Dangerous 0day vulnerability discovered in Adobe Flash Player
Yesterday, we wrote about the leak of confidential data from the Hacking Team cybergroup, which was subjected to large-scale hacking. The archive contained the source texts of several 0day exploits, including the LPE sandbox-escape exploit for Internet Explorer and the dangerous RCE + LPE exploit for the current version of Flash Player. The working version of the latter is already surfing the network and poses a very great danger to users, since the exploit is universal and allows you to remotely execute code in several browsers at once (current versions), including Google Chrome, Opera, MS Internet Explorer, and even MS Edge as part of Windows 10.

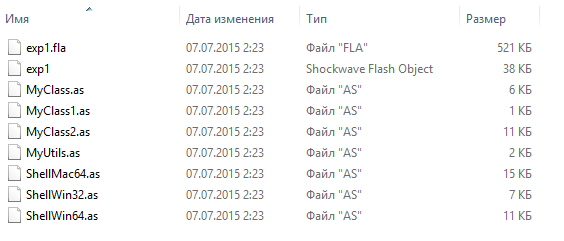
Fig. The source code of the exploit.
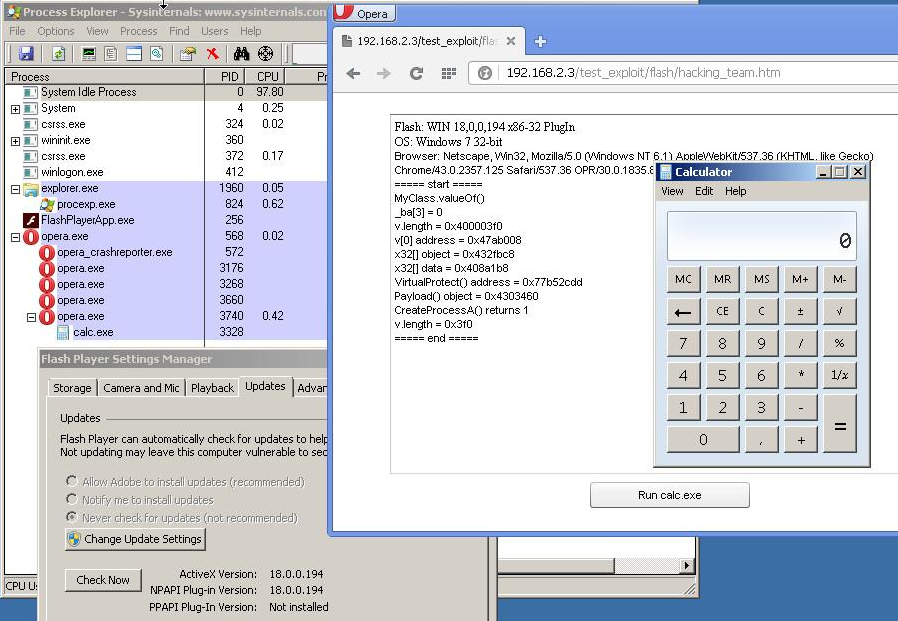
Fig. Demonstration of the success of the exploit for the Opera web browser on the 32-bit version of Windows 7.
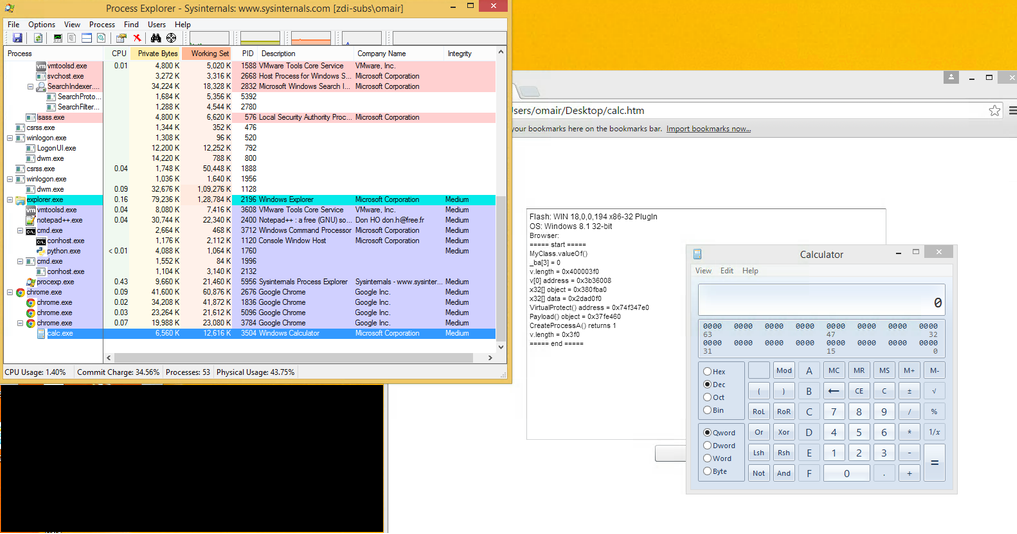
Fig. The same goes for Google Chrome. The source is here .
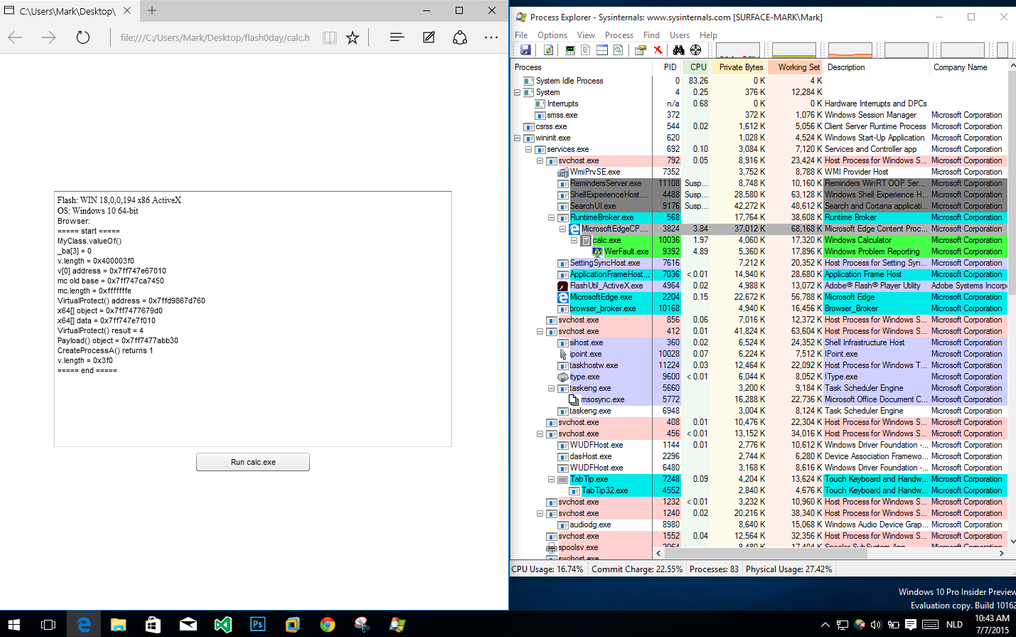
Fig. The exploit also works great on the latest MS Edge web browser on Windows 10 (build 10162).
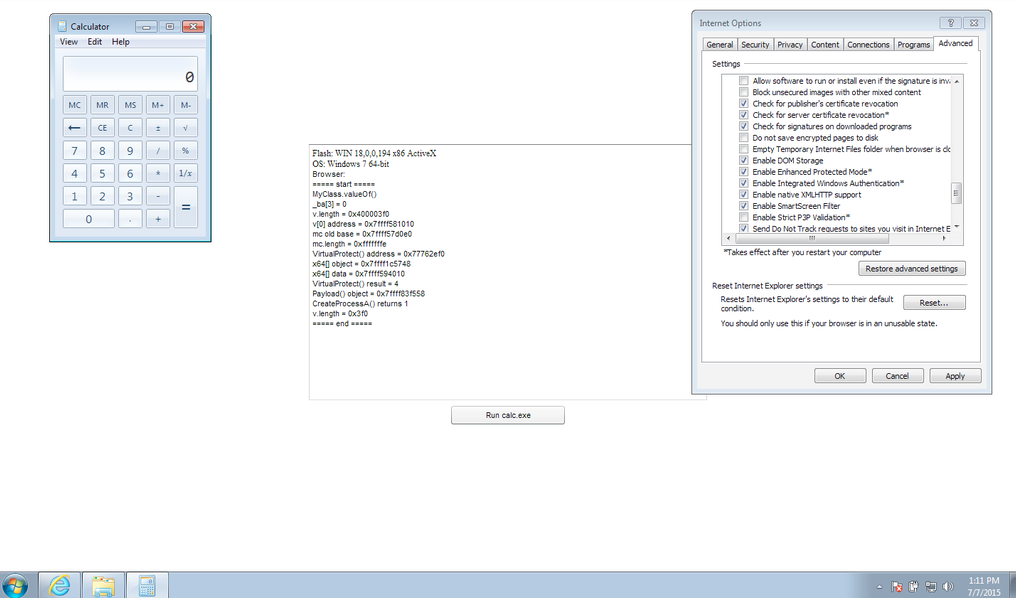
Fig. The exploit works fine for IE11 on the 64-bit up-to-date version of Windows 7 with EPM enabled .
In this case, the most dangerous development of the situation will be that this exploit can fall into one or more sets of exploits and will be used by attackers to organize drive-by attacks with automatic installation of malware.
We recommend that users disable Flash Player for the browser you are using before Adobe releases the corresponding patch. Instructions for this process can be found.here .
UPD: Symantec has also confirmed the relevance of this 0day exploit.
Leaked Flash zero day likely to be exploited by attackers
www.symantec.com/connect/blogs/leaked-flash-zero-day-likely-be-exploited-attackers
Users can use EMET to block the activity of this exploit.
www.kb.cert.org/vuls/id/561288
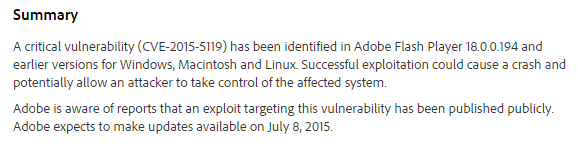
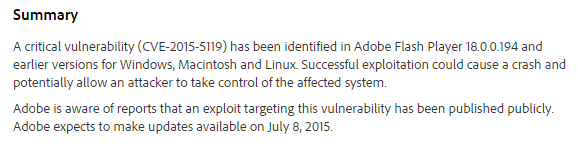
UPD1 : Vulnerabilities assigned identifier CVE-2015-5119 (Windows, Linux, OS X). See Security Advisory for Adobe Flash Player (APSA15-03)
helpx.adobe.com/security/products/flash-player/apsa15-03.html
UPD2: ESET antivirus products detect an exploit as SWF / Exploit.Agent.IG .
virusradar.com/en/update/info/11902

be secure.

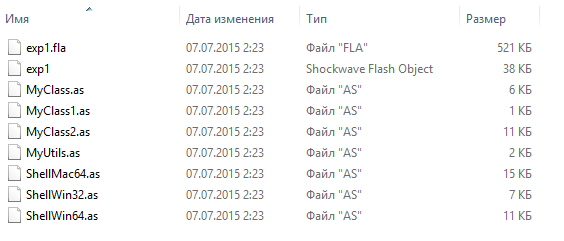
Fig. The source code of the exploit.
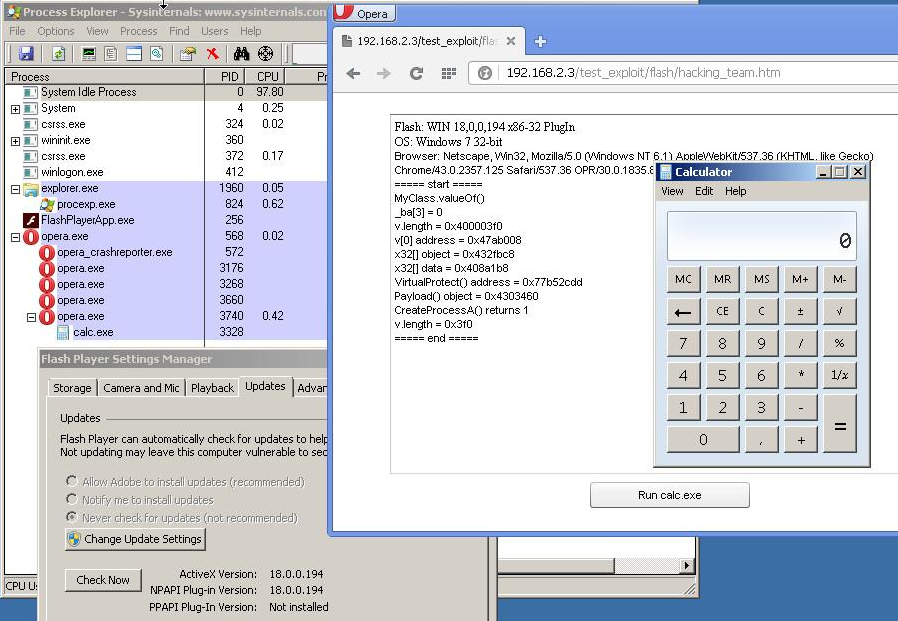
Fig. Demonstration of the success of the exploit for the Opera web browser on the 32-bit version of Windows 7.
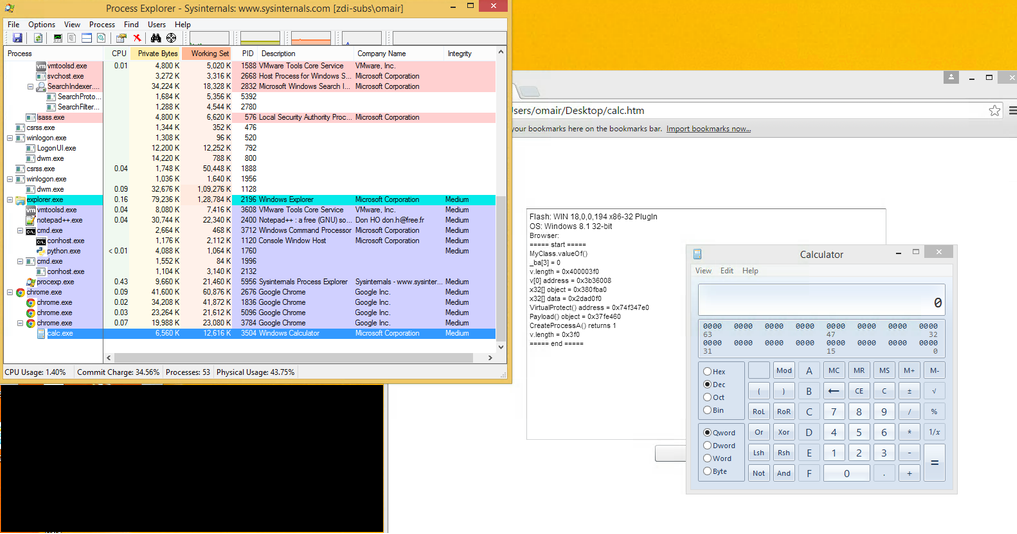
Fig. The same goes for Google Chrome. The source is here .
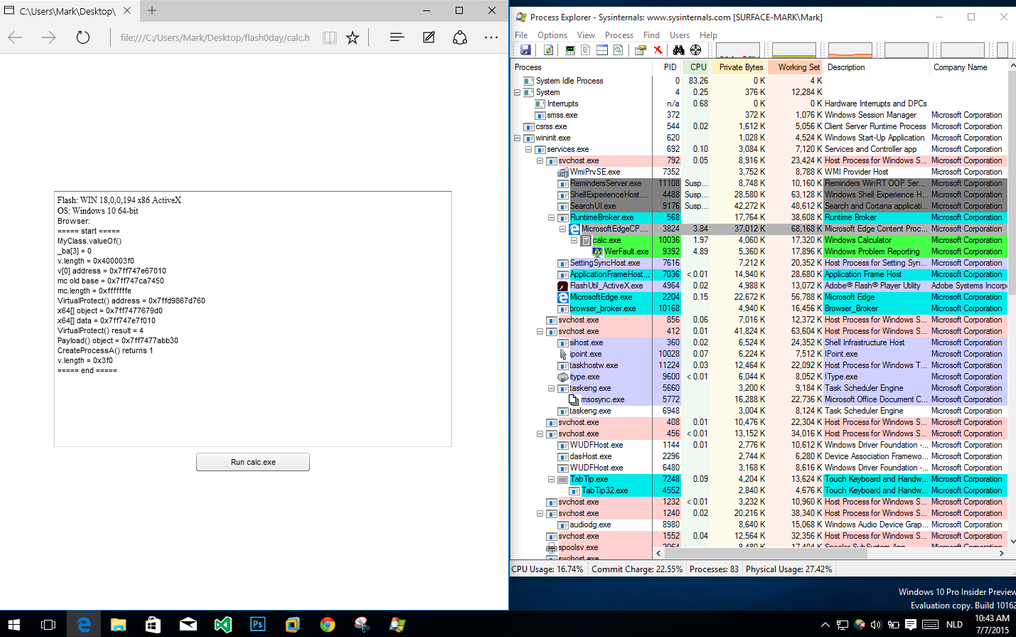
Fig. The exploit also works great on the latest MS Edge web browser on Windows 10 (build 10162).
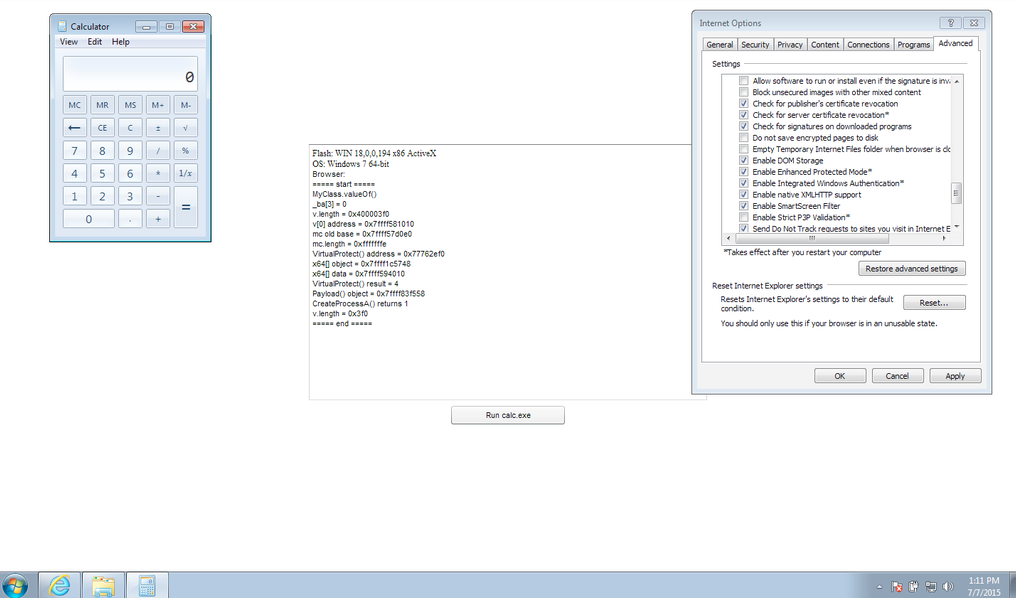
Fig. The exploit works fine for IE11 on the 64-bit up-to-date version of Windows 7 with EPM enabled .
In this case, the most dangerous development of the situation will be that this exploit can fall into one or more sets of exploits and will be used by attackers to organize drive-by attacks with automatic installation of malware.
We recommend that users disable Flash Player for the browser you are using before Adobe releases the corresponding patch. Instructions for this process can be found.here .
UPD: Symantec has also confirmed the relevance of this 0day exploit.
Leaked Flash zero day likely to be exploited by attackers
www.symantec.com/connect/blogs/leaked-flash-zero-day-likely-be-exploited-attackers
Users can use EMET to block the activity of this exploit.
www.kb.cert.org/vuls/id/561288
UPD1 : Vulnerabilities assigned identifier CVE-2015-5119 (Windows, Linux, OS X). See Security Advisory for Adobe Flash Player (APSA15-03)
helpx.adobe.com/security/products/flash-player/apsa15-03.html
UPD2: ESET antivirus products detect an exploit as SWF / Exploit.Agent.IG .
virusradar.com/en/update/info/11902

be secure.
