FBI: Sony attacked by hackers from North Korea
A few weeks ago it became known about a large-scale cyber attack on Sony (Sony Pictures Entertainment). As a result of the cyber attack, the attackers managed to gain access to several unreleased films, as well as private data of company employees. During the investigation of this incident, conducted by the FBI and FireEye, it was found that hackers were able to penetrate the company's internal computer network and install Destover malware (ESET: Win32 / NukeSped.A , Microsoft: Trojan: Win32 / NukeSped.A , Symantec: Backdoor.Destover) Due to the use of this family of malware in cyber attacks, the media reported so-called “Destructive attack”, since Destover specializes in destroying computer hard drive data.
Films stolen from Sony and other information, in particular, the data of company employees, were posted in the public domain. However, the company took quick steps to strip out many of these resources. Some archives with information managed to be at the disposal of krebsonsecurity .
The malware used in the cyber attack specializes in the complete destruction of computer hard drive data and is similar in function to malicious software called Wiper / Shamoon . Last year, Wiper was used for cyber attacks on organizations in South Korea.
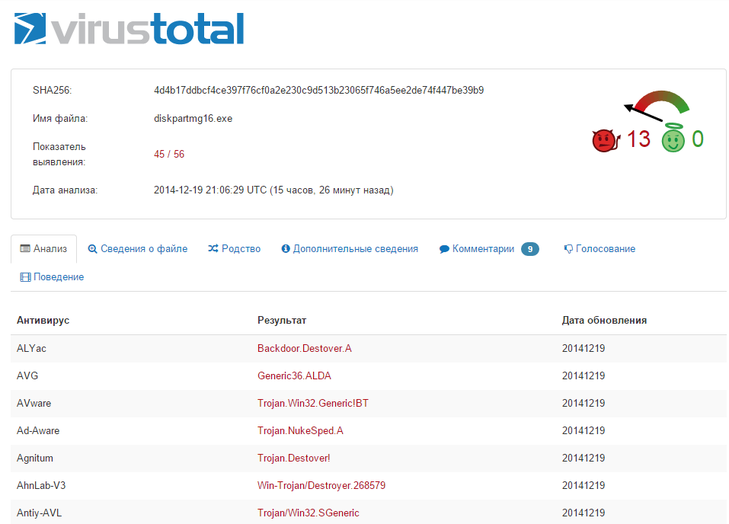
Fig. One of the executable malware files on VirusTotal has a high detection rate.
From the FBI report.
As a result of the investigation [of this incident ], which was carried out in collaboration with US government organizations, the FBI has enough information to conclude that the North Korean government is responsible for these actions [ cyber attack ]. So far, we cannot publish full information on this investigation because of the need to protect our sources, however, our findings are based on the following information:
Some additional information is in the krebsonsecurity report .
FBI National Press Office statement on Sony Pictures investigation: http://t.co/iGFpaBX1dq
- FBI (@FBI) December 19, 2014CrowdStrike says FBI conclusion matches own findings. Sony malware matches Silent Chollima (North Korean actor) in attacks tracing to '06
- Nicole Perlroth (@nicoleperlroth) December 19, 2014Films stolen from Sony and other information, in particular, the data of company employees, were posted in the public domain. However, the company took quick steps to strip out many of these resources. Some archives with information managed to be at the disposal of krebsonsecurity .
The malware used in the cyber attack specializes in the complete destruction of computer hard drive data and is similar in function to malicious software called Wiper / Shamoon . Last year, Wiper was used for cyber attacks on organizations in South Korea.
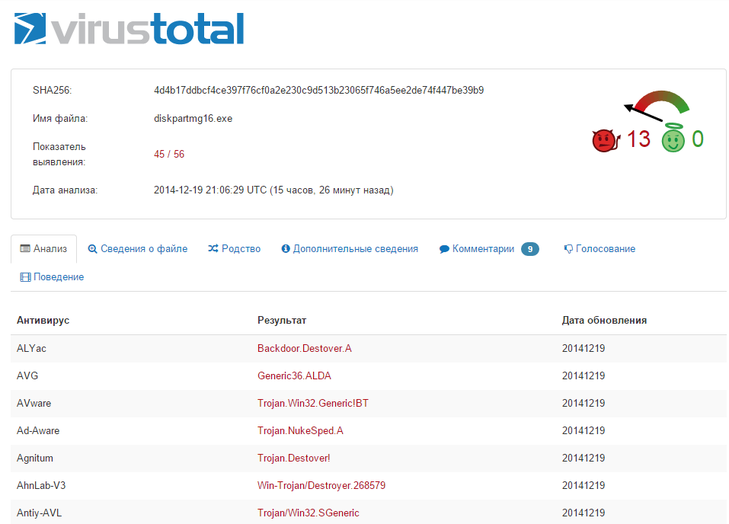
Fig. One of the executable malware files on VirusTotal has a high detection rate.
From the FBI report.
As a result of our investigation, and in close collaboration with other US government departments and agencies, the FBI now has enough information to conclude that the North Korean government is responsible for these actions. While the need to protect sensitive sources and methods precludes us from sharing all of this information, our conclusion is based, in part, on the following:
- Technical analysis of the data deletion malware used in this attack revealed links to other malware that the FBI knows North Korean actors previously developed. For example, there were similarities in specific lines of code, encryption algorithms, data deletion methods, and compromised networks.
- The FBI also observed significant overlap between the infrastructure used in this attack and other malicious cyber activity the US government has previously linked directly to North Korea. For example, the FBI discovered that several Internet protocol (IP) addresses associated with known North Korean infrastructure communicated with IP addresses that were hardcoded into the data deletion malware used in this attack.
- Separately, the tools used in the SPE attack have similarities to a cyber attack in March of last year against South Korean banks and media outlets, which was carried out by North Korea.
As a result of the investigation [of this incident ], which was carried out in collaboration with US government organizations, the FBI has enough information to conclude that the North Korean government is responsible for these actions [ cyber attack ]. So far, we cannot publish full information on this investigation because of the need to protect our sources, however, our findings are based on the following information:
- A technical analysis of the malware that was used in this attack to destroy hard drive data shows its similarity with other malware, which, according to the FBI, was developed by individuals from North Korea.
- The FBI also found significant similarities between the attacking infrastructure that was used in this cyber attack and the other that was used for cyber attacks against US government organizations and is owned by North Korea. For example, the FBI found that some IP addresses that belong to the infrastructure of North Korea interacted with computers that have IP addresses that are hardcoded into the malicious code [ Destover ].
- The software tools that were used in the attack on Sony have similarities with other tools that were used in cyber attacks on banks and media resources in South Korea in March last year. These attacks were carried out from North Korea.
FBI blames North Korea for Sony hack http://t.co/ONY8Sc92Dq <I look at some stuff the FBI doesn't discuss, NK's cyber skills, & takeaways
- briankrebs (@briankrebs) December 19, 2014Some additional information is in the krebsonsecurity report .
