Chameleon virus spreads over WiFi networks as a cold among people
- Transfer

A team of security researchers at the University of Liverpool in the UK provided evidence of a concept that allows you to infect WiFi networks in one fell swoop.
Researchers demonstrated a WiFi virus, called Chameleon , that can spread on the network in the same way that a “cold” spreads between people; scientists made it possible to replace the firmware of a vulnerable Access Point (AP) with an infected version. In case of infection of one access point,
Chameleon propagates itself on computers connected to it, and searches for new, uninfected Wi-Fi networks, which allows it to independently spread inside wireless networks, from point to access point.
Chameleon is a serious threat to IT security, because the attack scenario uses WiFi networks and the vulnerability lies in the fact that the attack cannot be detected by any of the existing defense mechanisms, including anti-virus and intrusion detection systems (Wireless intrusion detection system, WIDS).
Thus, this attack is considered the most modern and difficult to detect, since for WIDS, the criteria for detecting AP infection are usually changes in credentials, or traffic.
The virus spreads as follows:
1. A list of vulnerable access points at the current location is formed.
2. Hacking security encryption on the AP.
3. The AP administration interface is bypassed.
4. A backup of the AP configuration is saved.
5. The firmware on vulnerable access points is replaced with a new firmware infected with a virus.
6. The system settings are restored.
7. The virus propagates to connected computers (and again to step 1).
In order to analyze the behavior of the virus, a laboratory experiment was conducted for which scenarios of the behavior of the virus were simulated in two cities - Belfast (Northern Ireland) and London (England). Their choice is not accidental, since these cities represent a large (London) and medium (Belfast) urban wireless network infrastructure based on the density of access points.
The following data refers to two regions in which researchers conditionally distributed malware.
Belfast has about 14 553 access points, of which 22% are open, 61% are protected by WPA / WPA 2 encryption and 14% by WEP.
There are about 96,433 access points in London, of which 24% are open, 48% have WPA / WPA 2 encryption, and 19% have WEP.
Infection, starting at random from one of the access points, was able to spread throughout the network through weak access points.
Below is the dynamics of the spread of the virus depending on the radius between access points:
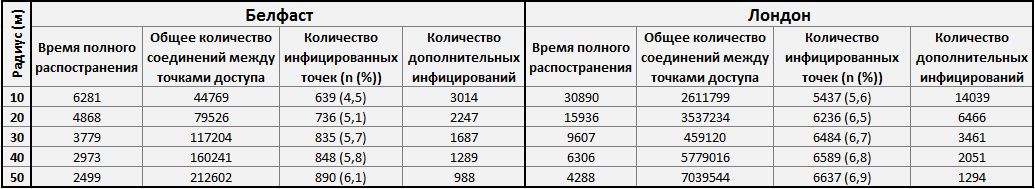
If the model did not change its state for 2 days in a row, the system chose a random access point for additional infection.
This experiment proves that the density of communication between access points is a more important factor in the spread of the virus than vulnerability.
In theory, such geographical areas with a high density of access points are more susceptible to infection.
" WiFi connections are becoming a growing target for hackers because of well-known vulnerabilities that make it harder to detect and protect against viruses, " says Marshall, one of the authors of Chameleon.

Chameleon quickly progresses in a completely healthy environment, but slows down with an increase in the number of infected nodes (this is shown in the table (the closer the points, the longer the infection takes) and on the graph).
The study also presented methods for detecting the Chameleon virus by monitoring Wi-Fi packets. This approach is quite specific, but in any case, it can be adapted to detect malware in the future.
Although Chameleon is just an experimental research product, there is a risk that in the future cybercriminals will use similar strategies to spread malicious code.
Link to research - jis.eurasipjournals.com
From the translator :these studies seemed rather vague. It seems that the researchers are biasing to practice, but at the same time, the original article gives only theory, and even then in a limited amount. Afraid to provide guidance for intruders? So after all, manufacturers of access points also need to fight. Plus, the experiment is quite spherical. It seems to me, when discovering a new vulnerability of this magnitude, it would be nice to watch it in a "living environment".
Only registered users can participate in the survey. Please come in.
At the moment, this is more likely the appearance of a threat, but what if the approach itself turns out to be working. What then?
- 23.6% Defense will be invented faster than the virus leaves the laboratory 115
- 47.9% Stickers on Chameleon protected 100% routers as a marketing move 233
- 27.5% Programmable Read-Only Memory for storing firmware 134
- 26.7% The amount of spam / advertising / identity theft, etc. will increase by an order of magnitude and more than 130
- 10% Ecumenical Apocalypse in which WiFi networks are hit hard 49
- 38.6% is unlikely to go beyond research 188
- 1.8% Own option (leave in the comments) 9
