MIT course "Security of computer systems". Lecture 5: "Where Security Errors Come From", Part 2
- Transfer
- Tutorial
Massachusetts Institute of Technology. Lecture course # 6.858. "Security of computer systems." Nikolai Zeldovich, James Mykens. year 2014
Computer Systems Security is a course on the development and implementation of secure computer systems. Lectures cover threat models, attacks that compromise security, and security methods based on the latest scientific work. Topics include operating system (OS) security, capabilities, information flow control, language security, network protocols, hardware protection and security in web applications.
Lecture 1: “Introduction: threat models” Part 1 / Part 2 / Part 3
Lecture 2: “Control of hacker attacks” Part 1 / Part 2 / Part 3
Lecture 3: “Buffer overflow: exploits and protection” Part 1 /Part 2 / Part 3
Lecture 4: “Privilege Separation” Part 1 / Part 2 / Part 3
Lecture 5: “Where Security System Errors Come From” Part 1 / Part 2
Filling in the credentials in iframes significantly increases the scale of the attack, and visiting a malicious page can very quickly compromise large sets of credentials.

Security researchers have discovered the vulnerability of unverified password managers, such as Chrome extensions for Windows , and later research by researchers, including those from MIT , revealed the vulnerability of the LastPass extension for the Safari browser .
Consider cross-domain queries. Do you think it is possible that the authorization form filled out by the password manager on https: // example.com would be submitted for logging in to the sitehttps: // www.isecpartners.com , can the password manager transfer data to a third party? Yes, it can, and this makes it possible to find a vulnerability or function that allows an attacker to create a domain login form, after which the malicious login form is sent to the authentic site https: // www.isecpartners.com .
Keep in mind that all verified password managers safely send passwords to different domains.
What is true for domains is also true for subdomains. A feature of subdomains is that their “sensitivity” to security can be very different from the security checks performed by domains. Subdomains such as blog. * , Forum. * Ormail. * may have completely different security requirements. Processing subdomains as domain equivalent increases the attack surface. It should be borne in mind that all verified password managers considered subdomains to be equivalent to the domain page.
It is necessary to carefully approach the identification of login pages. Internet applications change, and this causes the login pages to move. Therefore, their authenticity should be checked even more carefully than the authenticity of subdomains.
It should be borne in mind that most web applications have a small set of login pages. They can be linked with each other so that the appearance of the login page triggers autofilling or form auto-sending to one main domain. In doing so, the password manager will fill in any form of authorization for any meeting subdomain.
The attack vector in this case can be HTML email . For example, Google , Yahoo and Outlook use such a thing as filling out an online form. The slide shows an example with the following text: “if you have difficulty filling or sending this form, you can fill it in online at this link” and a link to the form that directs the user to the domain is provideddocs.google.com . And further on the page it says: “Never send passwords using Google Forms!”
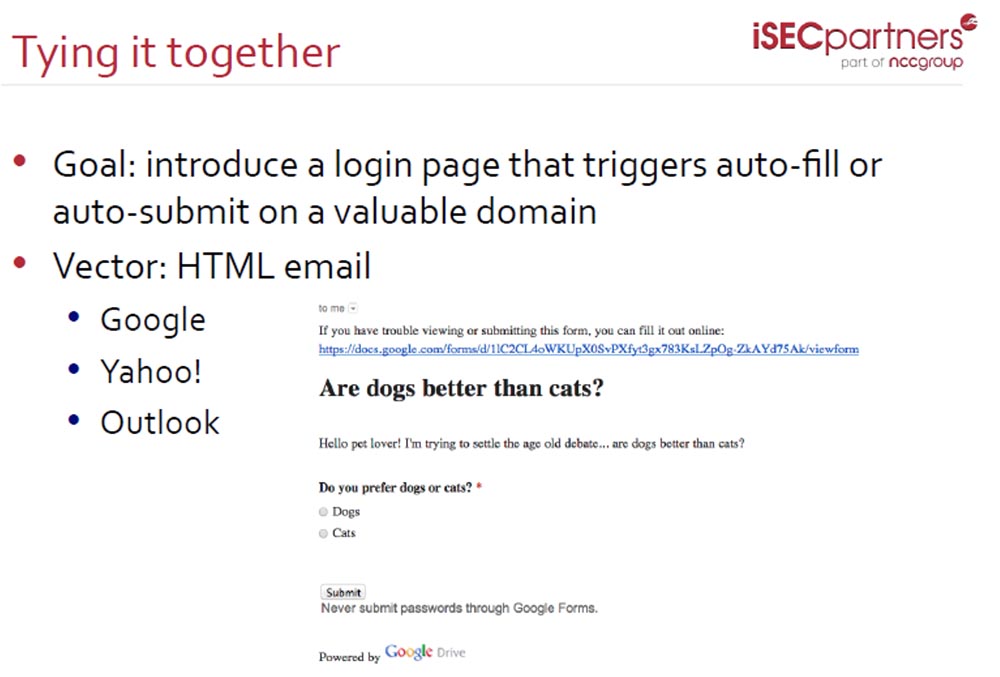
As people often use mail to send forms, attackers have focused on the users of these three services. You fill out a form, for example, answering questions from various surveys, and use your inbox to send it. How do these services resist attacks?
It is best opposed to Outlook hackers ( live.com ). It prevents the possibility of an attack by prohibiting the provision of any original material to a third party, including forms and personal information of users. Google ranks
second, which simply warns users against performing such actions, which does not exclude the possibility of password theft.
Yahoo allows you to steal passwords without warning.
The danger of the built-in autofill mechanism and the creation of authentication forms is that services do not always warn about the danger of sending them to a third party or the danger of using these functions on the pages of other Internet resources. For example, when passing the above survey, there is a suspicious function Submit . Answering the question who is better, a dog or a cat, and clicking on the Submit button , you not only confirm the answer you have chosen, but at the same time you confirm the sending of your login and password to the attacker.
YahooIt is the worst security service, especially if you use LastPass password manager .
Mobile versions of browsers are protected even worse. There are no extensions here, but security researchers have discovered a plugin for the mobile version of the Chrome browser called Javascript Bookmarklets . It runs a fake security code on hostile sites you visit. In fact, it masks their danger, creating a sense of false security that can cause you great damage.
You can familiarize yourself with other browser extensions and find out the results of research into attacks and password protection using the links of organizations in the field of security research Berkeley and Joint Stanford.
I want you to understand: having familiarized yourself with the basics of the work of password managers, you yourself can find almost all the security errors of these applications.
You need to understand what kind of functionality the developer laid out in the application and how it works in practice. If you do this, it will be much easier for you to find vulnerabilities.
Consider a TLS attack called CRIME , which is short for Compression Ratio Info-leak Made Easy . This is a security exploit that allows you to decode HTTPS sessions , including custom cookies, by intercepting encrypted traffic between the server and the browser. All versions of TLS , including TLS 1.2 , are vulnerable..
During this attack, the hacker intercepts user traffic, adds its data to it and sends requests to the server. The compression algorithm when repeating part of the text compresses it. After sending data to the server, the hacker looks for the length of the message and if it has decreased, then the correct sequence is selected. Thereby it is possible to select individual lines and parameters in the request, for example, cookie values.

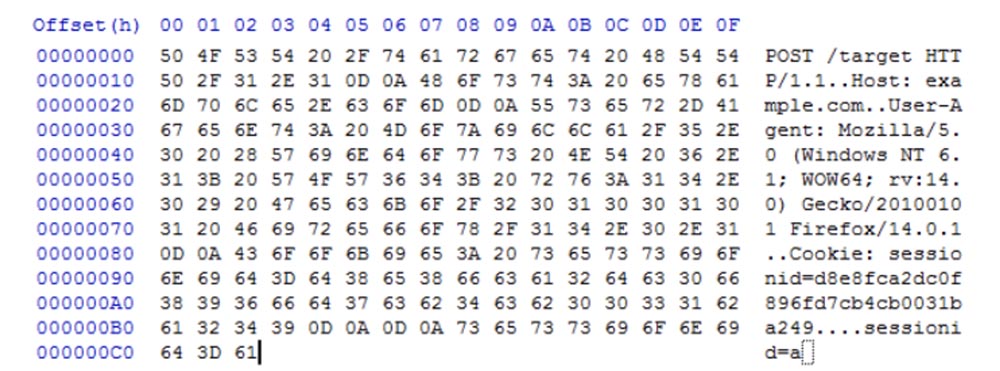
This attack is based on the fact that your browser interacts with the site using an internal interface - the HTTP protocol. At the same time, if I go to the site example.com , the browser sends it my cookies with all the information available in the previously completed authorization form, including the username and password. In HTTP form, it looks like this:
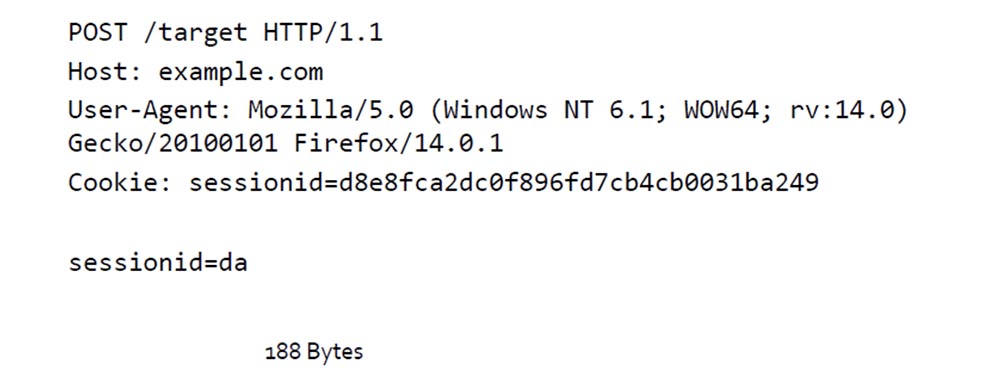
Even if the data is protected by an SSL / TLS connection , I can still get some of the information if I own the network. Here's what the SSL information looks like :

Here I see this information: the transfer time, who the message is sent from, that is, the user's IP, the message to whom the message is sent, that is, the recipient's IP, and the length of the message.
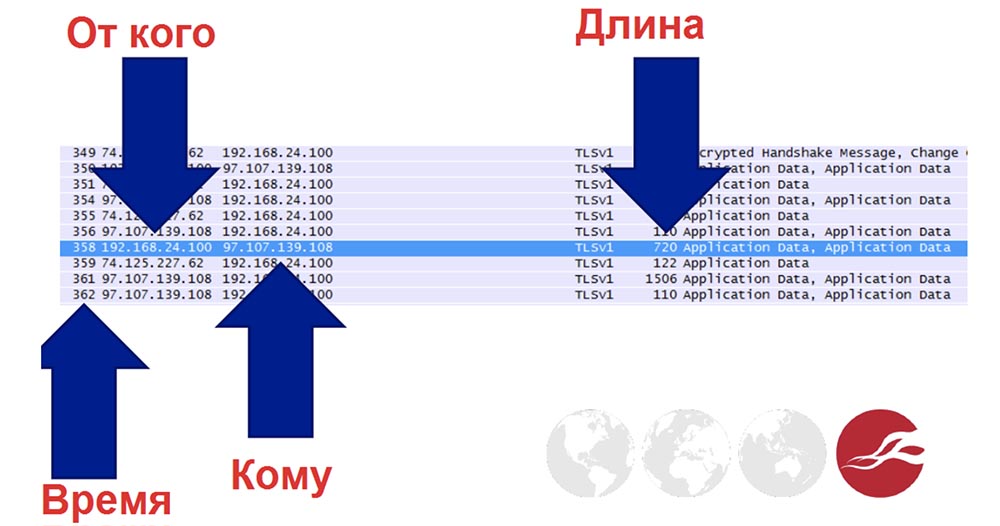
Such is the design of the cryptographic protocol of SSL protected sockets level . If you have the ability to analyze traffic, this data provides a huge field for malicious activity.
Consider the message that the browser sends.
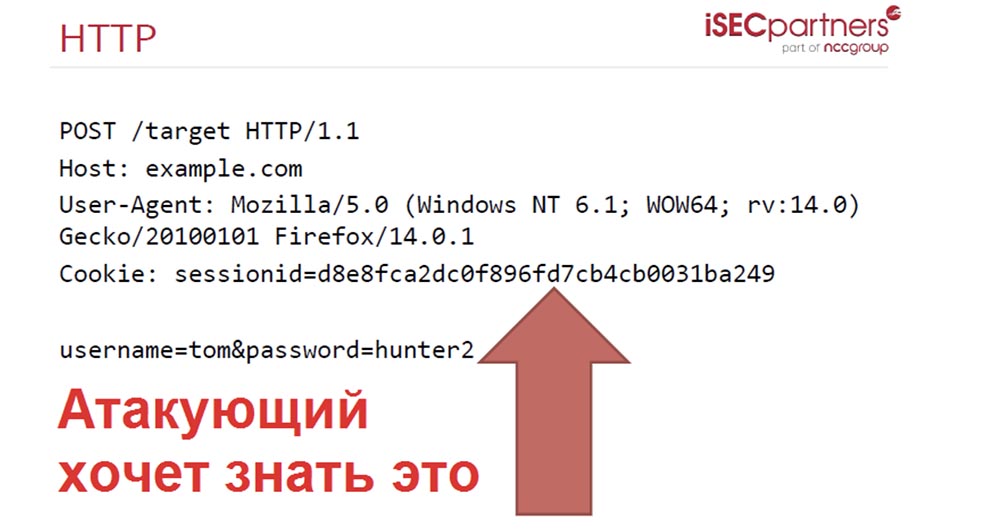
If the browser allows you to make cross-domain requests, it will send the request with a cookie containing the form data to any site that will be redirected to by an attacker, for example, example.com. If an attacker captures these cookies, he will be able to control the following parameters:

In order to guess the user's password, I start selecting the parameter for the line username = tom & password and instead of hunter2 I enter the letter a .
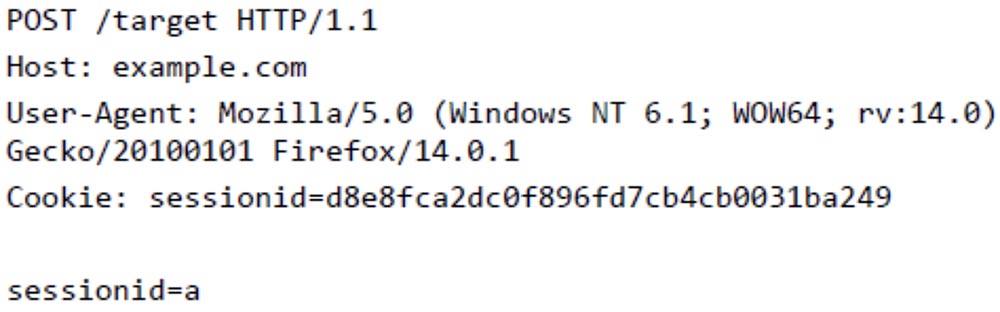
Then I look at the HTTP decryption and see that this parameter takes 195 bytes.
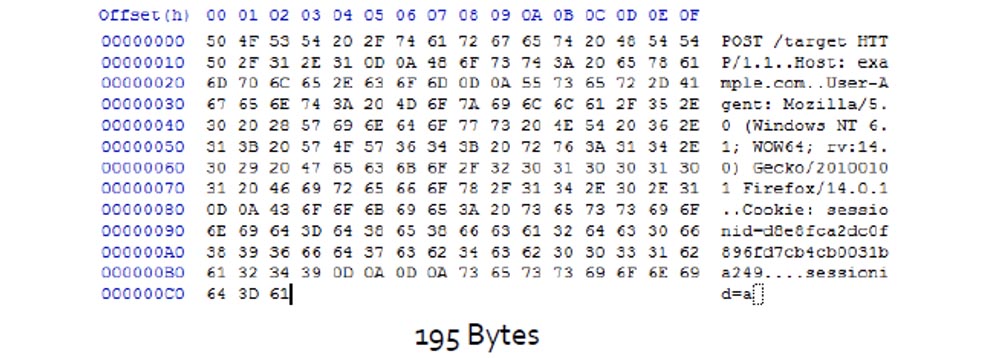
To make things easier, the hacker uses TLS compression.. The compression algorithm, when repeating a part of the text, compresses it, and the compression creates markers for these parts and places them in the form of an HTTP message .
In this case, the session ID is equivalent to the parts of the code marked with the corresponding marker, and the size of the compressed message is 187 bytes.
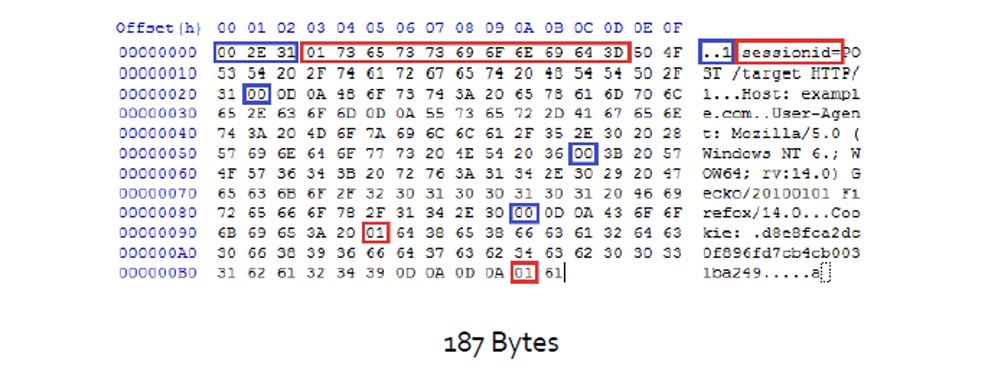
What happens if I equate session ID = d ?
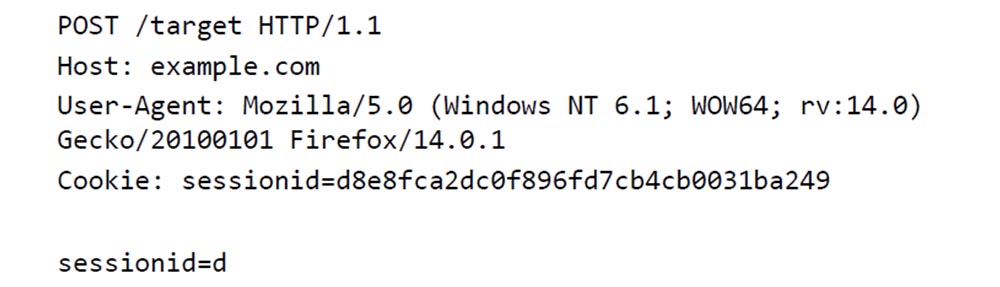
The message size is reduced because it needs to compress more bytes. This can be seen if we compare the number of arguments surrounded by a red frame in the 2nd line above.
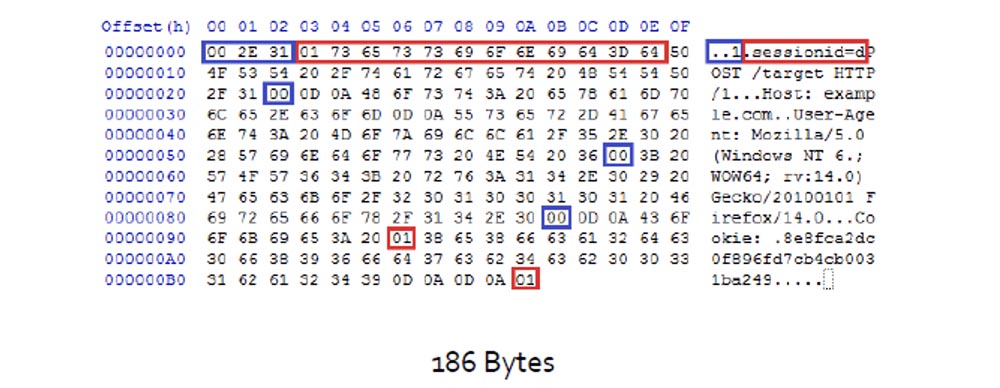
This is what the attacker sees. He sees that the message is compressed, and because of this he finds out that he guessed the first letter in the session ID . Then it replaces session ID = daand gets the message size 188 bytes.
So, successively substituting letters and numbers and analyzing changes in message size, he guesses the entire session ID . That is, it selects not the encryption key, but the content of the encrypted message itself.

In order to deal with CRIME , it is necessary to prohibit the browser to perform TLS compression . It is also necessary to change the SPDY protocol so that when the secret data is requested they are compressed in a separate context.
Consider HTTP violation cases . HTTP responses that come to the user after accessing the server may contain such secret data as CSRF tokens.or other confidential information. Attacks like CRIME require the knowledge of at least one secret session prefix and the ability to enter their data in the response message.
You can prevent an attack by banning the compression of responses or drowning out a CRIME attack , since this attack uses the MiTM principle (man in the middle) and can "bring down" actual requests. This is a content “noisy” attack that can be detected, since the attacker usually does not communicate directly with the server, but uses access to the router, and the server may even be “unaware” about the attack.
You can also protect yourself by placing various secret information in various files, such as javascriptHowever, this is difficult to implement in practice and it is also difficult to modify existing applications for this.
You can try to randomize sensitive information in requests, mainly for CSRF tokens , but this method will lead to a dramatic drop in performance.
Knowing the principles of application operation and vulnerabilities, you are able to "bring down" the entire Internet: SSL / TLS , DNS , DNSSEC / DNSEC , IPv6 , this is quite feasible.

And now I want to talk about a very big player in the field of security - the NSA , the National Security Agency, or the NSA. These are people who often create security problems and solve them themselves.
For some things I’m ready to hate them. However, NSA employees are not able to change the current policy. They contribute to the intellectual development of everything related to security, and I hope they believe that the result of their work will be used for good purposes.
In their work there are two sides of the medal, but this is only my opinion and it may not coincide with the opinion of my employers. And I think that not all the research data that I will tell you about is officially declassified.
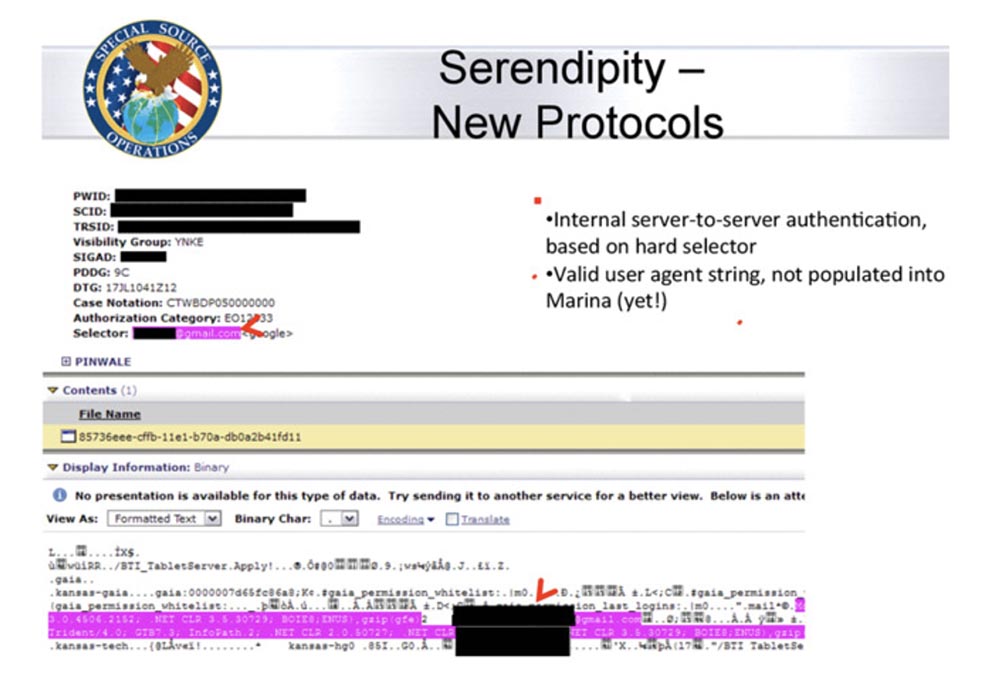
Snowden said that some statements can be proved as true, and some as false. An example of a false statement is the NSA 's statement that "there is direct access to Google networks”Because the true state of affairs with access to these networks is shown in the following figure, which the NSA itself did. Google
is currently encrypting all of its traffic because it’s worrying that someone can hack their network. In addition, all news is filtered through the media, and we see only excerpts from the documents. You see a smiley next to the phrase “ SSL is being added and removed here on the head server of Google ”, because it is from here that the NSA can extract data. Google
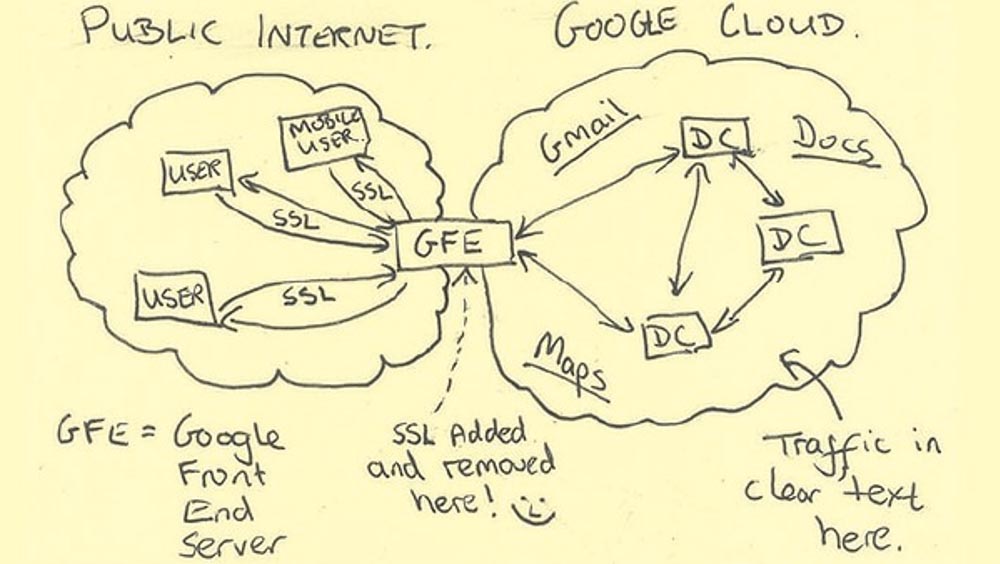
which has data centers around the world, makes extensive use of dedicated fiber optic lines for its networks. Due to this traffic is transmitted at high speed and it is very difficult to get to it.
The government has not only great technical capabilities, but also leverage. Some companies find it very difficult to resist coercion to cooperate with the government. An example of opposition to the state is the free email service Lavabit , created as an alternative to Gmail , because the latter violated the privacy of user correspondence requested by government services.
The state may also force companies not to publicly acknowledge that they cooperate with government services.
Consider the tools that the state has to implement security policies.
First of all, it is SIGINT - the Worldwide Protective Cryptological Platform. It is based on fiber-optic networks. The following site shows a diagram of a highly secret document published by Snowden. You see on it a lot of yellow dots, marked as CNE. Snowden assumes that equipment for hacking networks is located in these places. Their number is over 50,000 worldwide.
Networks can be hacked in a variety of ways. Government uses supply chain attack for this- Cyber attacks that target the least protected elements in the networks of various organizations. In order to protect themselves against such attacks, the government avoids cooperation of any kind, providing only direct access to its own networks, without any intermediaries and third parties.
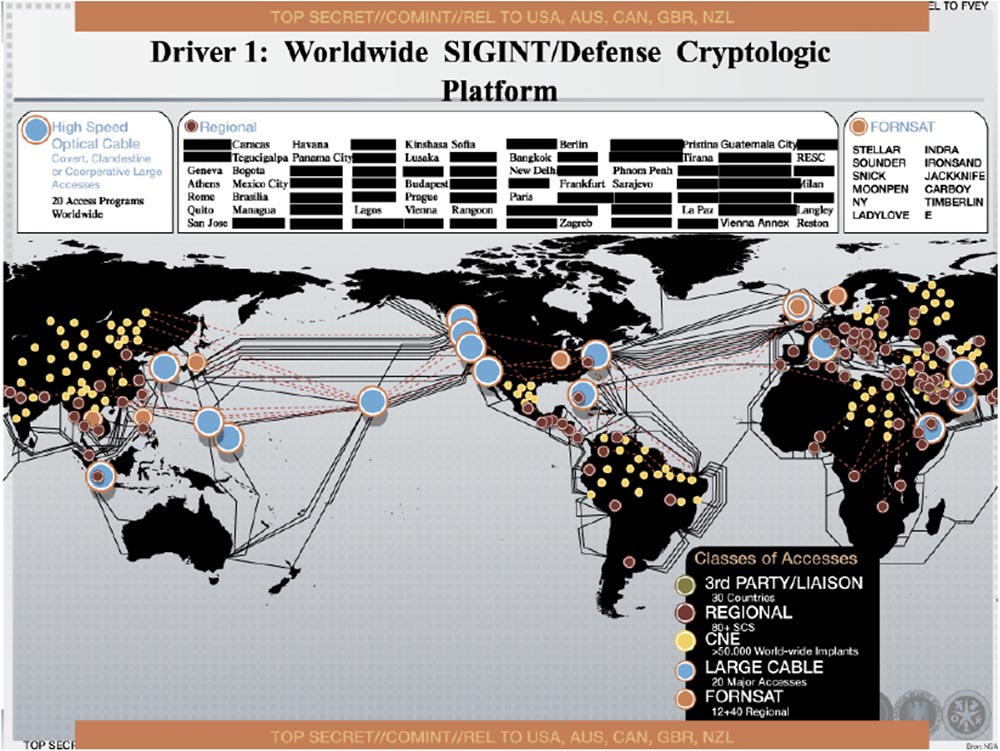
According to the non-governmental organization EFF (Electronic Frontier Foundation) and the trials initiated by it, the NSA loves to use the so-called “optical switches”, which allow to intercept telephone conversations, including from MPLS and prevent the intermediaries from leaking target information. The majority of intermediaries involved in the transfer of information between users not only in the US, but around the world are involved in this.
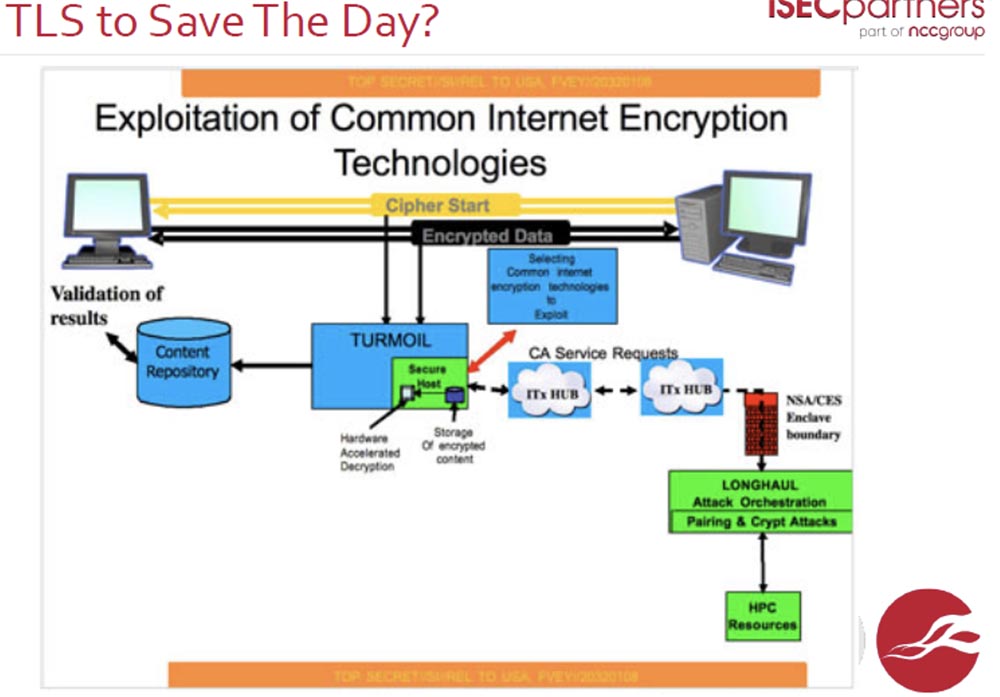
I hope thatTLS can counter this intervention.
The government is able to compromise even the internal network infrastructure using Pokemon’s private end- point encryption keys . This allows you to organize heartbleed attacks and standard network attacks. The government often uses the DOD networking model developed by the US Department of Defense. Such a system is used in google.com networks .
It is possible to use crypto attacks against TLS . The Stuxnet computer worm is supposed to infect Windows computers ., was developed at the initiative of the US government. It uses a conflict within the MD5 encryption algorithm that has a valid certificate. This worm intercepts data between controllers and logical stations and can interfere with the process of automated control of various industrial complexes. It is the only virus capable of destroying the physical infrastructure of networks.
There is an NIST organization that develops encryption standards for virtually everything. She recommends using a cryptographically secure pseudo-random number generator to create encryption keys. DUAL_EC_PRNG. However, it still has vulnerabilities. If you use the elliptic curve points specified in its encryption standard, then due to the large number of output bits per generation round, it is possible to penetrate the generator code and crack it using the brute force method . The creators of the algorithm were aware of this vulnerability from the very beginning. This does not mean that a backdoor was originally provided for in this generator, but it means that a backdoor can be created there at any time.
Note that NSA most often uses attacks based on contradictions within the latest MD5 encryption algorithms .

The state has a global impact on the Internet around the world. Most of the world's communications is carried out through the USA. Telephone conversations, e-mail and chats are carried out on the cheapest ways, not physically always direct, and you can always follow this path. Most of the world's Internet traffic passes through the United States. In any case, the way in which communication is made with the ultimate goal of your contact can easily be redirected to the United States, that is, the state can control any telecommunications flows around the world.
I will give an example of the “return” from such activity. The state intervenes not only in the communications of private persons, but also in the work of companies. In November 2013, the Washington Post published information that the NSA intercepts traffic between data centers.Google via fiber optic cable before it is encrypted between end servers and users' computers. Were published additional data on the government program MUSCULAR and fragments of packets stolen from the internal network of Google .
Employees of Google confirmed the fact of hacking into their network by the NSA, not being embarrassed in expressions - Google security specialist Brandon Downey directly wrote: “Fuck these guys!”, Meaning the unprecedented impudence of the NSA .
Therefore, it is difficult for people to trust US network equipment and services provided by US network providers. I will quote Cardinal Richelieu's words: “Give me six lines, written by the hand of the most honest person, and I will find in them something for which you can hang it.”
I do not want you to become paranoid in the sense of distrust to the government and have seen total espionage and breach of confidentiality of information and privacy. But as future software developers, you need to know how an attacker can act. If you work in a large company, a hacker can use government tools and techniques to organize an attack. So you need to do such useful things as Google does .by encrypting all your internal traffic and using penetration testing certificates.
I want to introduce you to several other types of malicious software. One of them is called Flame , or Flame.
We can say that this spyware is a cousin of the Stuxnet worm . It is capable of doing such crazy things as:
- delete all GPS tags from your photos on your computer;
- steal a list of your contacts through any phone connected to your computer or smartphone via Bluetooth;
- Take screenshots of your device, intercept keystrokes and record spy audio.
Flame does all this thanks to cracking MD5 hashes , in which it was possible to find contradictions, in particular the conflict of the chosen prefix. This was demonstrated by cryptographers in 2008, when they managed to create a fake CA- certificate, posing as a genuine certificate from RapidSSL . They managed to detect a vulnerability in the Internet Public Key Infrastructure (PKI) used to issue digital certificates for sites.
To generate a fake certificate, 4 purchases of valid certificates were made from RapidSSL . The search for this vulnerability required a 3-day conflict attack, produced using 215 Sony PlayStation 3 stations. After a general panic resulting from the publication of this information, CA authentication centers generally refused to use the MD5 encryption algorithm .
I note that Microsoft has forgotten about one of its Microsoft Terminal Server , which still uses MD5 certificates . The attackers are constantly looking for new ways to detect vulnerabilities in MD5 , and for them some difficulties are represented by the fact that the window for intercepting the timestamp appears only for 1 ms. However, creating just one arbitrary fake Microsoft root certificate allows an attacker to sign anything, such as Windows updates .. Thus, by contacting the MS server for updating your software, you risk catching Flame at the same time , since the update will have a legal signature. This case is especially interesting for me because it is an example of how a very good mechanism for updating software can be used by an attacker due to the presence of a security vulnerability.
And now we will consider the last question of our lecture - what should I do if I like to do computer security? First, you need to know what the concept of ethics in security means and figure out possible career directions.
Historically, there is always a debate on the topic “Responsibility or full openness” in the world? These disputes are switching to the “Openness or sale of weapons?” Plane, because in our time, the disclosure of protection technologies and the universal availability of confidential information is tantamount to free trade in powerful weapons.

The responsibility is to find vulnerabilities in software vendors, fix them and publish the results. The main thing here is to eliminate the vulnerability before it becomes known to a wide range of people.
Openness sounds great, but disclosing one's own company's vulnerabilities, especially if it is a major security researcher and spends a lot of money on it, is hardly appropriate. But nowadays, companies are fairly quickly organizing the elimination of vulnerabilities, so they must be honest with the users of their products and promptly disclose useful information about vulnerabilities and how to solve the security problem.
You should adhere to the following ethical principles and remember the following:
- You can use the “black market” of vulnerabilities and use hacker techniques only to use the information obtained for the benefit of solving security problems;
- Think of jailbreakme.com , which uses iOS vulnerabilities to gain root rights on mobile devices. If you visit this site, your phone can be immediately hacked, the hacker will get the rights to remotely control your device and be able to do anything with it, and you won’t even know about it;
- The most profitable way to become a hacker is to sell malicious exploits, however, you are playing the role of an illegal arms dealer, because you do not know who you are selling your exploits to and why they will be used for;
- be very careful in your activities, because the boundary between malicious hacking and noble security protection is very thin;
- Remember that there are many ways to earn money honestly, so refrain from the temptations to use the knowledge you have obtained to the detriment of others.
Security careers should be based on ethical principles.
Focus your work on ethical principles, but not vice versa. Write software provided with the necessary security. Create password managers that work great. Create encryption solutions that work great. You can make a lot of money if you develop solutions that are in demand everywhere.
Write more secure software. Remember that you can understand all the vulnerabilities, this is a very clear thing. You must fully understand how the system works, how system calls work. You should know what can happen in case of unforeseen situations, what to expect from them and how they will affect the operation of the system.
If you create a large-scale, extensive picture of the system, you will understand how all its components interact with each other. In order to understand how to use the vulnerability of the system, try to imagine yourself in the place of the criminal.
You can make a criminal career or a career as an academician, depending on what you have a greater inclination.
You can become an independent security researcher or penetration tester - pentester.
I’ll tell you what pentester does in our company iSEC Partners:
- every 2 to 3 weeks, it finds about 20-30 new companies and will test a wide range of technologies on them. For myself, I will say that in the year I worked at the company I learned more about security than during all the time I studied at MIT;
- conducts fascinating research while at the same time being a pentester and a security researcher;
- has a great influence in making the world safer;
- spends most of the time in thinking and improving, because he constantly trains his brain by solving a wide variety of security tasks;
- See how we work at Friday's Open Day!
You can email me at paul@isecpartners.com . We still have a couple of minutes, and I will try to answer your questions.

They ask me about the hardware modules for security. Yes, this is the latest security solution, which is a safe "iron". We can say that this is a box that stores sensitive information. You can use this information, but it cannot be extracted from this hardware. This solution is based on the hardware and technology of IBM .
I can say that such a solution to protect networks that have billions of users will be too expensive. You will need to provide personal encryption keys for each individual connection to the server of each user. Therefore, this solution currently does not scale so that, for example, to satisfy the needs of Facebook , Google or Yahoo users and optimally for small local networks of various companies. There are people who provide security at the micro level, and people who provide security at the macro level.
Thank you very much for your attention!
Full version of the course is available here .
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending to friends, 30% discount for Habr's users on a unique analogue of the entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to share the server? (Options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read aboutHow to build the infrastructure of the building. class c using servers Dell R730xd E5-2650 v4 worth 9000 euros for a penny?
