Zeus awarded maximum reward
Last year, we wrote that US law enforcement agencies wanted the author of the famous banking malware Zeus. Using this malware, hundreds of millions of dollars were stolen from bank accounts from users around the world, and the bot itself has long spawned a large number of its clones. Recently, the FBI has increased the reward for information leading to its capture to the amount of $ 3 million. This is the maximum reward that has ever been announced for the defendants in cyber affairs (cyber).
The defendant under the pseudonym "slavik" has been known in the underworld for a long time and is mentioned as the author of one of the earliest versions of Zeus. At the beginning of last year, we also wroteabout the capture by law enforcement officers of another cybercriminal. We are talking about the author of another banking Trojan program SpyEye under the pseudonym "Gribodemon". This bot was based on Zeus source code.
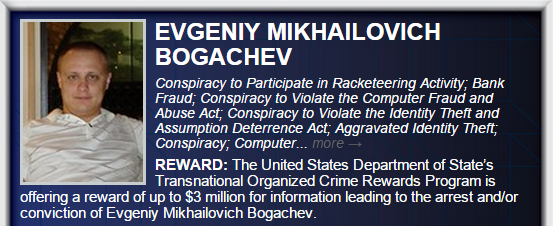
Fig. Orientation to the author Zeus from the site fbi.gov.
The story with Zeus has been going on for quite some time. The first versions of the bot were born in 2007 or even earlier. What distinguished Zeus from other malware was that it became the first crimeware toolkit or a full-featured tool to steal online banking data from various banks and transfer this information to an attacker’s server. To carry out such operations, it included a configuration file, which allowed attackers to quickly reorient it to the goals they needed (banking sites). Since then, several generations or versions of Zeus have appeared, the total financial damage from which is estimated at more than half a billion dollars. The number of different families or modifications of this malware and botnets based on it is already several dozen.
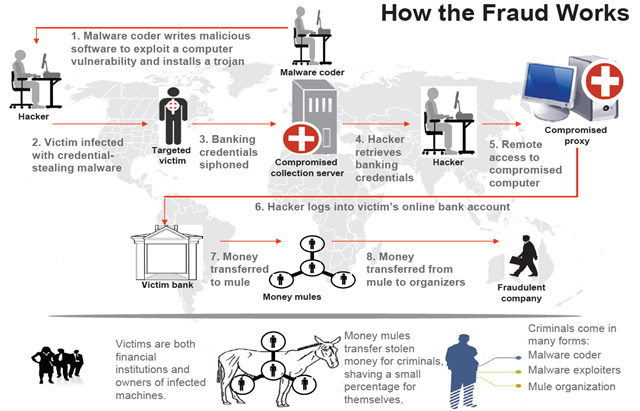
Fig. A typical scheme of work of cybercriminals who use banking malicious tools, including Zeus.
The defendant under the pseudonym "slavik" has been known in the underworld for a long time and is mentioned as the author of one of the earliest versions of Zeus. At the beginning of last year, we also wroteabout the capture by law enforcement officers of another cybercriminal. We are talking about the author of another banking Trojan program SpyEye under the pseudonym "Gribodemon". This bot was based on Zeus source code.
Fig. Orientation to the author Zeus from the site fbi.gov.
The story with Zeus has been going on for quite some time. The first versions of the bot were born in 2007 or even earlier. What distinguished Zeus from other malware was that it became the first crimeware toolkit or a full-featured tool to steal online banking data from various banks and transfer this information to an attacker’s server. To carry out such operations, it included a configuration file, which allowed attackers to quickly reorient it to the goals they needed (banking sites). Since then, several generations or versions of Zeus have appeared, the total financial damage from which is estimated at more than half a billion dollars. The number of different families or modifications of this malware and botnets based on it is already several dozen.
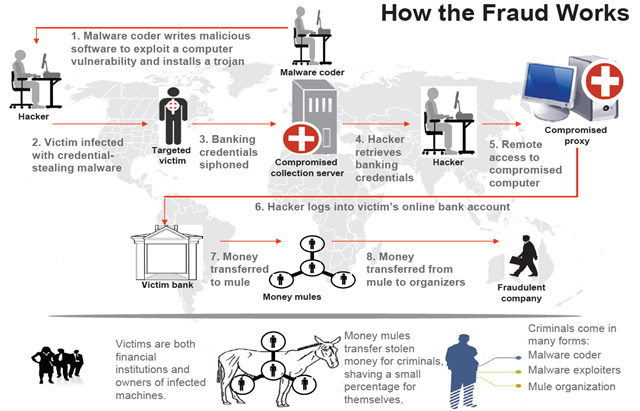
Fig. A typical scheme of work of cybercriminals who use banking malicious tools, including Zeus.
- The author of the trojan is developing the necessary functionality of the bot.
- The operator (hacker) is responsible for distributing the compiled executable files of the Trojan. He can use the services of spammers to organize spam mailings, to “ifremers” to redirect legitimate users of hacked sites to a trojan or other methods known in the cybercriminal world.
- The user becomes infected with a banking trojan, after which it uses a browser (in the process of which a malicious code is located) to work with online banking. The confidential data specified when working with the online banking system is sent to the attacker server.
- The operator (hacker) receives data sent by the bot in the previous step.
- The operator can use another compromised computer (proxy) to carry out fraudulent transactions with the victim’s account, thus hiding the source of the attack.
- Using the proxy specified in the previous paragraph, the operator logs into the user’s online banking account using the login / password pairs stolen at step 4.
- Funds from the victim's account are transferred to several fraudulent bank accounts in small portions, and then cashed out at ATMs by various persons involved in the criminal scheme (mules).
- The organizer (coordinator) of the entire criminal scheme receives funds from the "mules", while each of them "mules" gets its share.
