Arbor Pravail APS and DDOS
Good to all!
Not so long ago, we conducted a comparison of several protection systems against DDOS attacks that we managed to “touch”. As promised - we share our impressions of our chosen device. Here we will not tell you what it is, where and why a DDOS attack is born, we are sure that you already know this. We will consider the practice of using the system in a particular example (there will be many pictures). So, meet Arbor Pravail APS !



About two months passed from the moment of order to receipt.

An obviously seen box, worn in places, torn in places, sometimes painted with a pen or something else, but is this the main thing ?! Rather - open!
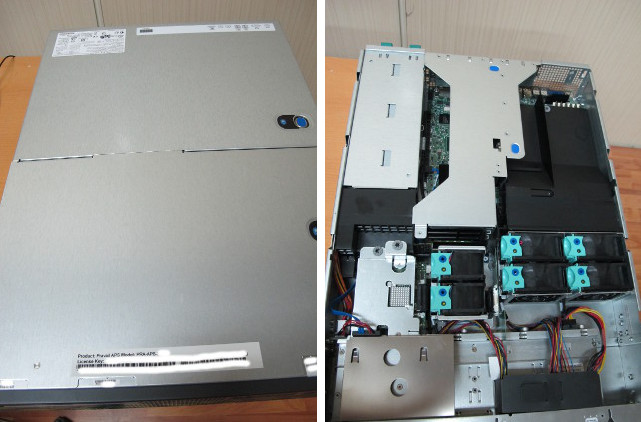
We opened it, it seemed a familiar Intel 2U chassis with a beautiful “face” and we certainly climbed inside to look inside =)

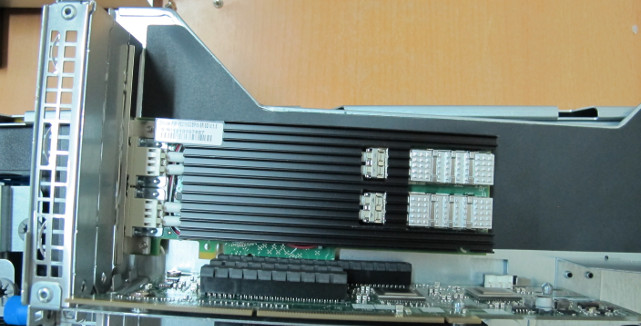
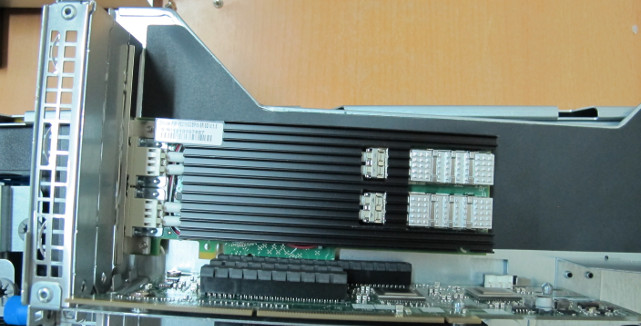
Nothing unusual, two processors, a memory… a design feature was given out by an unusual Silicom network card with a large heatsink, like on a GPU, that heats up , an overseas miracle =)
Enough "pampering", it's time to see it in action!

We connected it to one of our test routers and began to configure. The standard steps are the console, the address on the management port, installing acl, and almost everything. The main thing - do not forget the key to the license, filtering will not =)
In this post, we will not go into particular settings Pravail modes, they are quite simple (groups, filters, parameters), if Habravchanam will be interesting - will do a separate post for each item. In short - Pravail has basic settings for automatic protection of groups, which are based on several types of protected objects (web, dns, mail, vpn, voip, file, rlogin). Each type has a relatively detailed setting with three levels of protection. Switching between levels can be done in one click, at one time, all groups can be protected only at one level.
Let's get down to business!
DDOS attacks are different, they come to us constantly. It is interesting to look at Pravail in business, is it really as good as the manufacturer says about it, because all manufacturers say only the best about their products, isn’t it? =)
For example, we take a special case from the ordinary life of a regular web server, which we put on a permanent defense “for” Pravail. On this server we practice protecting sites that are attacked by all sorts of not-so-good robots.
Day X and hour Y coincided (I did not have to wait long). On our links, we recorded an anomaly, the total “excess" incoming traffic was approximately 3.5Gbit (~ 650kpps), in general this is not a lot by modern standards, spamhaus knows hello to crooked dns servers = \
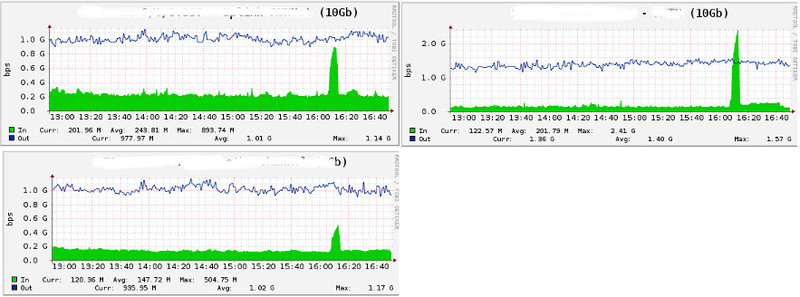
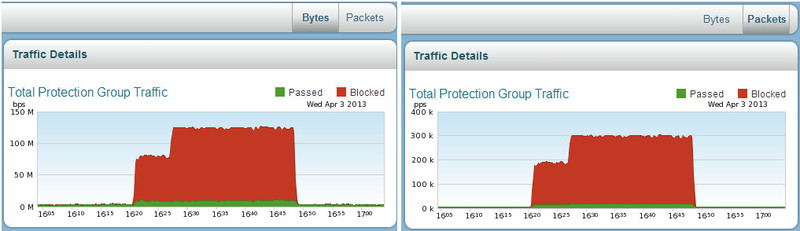
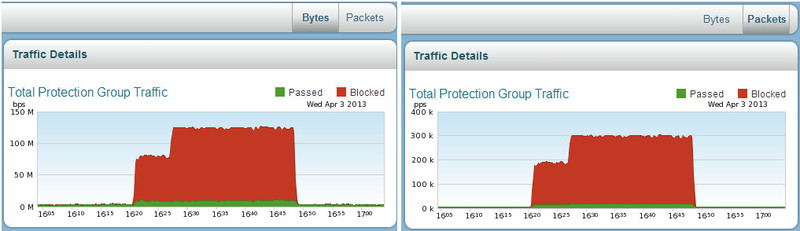
Through various filters on to Pravail in total about 130Mbit and 300k pps “reached”, what kind of traffic is this? Below we will analyze in detail the pictures.
Here we look at the reaction of the system to the attack, what Pravail sees and what can or should be done. Information will be displayed in the form of interface pictures with some description. Pictures are clear enough, there will be questions - ask.
In order to better represent the subject, please look at the picture:
This is the first thing we see getting into the system interface. Everything is clear and to the point.
After entering the Pravail interface, we get into the Dashboard. All important information on the protected groups and objects is collected here. Where and where most of the traffic goes, what is the load on the interfaces and the system. If necessary, we can do several actions with groups and objects (block, view packages or detailed information about the traffic of the source country). All actions are done in one click, just move the cursor to the object of interest to us and select the action.
The very first and main chart is the current traffic situation in the group. An anomaly in the graph draws our attention. We can look at blocked hosts (reason, time, duration) and make a detailed analysis of incoming packets (packet capture).

TOP-5 hosts of sources and recipients of traffic. Here we see where and where the traffic goes. Host lock (blacklist) and packet analysis are available.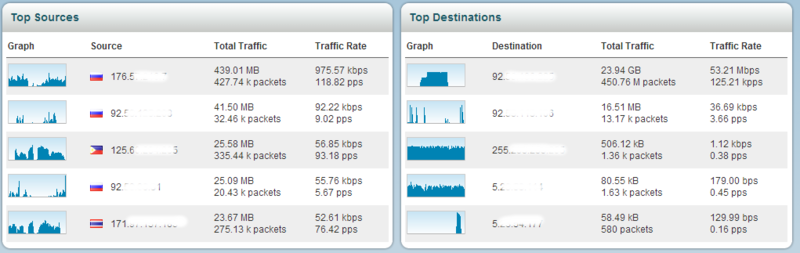
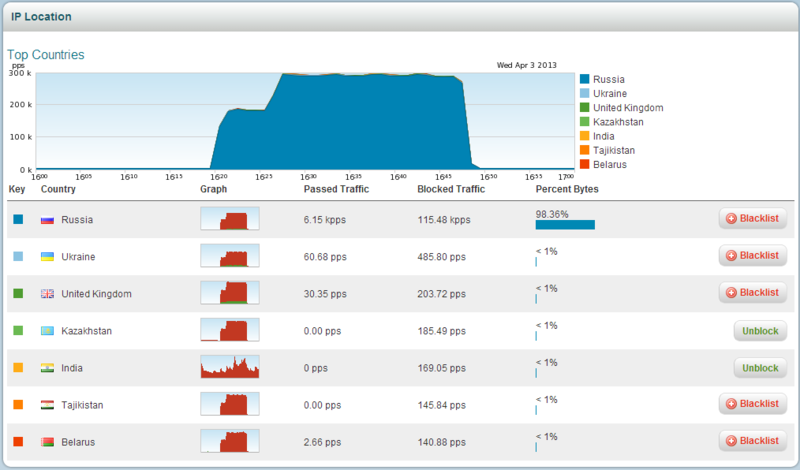
TOP-5 countries of traffic sources (remember geography). It is possible to view traffic details from a country and block it for a specific group.

Interface status, our 10Gb input and output ports. Here we can do a “packet capture” on each interface.

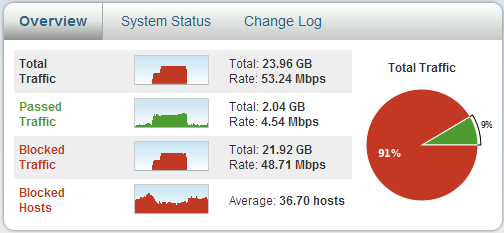
Summary traffic summary. Nothing can be done here.
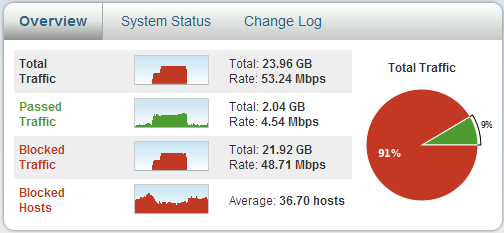
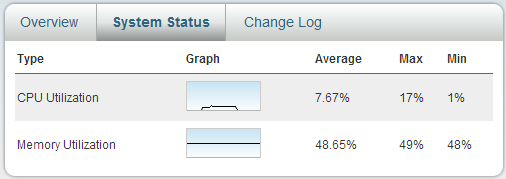
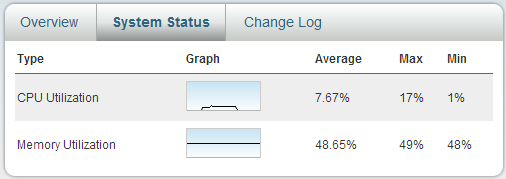
System load: look, think. Assumptions for the future can be made.
Next, we are transferred to the protected group, in our case, this group lists the IP addresses (you can also specify the network) of the protected objects. Inside we will see informative graphs with a minimum of actions regarding objects (ip addresses, countries, links, domains).
Protected group “protos” (we love SC, but the name is not connected =). We see the name, description, protected addresses, type of protection, its duration and the ability to edit the whole thing. You can select the data display period.

Summary of the protected group. Traffic in Mbps and pps, bad and good in details.
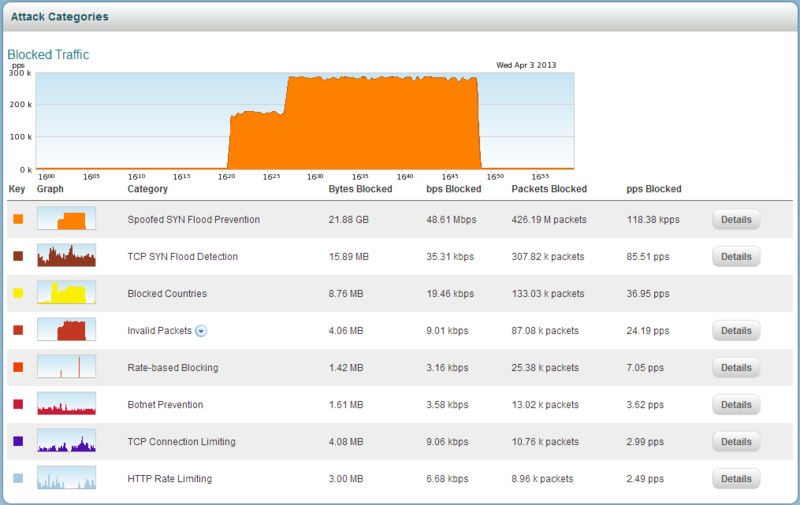
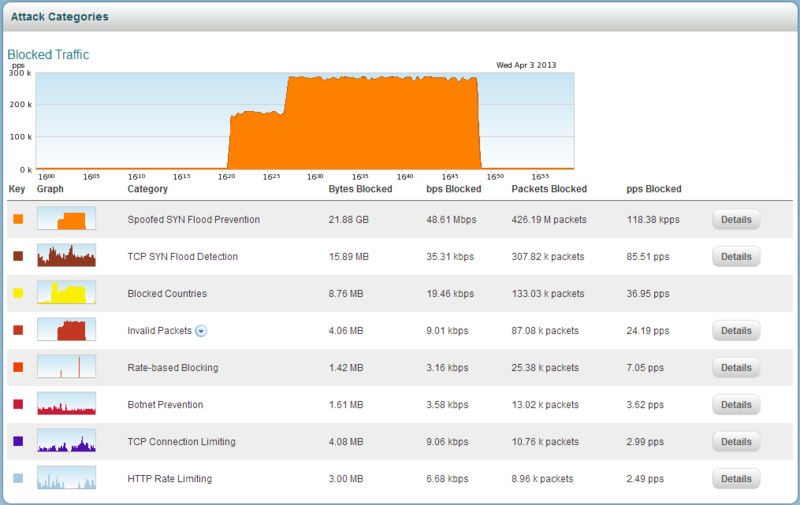
Sources of poor traffic. If necessary, you can look in detail at the "blocked hosts" (blocked ip addresses) of each category. “Detail” reveals to us the details, each category has its own data.
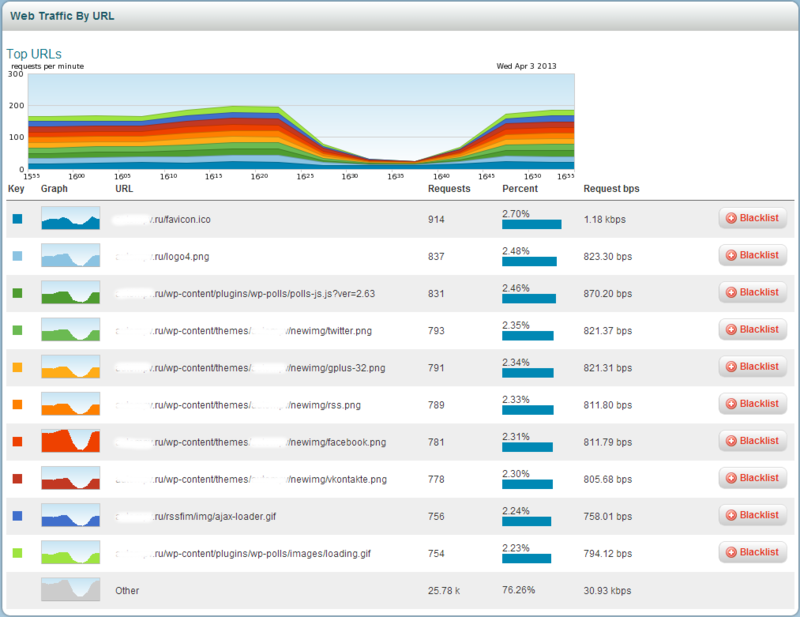
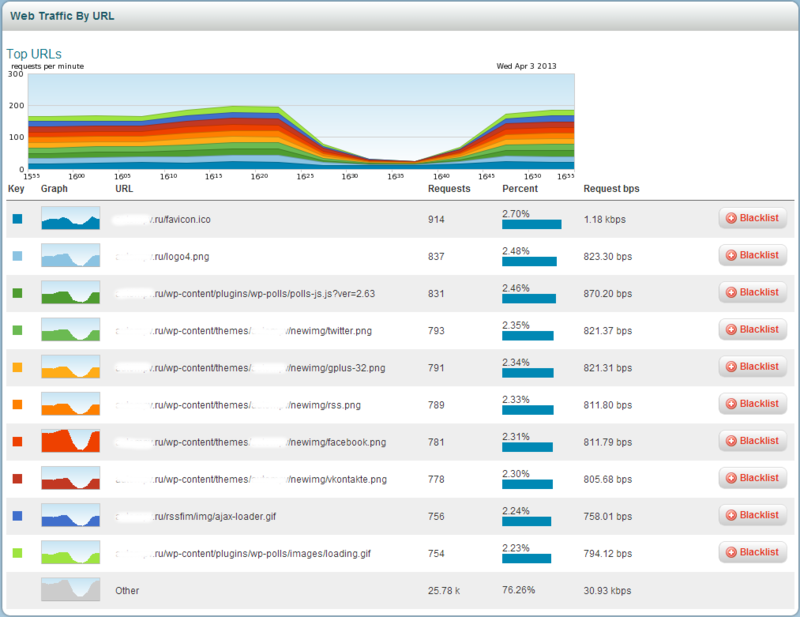
TOP site requests per minute. To the addresses. More requests - higher in the top. You can explicitly close "invalid" requests. Blacklist is triggered earlier.
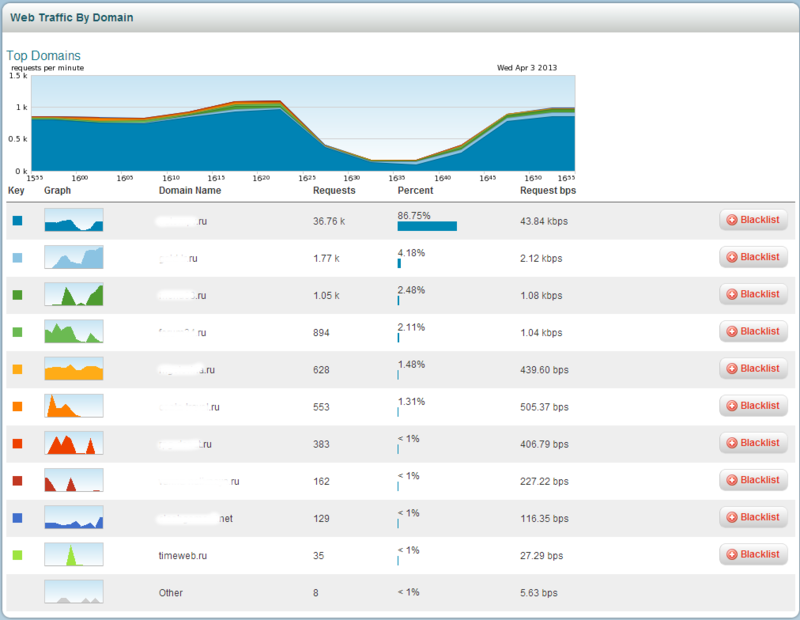
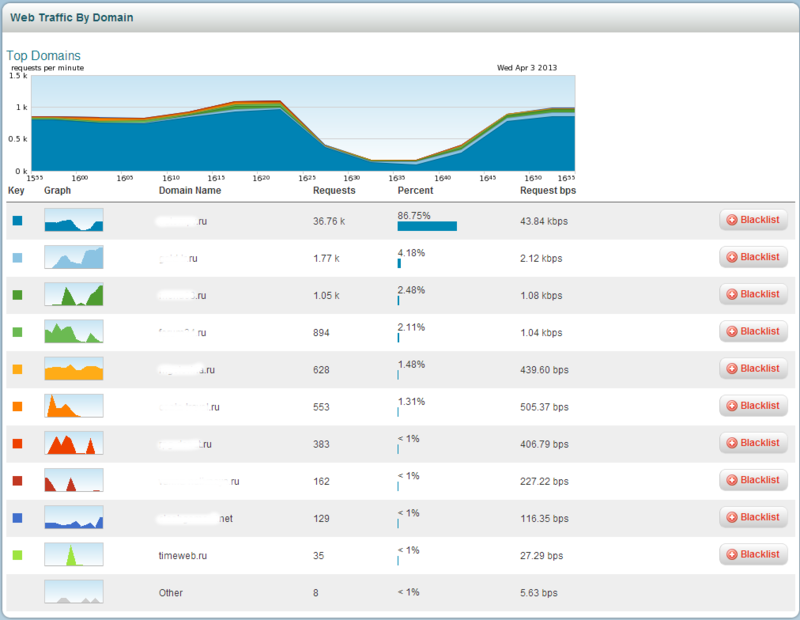
TOP domain queries per minute. Works similar to TOP-url's.
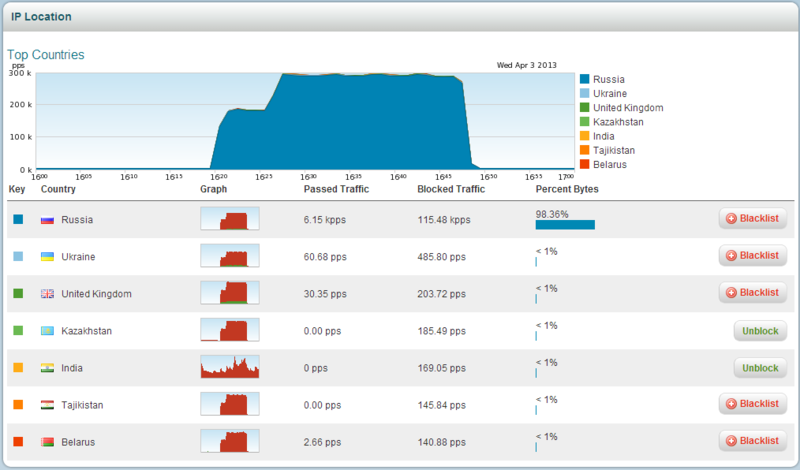
The "best" countries. It is determined by ip address. You can make a “packet capture” for the desired country. My favorite section. Who guesses why? =)
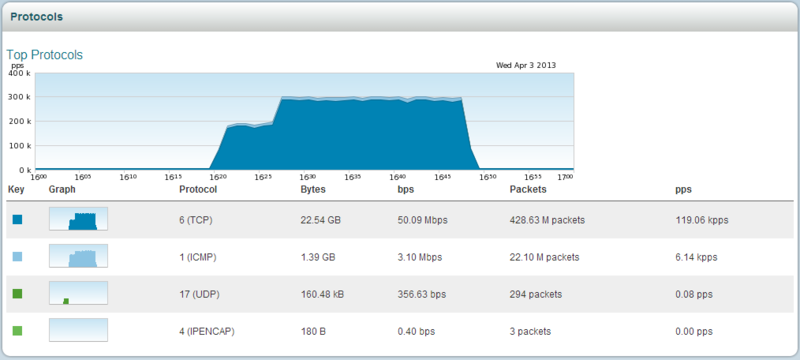
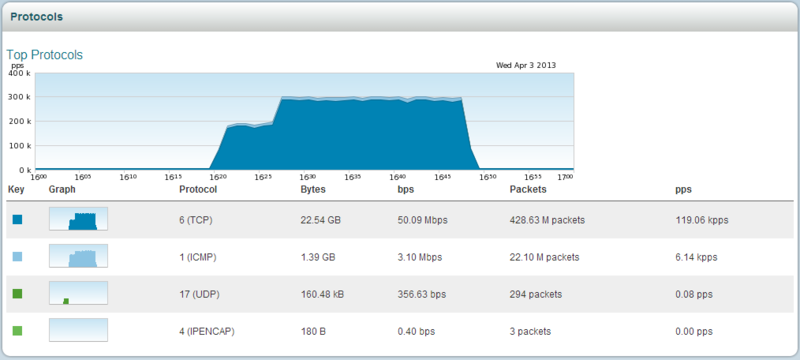
TOP protocols by types, informative schedule.
TOP services. You can also do "packet capture".

TOP-ip addresses. You can watch the reason for blocking or parse packets. If traffic from this address is currently running. And, of course, “whitelist” if the necessary addresses were blocked.

In general, this is all that Pravail gives us to monitor the status of the protected group.
And in the end, we have an excellent enterprise-class device for protecting against attacks on applications, which practically works in automatic mode. Of course, complex attacks will require manual configuration of protection settings.
This device can be safely placed on the edge of the corporate network and / or proactively protect important systems. Practice shows that with some adaptation of the system to the specifics of the protected object, you can achieve a confidently positive result. The protected object under attack will work and pretty well.
Can Internet providers use it? They can, but to protect individual nodes.
Why did we decide to choose Pravail? Because of all the systems that we saw - it was he who left the most pleasant impressions of the work.
And now - we have something to protect ourselves and our users!
Not so long ago, we conducted a comparison of several protection systems against DDOS attacks that we managed to “touch”. As promised - we share our impressions of our chosen device. Here we will not tell you what it is, where and why a DDOS attack is born, we are sure that you already know this. We will consider the practice of using the system in a particular example (there will be many pictures). So, meet Arbor Pravail APS !



Quick reference
Arbor Networks was founded in 2000 at the University of Michigan, whose innovative development was funded by the US Department of Defense. Since then, Arbor has specialized in detecting and processing network threats.
“He” has arrived!
About two months passed from the moment of order to receipt.

An obviously seen box, worn in places, torn in places, sometimes painted with a pen or something else, but is this the main thing ?! Rather - open!
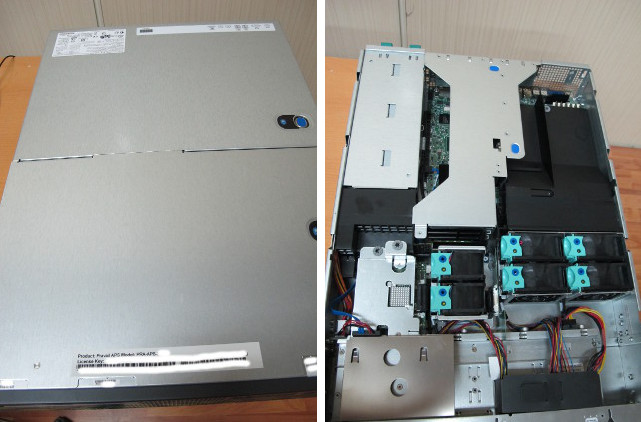
We opened it, it seemed a familiar Intel 2U chassis with a beautiful “face” and we certainly climbed inside to look inside =)

Nothing unusual, two processors, a memory… a design feature was given out by an unusual Silicom network card with a large heatsink, like on a GPU, that heats up , an overseas miracle =)
Enough "pampering", it's time to see it in action!

We connected it to one of our test routers and began to configure. The standard steps are the console, the address on the management port, installing acl, and almost everything. The main thing - do not forget the key to the license, filtering will not =)
In this post, we will not go into particular settings Pravail modes, they are quite simple (groups, filters, parameters), if Habravchanam will be interesting - will do a separate post for each item. In short - Pravail has basic settings for automatic protection of groups, which are based on several types of protected objects (web, dns, mail, vpn, voip, file, rlogin). Each type has a relatively detailed setting with three levels of protection. Switching between levels can be done in one click, at one time, all groups can be protected only at one level.
Let's get down to business!
Pravail vs DDOS = start
DDOS attacks are different, they come to us constantly. It is interesting to look at Pravail in business, is it really as good as the manufacturer says about it, because all manufacturers say only the best about their products, isn’t it? =)
For example, we take a special case from the ordinary life of a regular web server, which we put on a permanent defense “for” Pravail. On this server we practice protecting sites that are attacked by all sorts of not-so-good robots.
Attack start
Day X and hour Y coincided (I did not have to wait long). On our links, we recorded an anomaly, the total “excess" incoming traffic was approximately 3.5Gbit (~ 650kpps), in general this is not a lot by modern standards, spamhaus knows hello to crooked dns servers = \
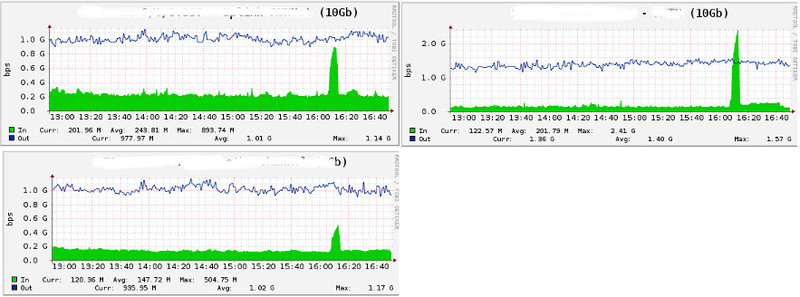
Through various filters on to Pravail in total about 130Mbit and 300k pps “reached”, what kind of traffic is this? Below we will analyze in detail the pictures.
Pravail: The Beginning
Here we look at the reaction of the system to the attack, what Pravail sees and what can or should be done. Information will be displayed in the form of interface pictures with some description. Pictures are clear enough, there will be questions - ask.
In order to better represent the subject, please look at the picture:
Dashboard Pravail APS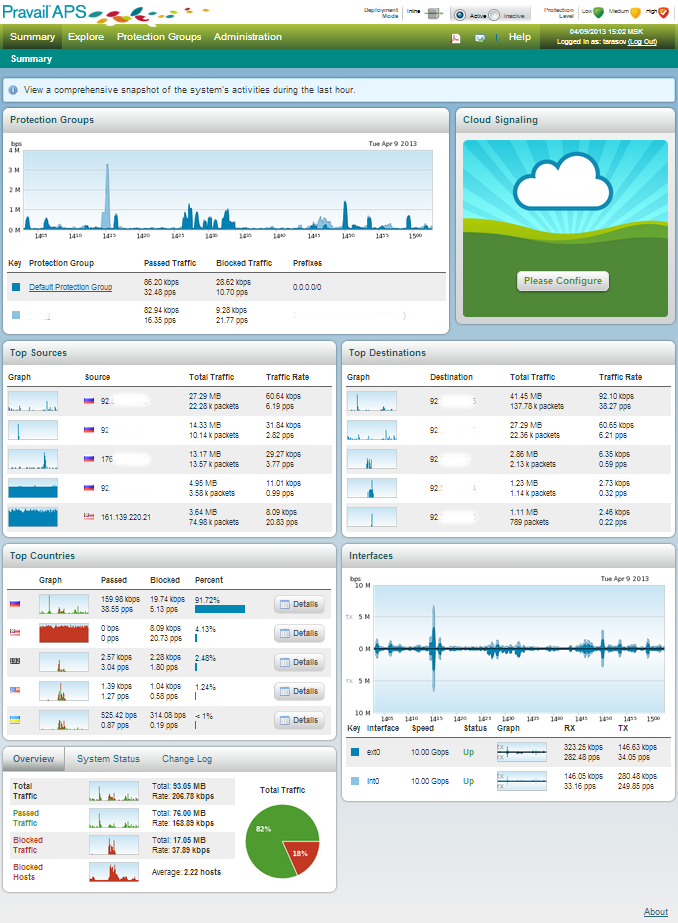
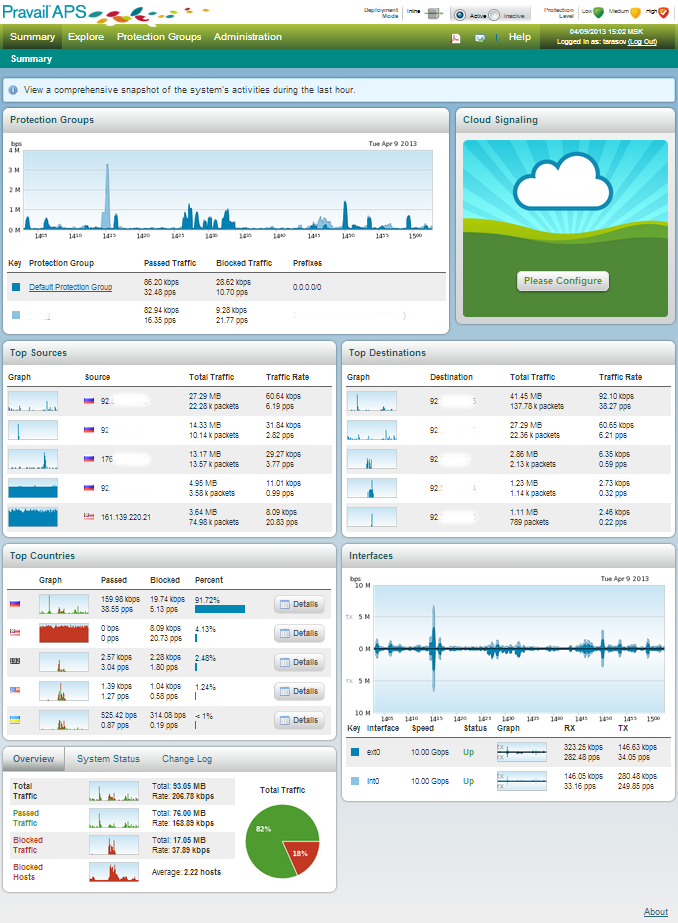
This is the first thing we see getting into the system interface. Everything is clear and to the point.
Look, look, look what I found!
After entering the Pravail interface, we get into the Dashboard. All important information on the protected groups and objects is collected here. Where and where most of the traffic goes, what is the load on the interfaces and the system. If necessary, we can do several actions with groups and objects (block, view packages or detailed information about the traffic of the source country). All actions are done in one click, just move the cursor to the object of interest to us and select the action.
The very first and main chart is the current traffic situation in the group. An anomaly in the graph draws our attention. We can look at blocked hosts (reason, time, duration) and make a detailed analysis of incoming packets (packet capture).

TOP-5 hosts of sources and recipients of traffic. Here we see where and where the traffic goes. Host lock (blacklist) and packet analysis are available.
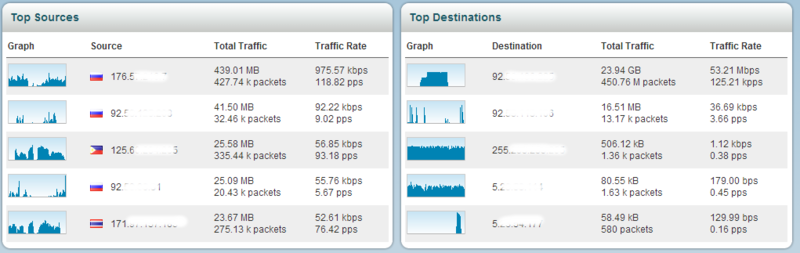
TOP-5 countries of traffic sources (remember geography). It is possible to view traffic details from a country and block it for a specific group.

Interface status, our 10Gb input and output ports. Here we can do a “packet capture” on each interface.

Summary traffic summary. Nothing can be done here.
System load: look, think. Assumptions for the future can be made.
Well, I found it, but what's next?
Next, we are transferred to the protected group, in our case, this group lists the IP addresses (you can also specify the network) of the protected objects. Inside we will see informative graphs with a minimum of actions regarding objects (ip addresses, countries, links, domains).
Protected group “protos” (we love SC, but the name is not connected =). We see the name, description, protected addresses, type of protection, its duration and the ability to edit the whole thing. You can select the data display period.

Summary of the protected group. Traffic in Mbps and pps, bad and good in details.
Sources of poor traffic. If necessary, you can look in detail at the "blocked hosts" (blocked ip addresses) of each category. “Detail” reveals to us the details, each category has its own data.
TOP site requests per minute. To the addresses. More requests - higher in the top. You can explicitly close "invalid" requests. Blacklist is triggered earlier.
TOP domain queries per minute. Works similar to TOP-url's.
The "best" countries. It is determined by ip address. You can make a “packet capture” for the desired country. My favorite section. Who guesses why? =)
TOP protocols by types, informative schedule.
TOP services. You can also do "packet capture".

TOP-ip addresses. You can watch the reason for blocking or parse packets. If traffic from this address is currently running. And, of course, “whitelist” if the necessary addresses were blocked.

In general, this is all that Pravail gives us to monitor the status of the protected group.
What is the result?
And in the end, we have an excellent enterprise-class device for protecting against attacks on applications, which practically works in automatic mode. Of course, complex attacks will require manual configuration of protection settings.
This device can be safely placed on the edge of the corporate network and / or proactively protect important systems. Practice shows that with some adaptation of the system to the specifics of the protected object, you can achieve a confidently positive result. The protected object under attack will work and pretty well.
Can Internet providers use it? They can, but to protect individual nodes.
Why did we decide to choose Pravail? Because of all the systems that we saw - it was he who left the most pleasant impressions of the work.
And now - we have something to protect ourselves and our users!
