2017 Cyber Attack Survey: 47% of attacks target company infrastructure
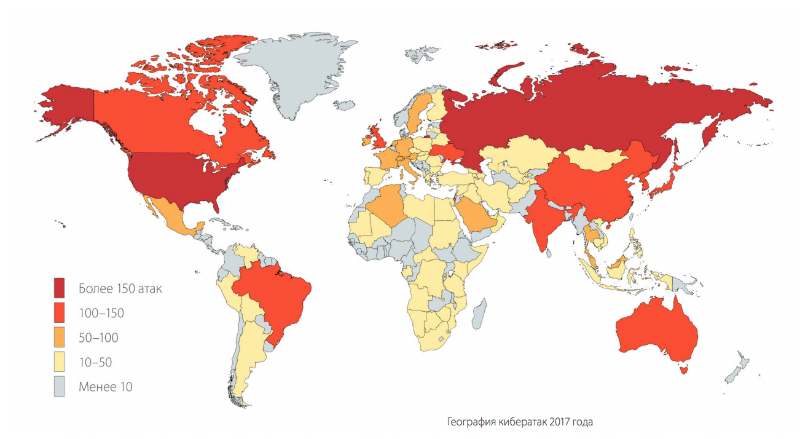
According to statistics compiled by Positive Technologies experts , the most frequent objects of attacks in 2017 were the infrastructure and web resources of companies, and among the main trends of the year, experts call encryption trojans, the development of the cyber services market, attacks on banks, cryptocurrency exchanges and ICOs.
The main trend of 2017, undoubtedly, became encryption trojans. Moreover, as an analysis of the behavior of attackers throughout the year showed, the problem is not so much ransomware, but viruses that irrevocably encrypt data, thereby causing enormous damage to the infrastructure of companies.
While some are infected with "malware", others are setting up their production. Due to the active promotion of ransomware as a service, the same trojans began to be reused by different people, and the threshold for entering the cybercriminal business is reduced, since anyone can now buy malware via the Internet. This means that the number of malicious campaigns will only increase.
Throughout 2017, the number of casualties among ordinary users grew: while in the first quarter Positive Technologies analysts counted 21 unique incidents that resulted in private injuries, by the end of the year their number was close to 100. The company's experts also associate this fact with popularity ransomware as a service, since newcomers to the cybercriminal environment who are looking for quick money most often send purchased trojans specifically to individuals. It is also worth noting that in 2017, the most interesting for attackers in principle was precisely ordinary users: this is 26% of all attacks.
The main motives of the attackers in 2017 were obtaining direct financial gain (70%) and data theft (26%). The most stolen data was medical information and payment card data. At the same time, as experts say, although the attackers continue to be interested in personal data, they are no longer valued on the darknet as much as before.
The hype surrounding cryptocurrencies in 2017 and the significant increase in the popularity of ICOs have also attracted attackers who targeted attacks on cryptocurrency exchanges, private wallets and ICOs. And while some registered crypto-wallets and transferred money to them, others emptied these wallets, for example, by selecting credentials.
The rapidly growing market for “smart things” did not go unnoticed by cybercriminals. Compromise of credentials from IoT devices has led to the fact that millions of routers, IP cameras, and vacuum cleaners and other utensils are in botnets and are used for mining cryptocurrencies, tracking people, DDoS attacks and more.
During 2017, we saw an increase in the popularity of large-scale malicious attacks: if in the first half of the year the shares of mass and targeted attacks were approximately equal, then by the end of the year the majority were massive cyber attacks (57%). According to Positive Technologies analysts, such attacks will continue and evolve in the future. Moreover, they will be aimed not only at making a profit, but also at a destructive impact. Malicious software turns into a real weapon that can lead to devastating consequences. If companies do not take the necessary protection measures, then new high-profile targeted attacks using specialized malware cannot be ruled out.
Active Directory (AD) is the main target of attackers during any attack on corporate information systems. Despite the strengthening of proactive defense systems, professional pentesters and attackers are finding new attack vectors on AD. Now is just another round of the game: security system manufacturers have learned to detect attacks like brute-force and pass-the-hash, and security researchers have developed a method for creating a golden ticket based on an NTLM hash. The appearance in January 2018 of DCShadow, a new technique for attacking AD, and the statement of the authors of the attack “SIEM will not help you” became a challenge for every Blue Team.
During the free webinar, which will be held on Thursday March 15 at 14:00Anton Tyurin, head of Positive Technologies attack detection methods research group, will tell you how modern Active Directory attacks work, how they can be detected in logs and network traffic, and what can be done to reduce the number of vectors. Target audience: employees of SOC, Blue Team and IT departments.
To participate in the webinar you need to register .
