Video instruction for Check Point Security CheckUP R80.10. Network Security Audit
- Tutorial
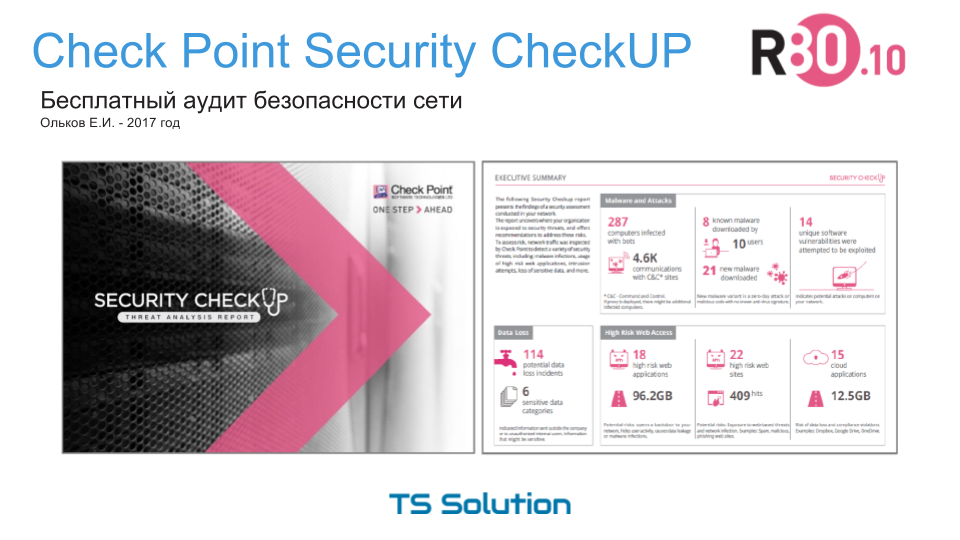
As we promised earlier, a detailed video instruction was prepared on how to independently conduct a network security audit using Check Point Security CheckUP R80.10 . Three parts were previously published:
However, using text and images is very difficult to create a detailed description. Especially for this, we have prepared a video instruction, which also consists of three parts:
1) Overview
2) Installation and initialization
3) Setting
I hope that this instruction will allow you not only to get to know the Check Point products more closely, but also to see the real security situation on your network. If during the testing you have questions, you can always contact us for help . You can find more Check Point material on our blog .
PS I would also like to thank RRC and Aleksey Matveev, as well as Aleksey Beloglazov from Check Point, for help in creating the instructions .
