IPv6 at gunpoint
It would seem, why now even remember about IPv6? Indeed, despite the fact that the last blocks of IPv4 addresses were handed out to regional registrars, the Internet works without any changes. The fact is that IPv6 first appeared in 1995, and its title was completely described in RFC in 1998. Why is it important? Yes, for the reason that it was developed without taking into account threats, with the same trust scheme as IPv4. And in the process of development, there were tasks to make a faster protocol with more addresses, and not more secure and secure.
Briefly about the growth rate
If you look at the charts provided by the regional registrar of IP addresses and autonomous systems, you can find that as of September 1, 2014, the number of registered IPv6 autonomous systems has already exceeded 20%. At first glance, this is a serious figure. But if we take into account only the real amount of IPv6 traffic in the world, now it is about 6% of all world Internet traffic, although literally three years ago it was only 0.5%.

Fig. 1. Actual volumes of IPv6 traffic
According to the most conservative estimates, by the end of 2015, the share of IPv6 traffic will reach at least 10%. And growth will continue. In addition, a special protocol for regional registrars has recently entered into force. Now a new block of IPv4 addresses will be issued only if the company proves that it has already implemented IPv6. Therefore, if someone needs a subnet of white IPv4 addresses, they will have to implement IPv6. This fact will also serve the further growth of IPv6 systems and increase traffic. As for ordinary users, providers have already begun to appear around the world that provide honest IPv6 addresses to end users. Therefore, IPv6 will be more and more common, and we cannot ignore this.
What's new in IPv6?
The first thing that catches your eye is the addresses. They have become longer, written in hexadecimal and difficult to remember. Although, after working with IPv6 for some time, you find that the addresses are generally memorable, especially if you use abbreviated forms of notation. Let me remind you that IPv4 uses 32-bit addresses, which limit the address space of 4,294,967,296 (2 ^ 32) to possible unique addresses. In the case of IPv6, 128 bits are already allocated to the address. Accordingly, 2 ^ 128 addresses are available. These are approximately 100 addresses for each atom on the surface of the Earth. That is, the addresses should be enough for a sufficiently long time.
Addresses are written as eight groups of hexadecimal values. For example, an IPv6 address might look like 2001: DB8: 11 :: 1. It is important to note that there can be several IPv6 addresses on one interface, and this is a standard situation. For example, the interface may have a private address, a white address, and another address will arrive via DHCPv6. And everything will work properly, for each task its own address will be used. If you need to go out into the world, then a white address will be used. It is necessary to the next server? Will go through a private address. All this will be solved by the usual analysis of the destination field.
All IPv6 addresses are divided into two groups: link-local and global unicast. By name, it is obvious that Link local is an address that is used only within a single link. Such addresses are further used for the operation of a number of mechanisms, such as automatic address setting, neighbor discovery, in the absence of a router, and the like. To enter the world, such addresses are not allowed.
Link local address is assigned automatically as soon as the host goes online, remotely such addresses are similar to the APIPA mechanismin Windows OS. Such an address always starts with FE80, but the last 64 bits is a poppy address with FFFE inserted in the middle, plus one bit is inverted. The mechanism for generating such an address is also called EUI-64. As a result, the address will be unique, since poppy addresses are usually different for all hosts. But some operating systems use a random identifier instead of the EUI-64 mechanism.
What are other news
Only the addresses of the change, of course, do not end there. The heading was also significantly simplified (see Fig. 2).
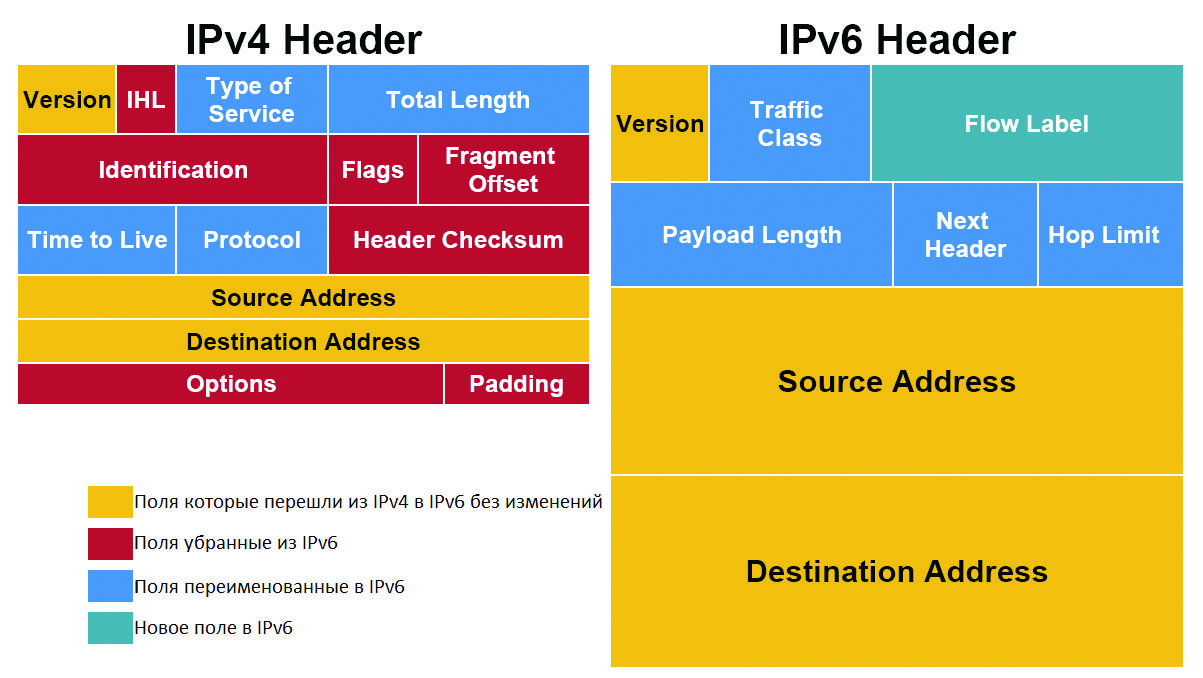
Fig. 2. Comparison of IPv6 and IPv4 headers
Now everything that is not required to route a packet from point A to point B has become optional. And if it’s optional, it’s moving to the extension header, which lies between the IPv6 header and the TCP / UDP data. In this same extension header, fragmentation, IPsec, source routing, and many other features already live.
The routers were greatly simplified, because you no longer need to recalculate the checksums, and as a result, IPv6 is processed faster than IPv4. Checksums removed altogether. Firstly, the frame at the L2 level has CRC, and secondly, the overlying protocols (TCP) will also ensure the integrity of the delivery. As a result, excess fields were thrown out of the header, it became easier, faster and more reliable.
Auto configuration and service protocols
There are two main options for assigning IPv6 addresses: stateless autoconfiguration - this is when the router sends the network address, default gateway and other necessary information to clients, and statefull autoconfiguration - when the DHCPv6 server is used. Therefore, if earlier DHCP was the only option for distributing information, then in IPv6 it became an additional option.
ICMP 6th version also did not go unnoticed, many features were added to it. For example, the Router discovery mechanism - clients can listen to what the router tells them (ICMPv6 type 134 router advertisement messages that come as part of the stateless autoconfiguration process), and when turned on, they can immediately call the router for help, they say, help configure (ICMPv6 type 133 messages router solicitation).
We also added the Neighbor discovery mechanism - we can say that this is a kind of ARP replacement, which helps to find the poppy addresses of neighbors, routers, and even to find duplicate addresses in the segment (duplicate address detection DaD), it works exclusively on multicast. There is no longer a pure Broadcast in IPv6, but we must not forget that silly penny switches broadcast the entire multicast, as a result, some of the new mechanisms are reduced to nothing.
Pentvester IPv6 Toolkit
Before moving on to vulnerabilities and attacks, it would be nice to consider what tools are in the arsenal of the pentester. Until recently, there was only one set of utilities for attacking the IPv6 and ICMPv6 protocols. It was THC-IPV6 from the notorious Mark van Hauser, the very author of the THC-hydra bruteforce and a host of other indispensable tools. It was he who, in 2005, became seriously interested in this topic and came to grips with the protocol of IPv6 protocol. And until recently, remained a pioneer.
But in the last year the situation began to change. More and more researchers are turning their attention to IPv6, and, accordingly, new utilities and new scanners have begun to appear. But for now, THC-IPV6 is still the best set of Pentester utilities. Its kit already includes more than 60 tools, divided into various categories - from scanning and mitts to flooding and fuzzing. But let's not forget the scapy tool, a utility that allows you to manually create any packages with any headers, even if such variations are not provided in any RFC.
IPv6 intelligence
Before attacking a target, you need to somehow detect it, so a standard pentest usually starts with a search for live hosts. But here comes the problem: we cannot scan the entire range. Scanning just one subnet will take years, even if you send a million packets per second. The reason is that only the / 64 subnet (or they are also called prefixes) is larger than the entire Internet today, and much more. Therefore, the most serious issue with IPv6 is target discovery.
Fortunately, there is a way out. First, you will need to find an AS (autonomous system) that belongs to the target (pentest object). There are enough services that allow you to search for their owners by AS; you can do this directly on the sites of regional registrars (the European registrar is RIPE NCC). Then, knowing the AS number belonging to a particular company, you can already search for the IPv6 subnets allocated to it.
The most convenient such search service is provided by Hurricane Electric (bgp.he.net). As a result, you can find several huge subnets, which, as we have already seen, are unrealistic to scan for live hosts. Therefore, you need to make a list of frequently used addresses and scan already point by point on them.
How can I compile such a dictionary? If we analyze how companies that have already implemented IPv6 assign addresses to clients, we can distinguish three main groups: auto configuration, manual address assignment, and DHCPv6.
Autoconfiguration can be done in three ways: based on the mac address, using the privacy option (i.e. randomly and, for example, change once a week) and fixed random (completely random). In this situation, it is possible to scan only those addresses that are based on a poppy. As a result, subnets comparable in size to IPv4 class A may come out, the process of working with such networks is not very fast, but still it is quite real. For example, knowing that the target company uses laptops of a certain vendor in large quantities, you can build a scan based on knowledge of how the address will be formed.
If the addresses are set manually, then they can be assigned either randomly, or according to some pattern. The second, of course, is much more common in life. A pattern can be :: 1, :: 2, :: 3 or :: 1001, :: 1002, :: 1003. Also, sometimes, service ports are used as the address, depending on the server: for example, a web server can have the address :: 2: 80.
If we take DHCPv6, then in this case usually the addresses are distributed sequentially from the pool (exactly the same behavior can be observed with a regular DHCPv4 server). In DHCPv6 you can often find a pool like :: 1000-2000 or :: 100-200. Therefore, in the end, we take the alive6 utility (it is included in the THC-IPV6 bundle and, like all the tools considered today, is included by default in Kali Linux) and run:
# alive6 -p eth0 2001:67c:238::0-ffff::0-2
Alive: 2001:db8:238:1::2 [ICMP echo-reply]
Alive: 2001:db8:238:3::1 [ICMP echo-reply]
Alive: 2001:db8:238:3::2 [ICMP echo-reply]
Alive: 2001:db8:238:300::1 [ICMP echo-reply]
Scanned 65536 systems in 29 seconds and found 4
systems alive
With this detection of living machines, only the part responsible for the host address will change. Using this approach, you can quite effectively and within a reasonable time frame find live hosts in previously discovered subnets.
But that's not all - of course, you can use DNS. With the advent of IPv6, DNS zone transfers and DNS bruteforces in the dictionary have not gone away. Applying all these techniques together, you can detect up to 80% of all included hosts in a given IPv6 subnet, which is very good. If only one host is compromised, it will not be difficult to find all its neighbors using multicast. It will be enough to run the same utility alive6, only with the -l switch.
From the latest features of THC-IPV6, and in particular the alive6 utility, one can note the ability to search for live hosts by passing an entire IPv4 subnet as a pattern for enumeration:
# alive6 -4 192.168.0/24
If we take the classic scan, then practically nothing has changed. The same Nmap, the same port scan options, the only difference is that now you can scan only one host at a time, but this is an obvious solution.
Perhaps the only additional technique for port scanning is to scan IPv4 first, and then obtain IPv6 information on these hosts. That is a kind of extension of the attack surface. For this, you can use both the ipv6_neighbor metasplit auxiliary module and separate ipv6_surface_analyzer scripts. They work on a similar principle - they take an IPv4 subnet at the input, scan it, find live hosts, check ports for openness, and then, having determined the MAC address, calculate the IPv6 address from it and already try to work on it. Sometimes this really helps, but in some cases (privacy option) IPv6 addresses cannot be found, even though they are.
INFO
When using IPv4 and ARP, it was quite useful to watch the ARP cache sometimes; on Linux, on a Windows platform, this could be done using the arp -a command.
Now, in the case of IPv6, in Linux, the ip -6 neighbor show command is used to view neighbors, and in a Windows environment this can be done with the netsh interface ipv6 show neighbors command.
Perimeter Threats IPv6
If you look at the external perimeter, you can find that many companies that have already begun to implement IPv6 are in no hurry to close their administrative ports (SSH, RDP, Telnet, VNC, and so on). And if almost everyone is trying to filter IPv4 somehow, then they either forget about IPv6 or don’t know that they need to be protected in the same way as in the case of IPv4. And if you can partially understand the IPv4 telnet used - for example, limited memory or CPUs do not allow full use of SSH - then every device that supports IPv6 today will simply be guaranteed to support SSH as well. There are even cases when ISPs expose IPv6 administrative ports on their routers. It turns out that even providers are more vulnerable to IPv6 attacks. This happens for various reasons. Firstly, there are not many good IPv6 firewalls, and secondly, they still need to be bought and configured. Well, the most important reason is that many do not even suspect IPv6 threats. There is also an opinion that while there are no IPv6 hackers, malware and IPv6 attacks, there seems to be nothing to protect from.
Threats Waiting Inside LAN
If you recall IPv4, then there will be three attacks that are still effective on local networks - ARP spoofing, DHCP spoofing, and ICMP redirects (this class of attacks was covered in detail during my speech at PHDays, so you can search corresponding video on the web).
In the case of IPv6, when the attacker is in the same local segment with the victim, the situation, oddly enough, remains approximately the same. Instead of ARP, NDP appeared, DHCP was replaced by auto-configuration, and ICMP just upgraded to ICMPv6. The important thing is that the concept of attacks has remained virtually unchanged. But in addition, new mechanisms like DAD were added, and, accordingly, new vectors and new attacks immediately appeared.
Neighbor Discovery Protocol (NDP) is a protocol by which IPv6 hosts can detect each other, determine the link layer address of another host (instead of the ARP used in IPv4), discover routers, and so on. In order for this mechanism to work, but it works using a multicast, each time a link-local or global IPv6 address is assigned to an interface, the host joins the multicast group. Actually, only two types of messages are used in the neighbor discovery process: requesting information, or NS (neighbor solicitation), and providing information - NA (neighbor advertisement).
The interaction in this mode can be seen in Fig. 3.
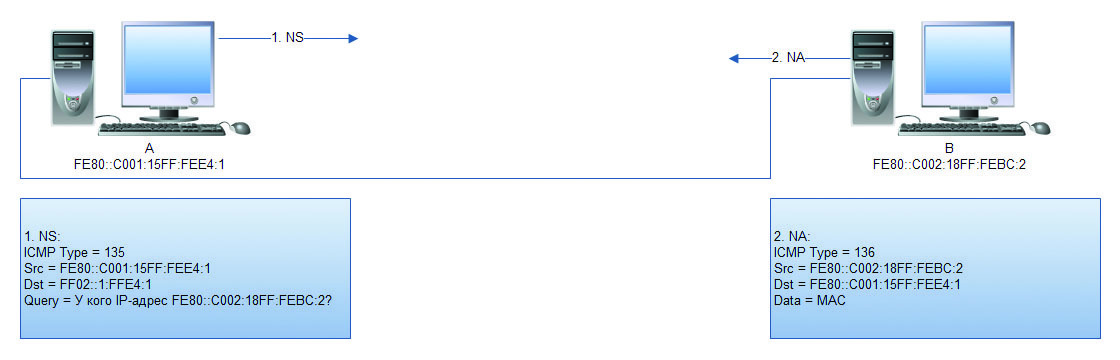
Fig. 3. Staffing ND
As a result, the attacker only needs to run the parasite6 utility, which will respond to all NSs flying in a single segment (see Fig. 4). Before that, you must remember to enable forwarding (echo 1> / proc / sys / net / ipv6 / conf / all / forwarding), otherwise a DoS attack will not be a MITM attack.

Fig. 4. Parasite6 utility operation The
minus of such an attack is that the attacker will try to poison the ND cache of all hosts, which is, firstly, noisy, and secondly, difficult in case of large volumes of traffic. Therefore, you can take scapy and carry out this attack manually and aiming. First you need to fill in all the necessary variables.
>>> ether=Ether(src="00:00:77:77:77:77",
dst="00:0c:29:0e:af:c7")
Вначале идут адреса канального уровня, в качестве адреса отправителя выступает мак-адрес атакующего, в качестве адреса получателя — мак-адрес жертвы.
>>> ipv6=IPv6(src="fe80::20d:edff:fe00:1",
dst="fe80::fdc7:6725:5b28:e293")
Далее задаются адреса сетевого уровня, адрес отправителя спуфится (на самом деле это адрес роутера), адрес получателя — это IPv6-адрес жертвы.
>>> na=ICMPv6ND_NA(tgt="fe80::20d:edff:
fe00:1", R=0, S=0, O=1)
The third variable you need to specify a correctly assembled NA packet, where ICMPv6ND_NA is ICMPv6 Neighbor Discovery - Neighbor Advertisement, and tgt is the actual address of the router, which is announced as the address of the attacker. It is important to set all flags correctly: R = 1 means that the sender is a router, S = 1 will indicate that the announcement is sent in response to an NS message, well, and O = 1 is the so-called override flag.
>>> lla=ICMPv6NDOptDstLLAddr
(lladdr="00:00:77:77:77:77")
Следующая переменная — это Link local адрес ICMPv6NDOptDstLLAddr (ICMPv6 Neighbor Discovery Option — Destination Link-Layer). Это мак-адрес атакующего.
>>> packet=ether/ipv6/na/lla
Осталось собрать пакет в единое целое, и можно отправлять такой пакет в сеть.
>>> sendp(packet,loop=1,inter=3)
The value loop = 1 means that you need to send infinitely, every three seconds.
As a result, after a while, the victim will update his neighbor’s cache and will send all the traffic that is destined for the router directly into the hands of the attacker. It should be noted that in order to create a full-fledged MITM, you will need to run another instance of scapy, where the addresses will be inverted to poison the router. As you can see, nothing complicated.
It is also worth noting that in IPv6 there is no concept of gratuitous NA, as it was in the days of ARP (gratuitous ARP is an ARP response sent without a request). But at the same time, the ND cache does not live long and quickly expires. This was designed to avoid sending packets to non-existent MAC addresses. Therefore, in the IPv6 network, NS - NA messaging occurs very often, which plays into the hands of the attacker.
Endpoint Threats
And since we’ve started talking about RA, we’ll smoothly move on to the threats of the end hosts, and in particular to those hosts whose work with IPv6 was not planned. That is, consider an attack on hosts running in the default IPv6 configuration on a regular IPv4 network. What happens if any modern OS gets an RA package? Since any system now supports IPv6 and expects such packets, it will immediately turn into the so-called dual stack. This is a situation where IPv4 and IPv6 are used simultaneously within the same OS. This immediately opens a number of previously inaccessible vectors. For example, it will be possible to scan the target, because IPv4 is usually filtered, and about IPv6, as we already know, they often do not think at all.
In addition, in most OSs, IPv6 takes precedence over IPv4. If, for example, a DNS query arrives, then it is highly likely that IPv6 will work sooner. This opens up huge scope for various MITM attacks. To carry out one of the most effective, you will need to host your own malicious IPv6 router. Each IPv6 router must join a dedicated multicast group. This is FF02 :: 2. As soon as the router joins such a multicast group, it immediately starts sending messages - RA. Cisco routers send them every 200 s by default. Another nuance is that clients do not need to wait 200 s, they send an RS-message - Router Solicitation - to this multicast address and thus immediately require all the information. This whole mechanism is called SLAAC - Stateless Address Autoconfiguration.
The attack is that you need to install your router (you should not take it literally, any Linux or even a virtual machine can act as a router), which will send RA messages, but this is only half the battle. Also, the attacker will need to start the DHCPv6 server, DNSv6 and NAT64 translator. As a service capable of sending RA messages, you can use Router Advertisement Daemon (radvd), this is an open source implementation of an IPv6 router. As a result, after the correct configuration of all the daemons, the victim will receive an RA and turn into a dual stack, and all the victim’s traffic will go completely invisibly through IPv6.
On the attacker's router, this traffic will be interrupted by the volume into regular IPv4 and then go to a real router. DNSv6 queries will also take precedence and will also be processed on the attacker side.
Thus, the attacker successfully becomes in the middle and can observe all the traffic of the victim. And the victim will not suspect anything. Such an attack carries the maximum threat, it works even when using IPv4 firewalls and static ARP records, when it would seem that there is no way to influence the victim.
How to protect IPv6
If we talk about protection against the attacks outlined above, it is first obvious that on the perimeter it is necessary to carefully filter all traffic and disable unused services, and special attention should be paid to administrative services. In order to reduce the impact of local attacks directed at the ICMPv6 service protocol, you can limit the surface of such attacks by breaking large networks into subnets (also called microsegmentation). The same network infrastructure can be divided into several vlanes, with a separate IPv6 prefix for each such vlan. In this case, the attacker will be able to attack hosts that are only in the same vlan with him, which will greatly limit the possible damage from attacks.

Fig. 5. SLAAC attack diagram
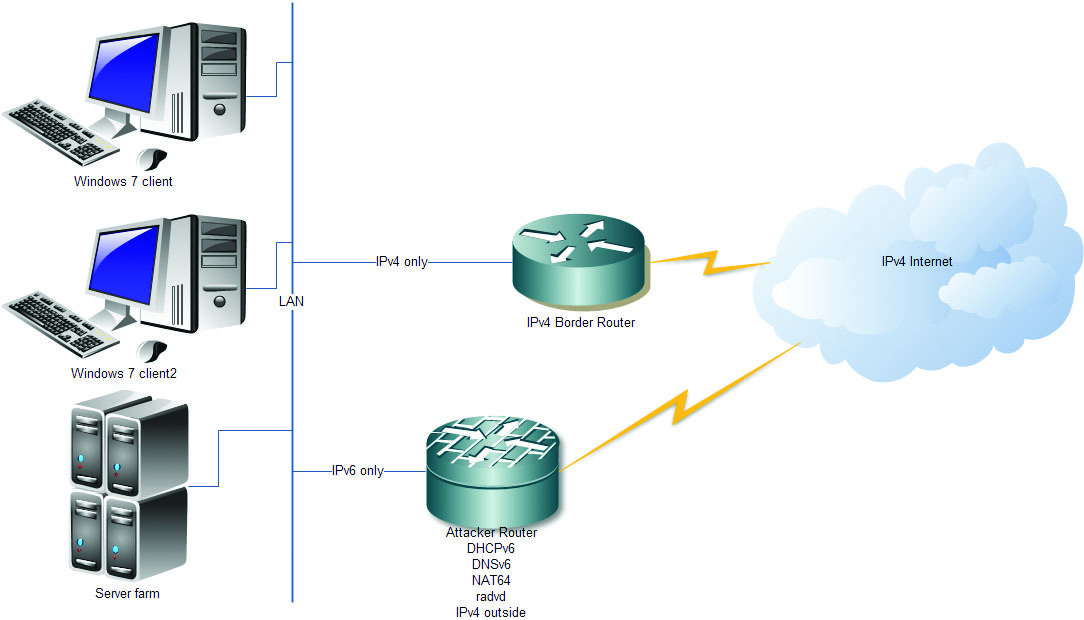
. 6. Result of SLAAC attack
Separately, there is protection against false RA messages, which, as you know, should only come from routers. Cisco has implemented a feature called Router Advertisement Guard, which prevents the injection of untrusted RA messages by separately marking potentially insecure ports. That is, RA packets simply will not be accepted from user ports. This feature works by analogy with DHCP snooping. The only negative is that such a feature is available only on a certain class of hardware - on the Catalysts of the 2960S, 3560 and 3750 series. In addition, DHCPv6 Guard and NDP Snooping appeared in 2012, again these are DHCP Snooping and Dynamic ARP Inspection analogues from the IPv4 world . These protective mechanisms are available on the Catalyst 4500/4948 and on the 7600 Series routers.
If we consider the protection of end hosts, then all the latest versions of Windows can completely disable the processing of RA-messages. If all IPv6 parameters are configured manually, this can be a good option, although it somewhat breaks the canonical mechanisms of IPv6. It turns off quite easily, right on the interface with the command
netsh int ipv6 set int X routerdiscovery=disabled
where X is the index of the interface (you can view the indices of IPv6 interfaces with the netsh int ipv6 show int command). The result is checked with the command netsh int ipv6 show int X.
If we look at the situation with the detection of IPv6 attacks, then everything is fine there. Detecting IPv6 attacks is easy enough, but it’s difficult to prevent them for now.
We conclude the story
What do we have in the dry residue? As it turned out, IPv6 itself is not safer, but not leaky than IPv4. The problem lies in the lack of knowledge and experience with this protocol. You need to filter IPv6 on the perimeter and turn it off if it is not used on end devices. Many people find IPv6 much safer than IPv4 because IPv6 requires IPsec. But this is a myth. Yes, IPsec can immediately work in an IPv6 environment, but is never required. IPv6 does some things better, others worse, but most things just differ from what everyone has gotten used to. In other words, IPv6 is no more or less secure than IPv4, IPv6 is simply unique and carries its own security concerns.
Posted by: Alexander Dmitrienko,PentestIT

First published in the Hacker Magazine on 11/2014.
Subscribe to Hacker


