Retrieving 4096-bit RSA keys using a microphone
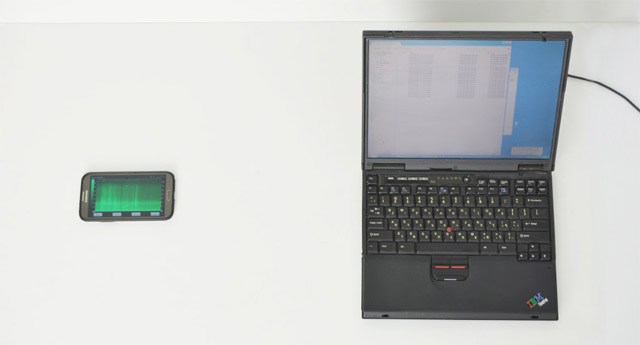
The famous cryptographer Adi Shamir (the letter “S” in the abbreviation RSA) and colleagues yesterday published a scientific paper entitled “ RSA Key Extraction via Low-Bandwidth Acoustic Cryptanalysis”. The complex name hides an exceptionally accessible method for extracting RSA keys (in the GnuPG implementation) using an ordinary mobile phone or microphone. Just put the phone 30 cm from the victim’s computer. If you use high-quality microphones, you can remove the keys from a distance of 4 meters.
This is hard to believe, but several successful experiments have already been carried out to extract keys from different computer models, and software has been written with the help of which independent researchers can check the results.
The work is a continuation of the famous presentation of Adi Shamir from 2004 . Then he showed the theoretical possibility of key extraction and demonstrated the difference in the sound picture when decrypting text with different RSA keys.
Now we have managed to reach a fundamentally new level, for which we must first of all thank the developer Lev Pachmanov, who wrote unique software for signal processing.
“Many computers emit high-frequency sound during operation due to vibrations in some electronic components,” explains Adi Shamir. “These acoustic emanations are more than annoying squeaks: they contain information about running software, including security-related computing.” In 2004, Shamir proved that different RSA keys cause different sound patterns, but then it was not clear how to extract individual bits of the keys. The main problem was that the audio equipment is not able to record sound with a sufficiently high sampling frequency: only 20 KHz for ordinary microphones and not more than a few hundred kilohertz for ultrasonic microphones. This is many orders of magnitude less than the frequency of several gigahertz at which modern computers work.
Now thanks to the aforementioned Pakhmanov, software has been created that extracts the full 4096-bit GnuPG keys from computers of various models after an hour of listening if the computer decrypts. A successful demonstration of such an attack was carried out using a smartphone that was 30 cm from the computer, as well as an attack using directional microphones from a distance of 4 meters. Background noise, as well as the sounds of a fan, hard drive, and other components usually do not interfere with analysis, because they are emitted at low frequencies below 10 KHz and can be filtered out, while the squeaks of electronic components of interest can be filtered out at higher frequencies. The use of multi-core processors facilitates the attack. The sounds of computers with the same hardware configuration also do not interfere with each other,

Among the attack scenarios:
- Installing a special application on your smartphone and arranging a meeting with the victim, during the meeting, placing a phone near his laptop.
- Hacking the victim’s phone, installing a special program there and waiting until the phone is near the computer.
- Using a web page that can enable the microphone through a browser (Flash or HTML Media Capture).
- Using traditional bugs and laser microphones for a new field of work.
- Sending your server to the hosting with a good microphone inside. Acoustic key extraction from all surrounding servers.
- Installing bugs in the ventilation holes of servers and workstations.
Finding out readers who have not yet dropped their jaw, Adi Shamir adds: “In addition to acoustics, a similar attack can be carried out by measuring the electrical potential of a computer case. To do this, it’s enough for an appropriately equipped attacker to touch the conductive parts of the case with his bare hand or connect to the ground pins on the other end of the VGA, USB or Ethernet cable. ” First you need to measure the potential of your own body relative to the grounding potential in the room by touching some kind of well-grounded object.
GnuPG developers got information six months agoabout vulnerability, as well as Shamir’s recommendations for alleged protection against this kind of analysis. The versions of GnuPG 1.x and libgcrypt released today contain the necessary algorithmic modifications that make analysis difficult, but some effects are still preserved, in particular, various RSA keys are still distinguished acoustically, says Shamir.
PS Maybe this is a coincidence, but two months ago Adi Shamir was not given an entry visa to the United States when he was going to the History of Cryptology cryptographic conference, although Shamir was one of the founders of this conference and made an opening speech at its opening in 1981. Since then, all 32 years he tried not to miss a single meeting. Now the sponsor of the organization is the NSA.
