Critical vulnerability in Grub2 bootloader allows to bypass password protection

Security researchers Hector Marco and Ismael Ripoll posted information about their 0-day vulnerability in the popular Grub2 bootloader, which is used on most Linux systems. Exploitation of the vulnerability allows access to the emergency console Grub2 bypassing the password. This, in turn, opens up the possibility for an attacker to conduct an attack aimed at increasing privileges in systems and access to all information.
Vulnerability Description
The integer overflow affects the bootloader functions grub_password_get () and grub_username_get (). Due to a check that was missed in the code, backspace is pressed 28 times and the memory is negatively erased with a negative offset. As a result, the stack memory is erased and the execution jumps to different addresses / offsets, which ultimately leads to execution retw instructions, and as a result of successful operation, the built-in shell starts up.
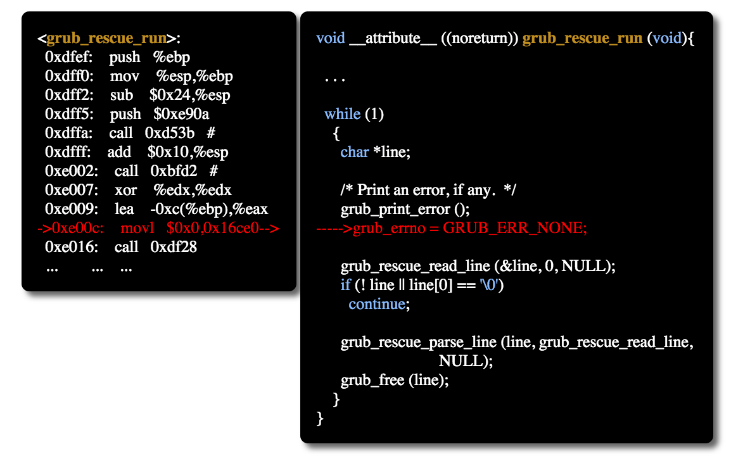
Researchers conducted a proof-of-concept demonstration exploiting an error in the grub_username_get () function - after pressing the Backspace key 28 times and once - pressing the Enter key, they gained access to the fully functional emergency console Grub2.
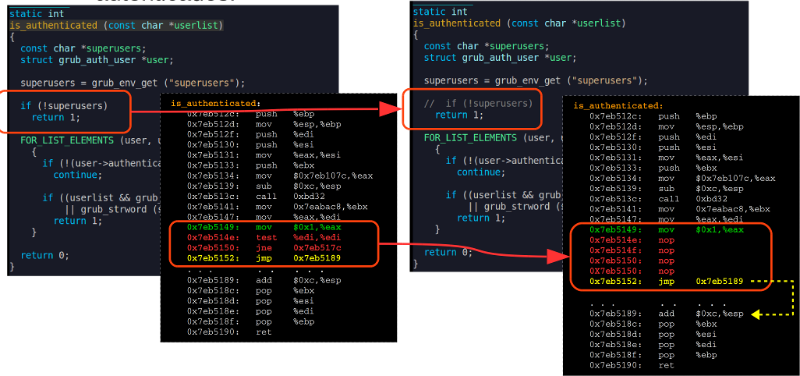
Moreover, Marco and Ripoll managed to gain full access to the operating system even though they did not have a real user password. To do this, they changed the working conditions of the is_authenticated () function, which verifies that the user has passed authentication - this can be done using the Grub2 write_word command:
What operation error may lead to
According to researchers, the discovered vulnerability can be used to conduct APT attacks, the purpose of which can be the theft of critical data. In order to gain access to information, attackers with access to a computer can take advantage of an error in Grub2's work to install malicious software on it.
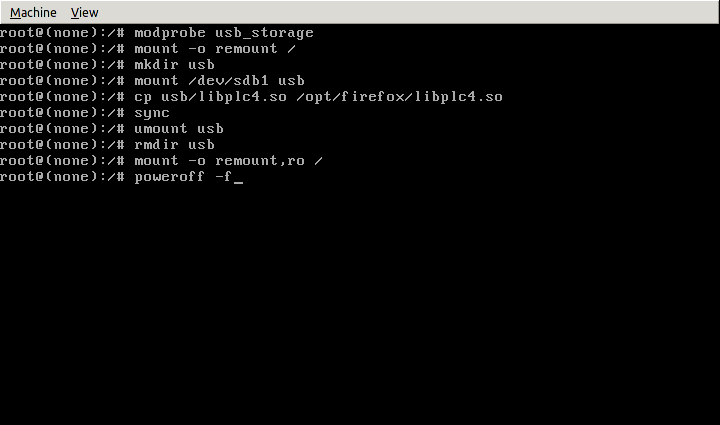
Marco and Ripoll also created a proof-of-concept demonstration of such an attack. To do this, a modified Firefox library libplc4.so was developed, which creates a new process and launches the management console on port 53. Then this library was written to a flash drive and copied to the victim computer, while the original library was replaced.
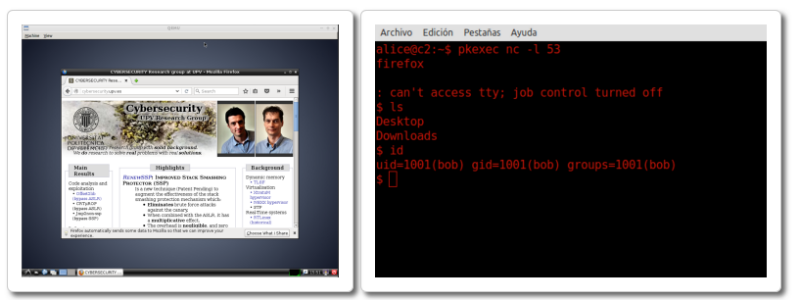
After the user starts Firefox, the management console will be activated, giving the attacker access to the user's data:
How to protect yourself
Vulnerable bootloader versions from 1.98 to 2.02. In order to check whether a particular system is exposed to the described vulnerability, it is necessary at the moment when Grub asks for the username, press the Backspace key 28 times, and then press Enter. If after that the computer restarts or the emergency console (rescue shell) starts, the system is vulnerable.
Researchers have notified major developers of Linux-based operating systems, as well as developed a patch that allows you to fix the error.
Note that a similar vulnerability was previously discovered in the Android mobile OS - it allowed to “pass through” the phone’s lock screen using a very long password. In addition, an error was discovered in the summer of 2015.in the security system of the Steam game store. An attacker could compromise the Steam user account due to incorrect operation of the password recovery function - the system took even an empty value as the correct code.
