Google has decided to postpone encryption of data on Android by default
Google, which promised full-disk encryption by default on devices running its new Android OS Lollipop, is apparently backtracking. Ars Technica reports that new smartphones running Android L do not contain this option enabled by default. The technical requirements of the device (hardware requirements) for this OS were published only in January of this year, and from them it became clear that they are not talking about encrypting data by default.

Talk about encrypting data on devices began after a series of materials published in the media by a fugitive NSA specialist Edward Snowden, from which it became clear that intelligence agencies can access user information stored on the device. Such an operation can be carried out using various software and online services, while encrypting data on the device by default would greatly complicate the process of obtaining personal and other information on the device for special services.
In 2014, a statement by Google about encrypting data on a device by default was published in a number of leading media, including The Washington Post.
Encryption by default nevertheless appeared, but only on two models of devices that are released by Google itself - Nexus 6 & Nexus 9. Other Nexus devices that were able to upgrade to Lollipop no longer contain this option enabled by default, even in the case of a complete reset the device itself ( full reset ). The same applies to smartphones from other manufacturers that began to appear after the mentioned Nexus models, i.e., encryption on them is turned off.
The following Lollipop technical documentation contains the following information.
It can be seen that Google allows OEM suppliers to decide for themselves whether to enable this option by default for the device or not. The same was stated for a previous version of Android called KitKat, in fact, nothing has changed in this regard.
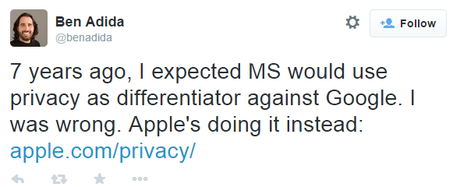
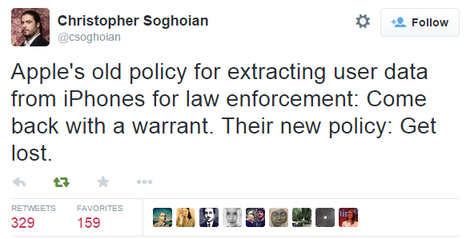
Recall that in September last year, Apple with the release of iOS 8 introduced an additional “NSA” protection feature that encrypts user’s personal data using the device’s unlock password ( passcode ).
Apple's .

Talk about encrypting data on devices began after a series of materials published in the media by a fugitive NSA specialist Edward Snowden, from which it became clear that intelligence agencies can access user information stored on the device. Such an operation can be carried out using various software and online services, while encrypting data on the device by default would greatly complicate the process of obtaining personal and other information on the device for special services.
In 2014, a statement by Google about encrypting data on a device by default was published in a number of leading media, including The Washington Post.
For over three years Android has offered encryption, and keys are not stored off of the device, so they cannot be shared with law enforcement. As part of our next Android release, encryption will be enabled by default out of the box, so you won't even have to think about turning it on.
Encryption by default nevertheless appeared, but only on two models of devices that are released by Google itself - Nexus 6 & Nexus 9. Other Nexus devices that were able to upgrade to Lollipop no longer contain this option enabled by default, even in the case of a complete reset the device itself ( full reset ). The same applies to smartphones from other manufacturers that began to appear after the mentioned Nexus models, i.e., encryption on them is turned off.
The following Lollipop technical documentation contains the following information.
9.9 Full-Disk Encryption
If the device implementation has a lock screen, the device MUST support full-disk encryption of the application private data (/ data patition) as well as the SD card partition if it is a permanent, non-removable part of the device. For devices supporting full-disk encryption, the full-disk encryption SHOULD be enabled all the time after the user has completed the out-of-box experience. While this requirement is stated as SHOULD for this version of the Android platform, it is very strongly RECOMMENDED as we expect this to change to MUST in the future versions of Android.
It can be seen that Google allows OEM suppliers to decide for themselves whether to enable this option by default for the device or not. The same was stated for a previous version of Android called KitKat, in fact, nothing has changed in this regard.
Recall that in September last year, Apple with the release of iOS 8 introduced an additional “NSA” protection feature that encrypts user’s personal data using the device’s unlock password ( passcode ).
On devices running iOS 8, your personal data such as photos, messages (including attachments), email, contacts, call history, iTunes content, notes, and reminders is placed under the protection of your passcode.
Apple's .