Hideninja VPN Application Launch History for Android (Part 1): First Prototype, First In-App Purchase Hack
We were hacked! We were hacked!- My reaction to hacking the In-App Purchase of my “Hideninja VPN" application for Android was not original. But I wrote about this only in the penultimate paragraph. And before him there are a few more lines about what kind of project this "Hideninja VPN" is. I will also talk about how the path from the first prototype was passed, how the project reached the top-5 at the request of “vpn” of the English-language Google Play, how the redesign influenced the user’s perception of the application, rake collecting and, finally, about the hacking In-App Purchase . Of course, I divided this material into several parts, otherwise reading it would be absolutely tiring. So, Part 1.
Here it is, hacked “Version 3.3 PRO”.
What are we talking about?
I am sure that you already have a question, what kind of project is this "Hideninja VPN". If you are familiar with what a VPN is , then you already understand what kind of service and value for the user we are talking about: this is a VPN service for Android, today it offers the user to connect to one of 20 own servers around the world . When you connect your device to "Hideninja VPN", all your traffic is encrypted on your device, passes through the server you selected in "Hideninja VPN", at the output from which your real IP address is changed to the IP address of the server, different from your real one.
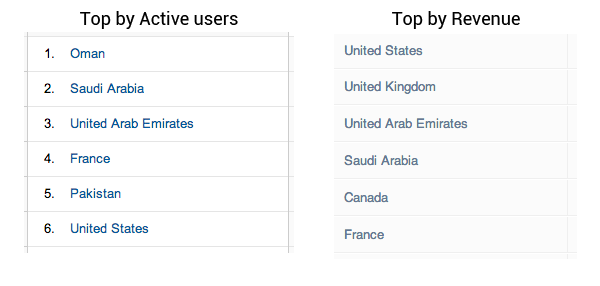
In Russia, so far, we are practically unlimited in our movement on the Internet, while in the West, and especially in the East, the problem of censorship on the Internet is very acute, which is confirmed by our statistics, which will be discussed below. In the most advanced cases, people without a VPN do not have access to Facebook, YouTube, Skype and other popular services at all, you may not even mention the problem of access to torrent sites and the risk of being caught downloading illegal content - this problem disappears before the pain of not being able to access on Facebook.
So, the statistics. The “Hideninja VPN” application was launched on Google Play in January 2013, as of September 2013: downloaded more than 300,000 times, has more than 135,000 regular active users, both indicators are growing.

The application is especially popular in the East, but - I won’t be surprised - the main paying users are from the USA, Great Britain - compare the top countries of active users (left) and top countries by income (right):
How it all started
In January 2013, I conducted a study and saw that in the VPN market for Android, among more than 1000 applications, there is not one that would suit me with its UI and UX, price, speed, but especially UI and UX. After reading user reviews from top-5 VPN applications, I realized that I was not the only one.
Looking at the number of downloads on Google Play among VPN application leaders (more than 7 million in total from top-3 players for “vpn”), he formulated the following simple hypothesis: since users download and use products with low quality UI and UX, with slow connection speed and annoying advertising or restrictions, and besides - they also buy paid functions and subscriptions in these applications, they will have to download and use a much more convenient application, in the development of which all knowledge about competitors' shortcomings will be taken into account.
If there is a hypothesis, it is necessary to prove it. And the solution is better than to go the way of creating MVP (Minimum Viable Product) and release it on Google Play, I did not find.
First prototype
Testing an idea by releasing a prototype with a minimum set of functions (MVP) for real users, from the point of view of business and marketing, is a quick and cheap way to test and gather first opinions about the idea of a product; to do this without a prototype is much more difficult. From a technical point of view, MVP is a set of crutches glued together and working on parole, that is exactly what the first prototype of “Hideninja VPN” looked inside (and outside - too).
So, what I had at the time of creating the first prototype:
- irresistible desire to make some kind of convenient application
- understanding how to implement VPN based on the latest Android API
Well, in fact, there was nothing more, the lack of certain necessary resources, as well as knowledge and skills in bringing mobile applications to the market, was covered by energy from an irresistible desire to do something of their own, necessarily cool and useful to people.
By a short search, a suitable version of the OpenVPN protocol implementation for Android was found, though only for version 4 and higher, but at the beginning of 2013 this did not seem to be such a big problem - the total percentage of downloads of the Tools category applications, most suitable for VPN on Google Play, 4ki from all versions has already strived at a good pace to 50%, which proved that support for versions 2.x would not be profitable.
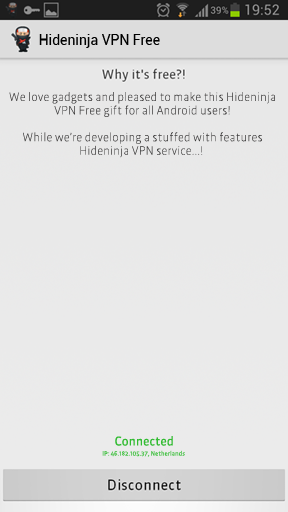
I made the simplest UI of the first prototype myself, adding one Connect / Disconnect button to the blank blank of the application screen, displaying the IP and country of the VPN server to which you are connecting, as well as several suggestions for at least some sort of clogging of empty space:
Looking ahead, I’ll say , that only in the 3rd major version of the application did I get an understanding of which UI&UX would be really user-friendly. Read about it in the next part.
The first prototype was able to connect a user to only one server (there was no possibility to select a server) and display the status of connected / disconnected.
Of course, this was not the same convenient and fast application that I was aiming for, but the first prototype showed me that there is still room for new players in the VPN market for Android, which means it makes sense to continue to test your hypothesis.
Is In-App Purchase Hacking So Terrible?
And again, I get ahead of myself: in the next part of the article I will talk about how we entered the market, how we started monetizing. Here I’ll just say that the In-App Purchase option was chosen, which, as it turned out, is ridiculously easy to crack!
September, rain, 3 a.m., I accidentally stumble on a thread about my project on w3bsit3-dns.com, which was very surprised, since the Russian-language Google Play was never our priority, and we did not show marketing activity aimed at Russian-speaking users.
I start reading the first post, I get to the attached files and see that two files are attached - the free version and the PRO version, which can be obtained only by paying 49.99 rubles. (price for Russia) through the in-app purchase mechanism.
My first reaction - oh well, of course, that's how PRO is for everyone. But after I installed the hacked version on a completely clean smartphone with a fresh Google Account, everything fell into place, and I was literally furious!
I note that until that moment I had not studied the topic of hacking applications, otherwise I would have immediately understood everything, in addition, I would have insisted on the implementation of at least standard security tools - ProGuard and License Verification Library (but they are successfully hacked using simple methods). It is especially important to protect yourself from hacking if you use the built-in Google Play tools (In-app Billing Version 3 API) to control and manage purchases and subscriptions, and not your own server.
But do not react sharply to hacking. Where it is better to start working with the audience, which we did. We launched a campaign on w3bsit3-dns.com, where we offer users to get PRO for free: absolutely legally and without hacking. This gave us loyal users, with whom we now constantly keep in touch and ask to help us if we need to test new versions.
Experience gained
Be sure to study competitors and the market; as soon as the application has basic functionality, albeit less than that of competitors, lay it out for testing.
You should not rush in blind fury at those who hacked you, it’s much wiser to see the advantages for the project in this and use them for the good.
What's in the next part of the story
I’ll talk about how we did it from the first prototype to the current version of the application. In the meantime, here is what all 3 versions that were released look like, feel the difference (first prototype, 2.0, 3.0, respectively):

