Keyloger iOS 7
- Transfer
The problem of keyloggers for mobile applications is becoming more noticeable in the world of mobile devices. It has long been known that jailbroken iOS 7 devices can be vulnerable to keyloggers who record and transmit all your gestures and clicks to attackers. Now this also applies to non-jailbroken iOS devices.
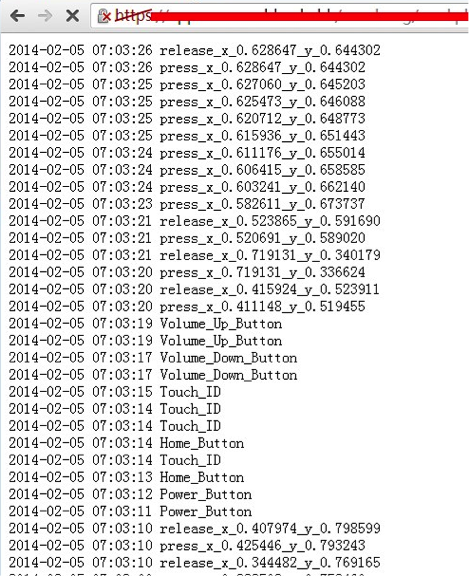
Evidence was presented on FireEye's blog post.Monday night, February 24th. The vulnerability is present in versions 7.0.4, 7.0.5, 7.0.6 and 6.1.x. Because of this, it is possible to implement a keylogger by phishing or through vulnerabilities in applications, bypassing the App Store application review system. This vulnerability can record and transmit in the background all touch gestures, as well as record keystrokes: “home”, volume rockers and the fact that TouchID was pressed. FireEye has already reported to Apple about this issue.
Users have the opportunity to avoid leakage of personal data. To do this, go to "Settings"> "General"> "Content Update" and prohibit "... in the background, the use of geolocation services or updating their content by programs ...". Disabling background updates to unnecessary application information helps prevent potential background monitoring. Despite this, you still have a chance to catch a keylogger. For example, an application can play music in the background when updating content in the background is turned off. Thus, malicious applications can be disguised as a music keylogging application.

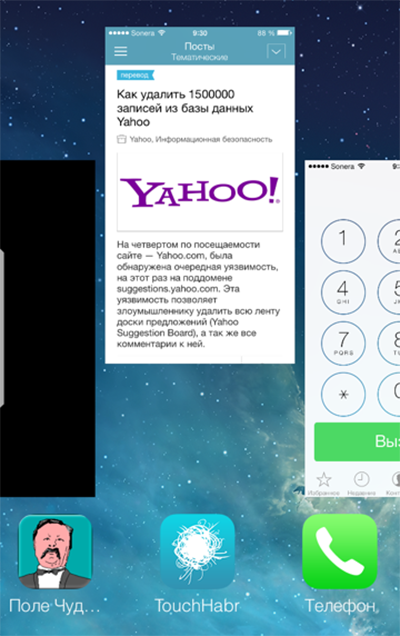
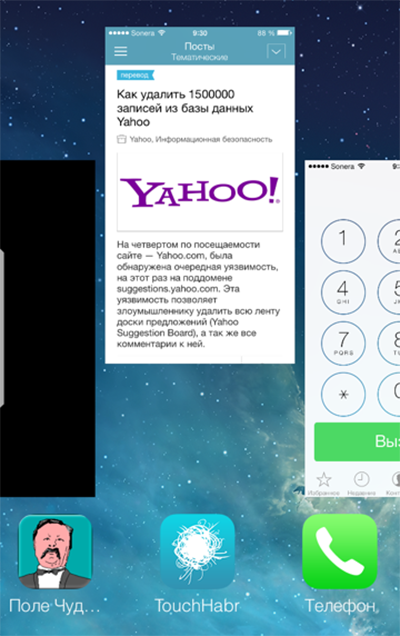
Prior to the release of the patch from Apple, FireEye recommends the following: close active applications through the application manager:
Apple recently released version 7.0.6 to fix problems with SSL encryption, which is used to protect sensitive information. Let's hope this vulnerability is fixed in the next version.
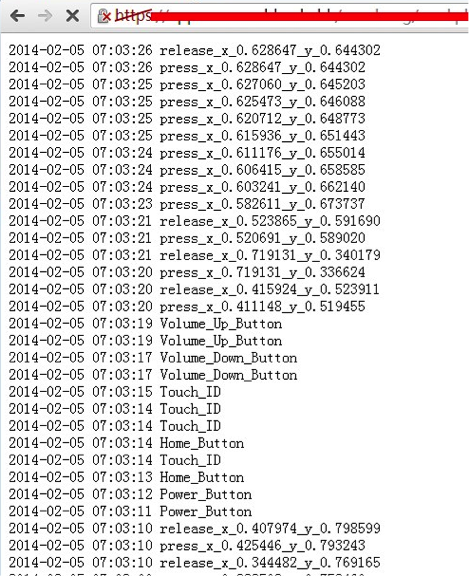
Evidence was presented on FireEye's blog post.Monday night, February 24th. The vulnerability is present in versions 7.0.4, 7.0.5, 7.0.6 and 6.1.x. Because of this, it is possible to implement a keylogger by phishing or through vulnerabilities in applications, bypassing the App Store application review system. This vulnerability can record and transmit in the background all touch gestures, as well as record keystrokes: “home”, volume rockers and the fact that TouchID was pressed. FireEye has already reported to Apple about this issue.
Users have the opportunity to avoid leakage of personal data. To do this, go to "Settings"> "General"> "Content Update" and prohibit "... in the background, the use of geolocation services or updating their content by programs ...". Disabling background updates to unnecessary application information helps prevent potential background monitoring. Despite this, you still have a chance to catch a keylogger. For example, an application can play music in the background when updating content in the background is turned off. Thus, malicious applications can be disguised as a music keylogging application.

Prior to the release of the patch from Apple, FireEye recommends the following: close active applications through the application manager:
To view and manipulate active applications, iOS7 users should double-click the home button and drag suspicious and unnecessary applications from the multitasking screen.
Apple recently released version 7.0.6 to fix problems with SSL encryption, which is used to protect sensitive information. Let's hope this vulnerability is fixed in the next version.
