Very difficult choice: 3 ways to protect a virtual machine
 Protecting or not protecting virtual environments from malware is a long-standing issue that has been closed without much discussion in favor of the first option. Another thing is how to protect ? We have developed the concept of agentless antivirus for the VMware platform for a long time: you can read more about it in this post by Evgeny Kaspersky. But technology does not stand still. Virtualization is attracting new applied IT areas, and with the growth of its applicability, specific security requirements are expanding. Obviously, one thing is needed for a virtual desktop, a second for a database, a third for websites, and so on. At the same time, agentless antivirus is far from the only protection option, and VMware is the most popular, but not the only virtualization platform.
Protecting or not protecting virtual environments from malware is a long-standing issue that has been closed without much discussion in favor of the first option. Another thing is how to protect ? We have developed the concept of agentless antivirus for the VMware platform for a long time: you can read more about it in this post by Evgeny Kaspersky. But technology does not stand still. Virtualization is attracting new applied IT areas, and with the growth of its applicability, specific security requirements are expanding. Obviously, one thing is needed for a virtual desktop, a second for a database, a third for websites, and so on. At the same time, agentless antivirus is far from the only protection option, and VMware is the most popular, but not the only virtualization platform.What are the alternatives and which one is more suitable?
Agentless concept.
There will be a “summary of the previous series”, since there is already exhaustive material on this issue (see link above).
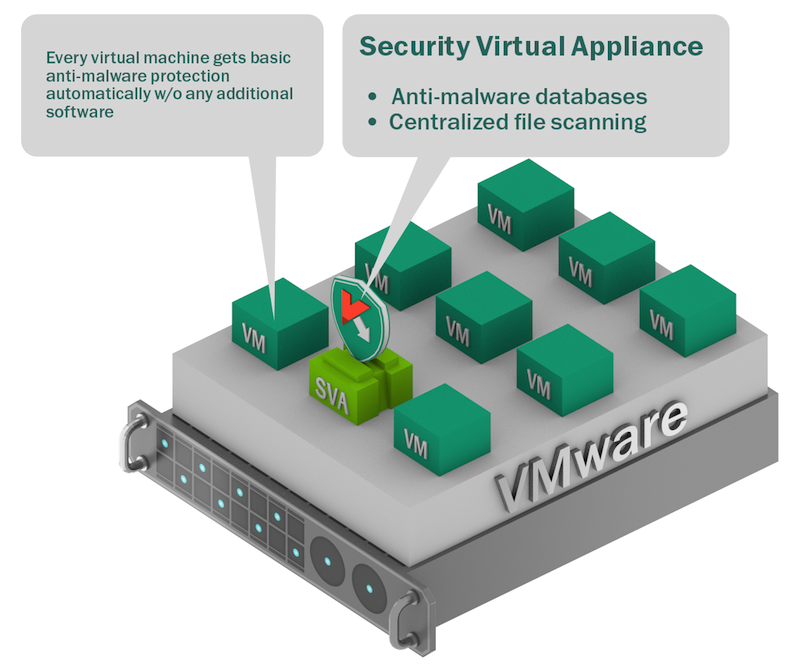
A special machine is allocated in the virtual infrastructure, on which the anti-virus engine is installed. Its connection with other virtual machines and scanned objects is provided by the native VMware vShield technology. In addition, vShield communicates with the anti-virus management system to configure, apply policies, enable / disable protection, optimize load, etc.
Sounds like a panacea, but this concept has a
This is exactly the features , because, apparently, VMware was not going to give a full interface for all the protective functions. In principle, this approach also has an application, but more on that below.
Now let's look at the following concept - Light Agent ("Light Agent").
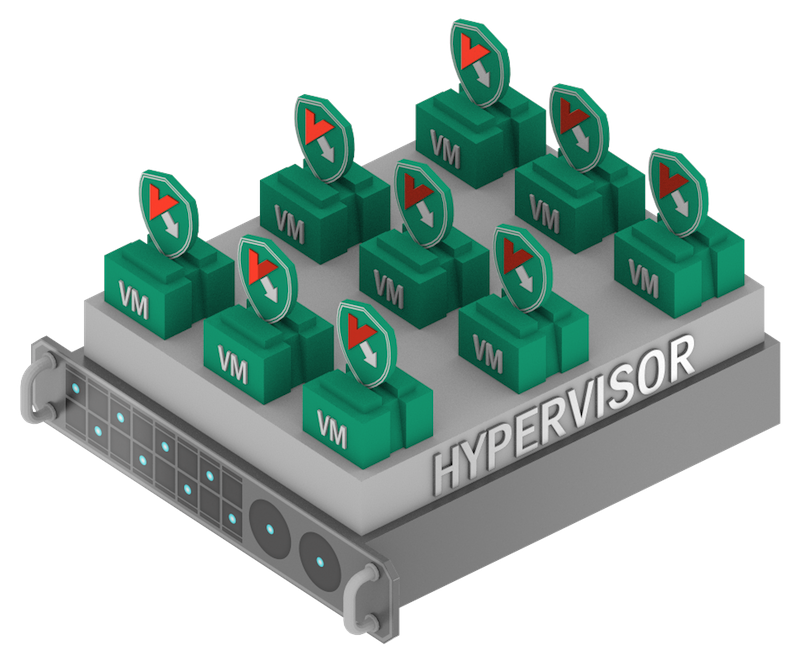
In this option, instead of vShield, a light agent interacts with the anti-virus engine , which is installed on each protected virtual machine. So we remove the limitations of the VMware interface to use the entire defense potential. And at the same time, we retain the advantages of an agentless approach — moderate appetite for resources, manageability, and resistance to “storms” (degradation of cluster performance due to the simultaneous updating or verification of many machines at once).

Yes, despite the name, light agentit will be "heavier" of an agentless solution - it requires memory in each virtual machine, processor resources, and new images of machines with a preinstalled agent. On the other hand, with today's capacities, these are very modest appetites, especially provided that in some standard operations it works even faster. And taking into account the growth in the quality of protection, it even becomes clear that the game is worth the candle.
Well, OK, what if the antivirus works only with Windows as a guest OS on a virtual machine, plus - I really want to have the most comprehensive set of security technologies, including cryptography ? Then a traditional endpoint product will be required .. Yes, it will be problematic to completely imprison it under a leafy virtual infrastructure, and such a solution will require more attention, but there are cases when such an approach is appropriate.
And now to practice. We recently released the third version of our product for virtual environments , implementing both security concepts (Agentless and Light Agent) in it. In addition to VMware, we now support Citrix XenServer and Microsoft Hyper-V . To the already available agentless solution for VMware, an option of protection using a light agent for all three platforms was added. Moreover, all products are managed from a single console., which is especially important for multi-hypervisor environments, so as not to create a console zoo.
So what tasks, which option is most suitable?
In general, the logic for choosing protection is as follows: for maximum protection, guest Windows needs a light agent , on other OSs (Linux, OS X), a product for endpoints . Alas, in the second embodiment, the application is limited due to performance considerations and the interaction of the antivirus with features of the virtual environment itself. We are working on supporting other OSs as an easy agent. And if productivity is critical, while the value and variety of data is low and access from outside is limited, then an agentless solution is suitable.
We analyzed typical application tasks using virtualization and compiled just such a curious tablet.

This is not an exhaustive and ambiguous picture - in different organizations the conditions may change, and the list of tasks will expand. Its goal is to show the threat model and methodology for assessing tasks and priorities.
Go back to the title. Well, that choice, it turns out, is not even difficult at all!
