MIT course "Computer Systems Security". Lecture 22: MIT Information Security, Part 3
- Transfer
- Tutorial
Massachusetts Institute of Technology. Lecture course # 6.858. "Security of computer systems". Nikolai Zeldovich, James Mykens. year 2014
Computer Systems Security is a course on the development and implementation of secure computer systems. Lectures cover threat models, attacks that compromise security, and security methods based on the latest scientific work. Topics include operating system (OS) security, capabilities, information flow control, language security, network protocols, hardware protection and security in web applications.
Lecture 1: “Introduction: threat models” Part 1 / Part 2 / Part 3
Lecture 2: “Controlling hacker attacks” Part 1 / Part 2 / Part 3
Lecture 3: “Buffer overflow: exploits and protection” Part 1 /Part 2 / Part 3
Lecture 4: “Privilege Separation” Part 1 / Part 2 / Part 3
Lecture 5: “Where Security System Errors Come From” Part 1 / Part 2
Lecture 6: “Capabilities” Part 1 / Part 2 / Part 3
Lecture 7: “Native Client Sandbox” Part 1 / Part 2 / Part 3
Lecture 8: “Network Security Model” Part 1 / Part 2 / Part 3
Lecture 9: “Web Application Security” Part 1 / Part 2/ Part 3
Lecture 10: “Symbolic execution” Part 1 / Part 2 / Part 3
Lecture 11: “Ur / Web programming language” Part 1 / Part 2 / Part 3
Lecture 12: “Network security” Part 1 / Part 2 / Part 3
Lecture 13: “Network Protocols” Part 1 / Part 2 / Part 3
Lecture 14: “SSL and HTTPS” Part 1 / Part 2 / Part 3
Lecture 15: “Medical Software” Part 1 / Part 2/ Part 3
Lecture 16: "Attacks through the side channel" Part 1 / Part 2 / Part 3
Lecture 17: "User Authentication" Part 1 / Part 2 / Part 3
Lecture 18: "Private Internet Browsing" Part 1 / Part 2 / Part 3
Lecture 19: “Anonymous Networks” Part 1 / Part 2 / Part 3
Lecture 20: “Mobile Phone Security” Part 1 / Part 2 / Part 3
Lecture 21: “Data Tracking” Part 1 /Part 2 / Part 3
Lecture 22: "MIT Information Security" Part 1 / Part 2 / Part 3
The next slide shows the message from Gizmodo, this is what I call trolling. From the direction of the attackers, it looked a bit evasive, no matter how many. Here they tell the whole world how they hacked our network, practically the day after it happened.
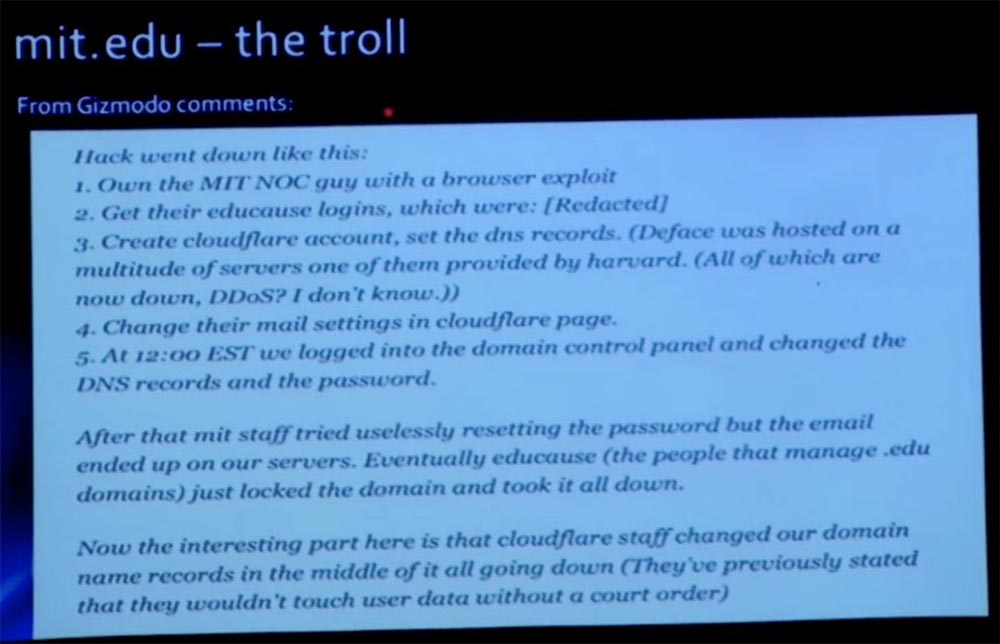
However, as soon as we realized that it was not MIT or anything that had been hacked into our mit.net network, but our registrar, we immediately contacted him, changed our records and blocked everything. However, there was some time in the DNS for some time, some of which exist for hours, so after taking action, we still observed some traffic flow. And while we were trying to eliminate the consequences of the attack, hackers publish such comments on Gizmodo: “They captured a guy from the network control center using a browser exploit”. Boyfriend “We got their training logins that were blah blah blah,” and so on. That is, the attack vector was supposedly a guy from the MIT NOC network control center.
Mark swore that it was not him. In fact, he did not swear, but explained that he was not compromised in any way. Therefore, after the incident, we published the truth about how the attack was actually organized. This link is www.exploit-db.com/papers/25306still valid if you want to read about it. In fact, hackers hacked into the registrar account of our domain EDUCAUSE. It turns out that every DNS account has been compromised. We do not know how long the hackers owned this data before they decided to use it to attack MIT. There was no fault of our institute in the incident. Later, in 2013, the registrar admitted his mistake of providing access to the top-level domain, and we all had to change passwords, since about 7,000 domain names mit.edu were compromised.
As a result, we have blocked our domain account so that it cannot be changed, but you know that if you tick the box "locked", which does not allow people to update the system, it is not very good. In any case, they fixed their system. So, this was not our fault, but such an attack was interesting in the sense that it showed how some of the basic Internet protocols could be used to attack.
So, the current threat landscape consists of two components: social attacks and network-based attacks. Social attacks can be characterized with the motto: “If you cannot use silicon, use carbon”! In other words, if you were unable to penetrate the victim's “iron”, hack the user through his keyboard. This is what is now observed especially often.
Based on my own 20 years of experience, I can say that network attacks that remotely use hosts do not happen often. Computer systems are becoming increasingly secure, at least outside. You know, in the old days, maybe ten years ago, Windows, Solaris, and Linux were sold with all their services, and I said that they glowed like a Christmas tree. Everything was included, because of the two criteria - convenience and security - they chose convenience, they wanted the user to get everything out of the box.

Now, I think we have found a reasonable compromise. When you install a "fresh" operating system, it starts a host-based firewall and there are no publicly available services. We have such things as Windows update and Apple update, there are package managers in all Linux distributions, so the OS out of the box, having access to the Internet, will quickly update to the current version. Now you do not have these ancient boxes with ancient services open to the whole world.
So, I tend to the fact that hackers climbed up the stack, perhaps on the eighth or ninth level. Now they deal more with people than with computers. And they try to use human weaknesses or weaknesses, such as fear, greed, gullibility, sociability, to take advantage of the rights of a legitimate user and gain access to applications or privileged access to the system. Instead of using hosts, they use people.
Recently on campus, we witnessed events called “targeted phishing.” I don't want to scare anyone. Manifestations of these attacks were observed in educational institutions throughout the country. This is a very serious threat, so we had to hurry to solve this problem, but MIT did not have to deal with such attacks directly. Targeted phishing is targeted at a specific community and uses believable messages. In the usual spam or phishing attacker, the attacker simply massively sends messages over the Internet, throwing a spammer network to catch people who, for some strange reason, may respond to these messages.
However, when targeted phishing, attackers narrow their network and find a community that believes in the credibility of the message received, for example, the Bank of America customer community or the MIT student, staff and faculty community. In this case, they were able to select communities of various institutions. For example, Boston University was one such community. Attackers attack the community with bogus e-mail messages pointing to a fictitious authentication site. A certain percentage of users clicked on the link and logged in, which, of course, provided the attacker with credentials. Then the attacker went to the real site and redirected the savings of these users to his account. The amount of damage was not reported, but I think it was big.
How can you deal with this? This is largely a problem of the ignorance of the user, so it is necessary to inform the community about this type of fraud. Just tell people that they don’t have to trust email and they’ll have to check links before clicking on them. However, from the experience and knowledge of human nature it follows that there will always be a certain percentage of users who ignore this warning and click where it does not follow, and I am just amazed by this. You can imagine that my mailbox is the recipient of all phishing emails addressed to members of my family. I receive mail from my father, from my sister, and sometimes it is difficult to determine its authenticity, so you should always pay attention to the address of the sender of the letters.
At present, many email clients do not like to show you a link to their address, which is very annoying, so that it becomes more difficult to identify the sender of the letter.

In my opinion, the root of the problem is that passwords are just dead technology. It is based on what you know - this is a password; what you are is biometrics; and on what you own is a token. The man-in-the-middle attack simply steals what you know, that is, the password. But if you can add something to it, it will stop the attack half way, and hackers will not be able to compromise your identity.
In the near future, we will launch a second authentication factor that will be tied to IDP Touchstone. You can familiarize yourself with the early access to this function if you visit duo.mit.edu, where we use a vendor called Duo Security. This is a two-factor authentication cloud system that is used in many educational institutions. The principle of operation is that you register your phone as the second factor and use a small mobile application for it. If you do not have a smartphone, you can authenticate using SMS, that is, the system will send you a message with a number. You can also create lists of 10 one-time passwords. In the near future, we will provide this system to the MIT community, at the moment it is fully functional, but not yet announced.
If you want to go to duo.mit.edu, you can select your phone and include the Touchstone user ID. Now I will show you a short demo about how the integration into the system takes place. The beauty of using standards and federated systems like SAML and Shibboleth, which are at the heart of Touchstone, is that we can easily lay down additional authentication factors. I intend to simply go to the tool that I use, and that will visually authenticate my Touchstone authentication with my certificate.
Now I use the address atlas.mit.edu. So, here is my usual Touchstone login, I’ll click Continue and get another invitation.
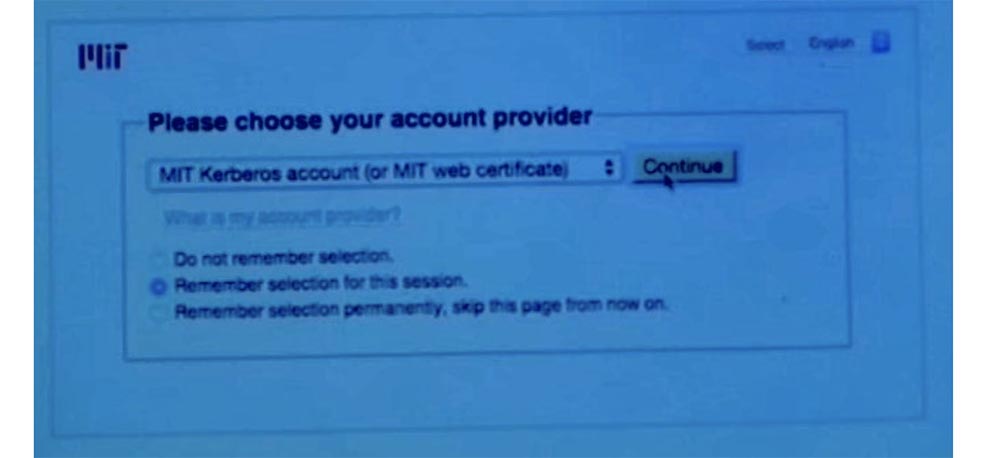
Unfortunately, it seems that I can not connect to Wi-Fi. Well, let's leave the demo for later, later we will edit the videotape of this lecture (audience laughter).
I did not rehearse this demo, so it happened. But trust me, it works. If you enter through the Duo, you can register, and all your interactions with Touchstone will now be two-factor. With this authentication scheme, you will be completely safe. It really works well.
Another threat that we have faced in the past few months is also targeted phishing, not only from educational institutions, but from people all over the country. We call this "police ID spoofing." And this kind of fraud goes beyond the digital world. The scam is that members of the MIT community are called from a police station located near their hometown. Police officers give them bad news. They say that you will soon be charged with tax fraud, or report that an accident has happened to your relative and offer to solve the problem for a certain amount.
Of course, in reality there is nothing of this. The call comes from an attacker who uses an outgoing call spoofing by using a fake ANI and SIP phone number, which is configured so that the received call trusts any information located in the "From" field, regardless of which number the call actually came from.
Mark Silis: The attacker signs up for a cheap SIP service, sets the phone number of a Lexington police station in his field, and sends you a message. This service is called “SIP-telephony numbers with substitution”. As soon as the call reaches the transcoding gateway, which turns it back into traditional telephony, the program says that everything is in order - this is the correct number, and we will show it to the user.

David Laporte: so you end up getting a call with very bad news from a place that you think is a police station. Again, criminals exploit human weakness. In this case, it is probably fear.
Mark Silis: or guilt.
David Laporte: Yes, if you did not break the law (laughs). But in any case, the essence of all calls comes down to the fact that you have to pay for something, although this may seem like a fraud. But if they say that my wife got into a car accident, I will not be able to calmly assess the situation and believe any absurd information that I can be told.
We had several people on campus who received such calls. I don't think they paid, but they were the targets of this attack. Again, this is not only ours. If you search Google for information, you’ll find messages about such calls in Pittsburgh newspapers and across the country.
But then again, this is a target phishing attack, right? They figure out where you live by just googling your name or by looking at a list of students or MIT employees, and find out some details about you. They just need to be plausible enough, after which they will call you, scare and engage in extortion.
In this case, mitigation is difficult because the telephone system is involved, which includes several “bridges”, which makes it extremely difficult to determine the real source of the call. Honestly, I am not a telephone guy, and for me this system consists of a lot of things that I will simply give up. But law enforcement agencies must be involved. You should contact your ISP to track these scammers along with the law enforcement agencies.
 \
\ There is one more thing regarding targeted phishing via e-mail. Some people call it "whaling" - it is a targeted attack on the top management of the organization.
I ran into this elsewhere, but we also experienced similar attacks here.
Attackers sent targeted messages to MIT executives using employee lists for greater likelihood of information. Being insufficiently attentive, the victims reacted to such messages. For example, an acquaintance asked for money to be transferred to him, and the real person on whose behalf the letter came was not aware of him. By agreeing, the victim sent money to someone on the other side of the country or on the other side of the world. So we also experienced this.
In short, be aware - SMTP is not a reliable protocol. With it, you can not check anything. So treat everything with distrust.
Mark Silis: are you going to tell them our story?
David Laporte: no, let's get you better!
Mark silis: well, it happened recently, I will not go into details and disclose names in order to preserve anonymity. So, one of the representatives of the MIT top administration reaches out to me and says: “Hey, I received this letter. It was from a high-ranking leader who asked me for help and asked me to transfer some money to him. I answered him, but he said that he did not know what I was talking about. How could this happen? Has someone hacked my email account? ”
According to Dave, people cannot imagine that email can be somehow forged without hacking into their mailbox, because this is a trust relationship.
It turns out it was someone's internet cafe in Nigeria or something like that. The attacker simply got acquainted with the organizational structure of MIT, found the senior executive director, found someone in the office of the vice-president for finance and wrote: “Hey, I need you to help me with this bank transfer, here is the account number”. Such things happen every day. Obviously, our employee has not transferred any money.
David Laporte: Was the letter absolutely believable?
Mark Sailis: yes.
David Laporte: I've already seen it.
Mark Sailis: even the tone of the letter and everything else seemed very believable.
David Laporte: Yes.

Mark Sailis:in fact, the attacker took the e-mail messages written by the senior manager for publicly accessible websites as a basis, because they send notes to the community and the like, which use exactly the same style, introduction and ending messages. Even the language and terms they used were identical. It was a material that the attacker turned to his advantage. Even I was surprised how plausible this message looked.
David Laporte: fortunately, the employee who was asked about it, took this message as extraordinary, although it looked quite plausible and decided to contact those whom he considered the sender of the letter, thanks to which the fraudulent scheme was revealed. However, things could not happen so quickly.
Therefore, I mentioned that today, in my experience, the network attack vector is not as common as before. This year has been a year of serious exploit usage. First of all, they aimed at the cryptographic SSL protocol and used its Heartbleed error, Microsoft's critical SChannel error and POODLE vulnerability in the implementation of open SSL v.3.
SSL is a security service, so when you openly provide your service, you start SSL. Thus, we had a lot of services vulnerable to such attacks. Shellshock was one of the attacks affecting the Bash shell, which allowed an attacker to remotely use the system. All this is a kind of “gold standard” for network exploits. They can be used remotely with administrative privileges. In this sense, the passing year was rather unpleasant, because, in my opinion, there was a sort of overkill with exploits.
How do we cope with it? After all, our services are public, so they should be publicly available. We cannot simply isolate ourselves from the whole world, because our systems are vulnerable to some kind of threats.
First, you need to automatically fix and update software. Previously, the delay between the release day and the patch could be quite long, but now it is necessary to reduce the release time of the patches to several hours after the vulnerability has been identified. So when these things float to the surface, we can download updates, at least for the systems we support. To update systems that we don’t support, we can use our people from the Communications Office and Monique, who’s in charge of public relations, to send a message to the community on time or at least warn them that they really need a patch because vulnerability and continued use of the program is unsafe.

A more active threat mitigation option is scanning. The StealthWatch tool I have already mentioned pulls NetFlow data out of our network devices, so that we can get basic heuristic information. If we see that the external IP address is talking to several hundred users of the MIT system, this is probably not very good.
If there is nothing wrong with this, then we can create a white list of IP addresses. We did this for a lot of research projects and just things that are legal.
We have automated BGP zero routing, where we actually watch the flow. And if we see abnormal behavior, we will reset the route on the fly. This procedure occurs every 5 minutes, and as soon as the scan is started, we can detect any threat. Thus, with respect to Shellshock and some of the earlier SSL vulnerabilities that were truly deadly, we scanned the community and sent out lists to those whose contacts we had to report that the service was working on such an IP address, we found out about its vulnerability , so please patch this service. This is precisely the need to convey important information to the community as quickly as possible.
Future trends include the improvement of requirements for IT-sphere. I call them “future trends,” but this future is going on at MIT right now. For example, we have been dealing with BYOD for a long time, this is a common practice in educational institutions. However, the organization of work and training on the principle of BYOD complicates the application of security policies, because you cannot fully control a device that you did not buy.
Improving services at MIT is, for example, that we have a corporate agreement with Dropbox, and each student gets the right to store an unlimited amount of their data there. Unlimited storage on Dropbox is great, but is fraught with problems related to secure data storage. In our case, we made sure that these vaults are always under the jurisdiction of the United States, but what happens if you are dealing with a supplier who works abroad where other legislation is in force? What if a person places confidential information on DropBox, where does it sync to the cloud? Many people think that the information "lives" in the cloud, but we know that Dropbox is synchronized with the local system. There are many problems here, because IT no longer manages Internet services,
The same goes for third-party email service providers. You can send confidential information through an email system that is not completely local. Thus, confidential data can leave the institution.
The use of cloud technologies is also associated with some problems. The Massachusetts Institute of Technology never had a perimeter, like most of the rest of educational institutions in the world in our time. If you started a small startup, and I am sure that you have a lot of friends who participate in startups, then you know that none of them use only local resources. They use material that is completely in the cloud. It is impossible to build a perimeter of defense or separate itself from the outside world if the data is found in the web services of Amazon, Salesforce.com, Google Apps or Dropbox. Therefore, we need more advanced methods to deal with security issues. There are data leaks in the same way and authentication and authorization problems occur. As you can see
The use of such things as authentication using the SAML markup language is very convenient, because MIT is really a reliable SAML architecture. When we wanted to add Dropbox, it was easy enough to integrate this service provider into our Touchstone infrastructure.

I’m sure I idealize some things, but you know, in a great scheme based on standards and federated systems, things like SAML and Shibboleth really make life easier in the cloud world.
Another fashionable phrase is “the Internet of things”, but in mit.net we have been building such management systems everywhere. These are computer systems that are built by wonderful people who equipped air conditioning last year. In most cases, these systems are not protected. Mark has a story about how they just put these systems on mit.net in public access. Anyone in the world can research them. We have almost completed our building management systems and intend to use VRF, a technology that allows you to implement several virtual routers on the basis of one physical router, so that they have a completely different forwarding path. And we will combine all this with a firewall, providing full control over access.
But when we move into the world of the Internet of things, this problem will only multiply. What can happen if the light switches have IP addresses and, who knows, maybe even my shoes will get IP addresses? It will be just crazy, and to be honest, I do not have an answer yet, how we will cope with it.
Many companies say that they cope with it, and they make you spend a lot of money on the proposed solutions. All I can think of is to provide a policy for accessing devices based on 802.1 X, that is, when I authenticate or my device is authenticated, they can coexist on the same network, and yet not be as widely open to the world as, say, My notebook.
At this point I finish and now I can answer your questions.
Lecture hall:You missed one slide presentation, which was dedicated to the campus firewall.
David Laporte: I swear, I didn't do it on purpose! Let Mark tell you about it!
Mark Silis: as David has already noted, when you install software out of the box, be it Linux or Windows, you already have a firewall by default. All this Internet of things and a huge variety of devices on mit.net have a safer default position, so they do not have to be open to the entire public network.
But there are legitimate reasons why people want to have a device in a public network, and this is normal. You know, one of the good things about MIT is that if people want to do something, you let them do it. They can do it automatically. They can do it themselves. They do not need to ask about the policy of the institute in this area. They do not need to do anything like that.
So, we are trying to move to the network topology, in which people will by default be under some kind of protection. If they want to go to a publicly accessible webpage, they can do so without anyone's permission. This process is automated and takes 1-2 minutes. We are trying to simply extend the default security to what it can extend to the default. But at the same time, we recognize that our goal is to not disrupt the innovation activity that takes place here. And therefore, if students or teachers want to access a web page located on an external network, that’s their right.
Audience: What type of traffic is most commonly seen on the MIT network?
Mark Sailis:Looking at StealthWatch, I would say that 80% of our traffic uses the HTTP protocol.
David Laporte: And this traffic includes HTTP streaming media.
Mark Sailis: Yes, movies, media files. I think the interesting question you could ask is how much of this traffic relates to research activities (audience laughter). I know that you all study hard, I did the same, so I still work here. As Internet providers, we are philosophical about this. There was a time when many schools tried to figure out what kind of traffic was broadcast across campus networks, but MIT does not. We are confident that neither I nor anyone else in the administration is able to make a judgment about the value of someone else's Internet activity.
David Laporte:because people live here, and this is not only work. I mean, people do a lot of research on Netflix, because we have a Netflix cache, and a lot of traffic flows there. But we also have thousands of students and staff who live here, so at night they turn on their Netflix box and start streaming.
Mark Silis: or whatever it is, so we were always aware of what our traffic was. But I would say that a significant part of the traffic, even today, is just scary. At night, half of the video stream ...
Audience: will you allow torrent traffic?
Mark Sylis: Porn?
Audience: No, not porn, but torrents!
Mark Sailis:a, torrents. Do you know what's interesting? Porn and torrents are very similar (audience laughter). I heard "porn", do not think that it was a Freudian reservation. Interestingly, the torrent traffic dropped significantly. I would say that over the years everything went awry. On the positive side, most things are much more affordable for people, like Netflix or Amazon Prime, where you can subscribe to anything for $ 4 a month, and usually people do. Our students are offered free TV Comcast. If you want to watch IPTV, you can easily connect it to your computer. Perhaps that is why the number of downloads of torrents has decreased dramatically, and this is a pleasant surprise.
Nikolai Zeldovich: well, great, let's thank Dave and Mark!
David Laporte: thanks guys!
Mark Sylis: Thank you for your attention!
Full version of the course is available here .
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending to friends, 30% discount for Habr users on a unique analogue of the entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to share the server? (Options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps until spring for free if you pay for a period of six months, you can order here .
Dell R730xd 2 times cheaper? Only here2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to build an infrastructure building. class c using servers Dell R730xd E5-2650 v4 worth 9000 euros for a penny?
