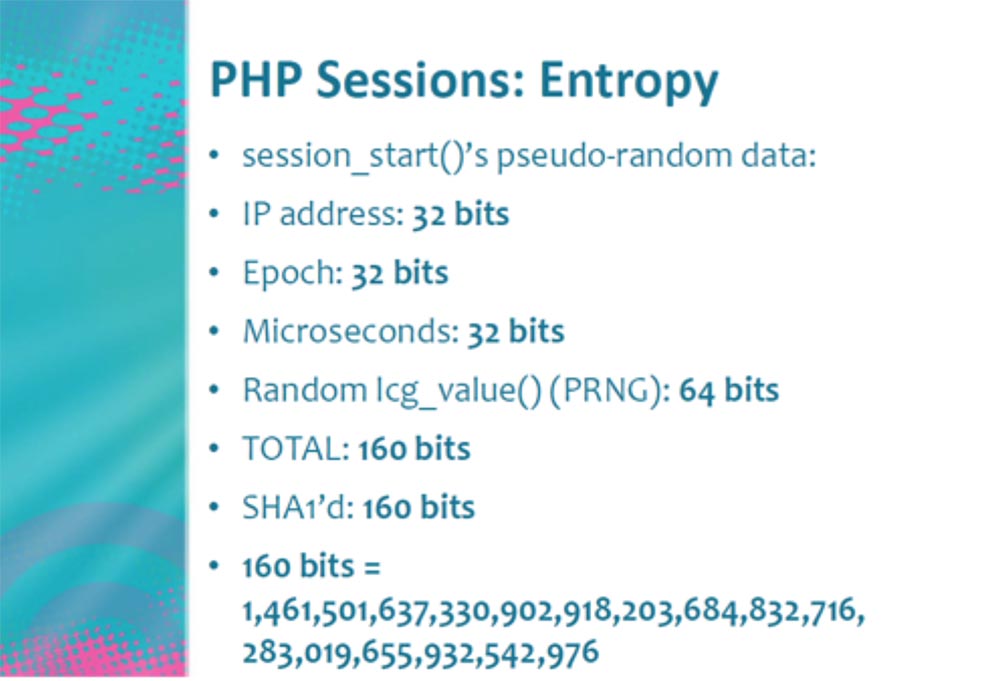
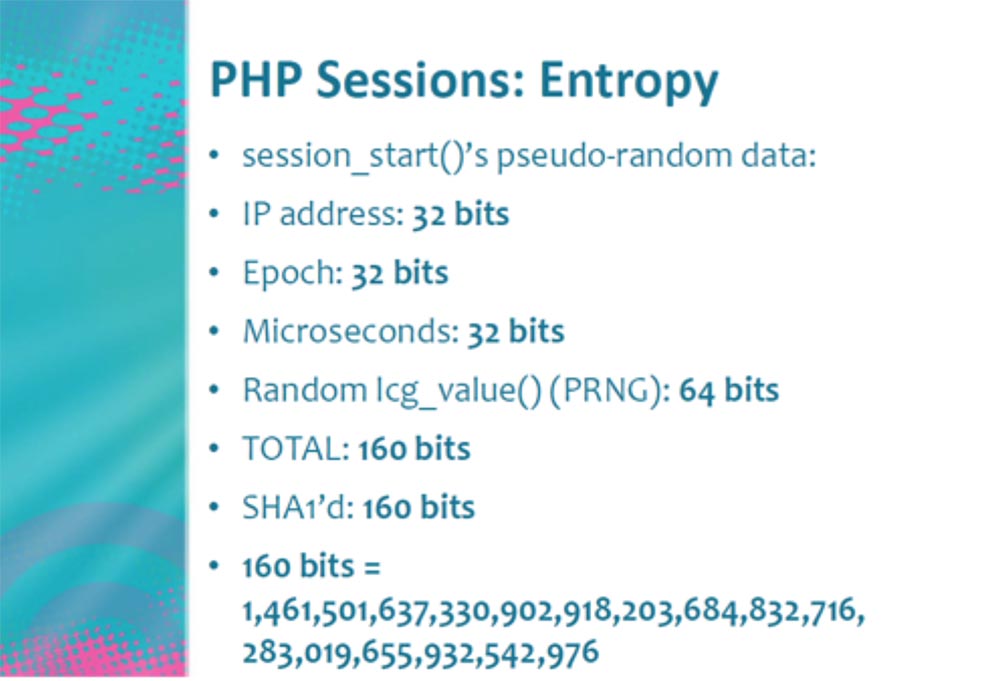
This is the part that starts and creates the session. It consists of several lines that contain the IP address of the authorized user, era, that is, the time elapsed since January 1, 1970, the number of microseconds required to create cookies, and all this looks like random numbers that are created in the range of 160 bits . 160 bits is a very large range for hacking, that is, an attack with password guessing using Brute Force technology.
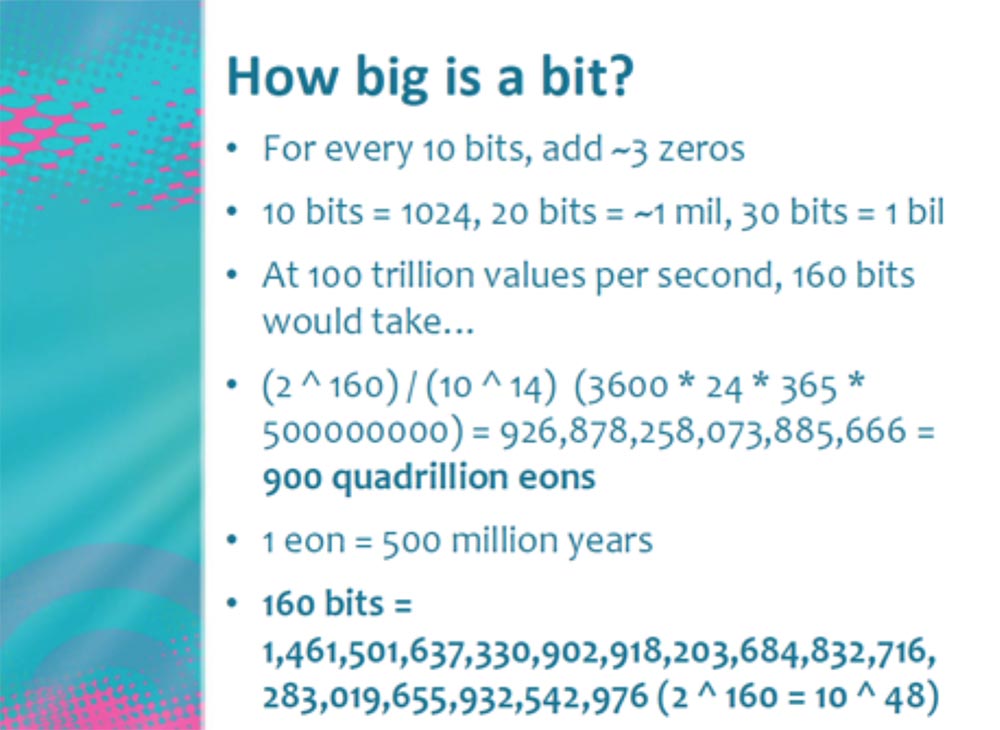
Consider how big each bit is. Each time you add a new bit, you double their total number. Therefore, 160 bits represent a gigantic number.
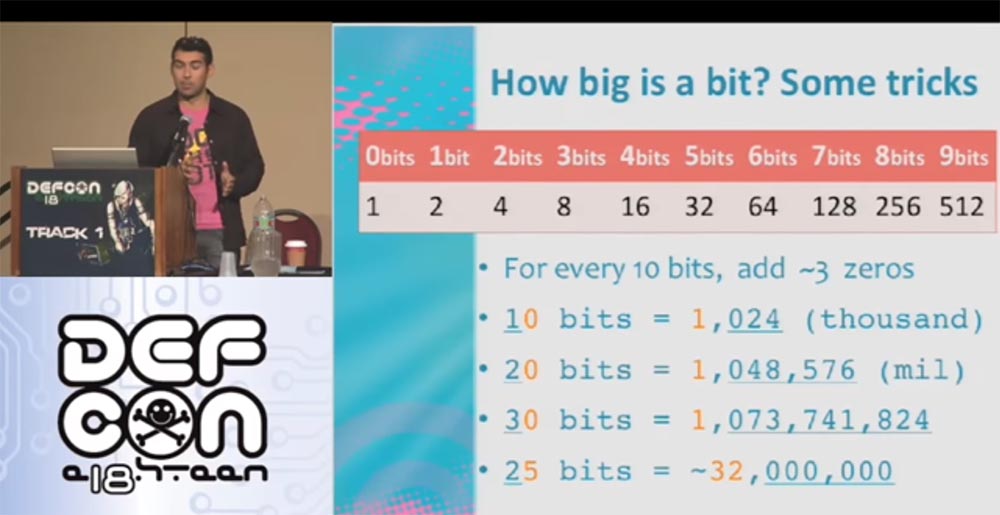
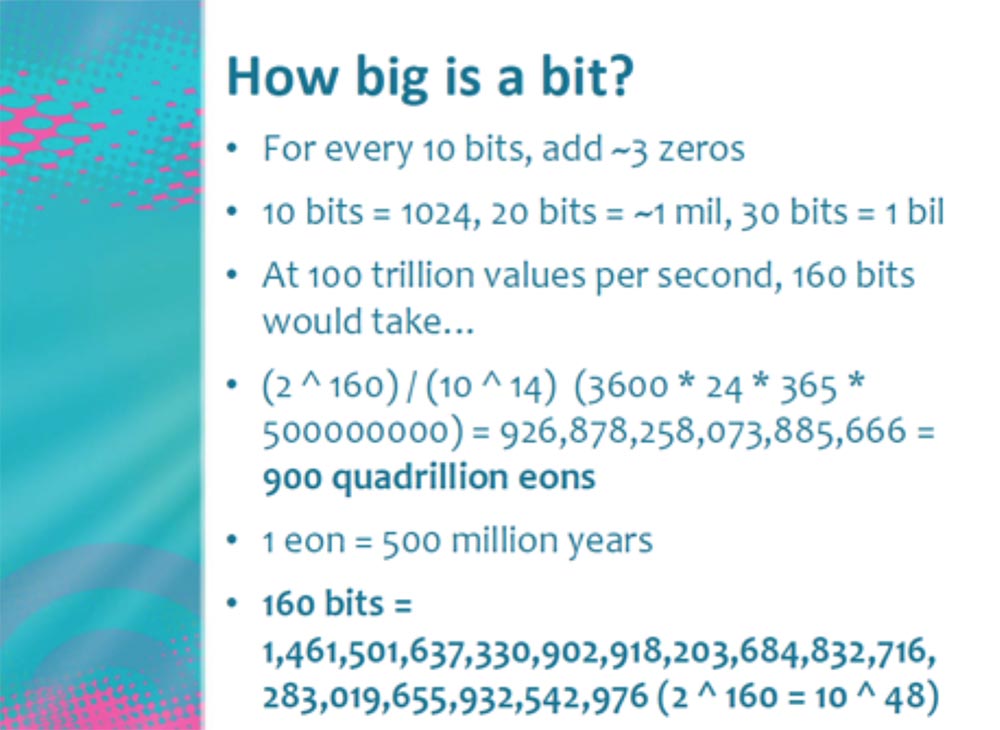
Each time, adding zero, we perform a trick with the bits - for every 10 bits three zeros are added, that is, 10 bits = 1000, 20 bits = 1,000,000, 30 bits = 1,000,000,000 and so on. Thus, if we use Brute Force with an intensity of one hundred trillion operations per second, 160 bits will be equivalent to 900 quadrillion Eon, where 1 Eon corresponds to 500 million years.
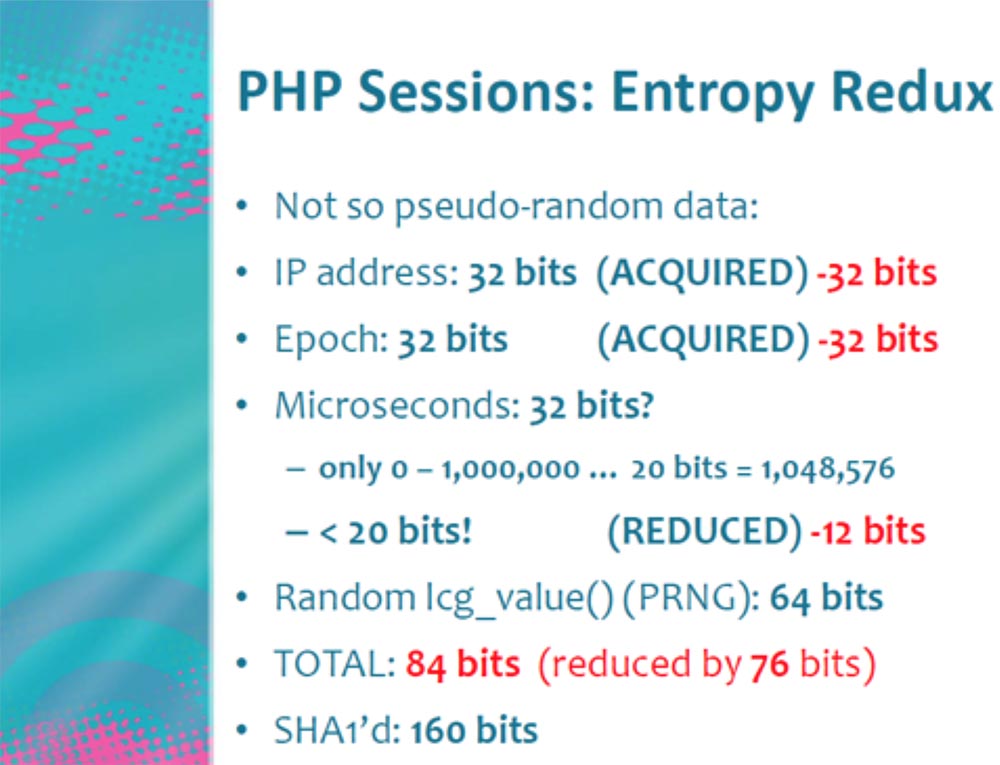
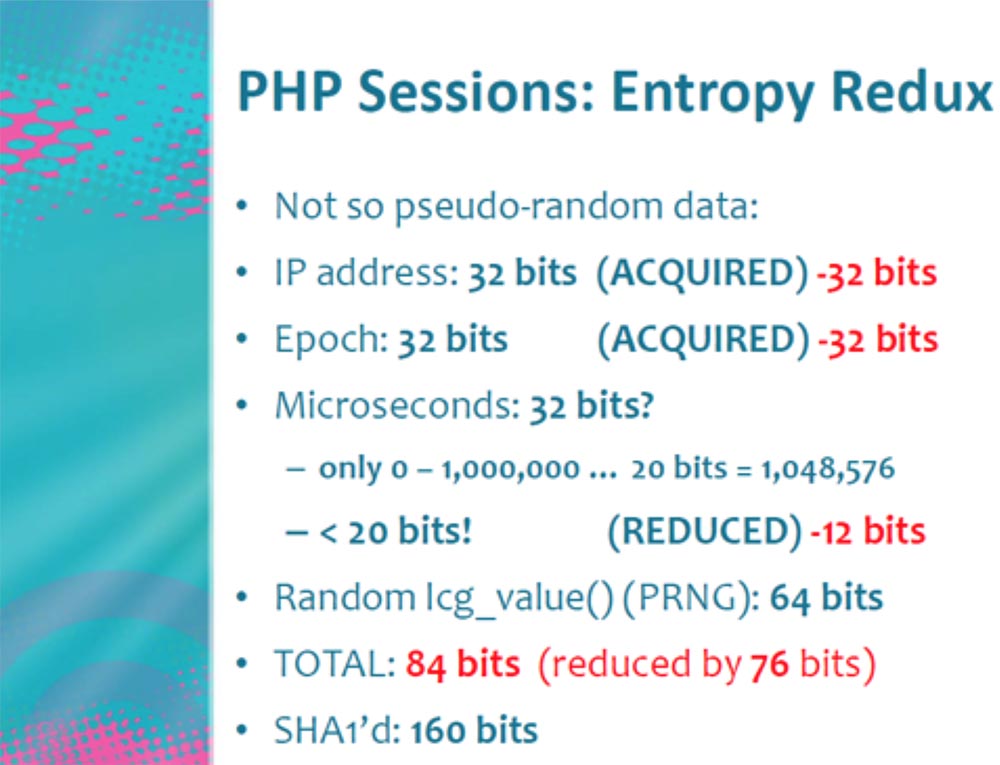
So we have 160 bits. How can I hack them? It doesn’t matter which computer you have. Consider the detailed how many bits each of these parameters really needs, that is, the process of returning the entropy of a PHP session, and what microseconds are.
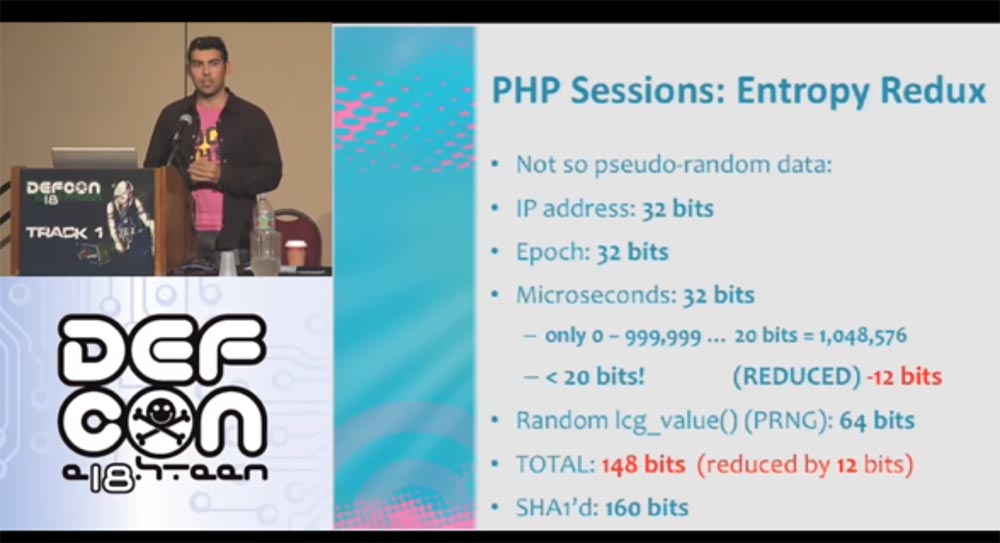
One second consists of a million microseconds. If you remember, a million is only 20 bits, and we have 32 bits. Thus, we have not done anything yet, but already saved as much as 12 bits. That is, in fact, we have 148 bits plus 12 extra.
Consider in detail the entrance to Facebook. When you go to the page, they check you out. The status is constantly updated, that is, Facebook captures when you log in to your account or log out. If you use live HTTP or a packet analyzer, you see how the HTTP request is returned, and you can recreate it. You can send requests every second and receive a server response.
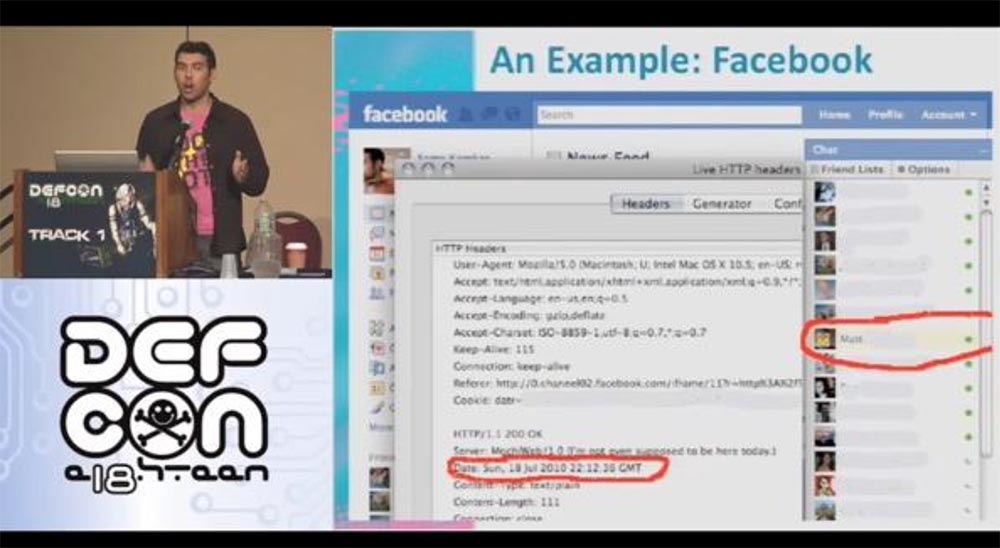
On this slide, the data returned by the server is circled in red. This is his local time. It does not particularly help us, because we do not know how exactly our time differs from the local server time. But this local time creates its own cookies. These are 32 bits, which we can also save by sending requests to the server every second, that is, free up the Epoch field. We developed a program that goes online every second, converts the Data parameter to Epoch and frees 32 bits. Thus, our savings are 12 + 32 = 44 bits out of 160. This is just wonderful - we got into our hands as many as 44 bits.
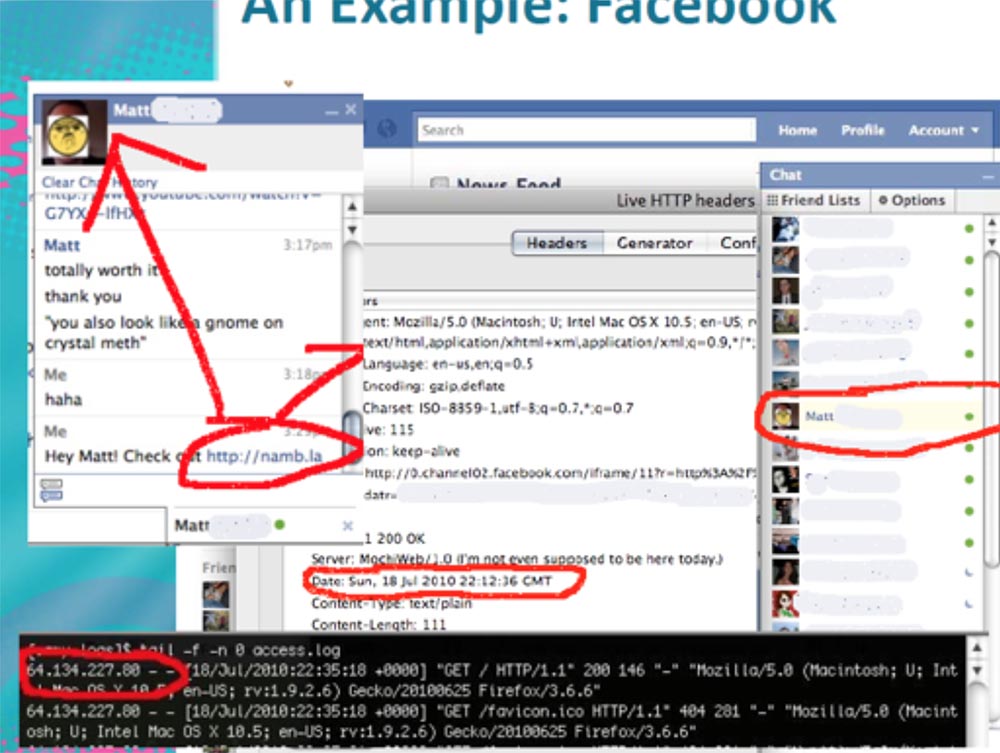
Let's continue further. If we send some information to our address in a chat, for example, my blog, then we can track its IP address. It appears in the Apache log, as shown in the next slide in a red frame.
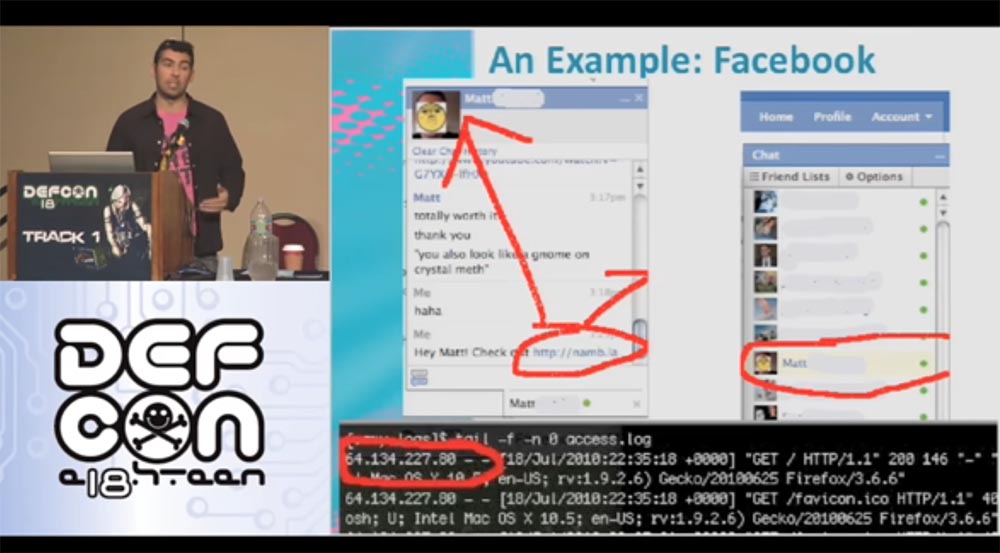
These are 32 more bits of our cookies. Thus, we get already 12 + 32 + 32 = 76 bits of saving out of 160 bits, that is, another 84 bits of cookies remain busy.
What else remains with us? Parameter Random Lcg_value of 64 bits. LCG is a linear congruent pseudo random number generator that is commonly used in cryptography. It was developed about 25 years ago, that's all I know about it. In fact, this LCG uses two generators connected to each other. I do not want to delve into the mathematical subtleties, just consider the code that is generated by this generator. It is a SEED - block cryptographic algorithm that creates a series of random numbers.
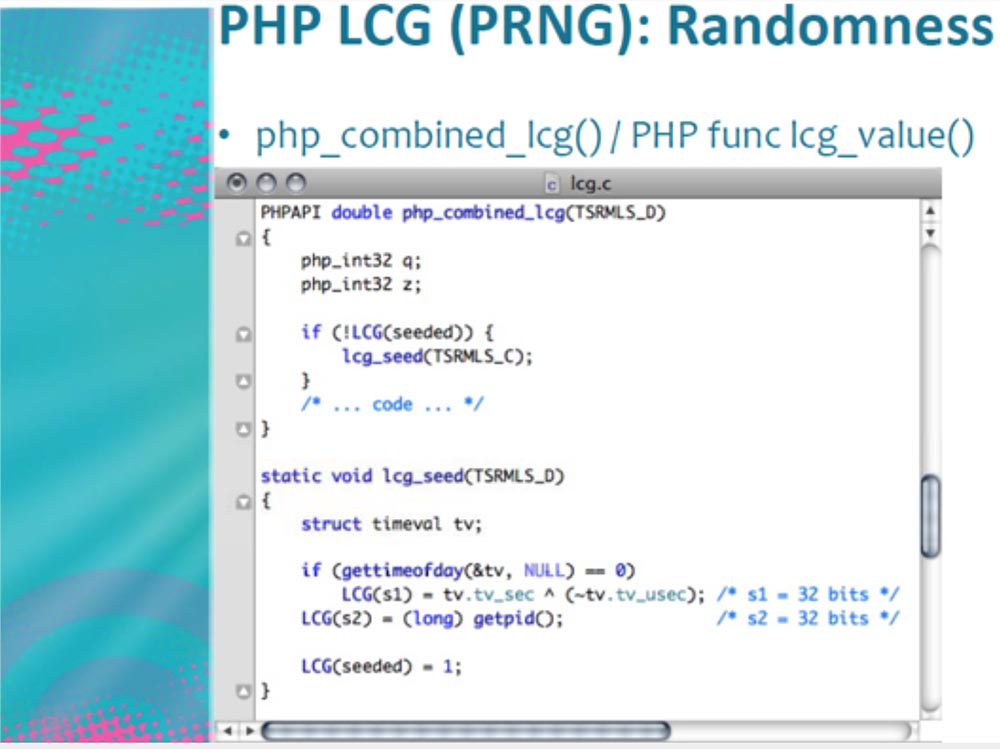
At the bottom of the screen, we see an LCG consisting of two variables s1 and s2 each 32 bits in size, that is, each SEED consists of 64 bits of entropy. Parameter s1 = tv.tv_sec describes Epoch, that is, the number of microseconds, and parameter s2 represents the process ID.
Let's consider s1 in more detail.
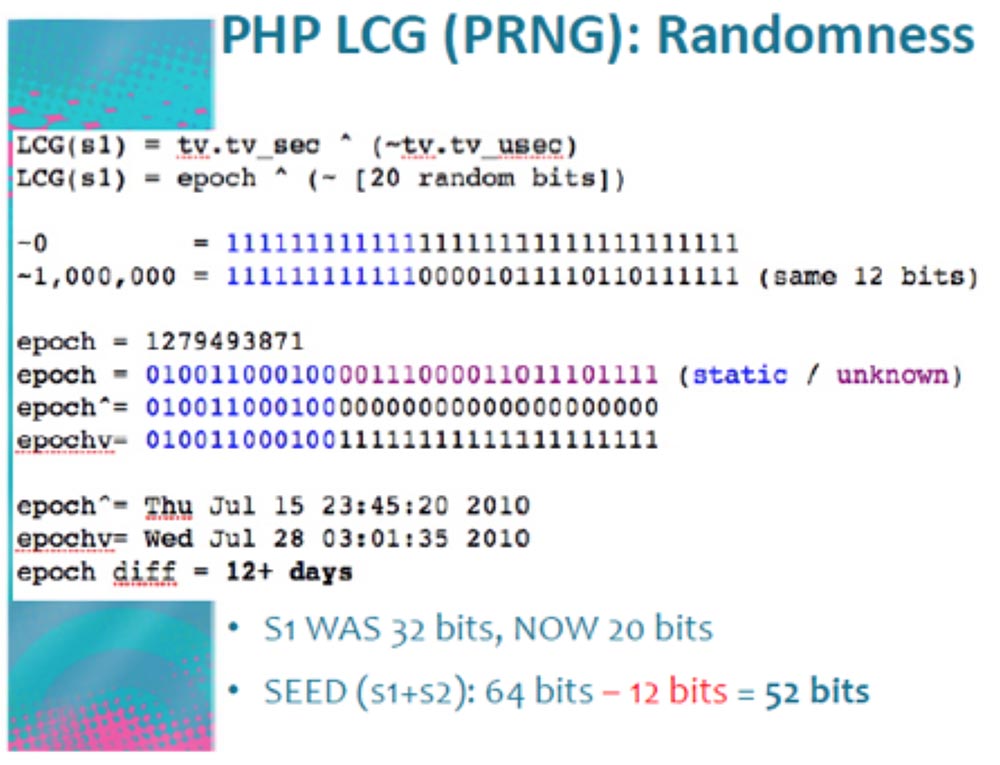
The generated PHP parameter LCG (s1) describes the Epoch in random bits, and it has a size of about 20 bits. We can send thousands and thousands of requests per second to the server, forcing it to overload the information sent back that relates to time. The difference in the readings of time is 12 hours + a day, we do not know what it really is, but for our process this is not important. As a result of the work of the program generating the requests, we use only 20 bits out of 32, that is, we save another 12 bits. Thus, the size of parameter s1 changes from 32 to 20 bits, and the total size of SEED (s1 + s2) from 64 bits turns into 52 bits.
Consider what an ID process is, designated as LCG (s2). We know that s2 = 32 bits. But Linux, which runs the Apache server, uses only 15 bits to create the PID, which means that 32 - 15 = 17 bits can really be freed from s2.
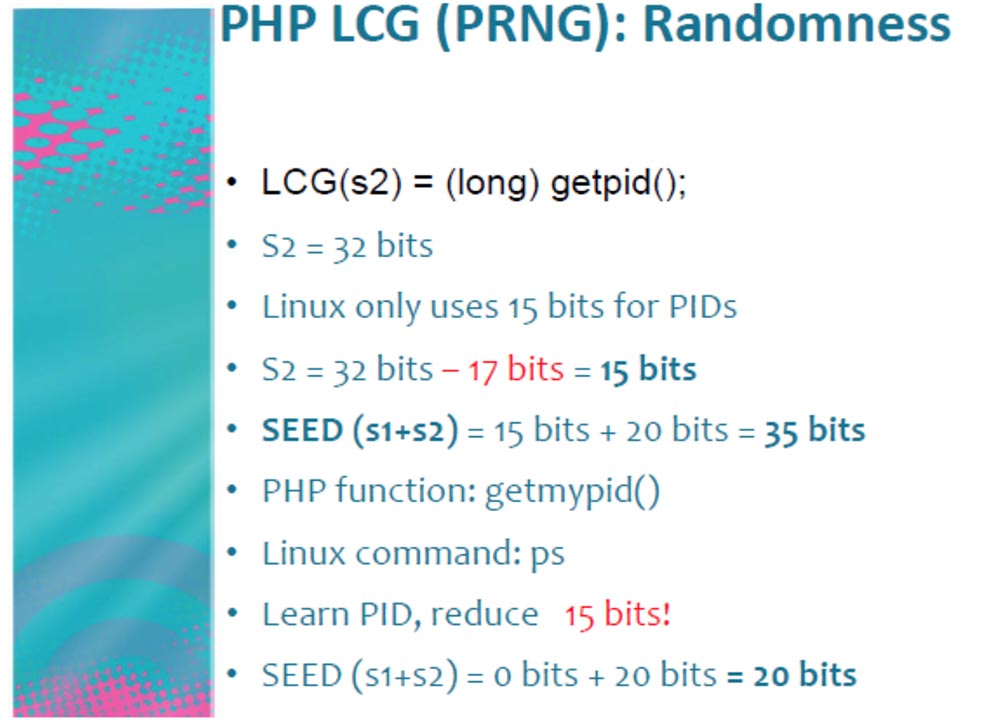
As a result, we get the size of SEED (s1 + s2) = 15 bits + 20 bits = 35 bits. The getmypid PHP function corresponds to the Linux command: ps, so knowing the PID, that is, executing it with our program, releases another 15 bits, total SEED (s1 + s2) = 0 bits + 20 bits = 20 bits.
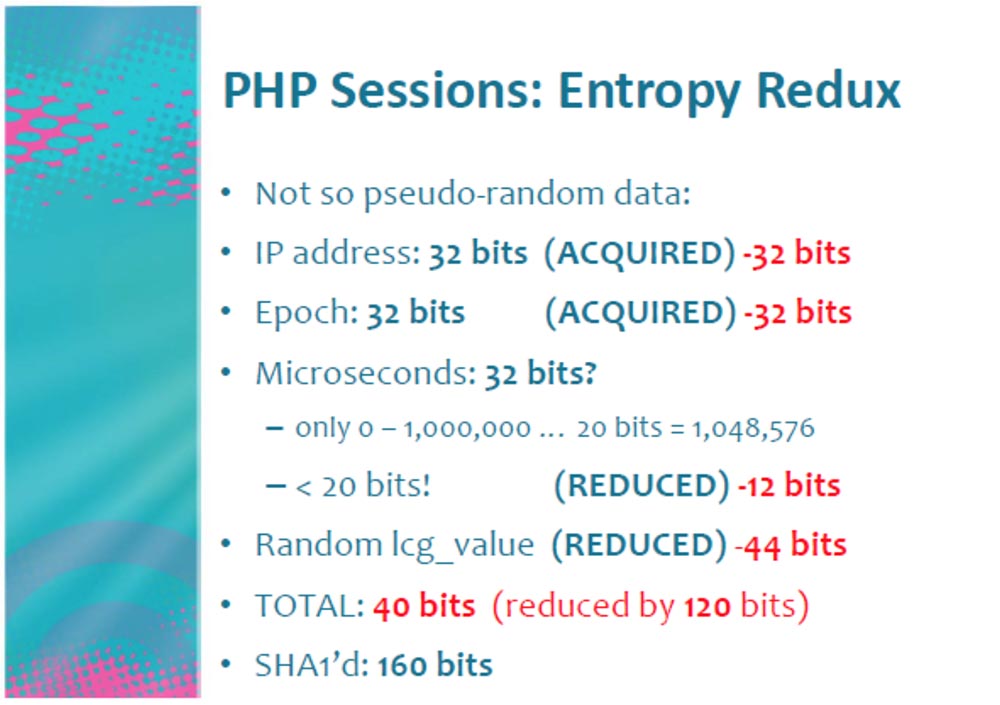
Thus, we were able to turn 64 bits of PRNG into 20 bits. As a result, we received not entirely random data and released as many as 120 bits for each PHP “cookie”!
But that is not all. We turned 32 bits of microseconds into 20 bits and reduced Random Lcg_value to 20 bits. Did we get 40 bits? Not! Let's first count the Lcg_value.
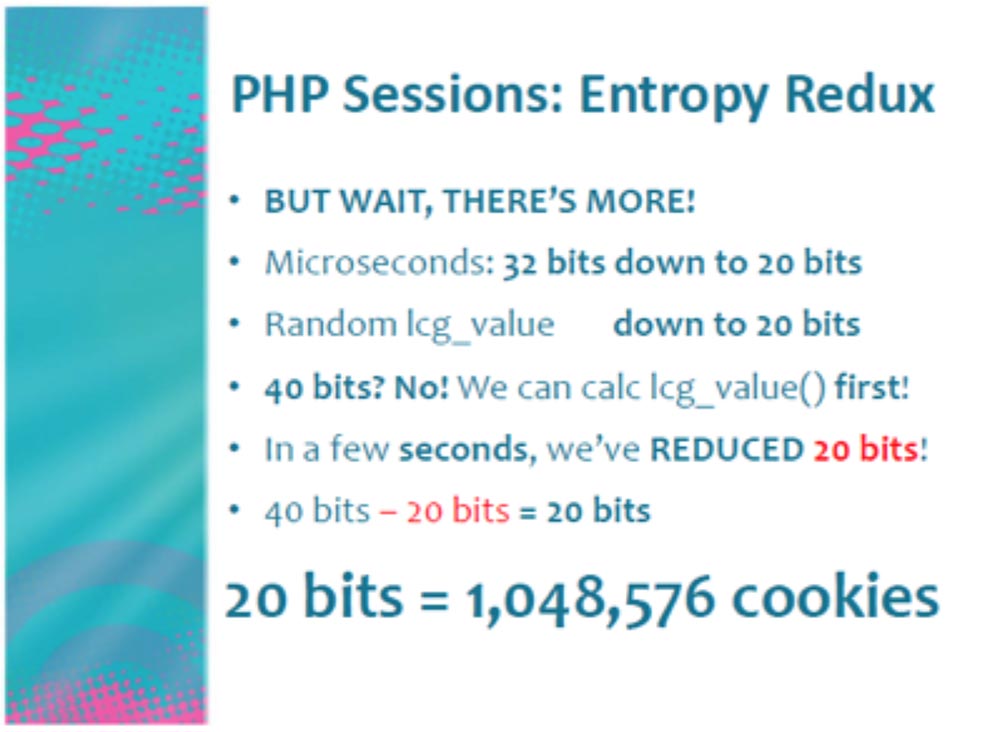
Choosing the optimal 4-MB time-memory ratio, time-memory trade-off, at which the computation time can be increased by reducing the used memory or, conversely, reduced by increasing the used memory, you can determine the actual value of SEED Lcg_value for a few seconds, freeing another 20 bits! By the way, I found the code for this operation on the DEFCON CD.
Then we get 40 bits - 20 bits = 20 bits. And 20 bits is more than a million cookies that are used to authenticate the user.
Let me explain again: we can easily create 500,000 authentication requests per day when we enter our Facebook page. That's how I created our “Snake”, our Robert Hansen!
I recall that in our case, such an entropy is a measure of the internal disorder of the information system, it increases with the chaotic distribution of information in the network and decreases with its ordering. Using PHP version 5.3.2, you can get a bit more entropy. It is also possible to create random sessions of your own volume or use your own random number generator. You do not need to understand encryption, just use the SEED provided by the computer operating system. If you are using Linux or another BSD, you do not need to use a process ID.
The attack is a very time-consuming process, but its implementation is facilitated in social networks, where I spend most of my time. Keep in mind that, in principle, Facebook is not a vulnerable resource, it creates its own version of PHP called HipHop, a kind of mixture of PHP and C ++, which works much faster.
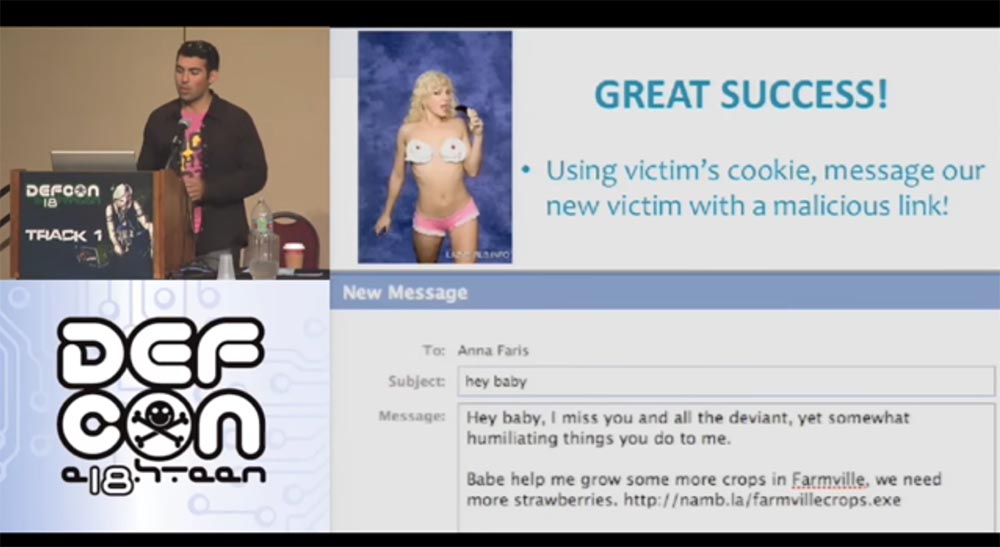
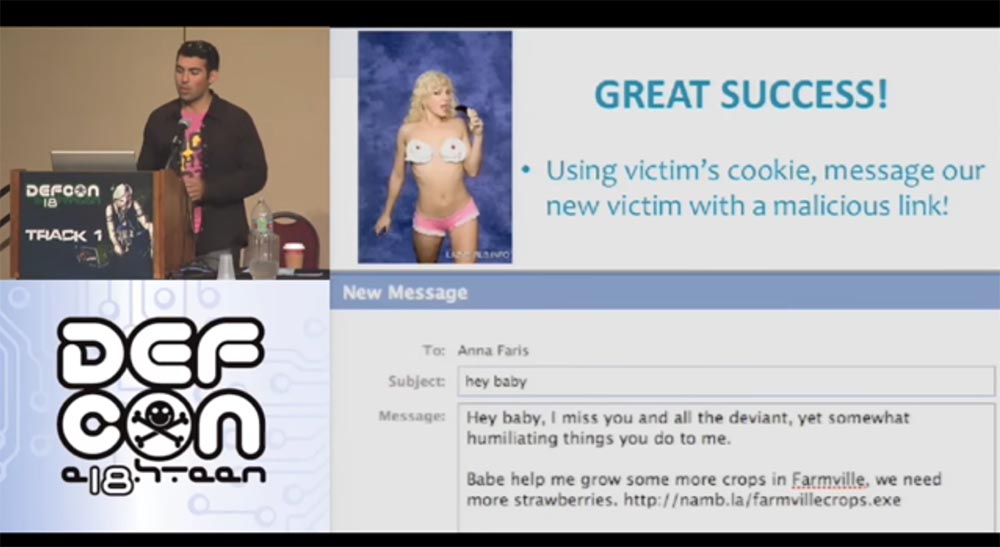
So, I register as a “Snake” and am going to introduce him to the girl Anna Faris. Using his cookies, I can write to her on his behalf, using a phishing link to my malicious blog with the address of the game on Facebook. I ask her to help me harvest my farmville game, as if I need more strawberries, and send her a link to the executable file. Now we are ready to attack her network.
Consider what this network is. Now I will show you how your network looks normal and "high".
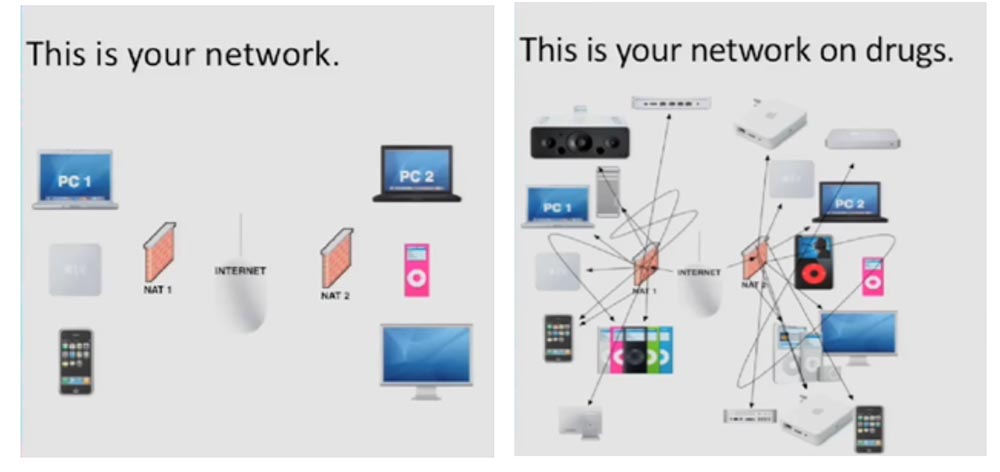
Let's try to learn more about NAT. This is a system in TCP / IP networks that allows you to access many public Internet resources using a single IP address. All your computers and devices located inside NAT share the same public IP address. Usually this is provided by the router provided to you by the network provider. There is also a firewall that protects your network, programs and computer ports from unauthorized entry. If you are in NAT and start, for example, Apache on port 80, no one can connect to you from the outside, except for internal users of your network.
However, there are XPS cross-protocol scripts, this is a cool thing that allows you to run an HTTP server on any port, sending data using JS form.submit (). This means that your browser establishes a connection with any resource on any ports.
The HTTP protocol is based on newline, which means that each line has data that is different from the data in the other lines, say, like XML data or a binary data stream.
There are other protocols based on the same “new line” principle, such as IRC. This is what the HTTP IRC client looks like. He uses a client computer to connect to the network using his IP address!
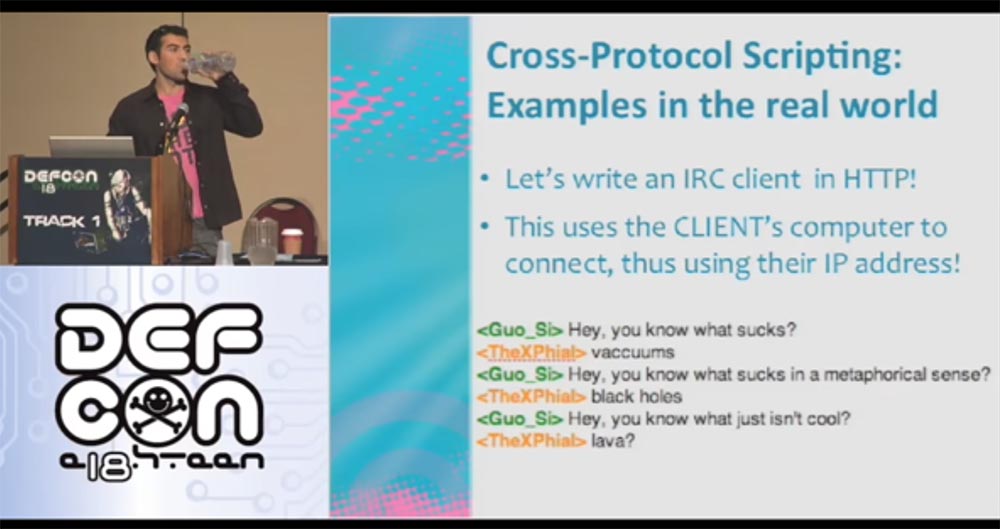
And here is an example of writing XPS IRC to connect to the irc.efnet.org server.
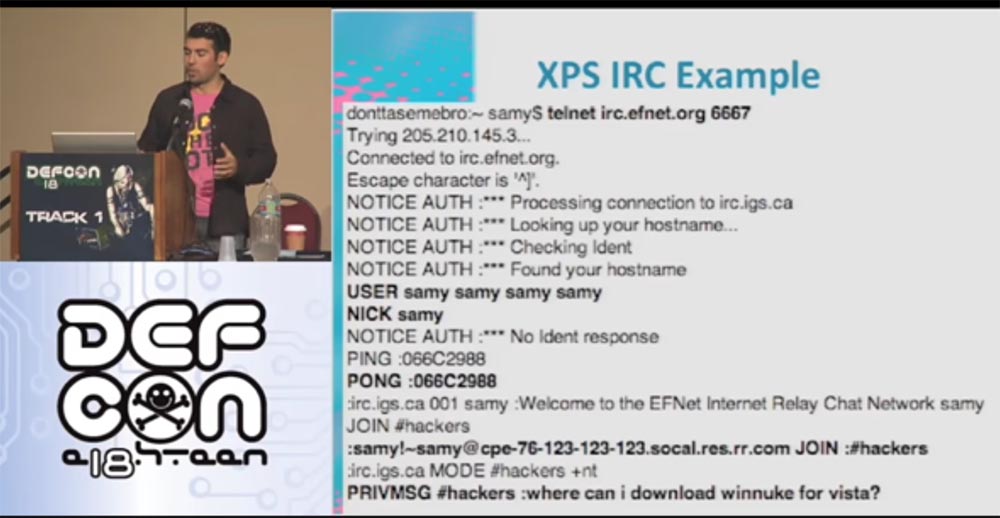
I enter my Samy login, respond to a ping request and join the #hackers channel to ask the question: “Where can I find winnuke for Vista”? Unfortunately, this no longer works, so if you find a working version, send it to me. The following slide shows what our IRS client looks like on the Internet.
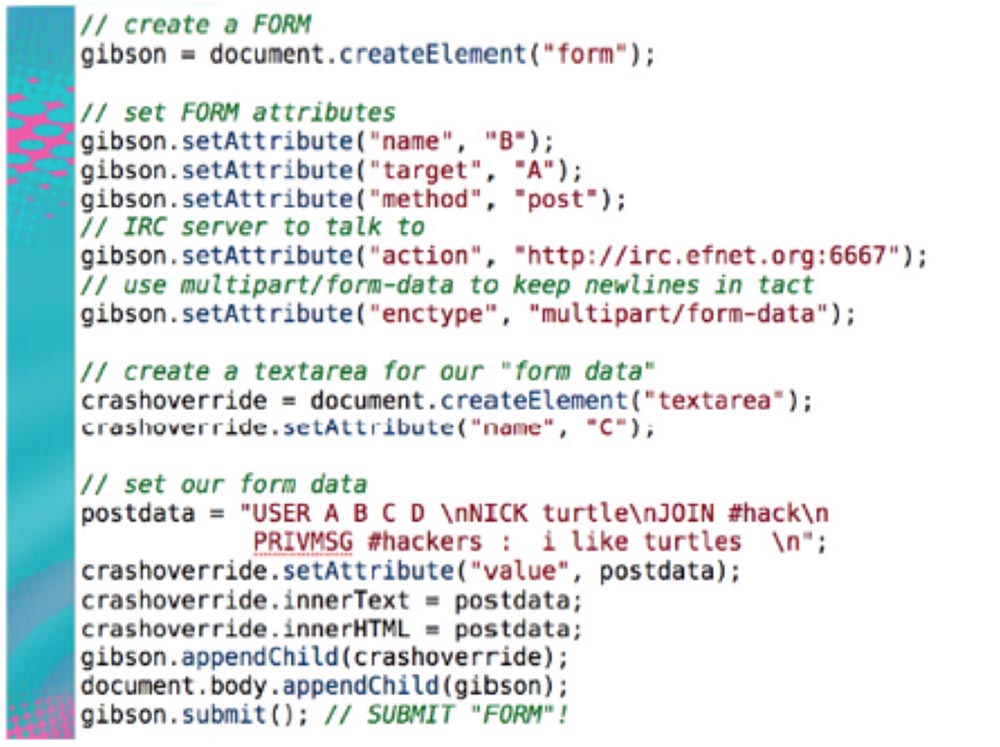
This is a form of creating a malicious page that contains the given code. You visit my malicious page, that is, your client connects to the IRC server, and your browser thinks it is an HTTP server. Therefore, it sends out HTTP requests with my malicious IRC data.
My IRC server accepts them and says: “I don’t understand this HTTP data, and I don’t understand this line, and this line, and the next one, but I understand this data - the ones that appear in the postdata line - I can interpret them, but I’ll ignore the rest. ” This means that I can use your IP address to connect to my IRC server.
This technique can be used for SMTP, which has been used by spammers for many years. Here your browser acts as a server for spamming. You go to the page and do not even suspect that it has a form that automatically connects your computer through port 25 to the HTTP server where the malicious text is located. And now you are sending out offers from your computer to buy Viagra as soon as you visit the Viagra website.
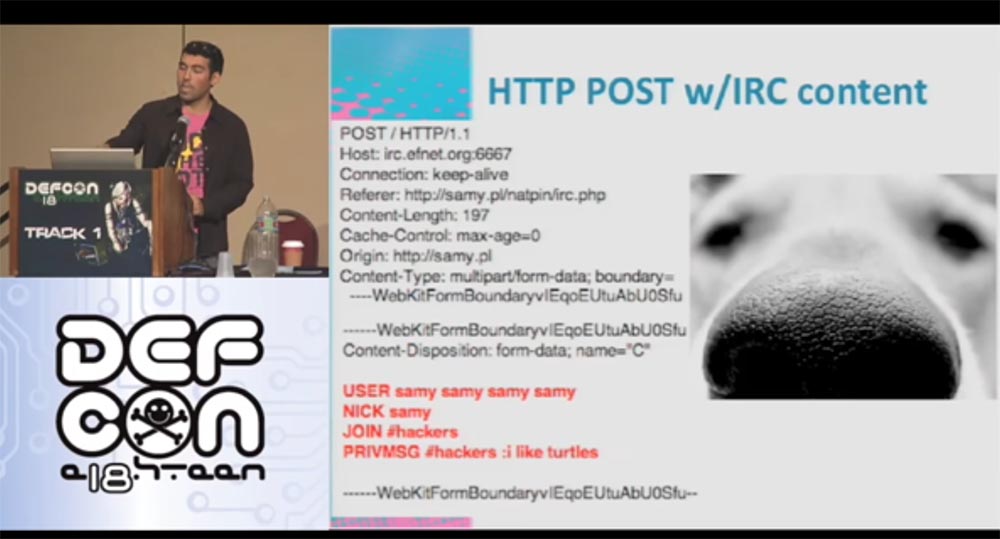
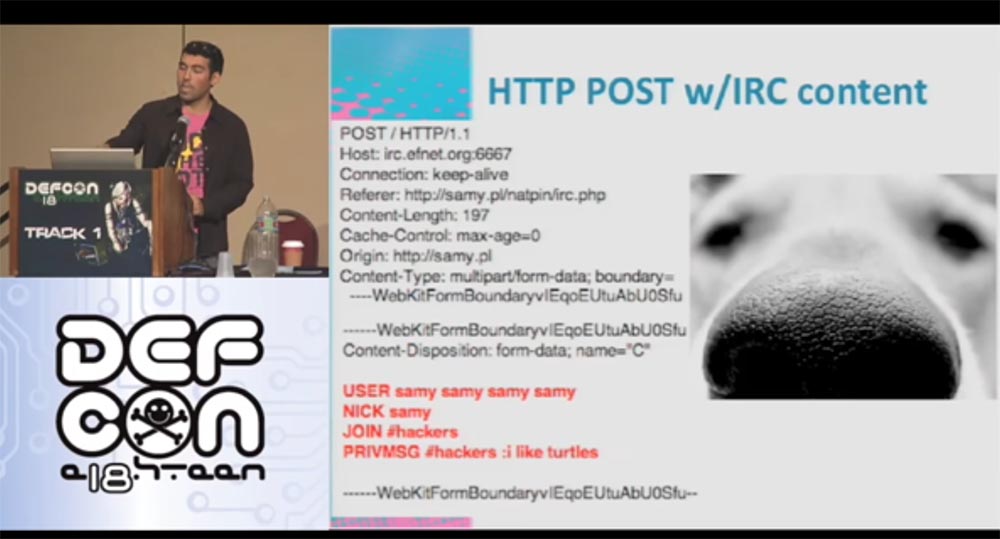
The following site shows what the HTTP post looks like. There is an HTTP header that your browser sends, and IRC data. I repeat again: the IRC server ignores data that it does not understand, until it comes across lines that are understandable to it.
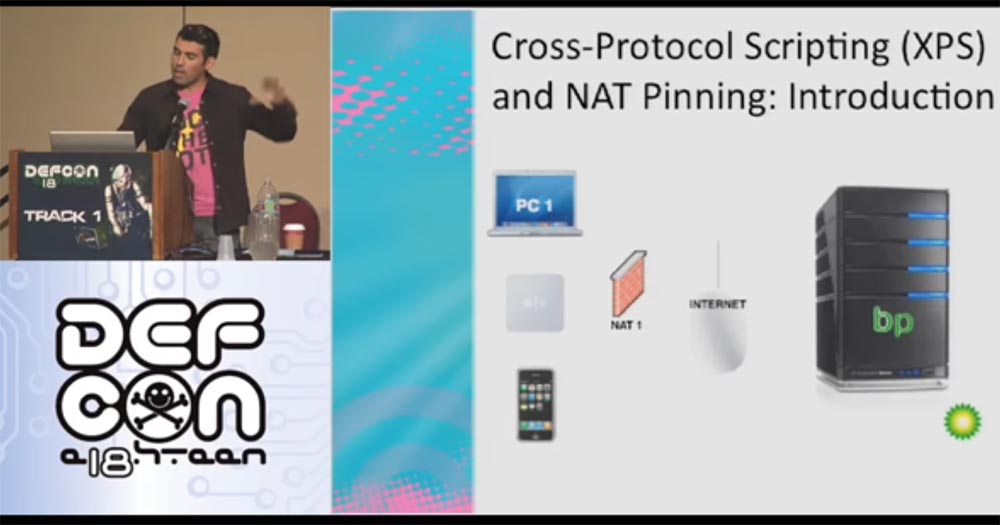
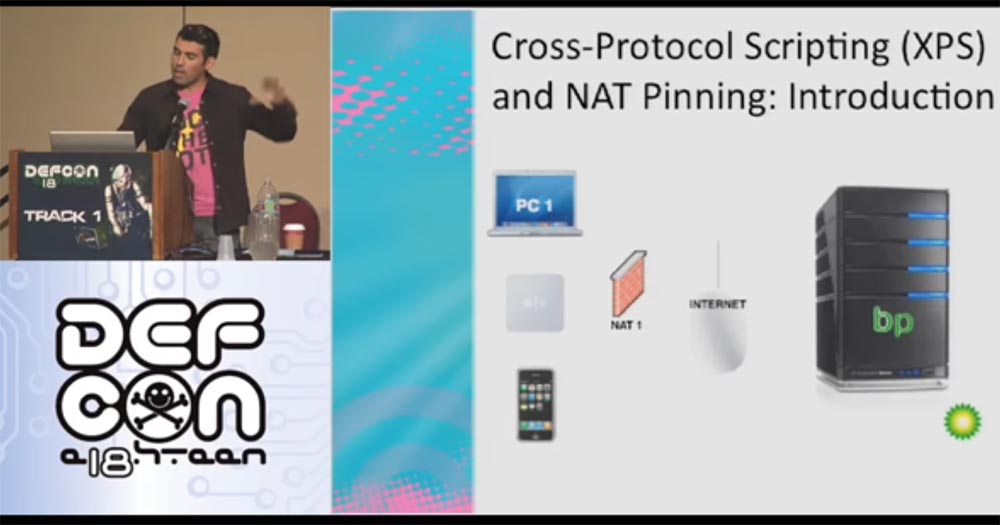
Now let's talk about the process, which I call NAT pinning. This is a technique in which the client’s browser is used to generate traffic representing the edge devices of the NAT network, which allows you to open and use additional ports of devices on the LAN network.
NAT pinning tricks not only the browser, but also the application-level router. In other words, when connecting through port 6667, the browser thinks it is HTTP, and the router considers it to be IRC. We can use this exploit to attack the client using a router.
Thus, the XPS is increased by 9000 times!
The following site shows a diagram of a malicious server where you are located behind the “wall” of your NAT.
You are already familiar with IRC, and now get acquainted with the DCC protocol - this is a direct client connection. Imagine that you are connected to an IRC server and are chatting with friends. You tell someone that you want to send this file here, so connect to me directly, I don’t want to use the server to send it. That is, when you send a person a request for a direct connection, this means that he must connect to this IP address and to this port. A few years ago, this process was not possible, but the routers became smarter and acquired new software. Therefore, now it has become possible that you visit my malicious website and pick up a form there, the data of which directs you to any of the ports I have indicated - 22, 80, 443, 25, 123 and so on. However, the browser is not up to date, what happens is that it simply processes the request, filling out its form, and I will attack you from all the ports I have selected. This is what the NAT pinning code looks like, which you can use for your own pleasure, it is also available on the DEFCON CD.

Here you can see that I choose port 6667 for attack, but it’s worth considering that now the browser is able to block certain ports.
Consider what a port lock is. What should I do if the browser blocks outgoing connections of non-HTTP ports? The size of the TCP or UDP port is 16 bits.
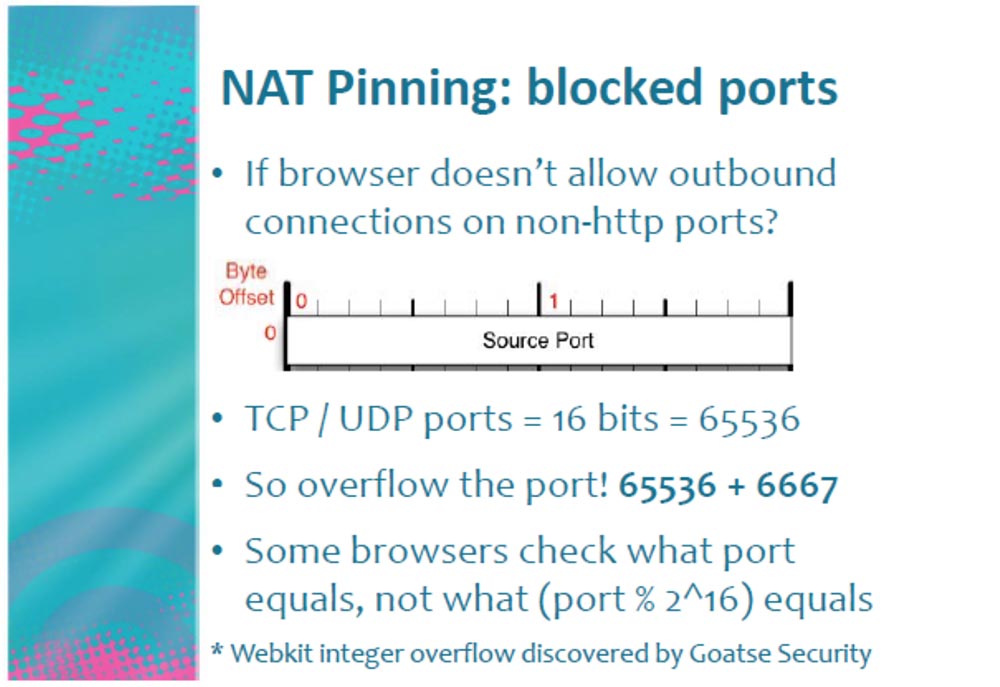
Suppose the browser says that it does not allow connection to port 6667, then we just overflow this port, adding another 16-bit port to it, that is 65536! As a result, the browser sees that this is not port 6667 at all, but port (6667 + 65536) = 72203, and sends data to the TCP stack at this address.
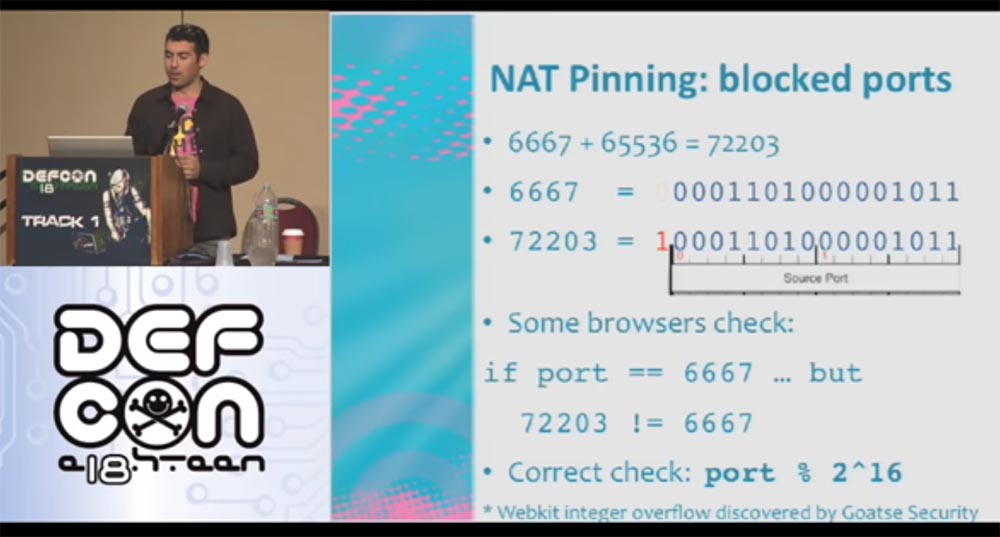
A port congestion tool called Webkit Integer was developed by the Goatse Security team, for which we are very grateful.
So, if Anna responded to my call and followed my link, I will attack her ports. After I joined port 80, it turned out that she had her own web server with her site about the Jacob 66 team from the Twilight series, that's how smart she is!
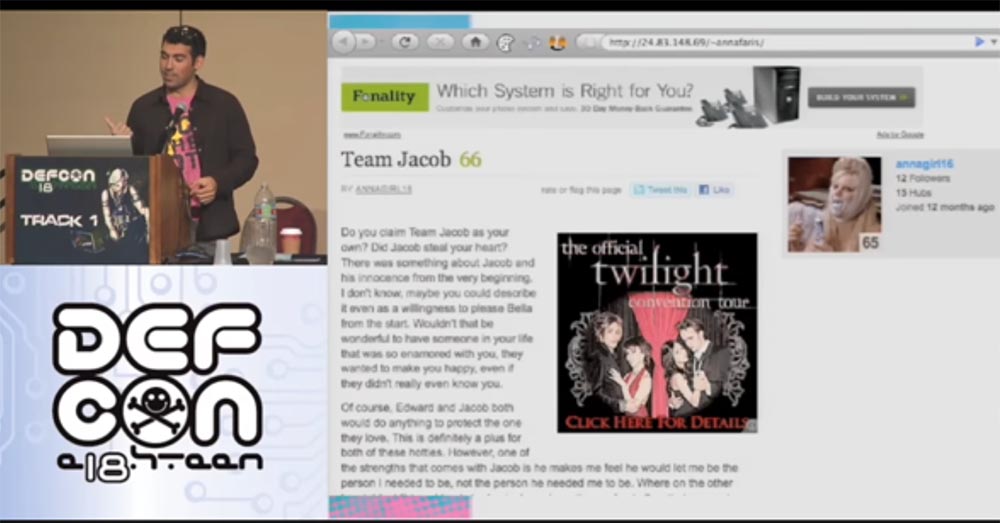
I also love Twilight and now I know how to conquer it! Actually, I belong to Edward’s team, but I won’t tell her about it. When we see her, I’ll tell her that I’m also in Jacob’s group!
It's time to consider how to protect yourself from NAT Pinning. There are several ways to do this. You can use a strict firewall that prohibits unknown outgoing connections.
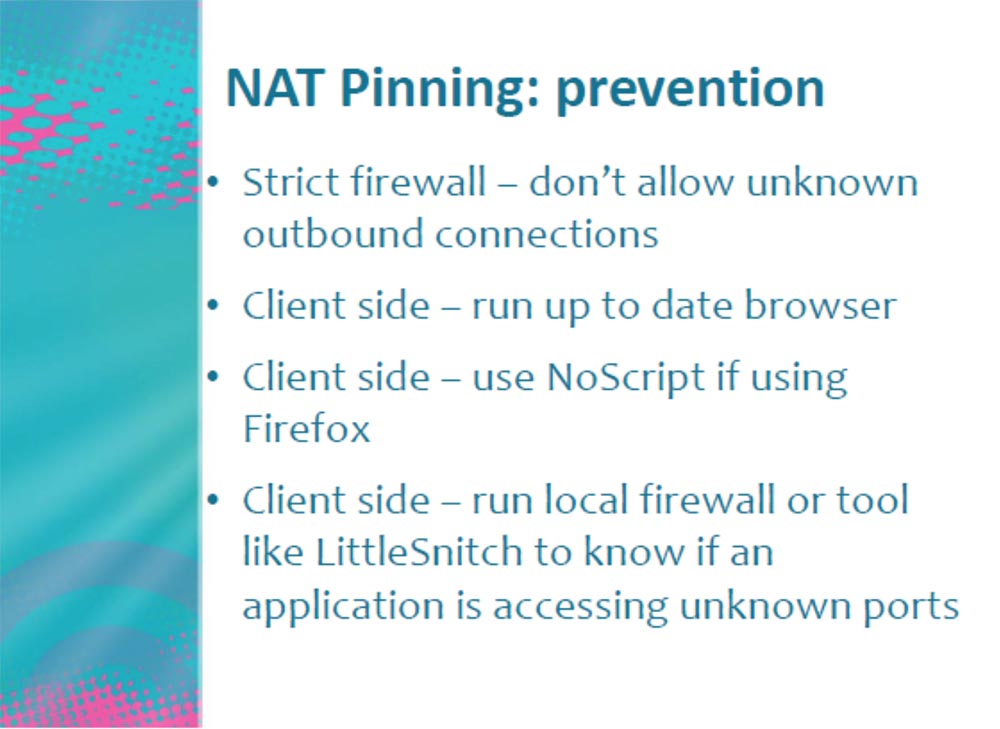
On the client side, you can use the most modern browser that has invulnerability, or enable NoScript mode when using the Firefox browser. In addition, the user can use a local firewall or tool such as LittleSnitch, which will notify you if an application tries to access an unknown port.
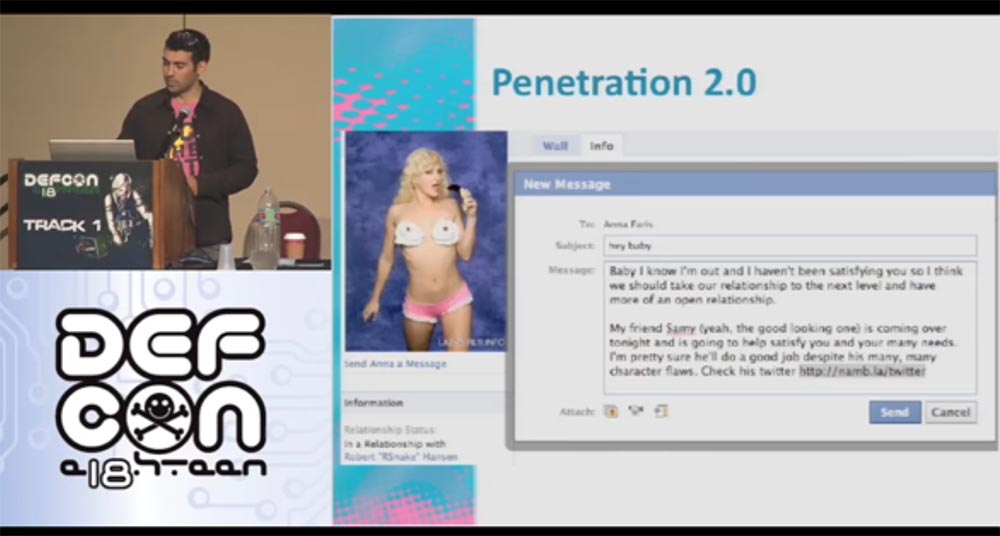
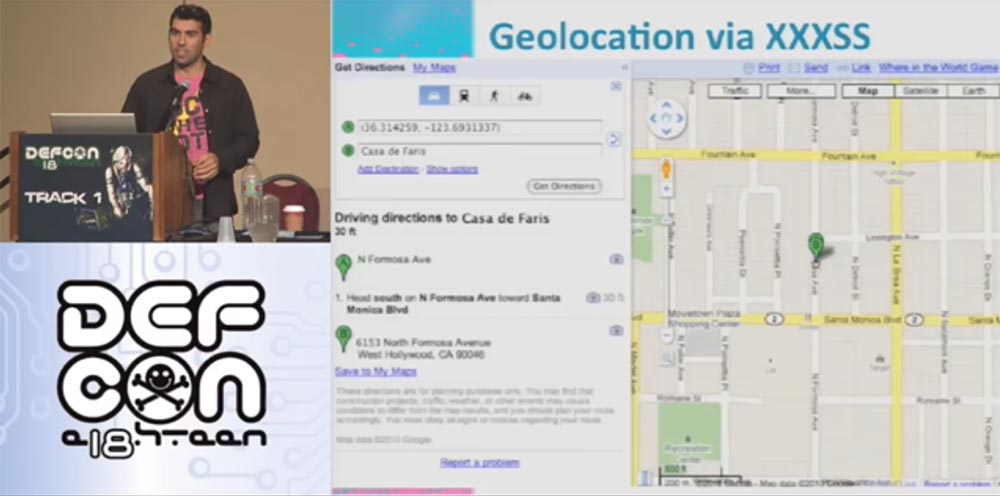
Consider what else can be done with our Anna. Let's try to determine its location. To do this, I, “Snake”, send her another message asking me to visit my friend Samy's page, my namb.la/twitter page.
Here I have an application called XXXSS for geolocation detection. When she visits my malicious site, this application scans her local network to determine which router is being used - its type, manufacturer, network provider, password and login to enter the network. It is very simple. I do not have access to her local network, but while her browser is on my malicious site, I can penetrate her network through her computer. I can connect directly through her IP address and get all the necessary permissions. I can also login using the login, determining the type and brand of the router. For example, for the Belkin router, there are default password tables and factory settings, that is, I can get everything that the provider has to remotely control the router. Having got control of the router, I remotely load Java Script into it.
Remote access uses AJAX, that is, the technology of accessing the server without reloading pages to capture the MAC address. Why do we need a MAC address and what does it contain that are interesting for us?
Google saves WiFi session data when you enter the network. And what does he remember in this data, which is transmitted when entering the Internet? The owner who logged in, that is, the MAC address of the device! In this case, this is the MAC address of your router. It also remembers the strength of the WiFi network signal when your device appears. And then our triple XXXSS, i.e. tripple XS / S, comes into effect. Suppose you are moving along a street in a car and the WiFi signal strength on your device is 10 out of 100, you turn to another street and it amplifies to 50 out of 100, on a parallel street it reaches 85 out of 100, and so on. Using the triangulation method, that is, the construction of serifs of signal strength on Google maps, you can determine the location of the strongest signal. This is where your computer will be located, that is, your home.
The Firefox browser has an extension called the Location Service. You can run a script that will force Firefox to go to Google and determine where my MAC address is coming from. He sends a request to Google HTTP with a request to tell him where this information came from.
Thus, when you visit my site, I use my XXXSS, get your MAC address, pass it off as my own and use my browser (I no longer need your browser) to get your coordinates on the map. All I needed for this was an exploit running on your router.
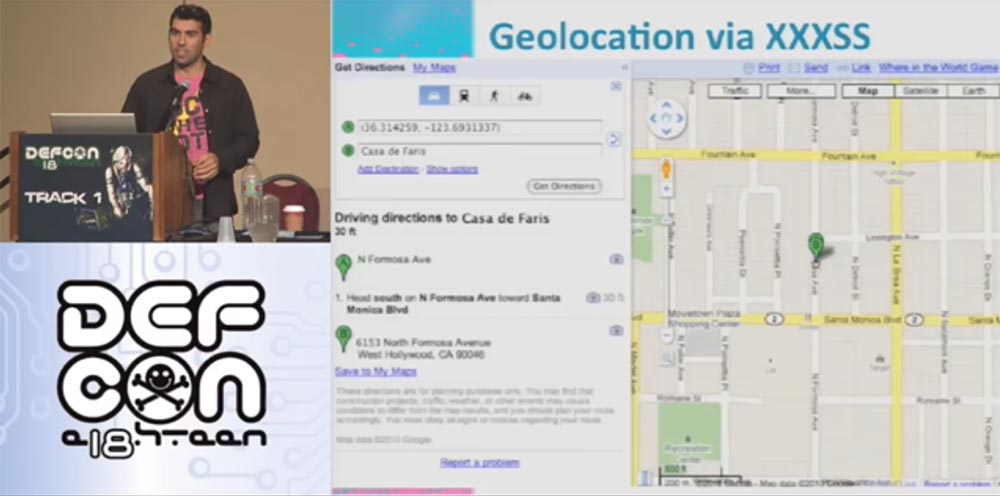
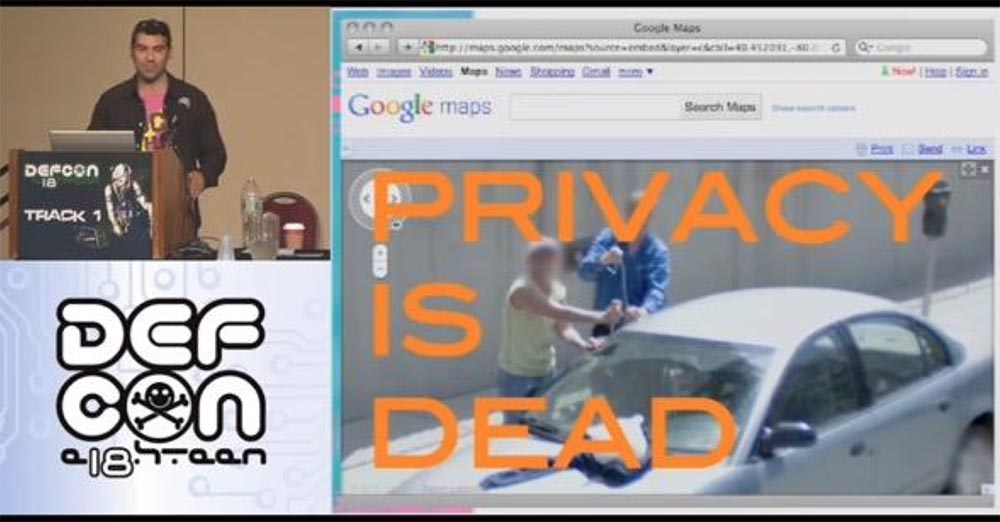
Do you know what I got as a result of these manipulations? That the Anne Faris router is 30 feet away from me. This is the accuracy of determining geolocation - 30 feet. I think Mark Zuckerberg said this better than me: "Privacy is dead!"
Thank you for attention.
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a 30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to Build Infrastructure Bldg. class using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?
My name is Samy Kamkar, I am investigating security issues, but not professionally, but for my own pleasure, like most of those present here. I am known as the “Narcissistic Vulnerability Pimp,” or “narcissist of narcissistic vulnerabilities,” I am the author of the Samy Worm virus, created on MySpace several years ago, and one of the founders of IP PBX Fonality. I am also called Chick Magnet, a “chick magnet,” and I'm a fan of Lady Gaga. And I also love cash.
On this slide, you see guys who have done me a great service - they allowed me not to touch the computer at all for a while. A few years ago, representatives of the USSS, United States Secret Service Electronic Crimes Task Forces, the US Secret Service cybercrime investigation team, burst into my house. They seized all my computers, took my laptop, mobile phone, CD and DVD players, and even the Xbox game console. The case ended in a court that forbade me to touch computers for life, but a couple of years ago I was "unban", and now I'm with you again, but without access to MySpace.
I’ll tell you why I want to talk about the Internet today. The Internet is new, it's cool, you can use it! But a few years ago I was bored. Because the Internet is good, but security is much wider. It covers all areas of web technology, and DEFCON is at the forefront of Internet security. This includes hardware engineering, network security, web application security, hacking hardware, and other funny things. Some guys even learned to pump cash from ATMs, but you probably don’t know about it. But the Internet is cool not only because of this. There is another reason.

If you have a computer, then you have an operating system that necessarily has a web browser. It is part of the software that allows me to deliver you some code that you use. This is such a delivery mechanism, thanks to which I can attack any of those present on the Internet. This is similar to the way apps from the App Store get to your iPhone, and you can get any content you want. Of course, Apple protects its content and protects you from annoying porn. Browsers act in exactly the same way, but no one protects them. No one cares that the sites you are viewing can be malicious.
Now I will show you my page on Facebook. She is very popular because many people like Anna Faris, she is amazing.
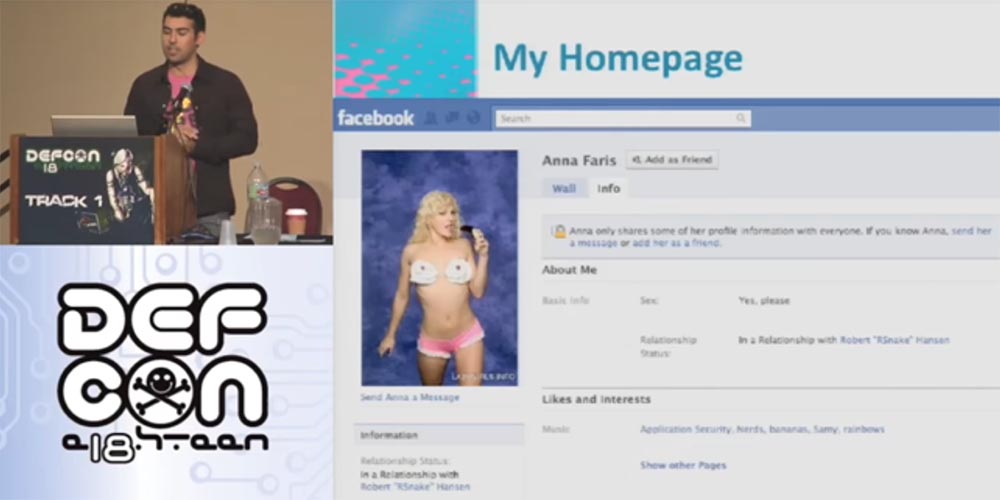
I usually post such a picture before creating a bunch of troubles. One guy wants to meet Anna. He studies her profile, looks at her photos, but cannot see everything, because he is not a friend of her. And then he had the idea to write to her through a messenger to establish a relationship. So who is this guy and how can I help him?
And then I find out a lot of interesting things!
The guy who will be the target of the attack is:
- professional specialist in the field of security of certified information;
- CEO of SecTheory;
- co-author of the work “XSS exploits: attack and protection against cross-site scripts”;
- author of the book “Determination of harmfulness”;
- co-author of Jeremiah Grossman, creator of Clickjacking, a technology for attacking websites;
- creator of ha.ckers.org and sla.ckers.org;
- Certified Software Security Specialist (ASS).
From the applause in the hall, I realized that you like my idea.
This is a very impressive resume. Now I will show you its author - this is Robert "RSnake" Hansen, Robert "Snake" Hansen. The problem is that I am going to attack this guy.
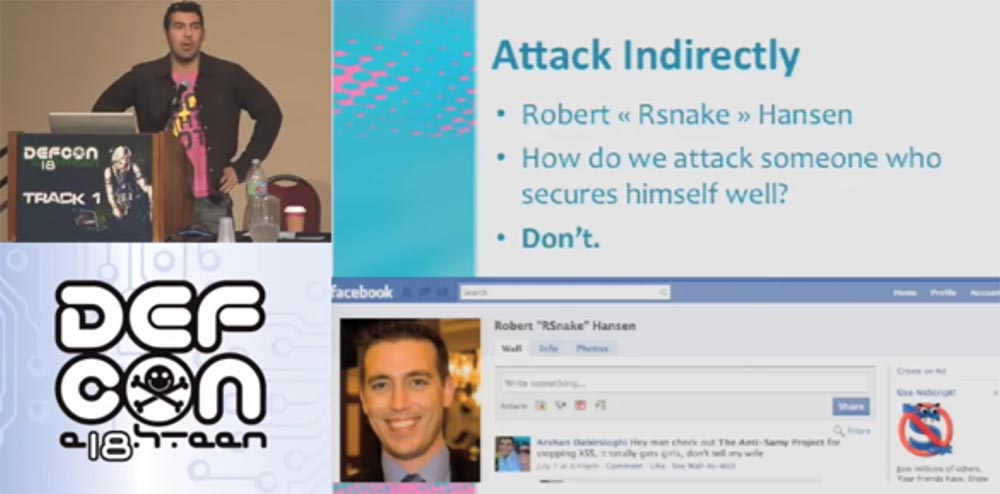
We can easily attack random people by sending them malware or forcing them to follow phishing links, but now I'm going to attack a specific person who understands security and uses many technologies to provide our own protection.
So how do I attack this person? Right - no way. I cannot do this, so I will act differently.
Our guy is registered on Facebook. Facebook is an amazing social network that has the properties inherent in all Internet resources. When authorizing on the main page at the end of the address bar, we see the symbols index.php. You probably think this is FIP, but no, it is just PHP, a general-purpose scripting language used to develop web applications. Surely many of you have heard about it or even programmed in this language. Its code is open source, so you can change the encoding and observe what it leads to. This is a great tool for managing Internet sessions that everyone can use for their needs. Everyone who uses PHP and sessions uses a session management system. They use software platforms, frameworks such as cakePHP, Kohana or Codelgniter.
A PHP session is a random string that is generated in URLs or cookies. Cookies are pieces of text that remain in your browser and contain session data.
When you go to any page of the site, the browser checks to see if its cookies are stored on the computer. When you go to Facebook and enter your username and password, a random line is generated from them. When you go to another Facebook page, she checks this line and says: “Oh, I know this guy, this is Samy!” That is, it performs your authentication and provides access.
Consider what PHP session code is.
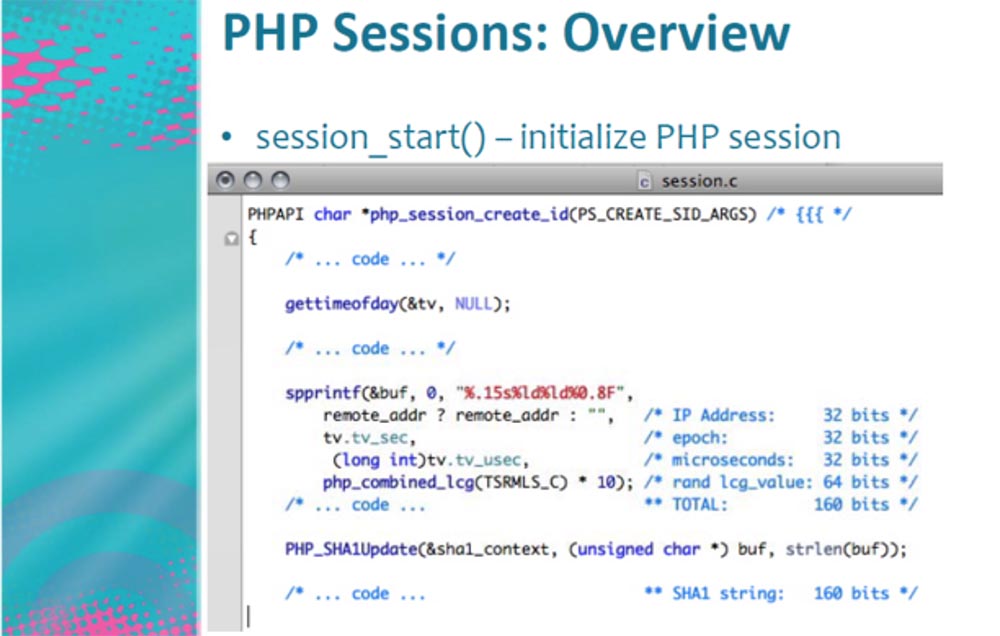
This is the part that starts and creates the session. It consists of several lines that contain the IP address of the authorized user, era, that is, the time elapsed since January 1, 1970, the number of microseconds required to create cookies, and all this looks like random numbers that are created in the range of 160 bits . 160 bits is a very large range for hacking, that is, an attack with password guessing using Brute Force technology.
Consider how big each bit is. Each time you add a new bit, you double their total number. Therefore, 160 bits represent a gigantic number.
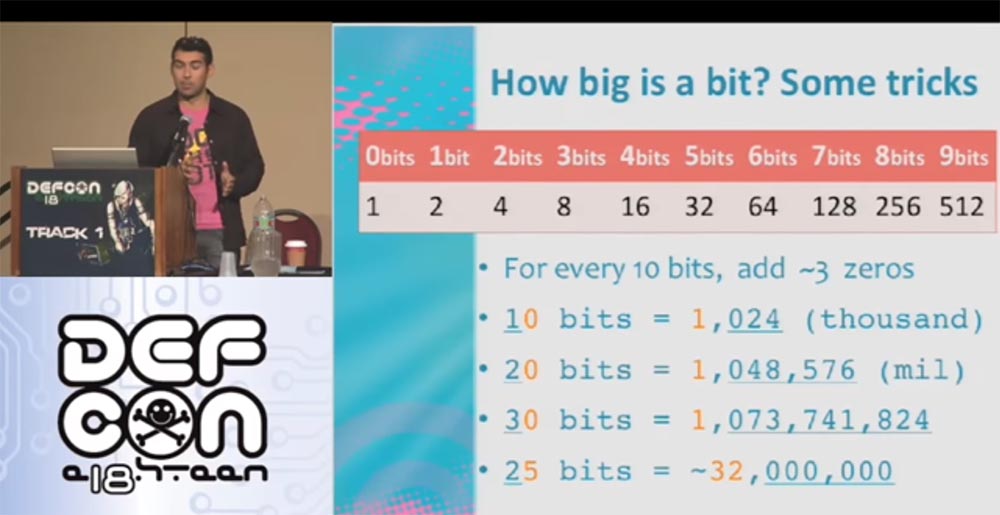
Each time, adding zero, we perform a trick with the bits - for every 10 bits three zeros are added, that is, 10 bits = 1000, 20 bits = 1,000,000, 30 bits = 1,000,000,000 and so on. Thus, if we use Brute Force with an intensity of one hundred trillion operations per second, 160 bits will be equivalent to 900 quadrillion Eon, where 1 Eon corresponds to 500 million years.
So we have 160 bits. How can I hack them? It doesn’t matter which computer you have. Consider the detailed how many bits each of these parameters really needs, that is, the process of returning the entropy of a PHP session, and what microseconds are.
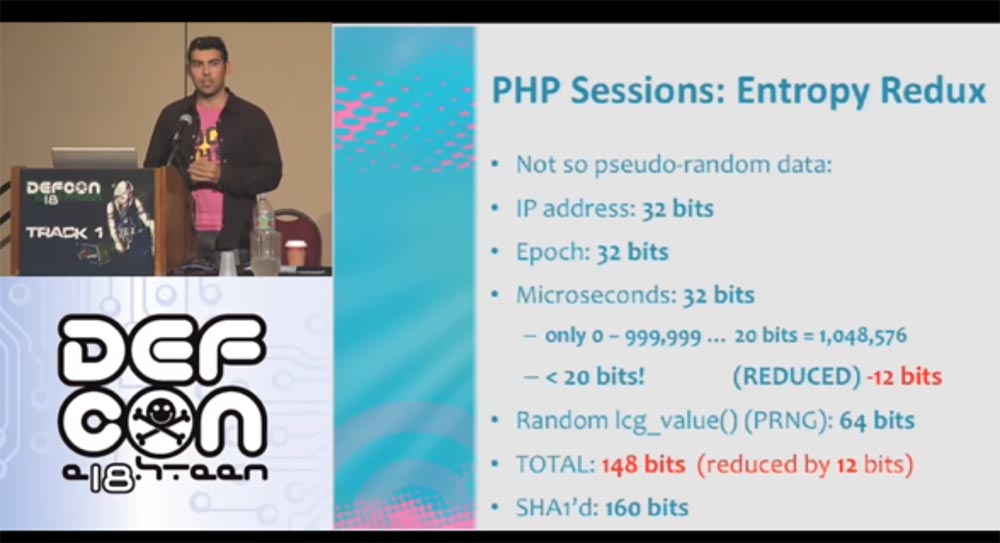
One second consists of a million microseconds. If you remember, a million is only 20 bits, and we have 32 bits. Thus, we have not done anything yet, but already saved as much as 12 bits. That is, in fact, we have 148 bits plus 12 extra.
Consider in detail the entrance to Facebook. When you go to the page, they check you out. The status is constantly updated, that is, Facebook captures when you log in to your account or log out. If you use live HTTP or a packet analyzer, you see how the HTTP request is returned, and you can recreate it. You can send requests every second and receive a server response.
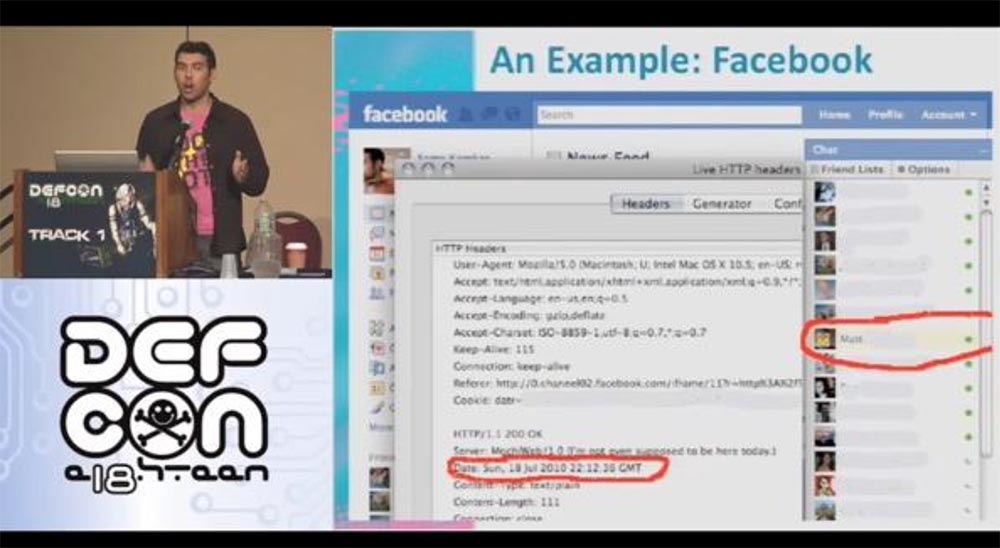
On this slide, the data returned by the server is circled in red. This is his local time. It does not particularly help us, because we do not know how exactly our time differs from the local server time. But this local time creates its own cookies. These are 32 bits, which we can also save by sending requests to the server every second, that is, free up the Epoch field. We developed a program that goes online every second, converts the Data parameter to Epoch and frees 32 bits. Thus, our savings are 12 + 32 = 44 bits out of 160. This is just wonderful - we got into our hands as many as 44 bits.
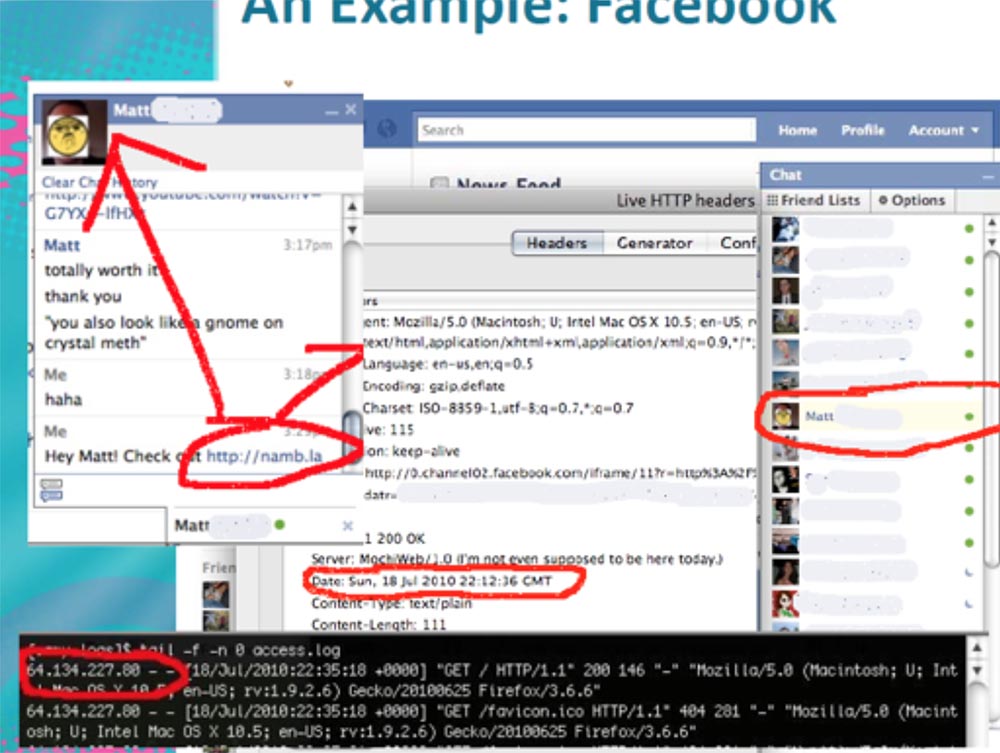
Let's continue further. If we send some information to our address in a chat, for example, my blog, then we can track its IP address. It appears in the Apache log, as shown in the next slide in a red frame.
These are 32 more bits of our cookies. Thus, we get already 12 + 32 + 32 = 76 bits of saving out of 160 bits, that is, another 84 bits of cookies remain busy.
What else remains with us? Parameter Random Lcg_value of 64 bits. LCG is a linear congruent pseudo random number generator that is commonly used in cryptography. It was developed about 25 years ago, that's all I know about it. In fact, this LCG uses two generators connected to each other. I do not want to delve into the mathematical subtleties, just consider the code that is generated by this generator. It is a SEED - block cryptographic algorithm that creates a series of random numbers.
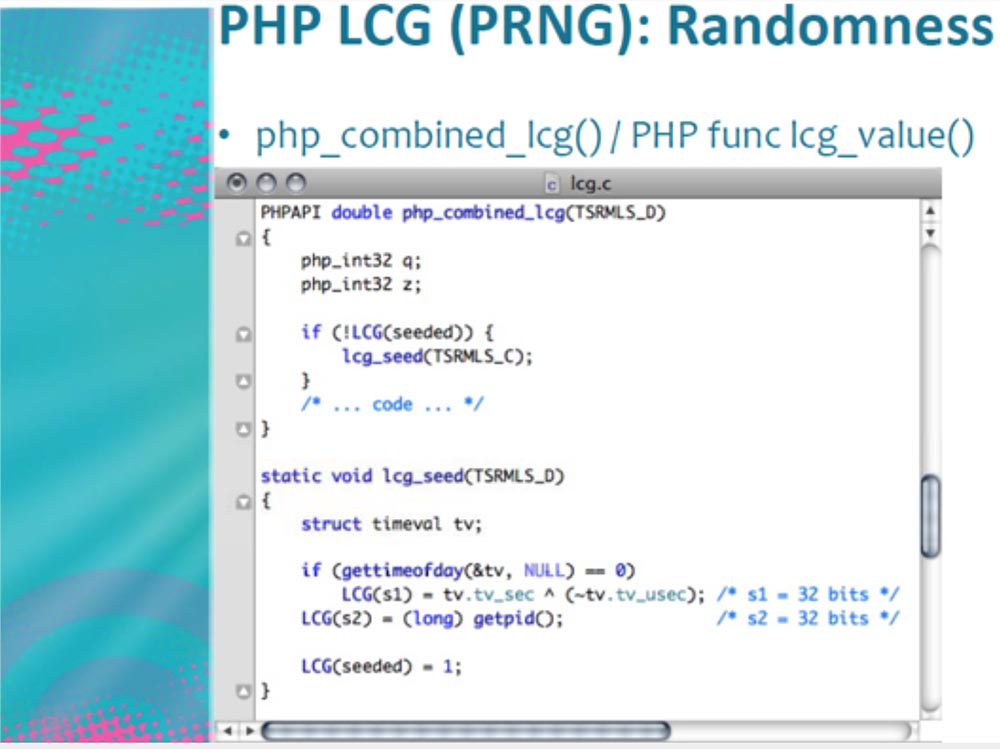
At the bottom of the screen, we see an LCG consisting of two variables s1 and s2 each 32 bits in size, that is, each SEED consists of 64 bits of entropy. Parameter s1 = tv.tv_sec describes Epoch, that is, the number of microseconds, and parameter s2 represents the process ID.
Let's consider s1 in more detail.
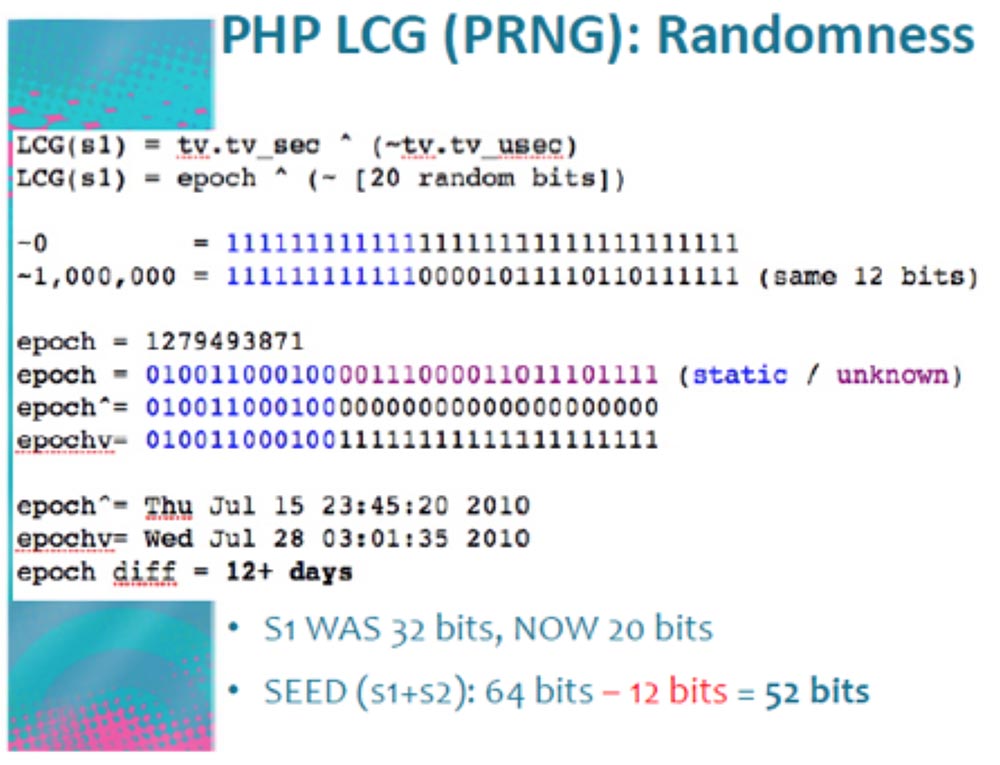
The generated PHP parameter LCG (s1) describes the Epoch in random bits, and it has a size of about 20 bits. We can send thousands and thousands of requests per second to the server, forcing it to overload the information sent back that relates to time. The difference in the readings of time is 12 hours + a day, we do not know what it really is, but for our process this is not important. As a result of the work of the program generating the requests, we use only 20 bits out of 32, that is, we save another 12 bits. Thus, the size of parameter s1 changes from 32 to 20 bits, and the total size of SEED (s1 + s2) from 64 bits turns into 52 bits.
Consider what an ID process is, designated as LCG (s2). We know that s2 = 32 bits. But Linux, which runs the Apache server, uses only 15 bits to create the PID, which means that 32 - 15 = 17 bits can really be freed from s2.
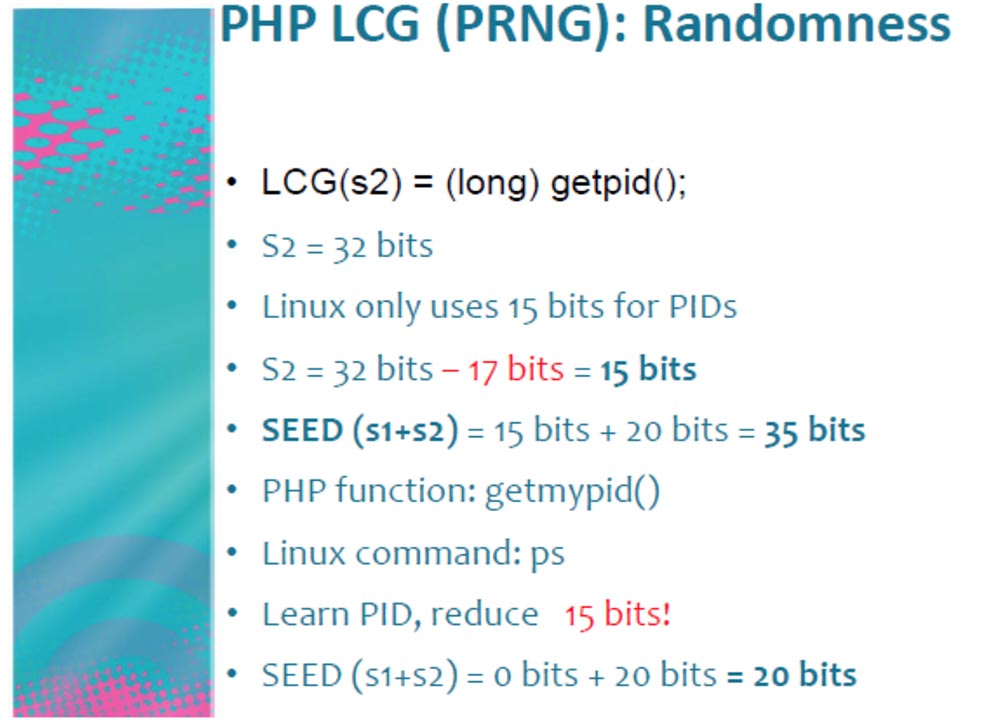
As a result, we get the size of SEED (s1 + s2) = 15 bits + 20 bits = 35 bits. The getmypid PHP function corresponds to the Linux command: ps, so knowing the PID, that is, executing it with our program, releases another 15 bits, total SEED (s1 + s2) = 0 bits + 20 bits = 20 bits.
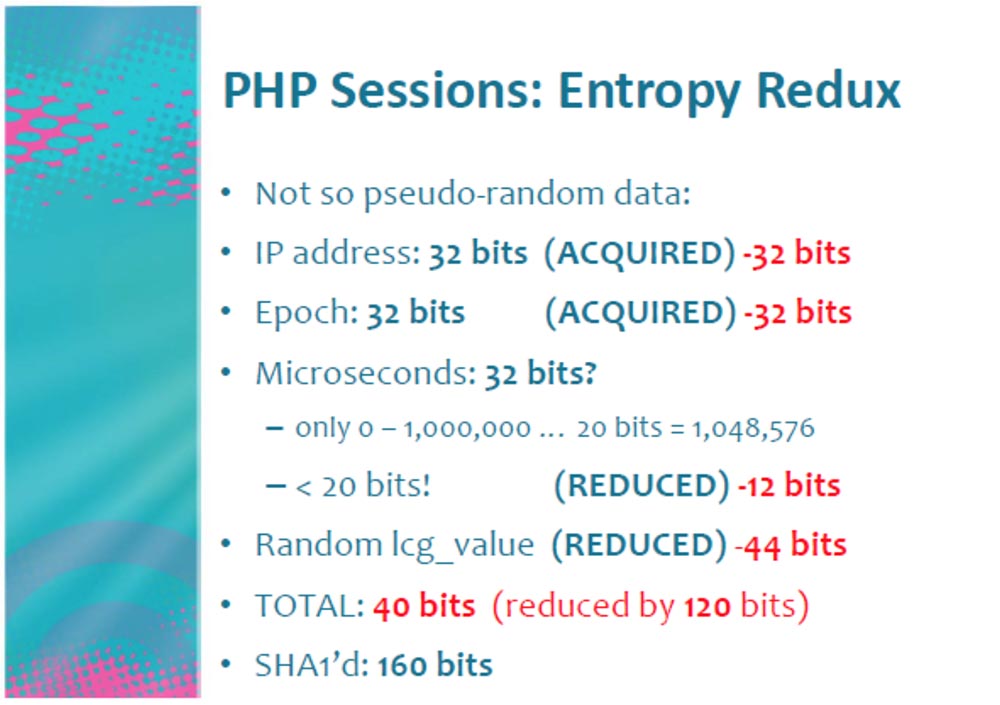
Thus, we were able to turn 64 bits of PRNG into 20 bits. As a result, we received not entirely random data and released as many as 120 bits for each PHP “cookie”!
But that is not all. We turned 32 bits of microseconds into 20 bits and reduced Random Lcg_value to 20 bits. Did we get 40 bits? Not! Let's first count the Lcg_value.
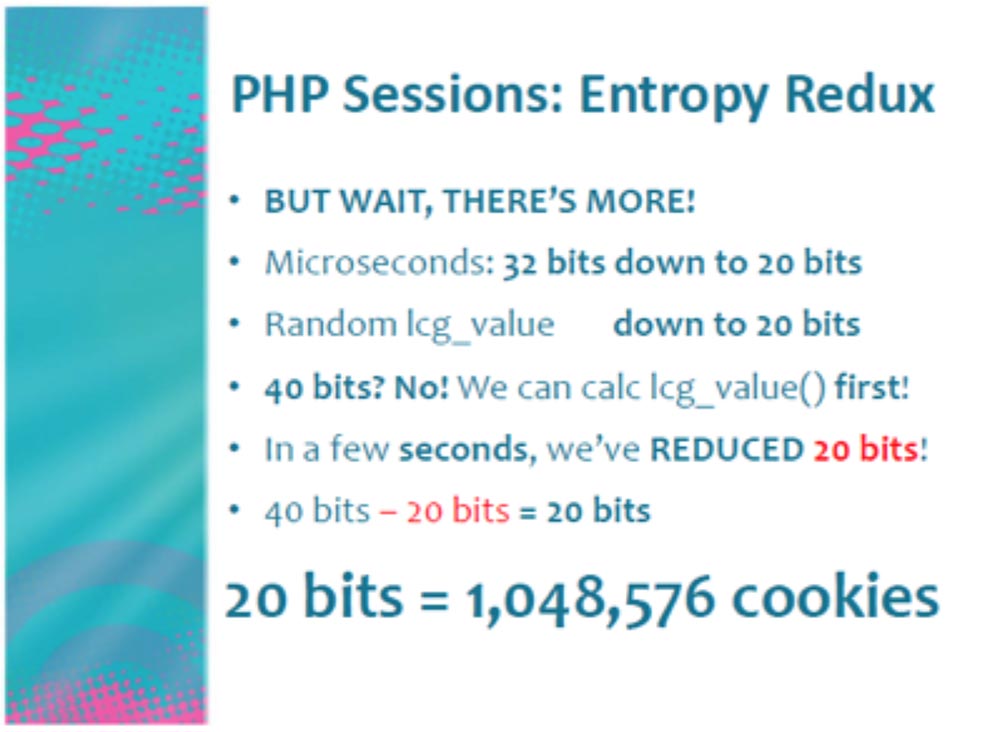
Choosing the optimal 4-MB time-memory ratio, time-memory trade-off, at which the computation time can be increased by reducing the used memory or, conversely, reduced by increasing the used memory, you can determine the actual value of SEED Lcg_value for a few seconds, freeing another 20 bits! By the way, I found the code for this operation on the DEFCON CD.
Then we get 40 bits - 20 bits = 20 bits. And 20 bits is more than a million cookies that are used to authenticate the user.
Let me explain again: we can easily create 500,000 authentication requests per day when we enter our Facebook page. That's how I created our “Snake”, our Robert Hansen!
I recall that in our case, such an entropy is a measure of the internal disorder of the information system, it increases with the chaotic distribution of information in the network and decreases with its ordering. Using PHP version 5.3.2, you can get a bit more entropy. It is also possible to create random sessions of your own volume or use your own random number generator. You do not need to understand encryption, just use the SEED provided by the computer operating system. If you are using Linux or another BSD, you do not need to use a process ID.
The attack is a very time-consuming process, but its implementation is facilitated in social networks, where I spend most of my time. Keep in mind that, in principle, Facebook is not a vulnerable resource, it creates its own version of PHP called HipHop, a kind of mixture of PHP and C ++, which works much faster.
So, I register as a “Snake” and am going to introduce him to the girl Anna Faris. Using his cookies, I can write to her on his behalf, using a phishing link to my malicious blog with the address of the game on Facebook. I ask her to help me harvest my farmville game, as if I need more strawberries, and send her a link to the executable file. Now we are ready to attack her network.
Consider what this network is. Now I will show you how your network looks normal and "high".
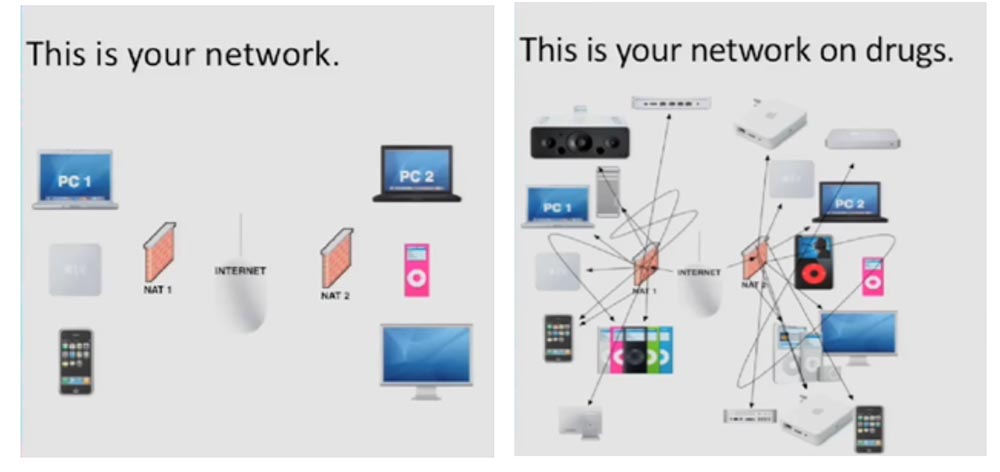
Let's try to learn more about NAT. This is a system in TCP / IP networks that allows you to access many public Internet resources using a single IP address. All your computers and devices located inside NAT share the same public IP address. Usually this is provided by the router provided to you by the network provider. There is also a firewall that protects your network, programs and computer ports from unauthorized entry. If you are in NAT and start, for example, Apache on port 80, no one can connect to you from the outside, except for internal users of your network.
However, there are XPS cross-protocol scripts, this is a cool thing that allows you to run an HTTP server on any port, sending data using JS form.submit (). This means that your browser establishes a connection with any resource on any ports.
The HTTP protocol is based on newline, which means that each line has data that is different from the data in the other lines, say, like XML data or a binary data stream.
There are other protocols based on the same “new line” principle, such as IRC. This is what the HTTP IRC client looks like. He uses a client computer to connect to the network using his IP address!
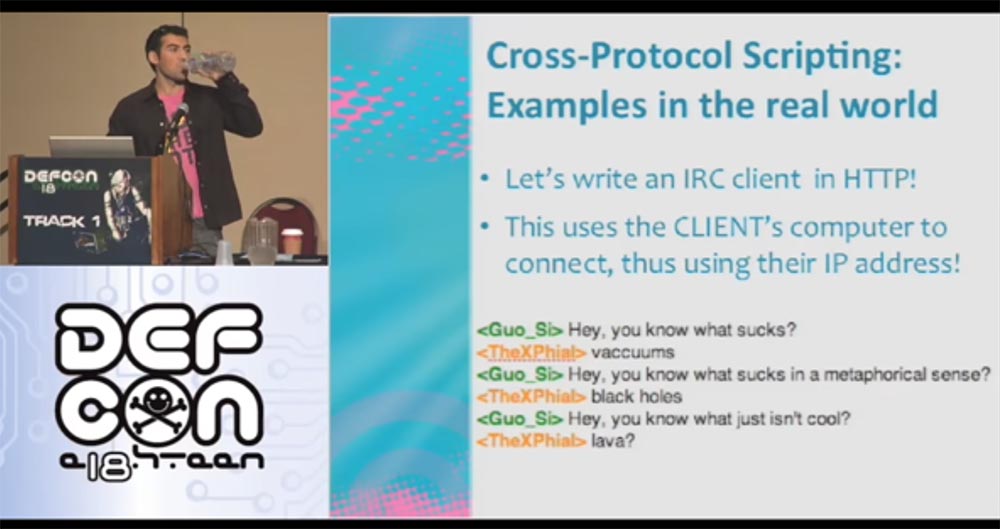
And here is an example of writing XPS IRC to connect to the irc.efnet.org server.
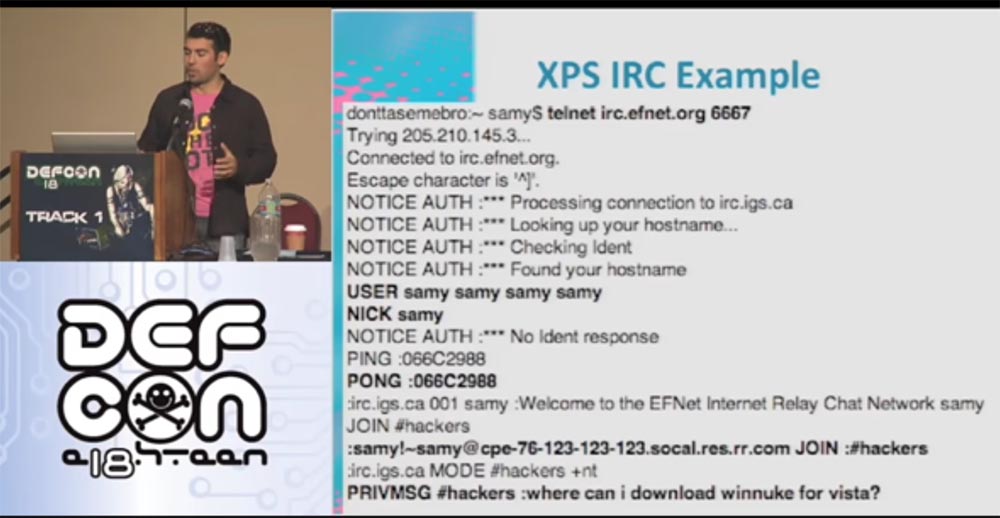
I enter my Samy login, respond to a ping request and join the #hackers channel to ask the question: “Where can I find winnuke for Vista”? Unfortunately, this no longer works, so if you find a working version, send it to me. The following slide shows what our IRS client looks like on the Internet.
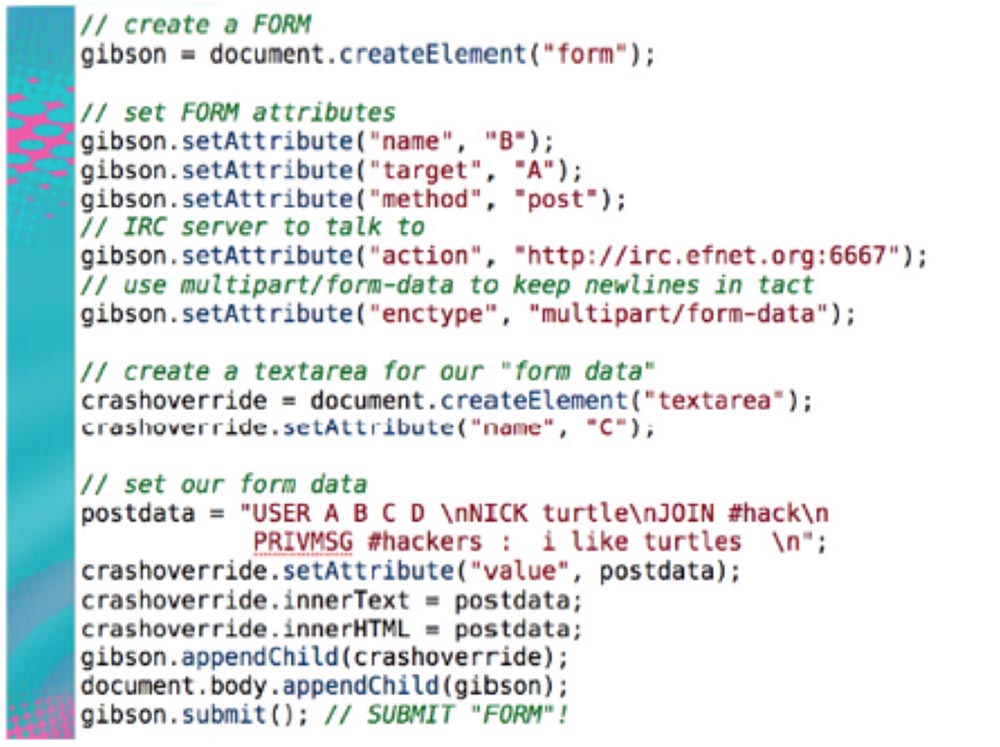
This is a form of creating a malicious page that contains the given code. You visit my malicious page, that is, your client connects to the IRC server, and your browser thinks it is an HTTP server. Therefore, it sends out HTTP requests with my malicious IRC data.
My IRC server accepts them and says: “I don’t understand this HTTP data, and I don’t understand this line, and this line, and the next one, but I understand this data - the ones that appear in the postdata line - I can interpret them, but I’ll ignore the rest. ” This means that I can use your IP address to connect to my IRC server.
This technique can be used for SMTP, which has been used by spammers for many years. Here your browser acts as a server for spamming. You go to the page and do not even suspect that it has a form that automatically connects your computer through port 25 to the HTTP server where the malicious text is located. And now you are sending out offers from your computer to buy Viagra as soon as you visit the Viagra website.
The following site shows what the HTTP post looks like. There is an HTTP header that your browser sends, and IRC data. I repeat again: the IRC server ignores data that it does not understand, until it comes across lines that are understandable to it.
Now let's talk about the process, which I call NAT pinning. This is a technique in which the client’s browser is used to generate traffic representing the edge devices of the NAT network, which allows you to open and use additional ports of devices on the LAN network.
NAT pinning tricks not only the browser, but also the application-level router. In other words, when connecting through port 6667, the browser thinks it is HTTP, and the router considers it to be IRC. We can use this exploit to attack the client using a router.
Thus, the XPS is increased by 9000 times!
The following site shows a diagram of a malicious server where you are located behind the “wall” of your NAT.
You are already familiar with IRC, and now get acquainted with the DCC protocol - this is a direct client connection. Imagine that you are connected to an IRC server and are chatting with friends. You tell someone that you want to send this file here, so connect to me directly, I don’t want to use the server to send it. That is, when you send a person a request for a direct connection, this means that he must connect to this IP address and to this port. A few years ago, this process was not possible, but the routers became smarter and acquired new software. Therefore, now it has become possible that you visit my malicious website and pick up a form there, the data of which directs you to any of the ports I have indicated - 22, 80, 443, 25, 123 and so on. However, the browser is not up to date, what happens is that it simply processes the request, filling out its form, and I will attack you from all the ports I have selected. This is what the NAT pinning code looks like, which you can use for your own pleasure, it is also available on the DEFCON CD.

Here you can see that I choose port 6667 for attack, but it’s worth considering that now the browser is able to block certain ports.
Consider what a port lock is. What should I do if the browser blocks outgoing connections of non-HTTP ports? The size of the TCP or UDP port is 16 bits.
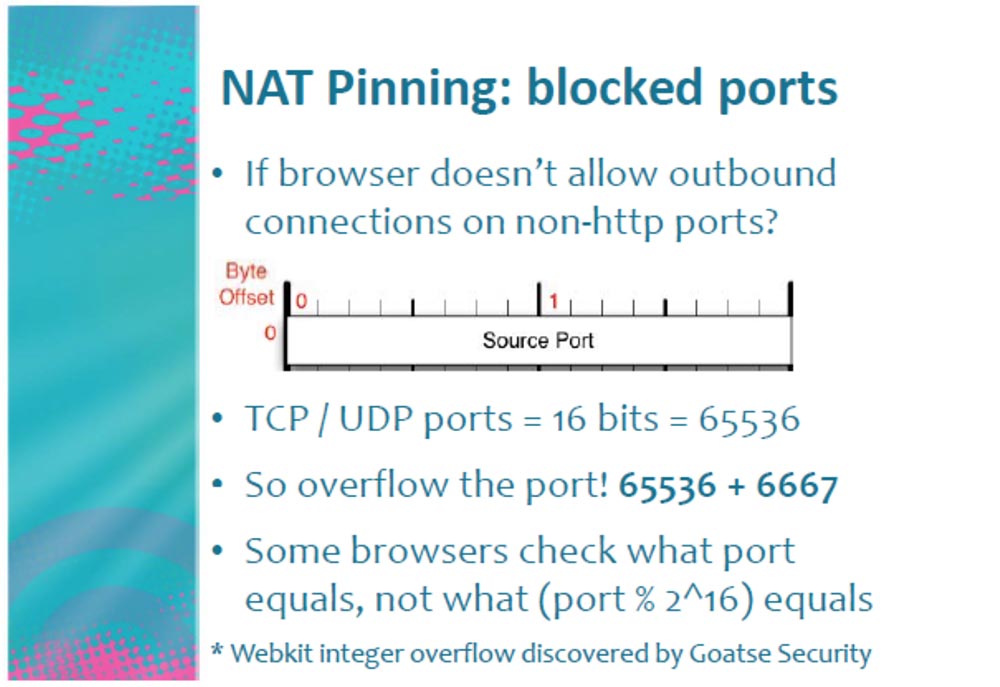
Suppose the browser says that it does not allow connection to port 6667, then we just overflow this port, adding another 16-bit port to it, that is 65536! As a result, the browser sees that this is not port 6667 at all, but port (6667 + 65536) = 72203, and sends data to the TCP stack at this address.
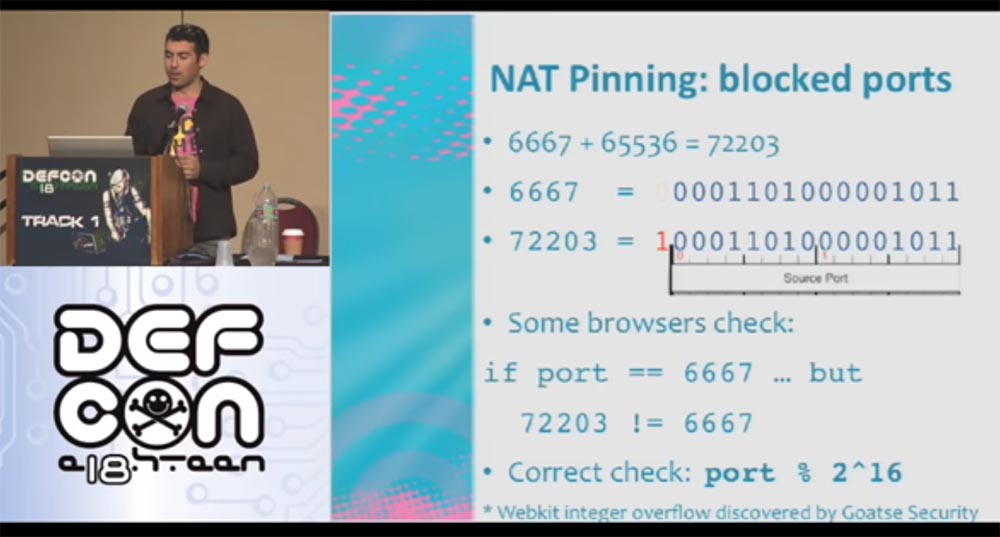
A port congestion tool called Webkit Integer was developed by the Goatse Security team, for which we are very grateful.
So, if Anna responded to my call and followed my link, I will attack her ports. After I joined port 80, it turned out that she had her own web server with her site about the Jacob 66 team from the Twilight series, that's how smart she is!
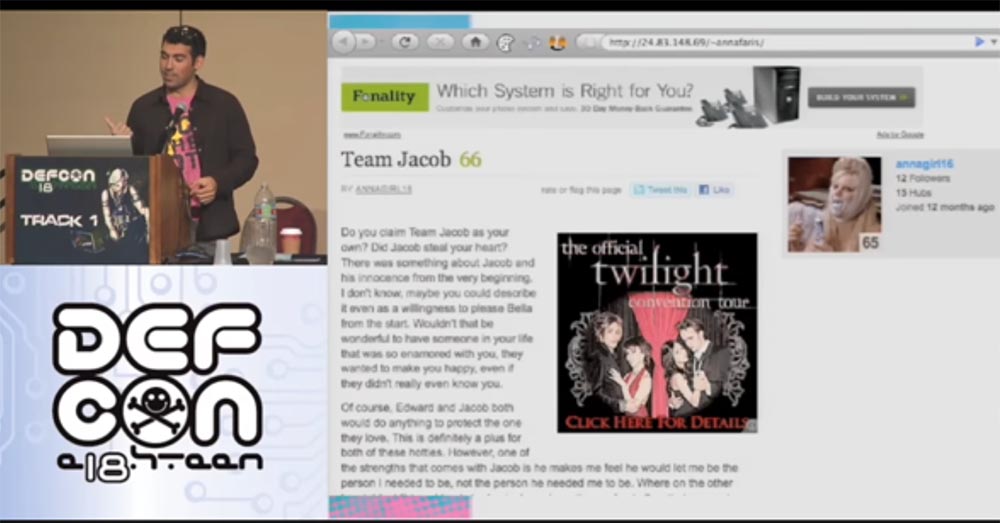
I also love Twilight and now I know how to conquer it! Actually, I belong to Edward’s team, but I won’t tell her about it. When we see her, I’ll tell her that I’m also in Jacob’s group!
It's time to consider how to protect yourself from NAT Pinning. There are several ways to do this. You can use a strict firewall that prohibits unknown outgoing connections.
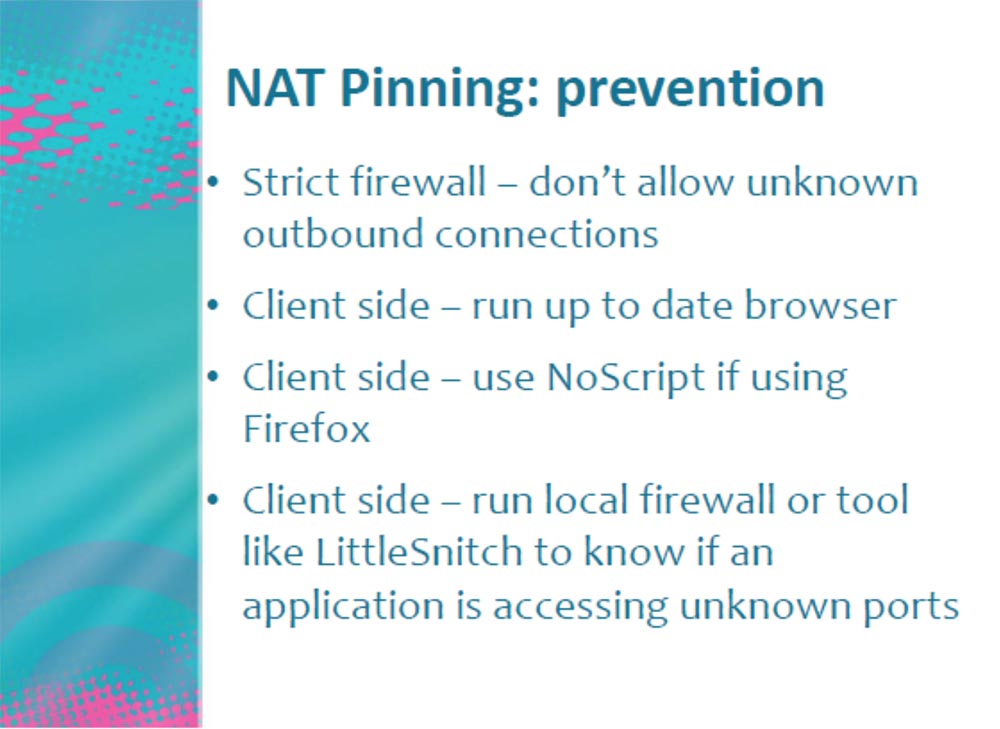
On the client side, you can use the most modern browser that has invulnerability, or enable NoScript mode when using the Firefox browser. In addition, the user can use a local firewall or tool such as LittleSnitch, which will notify you if an application tries to access an unknown port.
Consider what else can be done with our Anna. Let's try to determine its location. To do this, I, “Snake”, send her another message asking me to visit my friend Samy's page, my namb.la/twitter page.
Here I have an application called XXXSS for geolocation detection. When she visits my malicious site, this application scans her local network to determine which router is being used - its type, manufacturer, network provider, password and login to enter the network. It is very simple. I do not have access to her local network, but while her browser is on my malicious site, I can penetrate her network through her computer. I can connect directly through her IP address and get all the necessary permissions. I can also login using the login, determining the type and brand of the router. For example, for the Belkin router, there are default password tables and factory settings, that is, I can get everything that the provider has to remotely control the router. Having got control of the router, I remotely load Java Script into it.
Remote access uses AJAX, that is, the technology of accessing the server without reloading pages to capture the MAC address. Why do we need a MAC address and what does it contain that are interesting for us?
Google saves WiFi session data when you enter the network. And what does he remember in this data, which is transmitted when entering the Internet? The owner who logged in, that is, the MAC address of the device! In this case, this is the MAC address of your router. It also remembers the strength of the WiFi network signal when your device appears. And then our triple XXXSS, i.e. tripple XS / S, comes into effect. Suppose you are moving along a street in a car and the WiFi signal strength on your device is 10 out of 100, you turn to another street and it amplifies to 50 out of 100, on a parallel street it reaches 85 out of 100, and so on. Using the triangulation method, that is, the construction of serifs of signal strength on Google maps, you can determine the location of the strongest signal. This is where your computer will be located, that is, your home.
The Firefox browser has an extension called the Location Service. You can run a script that will force Firefox to go to Google and determine where my MAC address is coming from. He sends a request to Google HTTP with a request to tell him where this information came from.
Thus, when you visit my site, I use my XXXSS, get your MAC address, pass it off as my own and use my browser (I no longer need your browser) to get your coordinates on the map. All I needed for this was an exploit running on your router.
Do you know what I got as a result of these manipulations? That the Anne Faris router is 30 feet away from me. This is the accuracy of determining geolocation - 30 feet. I think Mark Zuckerberg said this better than me: "Privacy is dead!"
Thank you for attention.
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a 30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to Build Infrastructure Bldg. class using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?
