Vulnerability in WP-Slimstat 3.9.5 Plugin for WordPress
- Transfer
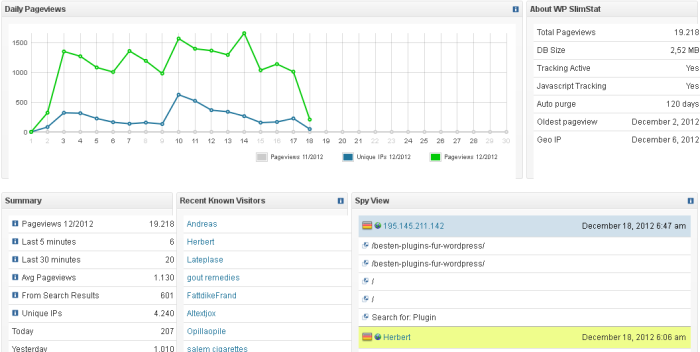
Users of the WP-Slimstat plugin version 3.9.5 and below should upgrade as quickly as possible! During the next security audit, we discovered a security error due to which an attacker could obtain the “secret” key of the plug-in and, thereby, perform SQL injection.
Successful implementation of this bug can lead to Blind SQL-Injection attacks, which allow an attacker to obtain data from the database, including the username, password hash, and in some configurations, WordPress secret keys (full control over the site).
WP-Slimstat uses a "secret" key to sign the data transferred from / to the client. Having looked at how this key is generated, we can conclude that it will not be difficult for an attacker to recognize it:

The hash from the time the plugin was installed is used as the “secret” key. An attacker can use such sites as, for example, Internet Archive to find out the approximate time for creating the site (after this there are approximately 30 million values to verify that it takes about 10 minutes for modern CPUs).
In order to be able to perform brute force, you only need to get valid and signed data from the plugin. They are easy to find in different fragments of the generated web pages:

At first glance, this may seem complicated, but looking at how this data structure is used in the plugin, you can follow a simple way of signing data and hashing a composite string consisting of payload and “secret” »Token:

Knowing this information, an attacker can brute force timestamps until he receives the same signature as the attacked site.
During the investigation, we were able to establish that we can transfer arbitrary data when unserialize () is called , which will be transferred to the maybe_insert_row () method later via the $ content_info variable :


Given that we control $ _data , we can add an associative array to it whose indices are SQL expressions, for example:
array(“1=sleep(100)–“=>”1″)This ability to fulfill any requests allows an attacker to get any data from the database. This is a dangerous vulnerability and you should update the plugin as quickly as possible.
