About cheap data centers, RKN and DDoS protection
Sometimes the project lives in an inexpensive foreign data center, falls under Roskomnadzor’s carpets, periodically finds itself under DDoS attacks, but at the same time has terabytes of data and traffic.
How to live with it?
Preamble
We have a small photo bank on support. We will not give the name and country, only some technical data:
50 TB of data for storage, about 100 GB are updated monthly, “hot data” (95% of requests go to them) - 200 GB.
Average traffic - 50 TB / month.
Several years ago, we chose several Hetzner SX series servers with large disks for posting photos (for storing PD, we had to come up with a more complex solution, but more about that another time).
In Southbridge, hesitated that Hetzner was suitable for such a project, but the required level of accessibility and quality of connectivity was achieved.
Plus, for such a project, using a CDN will be an order of magnitude more expensive than distributing statics from servers in an inexpensive data center.
Plot
Here Roskomnadzor appears in our history, so that his name will not be mentioned in vain. In the spring of 18, carpet blockages began, and by May they covered many of our clients.
Some customers have solved the problem with access to Hetzner, Amazon, MS Azure, GCE, Digitalocean drastically: the servers were transferred to Russia entirely (hello, Selectel!), But for our hero, a small photo bank, constantly carrying 50 TB of data back and forth is too expensive , and we were not going to leave the project servers in Russia after the end of locks.
For large and inadequate problems, small and adequate solutions are needed.
Solution to the problem
For example, use other (unblocked) servers or services for frontend. Changing the range of ip-addresses did not help 100%, because The PKN every day blocked new and new IP subnets, so we decided to connect proxying through Cloudflare.com. Suddenly, who does not know, they not only protect against DDoS attacks (not as good as the best players in this market), but also provide a CDN service (and they do it well).
This is a great solution if the Cloudflare addresses you use are not blocked)
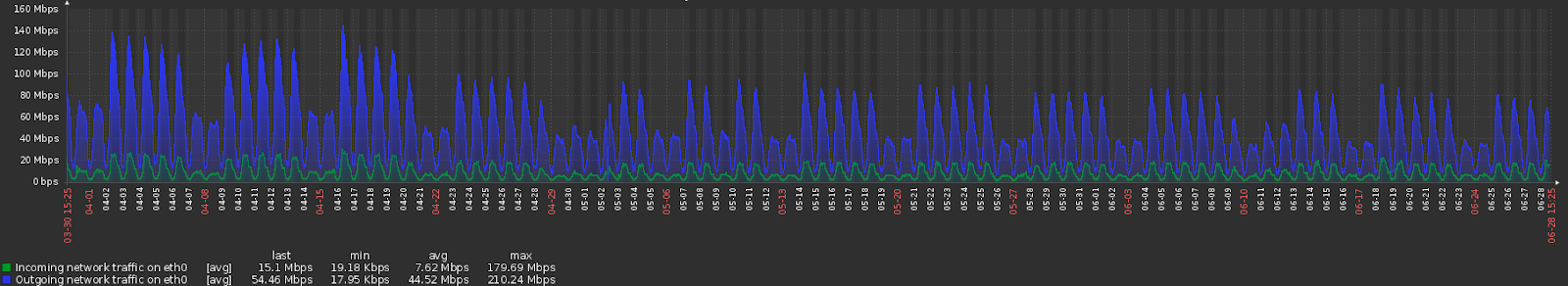
Ok, turned on - and began to monitor the stability and performance of traffic. After connecting the CF, we saw the following picture on the traffic counting chart from one of the servers (picture from Hetzner statistics):
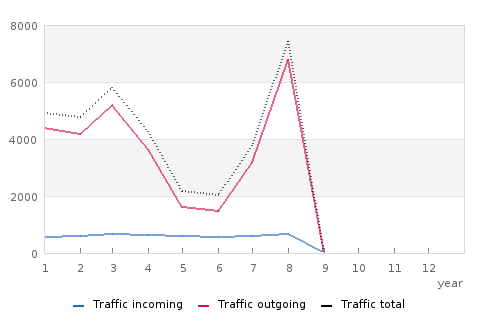
Incoming traffic changed within the margin of error (which is confirmed by the schedule for uploading new photos, for which a separate monitoring metric was made), outgoing on this server at the time of connecting the CF dropped 3+ times. The total real traffic fell not 3 times, just CF began to distribute traffic between servers differently.
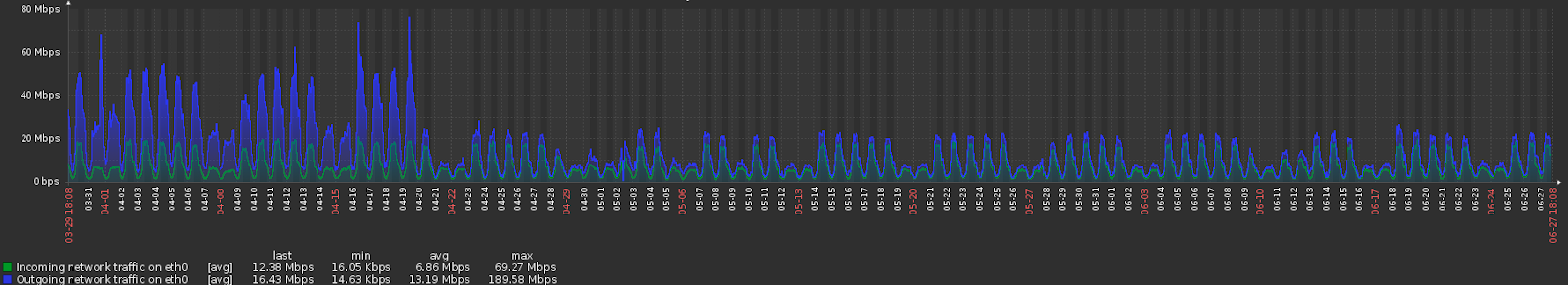
For example, the schedule for the same server from our monitoring system (for 3 months so that it is not too small):
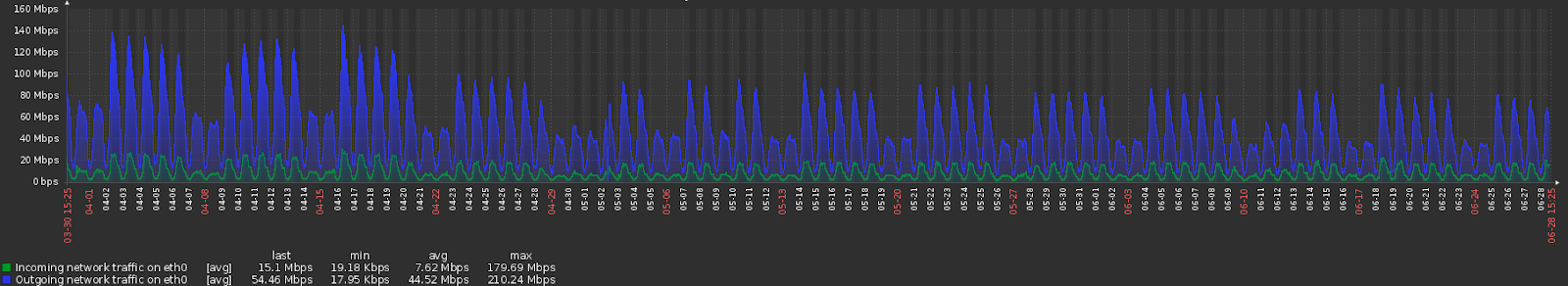
And one of the others:
But the total traffic still fell by 20%, i.e. CF saved some traffic to the project.
The average latency has increased, but we will not show these graphs.
The reason: Cloudflare has few distribution points for traffic in Russia. In Europe and North America, it is already acting much more efficiently.
And in parallel with the traffic, we monitor the activity of using the service. New photos are loaded into the service, and we monitor their number (and incoming traffic).
Schedule for 3 months (April-June) from one of the servers that process requests for downloading photos:
And here is another server:
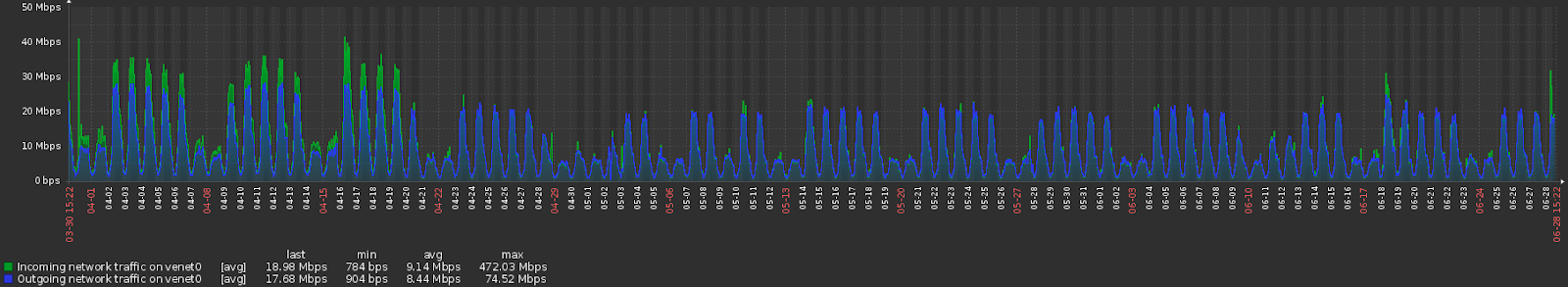
Cloudflare began to distribute traffic across backends in a slightly different way. But the content continued to load, the service worked, a catastrophic decline in quality did not occur (according to feedback from service users, the difference was not noticeable in principle).
The risk of getting a blocked address to Cloudflare is also there, but it can be reduced by taking a paid rate.
After completing the “carpet blocking of the name of the RKN,” we turned off Cloudflare.
What is the result?
- For 5–20 $ / month (in our case it was just $ 5 / month) you can solve a similar problem and not spend thousands of dollars on renting more expensive servers and transferring data.
- Even for projects with terabytes of traffic, free or almost free solutions are suitable. Tested in practice.
As an alternative:
- DDoS-GUARD offers a free rate with traffic proxying and protection from DDoS attacks.
- Several DDoS protection service providers had a free help service with such locks. (By the way, we also didn’t take extra money to solve the blocking problem).
- You can take one of the well-known CDN services: keycdn.com, cdn77.com, Akamai CDN, CDNVideo, Ngenix.net, etc. They solve the problem of protection against blocking for their clients themselves. But this is a) more expensive b) does not solve the problem of returning non-static content.
- You can connect another proxy service and protection against DDoS attacks (we worked a lot with Qrator and SkyparkCDN / G-Core Labs, for example), but they will have to pay for every megabit of useful traffic, and it will be really expensive.
- “You can deploy your own unblocked frontend” with any of the providers in the world, while choosing an unlocked address range, and ensuring good connectivity between your servers and the frontend servers. If you seriously need to do this - you can pre-check the address automatically by the list or manually here .
Personally, I recommend packet.net and servers.com for such “frontends” - excellent connectivity and the ability to take an hourly paid server.
ps If that - I am one of the speakers of "RedSlerom". Come, it will be interesting:
https://slurm.io/redslurm/
