Features of national information security
Rereading one discussion in the Ukrainian group of information security experts on LinkedIn, I could not resist and expressed my thoughts about this in a short article. After a couple of timid comments, the moderator closed the topic, because in his opinion it does not lie in the information security plane. I do not think so. That's actually what I think about this.
Business ethics (I'm not talking about morality, morality is a little different) - what is it? Why is this needed? How to use it? How do you monetize your business ethics? After several rather large banks rained down almost two years ago, the problem of business ethics came up a bit, but then drowned as unnecessary. I’m saying that several commercial institutions with a high reputation monetized it at the same time using the “Hop!” Method. Withdrew funds from the troubled asset and transferred the debt to the shoulders of ordinary people.
Gilenko hardly built the bank "Nadra" with the goal of "throwing" a certain number of depositors. But when it became clear that, honestly, the bank was “not a tenant”, the decision was made “save as you can”, and the owners of the rescue equipment had more than ordinary investors. A reputation that has been built up over the years has been converted to wholesale in profit. And it can be in any business.
But I'm not even talking about business ethics per se. I want to talk about simpler things - about information security (IS). In carrying out our work, we are creating various information security systems. What are we guided by when creating them? What do we write in the section of the ToR “Basis for Development”?
We write: “Regulatory documents”, “Industry standards”, “Modern technologies”, “The market of specialized equipment and software”, “Best practices”, “Experience in the implementation of such systems”, something else. But we think: "Maximum profit."
Many times I have come across the fact that many IS tasks can be solved by administrative and operational measures, but to solve them, expensive equipment was purchased and no active administrative and operational measures were taken. Someone will ask me why? Or is it clear to everyone?
Both sides - the Customer and the Contractor, in the person of those responsible at each level, sit around a clearing with the name “Information Security” (the same is true for IT in general) with only one thought - “so that we have the most and there is nothing for us ".
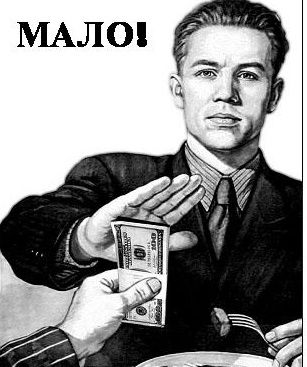
Now I do not want to talk about the competition between integrators or specialized companies (market players - residents) and the role of kickbacks in it. Although now, even in competitions between vendors, kickbacks often become key factors. Kickbacks have become the largest (I hope that they are not yet market-forming, although no one keeps statistics) the “driver” of the IT and information security business. IT and information security have become sticky fish on the body of production, trade, and the service sector.
Once I asked one successful sales manager - “has he recently had sales without kickbacks?” - in response, I heard a long pause, and then some ornate explanation of why kickbacks are not as bad as it seems at first glance .
Even if you make your face a brick and your lips a bow (that is, ignore the issue of kickback ethics - many work at lower rates, because the employer believes that IT / IS employees themselves will steal the rest), the question of the optimal planning and use of IT / IS remains budgets.
I want to talk about how rollbacks make our IT and information security solutions not optimal. The choice of decisions is often determined by inflating budgets and kickbacks, and not by technical characteristics. In one large private (!) Enterprise, I observed a picture of how two different network security systems were built over the years by two different departments (with this money one could be built, but twice as functional). Almost every department had its own server, in the ITC there were more than one SAN system.
Moreover, few people think that once sitting on the rollback needle, a specialist involved in making a procurement decision cannot remain objective in choosing IT / IS solutions. After all, if he wants to “jump” from a non-optimal vendor in favor of another (they also give kickbacks) of a more optimal one, then he can “crawl sideways” - he is at risk of divulging information about kickbacks, losing the reputation of a specialist. Now IT / Ibshniki cope with this through regular rotation (change of job), but the essence remains the same.
In total, an interesting thing comes out - the IS service at the enterprise (part of the SB) should protect the business from economic damage, but who will protect the business from the IS service? What are your thoughts on this? To steam or not to steam about this? Or am I so angry because I didn’t have a bike before?
PS Yes, there are people to whom the above does not apply, I am aware, but I'm not talking about them.
Business ethics (I'm not talking about morality, morality is a little different) - what is it? Why is this needed? How to use it? How do you monetize your business ethics? After several rather large banks rained down almost two years ago, the problem of business ethics came up a bit, but then drowned as unnecessary. I’m saying that several commercial institutions with a high reputation monetized it at the same time using the “Hop!” Method. Withdrew funds from the troubled asset and transferred the debt to the shoulders of ordinary people.
Gilenko hardly built the bank "Nadra" with the goal of "throwing" a certain number of depositors. But when it became clear that, honestly, the bank was “not a tenant”, the decision was made “save as you can”, and the owners of the rescue equipment had more than ordinary investors. A reputation that has been built up over the years has been converted to wholesale in profit. And it can be in any business.
But I'm not even talking about business ethics per se. I want to talk about simpler things - about information security (IS). In carrying out our work, we are creating various information security systems. What are we guided by when creating them? What do we write in the section of the ToR “Basis for Development”?
We write: “Regulatory documents”, “Industry standards”, “Modern technologies”, “The market of specialized equipment and software”, “Best practices”, “Experience in the implementation of such systems”, something else. But we think: "Maximum profit."
Many times I have come across the fact that many IS tasks can be solved by administrative and operational measures, but to solve them, expensive equipment was purchased and no active administrative and operational measures were taken. Someone will ask me why? Or is it clear to everyone?
Both sides - the Customer and the Contractor, in the person of those responsible at each level, sit around a clearing with the name “Information Security” (the same is true for IT in general) with only one thought - “so that we have the most and there is nothing for us ".
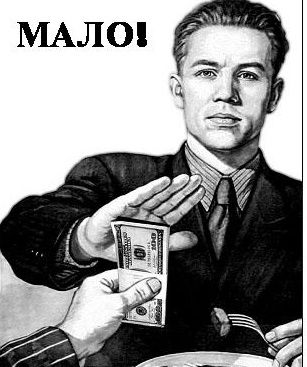
Now I do not want to talk about the competition between integrators or specialized companies (market players - residents) and the role of kickbacks in it. Although now, even in competitions between vendors, kickbacks often become key factors. Kickbacks have become the largest (I hope that they are not yet market-forming, although no one keeps statistics) the “driver” of the IT and information security business. IT and information security have become sticky fish on the body of production, trade, and the service sector.
Once I asked one successful sales manager - “has he recently had sales without kickbacks?” - in response, I heard a long pause, and then some ornate explanation of why kickbacks are not as bad as it seems at first glance .
Even if you make your face a brick and your lips a bow (that is, ignore the issue of kickback ethics - many work at lower rates, because the employer believes that IT / IS employees themselves will steal the rest), the question of the optimal planning and use of IT / IS remains budgets.
I want to talk about how rollbacks make our IT and information security solutions not optimal. The choice of decisions is often determined by inflating budgets and kickbacks, and not by technical characteristics. In one large private (!) Enterprise, I observed a picture of how two different network security systems were built over the years by two different departments (with this money one could be built, but twice as functional). Almost every department had its own server, in the ITC there were more than one SAN system.
Moreover, few people think that once sitting on the rollback needle, a specialist involved in making a procurement decision cannot remain objective in choosing IT / IS solutions. After all, if he wants to “jump” from a non-optimal vendor in favor of another (they also give kickbacks) of a more optimal one, then he can “crawl sideways” - he is at risk of divulging information about kickbacks, losing the reputation of a specialist. Now IT / Ibshniki cope with this through regular rotation (change of job), but the essence remains the same.
In total, an interesting thing comes out - the IS service at the enterprise (part of the SB) should protect the business from economic damage, but who will protect the business from the IS service? What are your thoughts on this? To steam or not to steam about this? Or am I so angry because I didn’t have a bike before?
PS Yes, there are people to whom the above does not apply, I am aware, but I'm not talking about them.
