Mail.Ru is testing a new way to infect computers

Once in the middle of the night nostalgia struck me and I decided to download the song “Angelica” - “Town” from the hares.
I find, the bitrate is suitable, I choose mp3 and download .
But for some reason the .exe file was downloaded ... and from the strange address dls3.moilru.ru/output/.../02/96/6b/9f/audio/varum_anzhelika_-_gorodok_zaycev_net.exe
what nonsense I think.
I choose the .rar format, the same is downloaded - the .exe file is 160KB in size.
I run whois by domain and get:
domain: MOILRU.RU
nserver: ns1.reg.ru.
nserver: ns2.reg.ru.
state: REGISTERED, DELEGATED, UNVERIFIED
person: Private Person
registrar: REGRU-REG-RIPN
admin-contact: http://www.reg.ru/whois/admin_contact
created: 2013.05.13
paid-till: 2014.05.13
free-date: 2014.06.13
source: TCI
Oops! Fresh!
Fill the file with VirusTotal and get a report on the file.
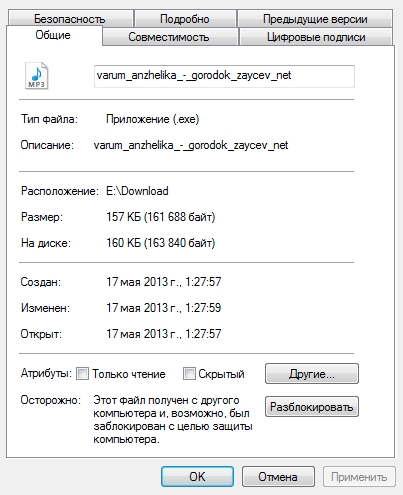
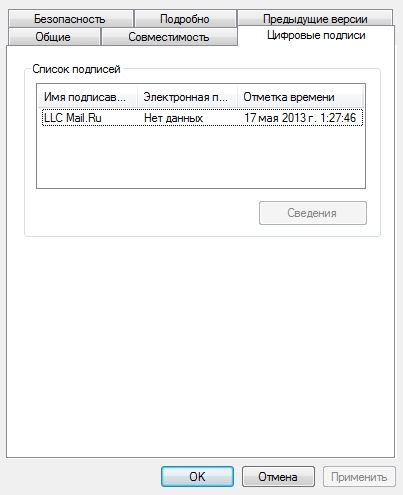
Screenshots of file properties.
Selectively poked other compositions, everywhere the executable file sways instead of mp3.
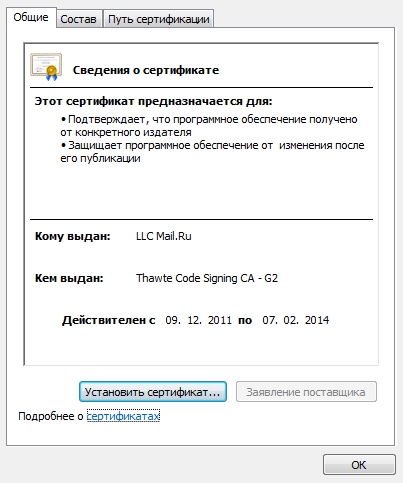
The downloaded files have different sizes, but everyone has a signature with the mail.ru certificate.
My user agent:
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:21.0) Gecko/20100101 Firefox/21.0
I change it to Android. A redirect to m.zaycev.net goes right away and now normal mp3s are already downloading ...
Wow!
He listened, called, to the music at night.
The comments reminded me of another article .
PS I ask a rhetorical question - how can one sign so many different files with a mail.ru certificate without it?
PPS Checked the IP site, DNS and gateway provider - no spoofing. It was checked by a second antivirus - clean.
Update
(After 12 hours):The distributing domain has been changed to downloader.com and the url format has been changed:
http://dwnloader.com/MjU1NTtodHRwJTNBJTJGJTJGZGwuemF5Y2V2Lm5ldCUyRjExNWE3ZGY2LTE4NjMtNGQxNy1iOWRjLWM5MTI0ZGIwZGVkOCUyRjE2NTA1JTJGMTY1MDUxOCUyRm5hdGFsaV8tX29fYm96aGVfa2Frb3lfbXV6aGNoaW5hXyh6YXljZXYubmV0KS5tcDM7bmFtZT1uYXRhbGlfLV9vX2JvemhlX2tha295X211emhjaGluYV8oemF5Y2V2Lm5ldCkubXAzO3NpemU9ODY1MDc1Mjt0eXBlPW1wMw==
A little later, the domain was again changed to dawnloader.ru (78.140.165.153)
. Two days later, it was changed to dwnloader.net (46.254.18.232).
Which redirects to other domains, from which the download occurs:
vengera.ru
savtopo.ru
dojdipo.ru
astonka.ru
hkovma.ru
owsezam.ru
gudlet.ru
pilagi.ru
zyankokhi.ru
iqtaxib.ru
goditsa.ru
ekzofo.ru
rfaksa.ru
liqra.ru
skachatfayl.ru
dwnloader.net
These domains are also involved in the infection of visitors to the torrentino.com service.
All of them are on IP 146.255.192.214. The Data Center does not respond to abuses :(
Inside the same file signed by a certificate from mail.ru.
I am in Ukraine, which is probably why I do not get a file signed by LLC Pentagon.
Update
(After 16 hours)An inscription appeared at the jump:
The file is downloaded using a special loader (trojans) from our partners - Mail.ru and Rambler . Launching the bootloader is absolutely safe for your computer, which is confirmed by a digital signature, but false positives for antiviruses are possible .
I translate: We agreed with Kaspersky Lab, it does not consider these files as trojans, and Dr.Web, which classifies files as trojans, is not an antivirus at all.
And the answer was received from distributors:
From: Nikolay nik [a] openprog.ru
You are complaining about the bootloader (which supposedly contains a virus).
We hereby inform you that there is a false positive response. The file itself is nothing more than an HTTP client for downloading any content and it is certainly not a virus. The file is digitally signed by its manufacturer, Mail.Ru, and is located on Mail.Ru servers, which further confirms the origin and reliability of this file.
Heuristic analyzers of some antiviruses can be triggered by the internal structure and actions of this file, however we guarantee that the triggered data is false.
If you have questions about files that are distributed from our server - please write about them on nik [a] openprog.ru
They also lack IP and they ordered new ones from the Data Center :(
