The recently adopted 802.11ah Wi-Fi standard can bring back already forgotten security concerns.
As it was already mentioned on Habré , developers decided to please consumers with the new Wi-Fi protocol for the Internet of things. True, it is possible that to ensure safety in the process of using this product will be much more difficult than before.
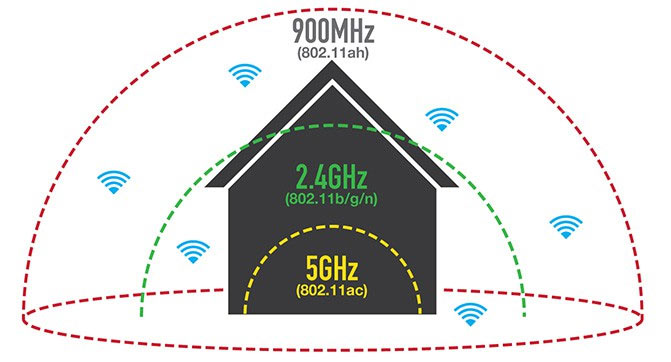
The new IEEE 802.11ah protocol is known in the Wi-Fi Alliance circles as the Wi-Fi HaLow. It differs from the currently used Wi-fi, which is typical for most modern devices, in several key characteristics. Firstly, it is a low-power protocol that will work in the range up to gigahertz. Secondly, the new product has a much greater range than traditional Wi-Fi, and it is thanks to this feature that it will be extremely effective in applications that regulate the operation of traffic lights and surveillance cameras in smart cities.
The new version of Wi-Fi can also be useful for connecting small, low-power gadgets, such as smart watches, fitness bracelets with other useful accessories and clothing items, for which Bluetooth is now being used. The Wi-Fi Alliance, which approves Wi-Fi-enabled devices and is testing a new development, assures that it is an extended and improved version of the existing protocol.
“HaLow Wi-Fi perfectly matches the unique needs of the Smart Home, Smart City and industrial markets due to its low energy consumption and the ability to work through walls. Moreover, the range of the protocol significantly exceeds the performance of modern Wi-Fi, ”said Edgar Figueroa, president and CEO of the Wi-Fi Alliance.
But, as with any new protocol or system, the introduction of Wi-Fi HaLow involves additional security challenges. One of the main problems in this context is to provide reliable protection for all versions of the protocol. Device manufacturers are used to resolving issues as they become available, and you have to deal with previously unknown vulnerabilities, which require hundreds and thousands of hours of work of security consultants to overcome. According to experts, Wi-Fi HaLow will not be an exception.
“While the standard protocol is good and safe, the launch of new versions by various vendors can cause certain security problems. This applies to all protocols, ”said Caesar Kerrudo, Technical Director of IOActive Labs, who conducted numerous studies on the security of various smart devices and the functioning of smart cities.
Many gadgets that are ready to work on the new protocol - will appear in the public domain, in the best case, in a few years - are produced by companies that do not pay enough attention to modeling potential threats, possible attacks, as well as other issues that hardware and software developers have it’s not the first ten years. But the attackers are at hand.
"While the standard protocol is good and safe, launching new versions of it by various vendors can cause certain security problems."
Kerrudo is confident that HaLow’s increased Wi-Fi range can also play a trick.
“A solid range implies that criminals will have the opportunity to attack from a decent distance. So, for example, you may be the victim of a hacker using gadgets from a friend who lives through three or more houses. And, much worse, if the new standard becomes generally accepted and appears in smart homes, smart cities and smartphones, a golden age will begin for hackers, because they will be able to hack anything they want, being very far from the crime scene, ”Kerrudo warns.
“For example, if an attacker in China wants to hack smart homes and cities in the United States, it will be enough for him to access several smartphones in the United States, and with their help manage the functions of the respective buildings and settlements.”
The emergence of new versions of a technology makes you think about additional aspects of security and confidentiality, and this trend also applies to the distribution of devices not related to computing operations. The concept of voice control of climate control, entertainment complexes and other systems at home has become a reality, as well as the ability to send e-mail from the
“Nothing new, you say, but until recently we did not have various technologies (protocols) designed for use in smart homes, cities, etc. When all these elements are interconnected and they use the same technology, the field of activity of attackers increases significantly, ”summarizes Kerrudo.
In honor of the fact that the total network capacity of the Dutch data center in which we provide services has reached 5 Tbps (58 points of presence, inclusion in 36 exchange points, in more than 20 countries and 4,213 peer-to-peer inclusions), we offer dedicated servers for rent at incredibly low prices.
