Background: quantum finger cryptography

The history of quantum cryptography did not begin with communication technologies, but with an attempt to solve a completely different problem - to create money that cannot be faked.
In 1983, Stephen Wiesner of Columbia University proposed creating state-made quantum banknotes that cannot be copied even if one who wants to do this has the printing equipment and paper used to make the original. The likelihood of making an exact copy of an original protected by quantum technology tends to zero.
How did it all start?
The essence of the technology is that on each banknote there are traps with photons, each of which is polarized in a certain way according to two different bases. One basis provided for “cross-shaped” polarization: that is, the photon could be polarized at an angle of 0 or 90 degrees from a certain vertical, and the second - diagonal, that is, with angles of 45 and 135 degrees.
To copy a banknote, the counterfeiter must measure the polarization of the photons, but he does not know in what basis each of them is polarized (the Central Bank keeps this information, as well as the polarization parameters, secretly, and only he knows which polarizations correspond to the banknote number). A criminal can choose bases randomly, and then he has some chances of success, though very small. But they become insignificant if you create photonic traps. That is, to increase the number of photons on each banknote (the probability of guessing decreases as an inverse power function of the number of photons). If each banknote is equipped with a dozen traps, the likelihood of a successful fake drops to almost zero.
It was a great idea, but, unfortunately, not technically feasible: convenient and affordable mass traps for photons, suitable for placement on money, have not yet been created.
What is quantum communication and when did the working system appear?
Wiesner also suggested that a similar mechanism could be used to create confidential communication channels. A year after the publication of his article, scientists Gilles Brassard and Charles Bennet developed the first protocol for quantum communication, which they named after the first letters of their names and the year the technology was created - BB84. This protocol is widely used in modern quantum communication networks.
Bennett and Brassard proposed to encode data in the quantum states of single photons, for example, in their polarization. As in the case with other quantum objects, the fact of measurement itself necessarily affects the state of the object, therefore, if someone else tries to “eavesdrop” on the transfer of photons — that is, to measure the states of the photons that we exchange, we will notice this because they will change states of photons. Therefore, in theory, it is impossible to connect to the channel of quantum data transmission unnoticed in principle - the fundamental laws of quantum mechanics do not allow (in practice, this technology also has some vulnerabilities, but more on that below).
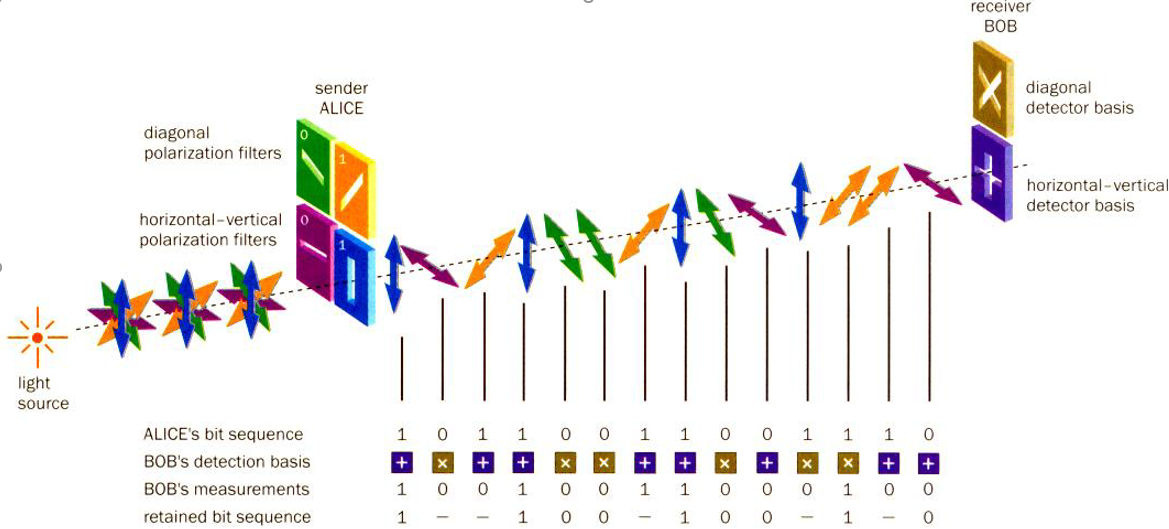
BB84 Protocolworks as follows. One of the interlocutors (traditionally called Alice) sends the other (Bob) photons polarized in one of two, non-orthogonal to each other, bases: rectangular or diagonal. Bob receives them and measures the polarization, choosing the basis for measurement at random, and writes the measurement results and bases. Then he and Alice exchange information about the bases used (but not about the measurement results) over an open channel, and the data obtained with mismatched bases is reset. Only the values measured in the matching bases remain (in the technology of quantum key distribution this is called “key sifting”).
Wolfgang Tittel, Grégoire Ribordy and Nicolas Gisin, Quantum Cryptography, Physics World, Volume 11, Number 3https://iopscience.iop.org/article/10.1088/2058—7058/11/3/30
A possible “spy” that eavesdrops on the data transmission on this communication line (it is usually called Eve) can intercept a single photon, measure its polarization and try to forward a copy of the photon to Bob.
But, in accordance with the theorem on the impossibility of cloning an arbitrary quantum state, this will lead to an increase in the number of errors in the distributed quantum key. As a result, both Alice and Bob will understand that an outsider is listening to their channel. To determine the level of errors in the key after the quantum distribution procedure, Alice and Bob compare a small part of the key over the open channel. It is believed that if the key error level is less than 11 percent, then the security of the communication line can be guaranteed.
Bennett and Brassard conducted the first experiment on transmitting information on a quantum channel at the end of October 1989. They were not lucky - their idea was not taken seriously, so the scientists decided to create a prototype of the experimental setup on their own and at their own expense. Implement help installation friends. The first installation for absolutely secure quantum communication transmitted data over a distance of 32.5 centimeters. Brassard recalls that their system provided data protection only from a person who would be completely deaf: the power supply was very noisy, and the noise was different depending on what polarization of the photons the installation was providing at the moment.
Despite all the shortcomings, the installation was working. Actually, from this moment the history of quantum communications and quantum networks began, which today stretch for thousands of kilometers and go into space.
Why is all this necessary?
Without encryption, virtually no data is transmitted today. The most popular encryption methods that are used now are based on one assumption: the task of decrypting messages is so complicated that the attacker's computing power is not enough to solve it. In other words, the cost (both in money and in time) of decryption will turn out to be disproportionately higher than the value of the information thus obtained. This applies to both symmetric encryption (AES, DES, Russian GOST 28147-89 ) and asymmetric (for example, RSA).
Is quantum communication so safe?
At the moment, it is completely safe, but the situation may soon change due to the advent of a quantum computer.
The fact is that in public-key encryption systems, the so-called one-way functions are used, in which, by a known argument, finding the value of the function is quite simple, but the reverse operation is extremely complicated. For example, multiplying even very large numbers is a simple task for a computer, but the reverse - factorization (factorization) - requires many times more computational time than for solving the original problem, and the complexity of this task grows rapidly with increasing number.
The use of the asymmetry of multiplication and factorization is based, for example, on the widespread RSA encryption algorithm, and many other encryption systems, which are called “asymmetric”. Their main advantage is that for their use it is not necessary to transfer encryption keys through a special secure channel (for example, a flash drive with a trusted courier), as is the case with symmetric algorithms, where the same secret key is used for encryption and decryption.
In asymmetric technologies, two keys are used - public and private, the first can be transmitted over networks, and it can only be used to encrypt a message, and decryption requires a private key that is stored by the user. The private and public keys are interconnected by an asymmetric function, and it is believed that it is practically impossible to restore a private key from a public key using modern technologies (this may take billions of years).
But now, in the future, the situation may change if quantum computers appear. Back in the mid-1990s, mathematician Peter Shore developed a quantum algorithm that got his name. The algorithm allows factorization almost as fast as multiplication. Quantum devices on which the Shore algorithm can be run already exist, but so far they have successfully factorized only the numbers 15 and 21. With the advent of more advanced quantum machines, all cryptosystems based on this asymmetry will become useless.
Some scientists call the quantum computer “the information atomic bomb,” which will have to remove most of the information and banking services we are used to today: about 50% of the Internet traffic of these services is encoded with public key algorithms. Moreover, the fact that a quantum computer has not been created now does not mean that the data that you are exchanging now is safe - perhaps it will be decrypted in the future. For example, the US intelligence agency NSA in its data center in Utah stores at least a few exabytes of unencrypted data . As soon as new decryption methods appear, they can be decrypted.
But quantum physics also gives us protection against the computational capabilities of both quantum and future classical computers and computational algorithms - the quantum distribution of keys.
Is this just a theory or are there real cases?
In short, it has long been not only a theory. The quantum technology market is still small, the first company that set itself the goal of making money on quantum cryptography - ID Quantique - appeared ten years after the first experiments of the Bennett group in 2001. It was founded by immigrants from the University of Geneva, among which was the outstanding physicist Nicolas Gisin. But the first to put technology on commercial footing was American Magiq Technologies Inc. In November 2003, she announced that she was ready to offer her potential customers a quantum key distribution system that can operate at a distance of 120 kilometers.
A few months after this, ID Quantique launched its system on the market, and very soon it became one of the market leaders. Using quantum technologies, she organized data protection during the regional elections in Geneva in 2007, and in February 2018 set a record for the range of transmission of quantum data via fiber optic cable - 421 kilometers.
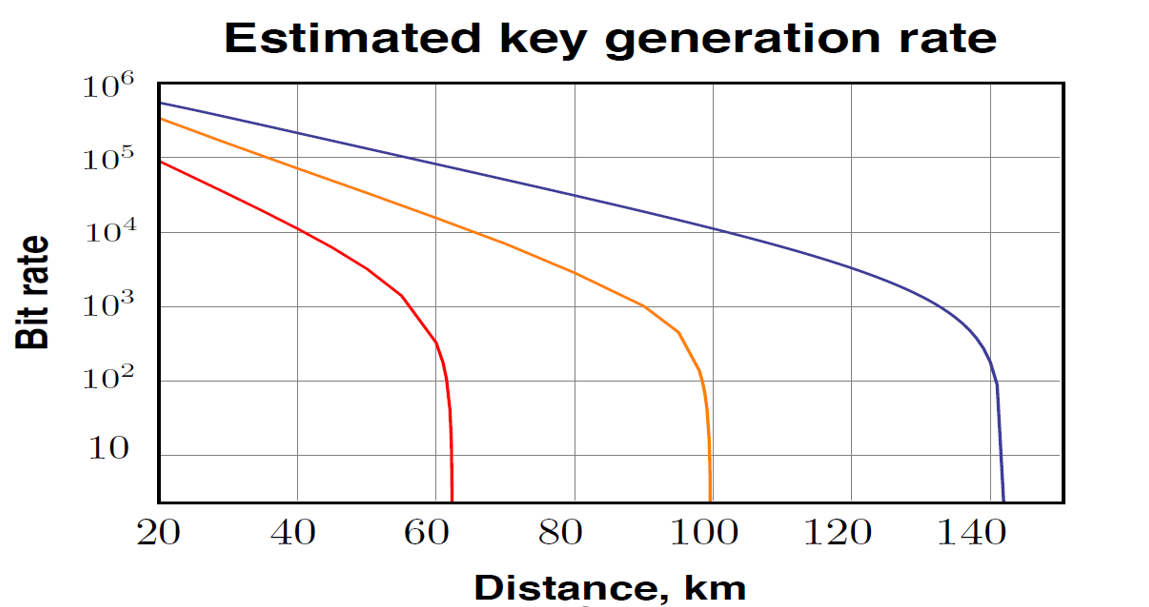
Range and data rate still remain the main problem of quantum communication. The fact is that the transmitted data is encoded in the states of single photons, at this stage the quantum communication lines are very vulnerable to interference and noise, therefore, in practice, transmission of the quantum key in transmission networks is carried out at distances up to 100 km. At longer distances, the key generation speed becomes too low.
Phys. Rev. Lett. 121, 190502 (2018) Secure quantum key distribution over 421 km of optical fiber
In most cases, quantum communication is used within the same settlement. For greater distances, quantum networks are built from many separate fragments connected by specially protected nodes.
Today, three companies dominate the global market for commercial quantum communication systems: the Chinese Qasky and QuantumCTek, as well as the Swiss ID Quantique. They supply almost the entire spectrum of solutions and components: from sources and detectors of single photons, quantum random number generators to integrated devices:
- ID Quantique offers two types of systems: based on a bidirectional circuit (Plug and Play) and coherent single-pass (coherent one way - COW). These devices are designed to work in urban fiber optic networks and allow the transmission of quantum keys at distances up to 70 kilometers.
- Qasky produces systems for government agencies; there are no products on the market.
- QuantumCTek in 2018 showed devices for urban networks: key generation systems, compatible switches, devices for secure telephony.
Quantum communications protection technologies are actively used by large banks and financial organizations, government agencies, as well as data centers. The global quantum cryptography market in 2018 was estimated at $ 343 million , and in 2021 it is expected to double in size to $ 506 million . In Russia, the first attempts to transfer quantum keys to the laboratory took place in the early 2000s at the Institute of Semiconductor Physics SB RAS. In 2014, a prototype of a working quantum communication system was presented at the ITMO University of St. Petersburg - then it was a question of transferring data between two buildings of a university at a distance of 1 kilometer, that is, actually about a laboratory experiment.
In 2016, the Russian Quantum Center launched the first urban quantum communication line, based on the use of “ordinary” optical fiber. She connected the two offices of Gazprombank, located at a distance of about 30 kilometers from each other.
At present, experimental and commercial quantum networks have been created and are being created in Moscow, Kazan and St. Petersburg. The projects are mainly supported by large Russian banks and Rostelecom.
Are there any larger projects?
Several large quantum networks are being built in the world. In the USA (Quantum Key Distribution, Quantum Xchange), in Europe (SECOQC and Swiss Quantum), in Japan, Toshiba is involved in this project, but China is developing the largest project.
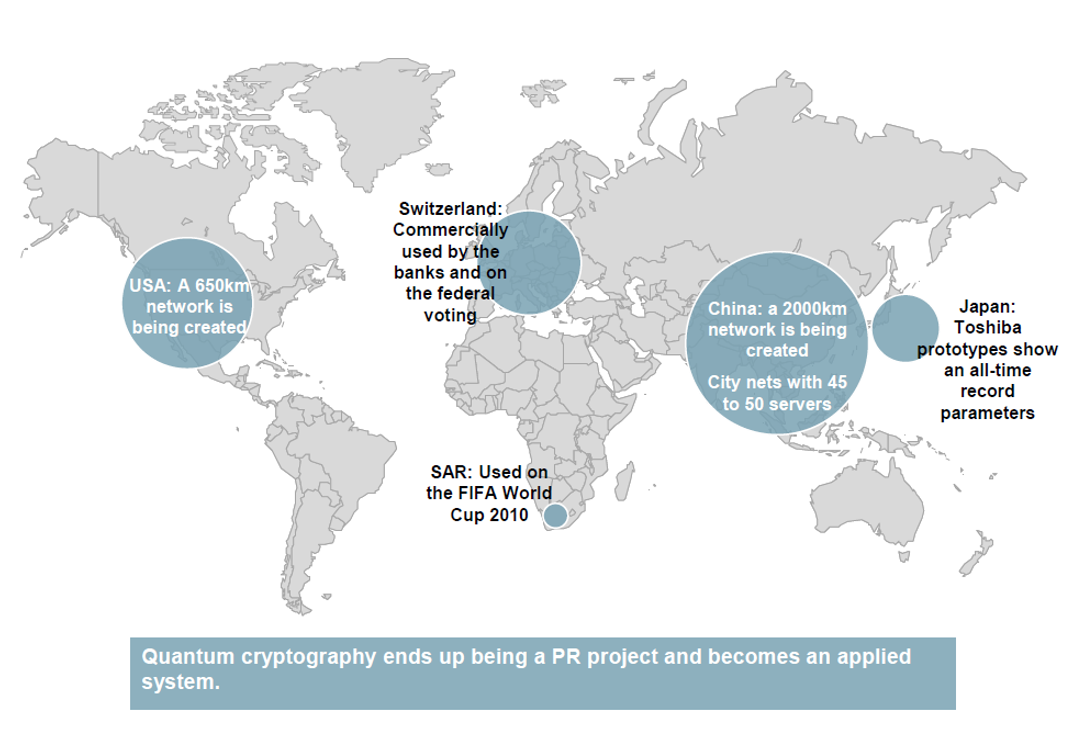
The Chinese quantum network today is about 2 thousand kilometers in length and connects the capital and several major financial and industrial centers.

In addition, China is one of the pioneers in the field of space quantum communications. Satellite channels are one way to solve the problem of distributing a quantum key over long and intercontinental distances.
In 2016, China launched the Mo-Zi small satellite(a.k.a. QUESS - Quantum Experiments at Space Scale, "Quantum Experiments of Space Scales"), developed by the Jian-Wei Pan team from the University of Science and Technology in Shanghai. In 2017, data appeared on the results of the experiment with the satellite: the device ensured the distribution of quantum keys at a distance of over 7600 kilometers between the observatories in Beijing and Vienna. Chinese scientists plan to develop global quantum communication lines, where the satellite will act as a trusted node.
What about quantum technologies in Russia?
In addition to the Russian Quantum Center (RCC) and its subsidiary company QRate, groups of MSU employees work together with InfoTeKS OJSC and St. Petersburg ITMO (Quanttelecom company) in the Russian Federation to implement a quantum communication project.
Moscow State University and Infotex presented a pre-production model of a quantum telephone - a voice communication system where voice data encryption is provided by means of a quantum key distribution. According to the developers, the total investment in the project will be about 700 million rubles, and the cost of a basic set of equipment - a server and two phones - will be about 30 million rubles .
The RCC was the first in the world to develop a quantum protected blockchain - a tool for creating a distributed database in which it is almost impossible to fake records. Quantum cryptography methods helped protect the blockchain from the threats posed by the advent of a quantum computer. The circuit was tested on urban fiber networks.
In addition, the RCC and QRate built a quantum network and demonstrated a multi-site session of quantum-secure video conferencing at the St. Petersburg International Economic Forum. The heads of Sberbank, Gazprombank and the audit company PwC Russia took part in the quantum communication session.
QRate has also developed a serial installation for quantum cryptography, which can be integrated into the existing standard telecommunication infrastructure and adapted to work with cryptographic protocols. The devices use detectors and sources of single photons created in the RCC.

At the design and creation stage, there is a quantum network in Skolkovo, negotiations are underway on the development of an existing quantum network with Sberbank and Gazprombank.
In the future, QRate also plans its own space project: to install a quantum signal transmitter on a small satellite of the Cubsat standard, and to distribute quantum keys between two ground stations.
Are there conferences on quantum technology?
Yes, there are, including in Russia.
ICQT
Once every two years, the International Conference on Quantum Technologies, ICQT, takes place in Moscow. The event is attended by scientists, top managers of technology companies and information security specialists. Here are some big names with ICQT 2019: Eugene Polzik, Rainer Blatt, Peter Zoller, Tommaso Kalarko, Khartoum Neven, Mikhail Lukin, Christopher Monroe. This time the conference takes place from July 15-19 .
July 18 will be a free open day. You can listen to speakers from Google, Airbus Blue Sky, D-Wave and Quantum Flagship. Anyone can come, but you need to register at the Taipad.
QEC2019 Quantum error correction
From July 29 to August 2, a conference will be held in London dedicated to the correction of quantum errors. It is called “Quantum error correction”. Quantum information has a large number of unusual properties, one of them is just the correction of quantum errors.
The conference is organized by a group of scientists from the Institute of Physics. The conference is not attended by the entire association, but by a group dealing with quantum technology issues - Quantum Optics, Quantum Information and Quantum Control group.
QCALL Early-Stage Researchers Conference 2019
A conference on quantum technologies in Italy will also be held from September 16 to 19 this year. Young scientists who specialize in quantum technology are invited to attend. The core of the conference is 15 researchers from Europe. The organizers hope to combine the efforts of a large number of scientists from around the world on solving the most important issues of modern quantum science.
