Hidden SMS threats: the mobile operator knows too much
We talk about the potential threat to security and privacy when using SMS.
Those who first came across a mobile phone, in addition to calls, found out about the presence of short text messages. And if initially messages were often used to exchange information without the participation of a live operator (remember a pager), now they have become the main tool for notifications and verification.
We conducted a thematic survey in our telegram channel :
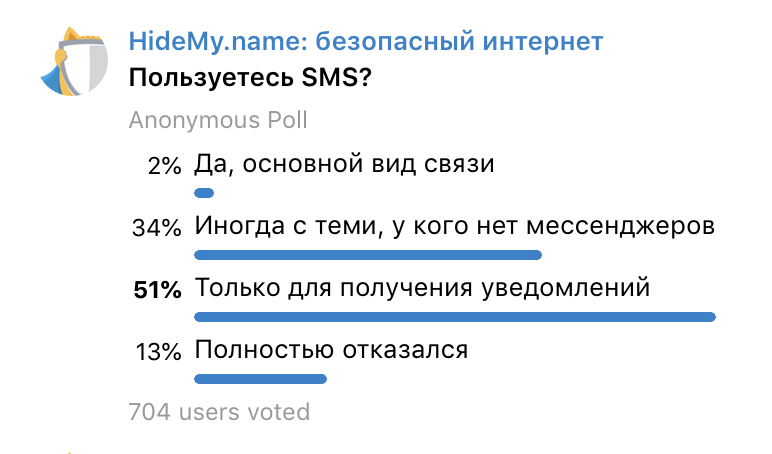
Result: 87% use SMS . It’s not obvious to everyone, but the answer “ Only for receiving notifications ” threatens privacy even more than SMS correspondence with someone who does not have instant messengers. Congratulating a relative on holidays, you think about what you write. Who sends notifications - no.
The sample is modest, but in large numbers the difference will be insignificant.
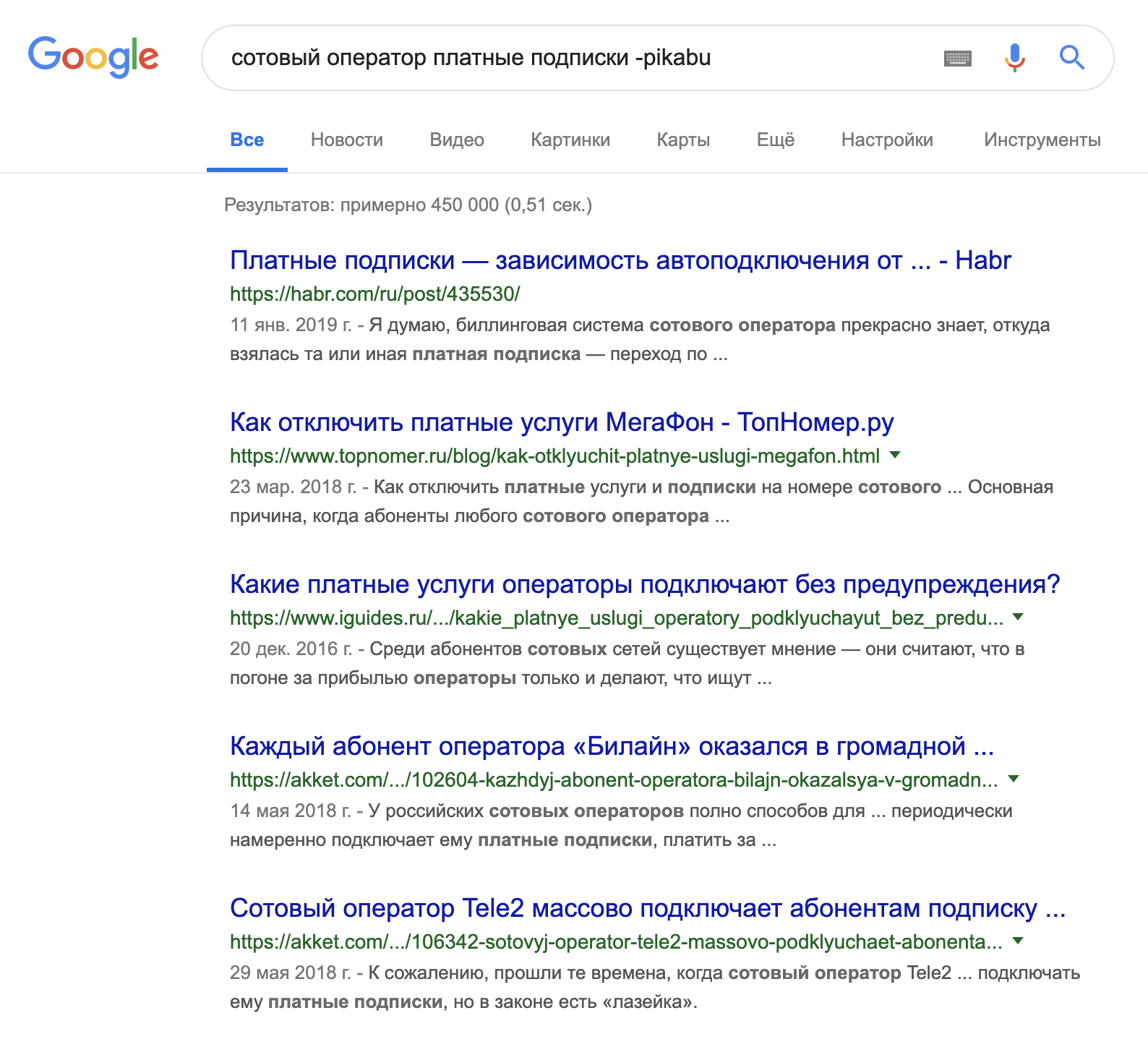
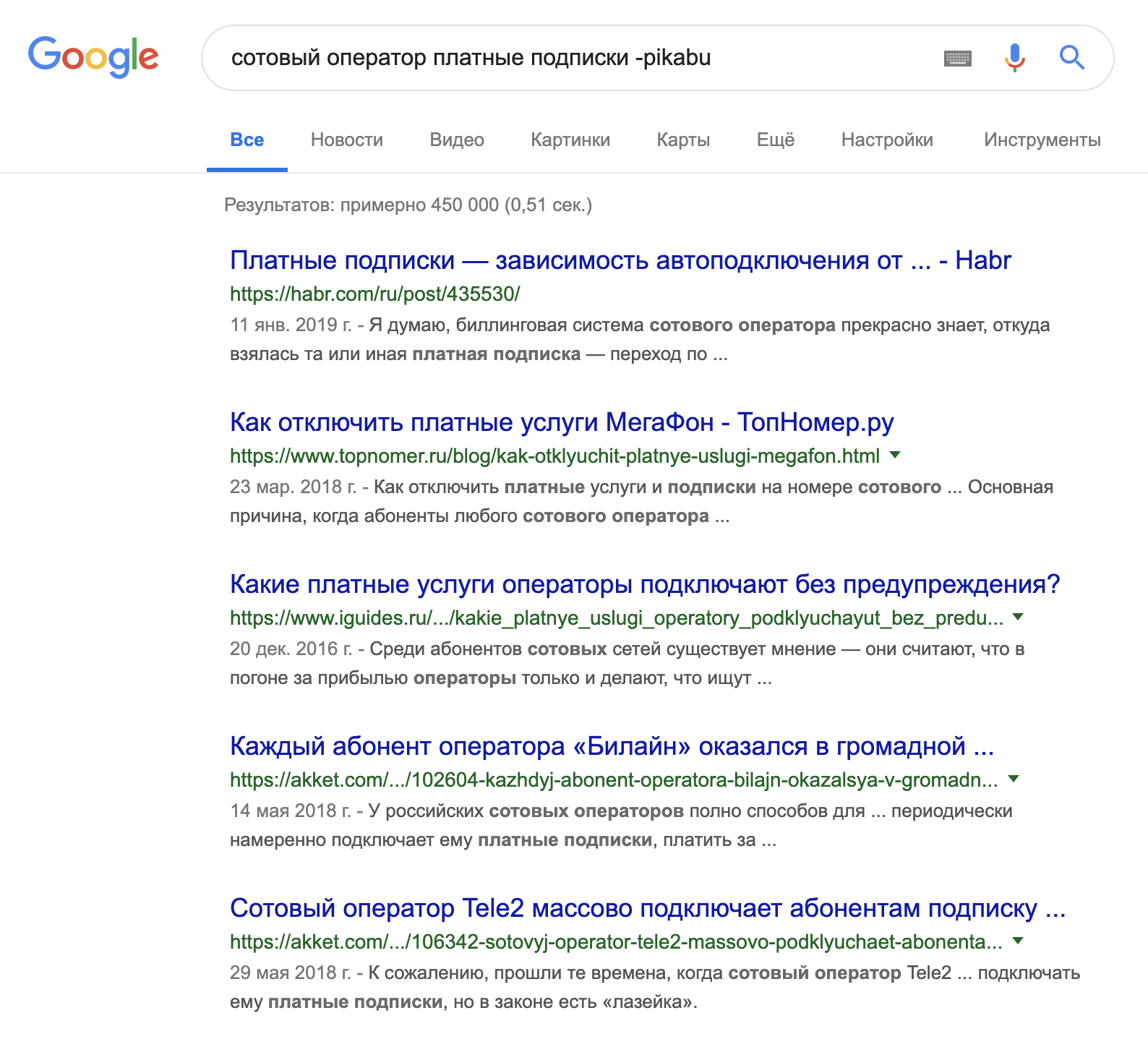
Regularly there are stories about automatic subscriptions to paid services. Last month, on Habr, they spoke about Megafon :

A year ago about MTS on Medusa :

To understand the scale of the problem:
You lose a SIM card, apply with a passport to the salon of a mobile operator, an employee issues a new card with your number in a minute. The usual scenario? He can do the same thing of his own free will, without your knowledge, if the benefit exceeds the consequences and the likelihood of punishment.
But the re-issuance of SIM cards by fake proxy is noticeably more popular . Aware of the problem, mobile operators offer to protect themselves by prohibition of actions on behalf of the subscriber by proxy. Although they could solve the problem globally by setting a default ban.

Having fallen into the wrong hands, your number becomes the key to mail, instant messengers, and many payment instruments. That is wherever access recovery or verification via SMS is used.
The relatively good news is that most modern banks can track the fact of a SIM card change, which means they will not be allowed into the Internet bank and they will not send a confirmation code for online payment. At least until you confirm the change of card in the department or by phone. But do not forget that the entries on the “Spring Package” are kept by the operator for six months, and there, among other things, there are your answers to the “secret questions”.
The law enforcement agencies can also gain control over your SMS, as we already mentioned earlier. Without re-issuance of a SIM-card and completely invisible to the subscriber
Here is the fun part.
Notifications from companies : online services, restaurants, clubs, clinics, shops, delivery services, car sharing. Many sign their messages, which means that you can immediately determine what services the client uses. How much personal information is contained in such messages, you can imagine for yourself.
Notifications from banks . From such messages you can get information:
• about account balances;
• about withdrawals and replenishment in which ATMs;
• about your total turnover for any period;
• about deposits: amount, term, interest paid;
• About approved loans, payments on them and debts;
• on issued cards, on a part of their numbers, and sometimes a part or a whole pin-code;
• about all transactions of the user, his purchases;
• about paying bills;
• about transfers to other people, including their names and account numbers.
And what the operator saves is not protected by any “banking secrecy”.
The information collected allows you to create a thorough and personalized customer profile. Analytics do not require a lot of resources: textual information on templates, keywords, and the type of destination is easily processed by algorithms.
Such a profile provides almost unlimited opportunities for the operator and anyone else who has received unauthorized access, including a database leak.

About information leaks on @dataleak
Open your SMS and see what information you share with the operator in the clear.
How many SMS archives are stored? According to the Mobile-Review investigation - 3 years, according to Maxim Katz - at least 2 years.
We switch to using Push notifications instead of SMS.
Sample scenario from Alfa Bank:

A similar procedure is available in most other banks with mobile applications.
We use verification applications in the smartphone (Google Authenticator and analogues), smart cards, tokens, or at least confirmation by e-mail of a reliable mail service.
Everyone with whom you communicate via SMS can be transferred to safe or relatively safe messengers of foreign manufacture. Show them personally that using instant messengers is not scary and not painful.
For discussion.
Using a foreign SIM card
Several doubts about the reliability of this option:
If someone wants to talk about the “inner kitchen” of these issues, but is not ready to do this in public comments, you can anonymously write in our telegram bot marked “for Habr.” By your permission, we will add anonymized information to the article.
Complete rejection of SMS
It’s hard to imagine how to live with it. But in our vote, this option gained 13% ...

Can you completely refuse SMS?
“Historically,”
Those who first came across a mobile phone, in addition to calls, found out about the presence of short text messages. And if initially messages were often used to exchange information without the participation of a live operator (remember a pager), now they have become the main tool for notifications and verification.
We conducted a thematic survey in our telegram channel :
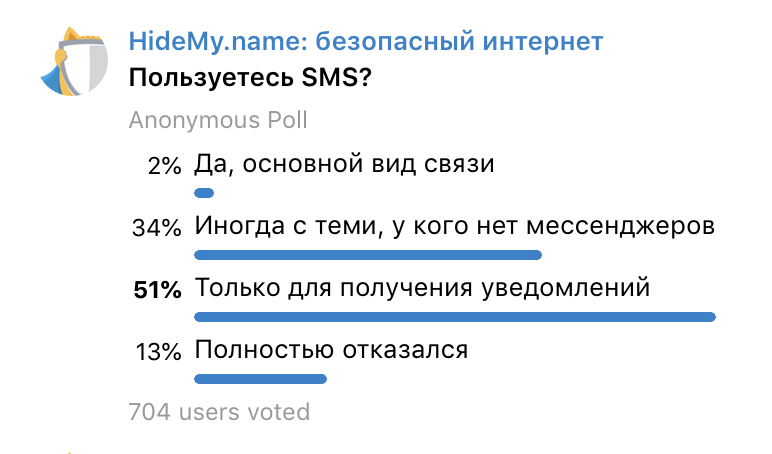
Result: 87% use SMS . It’s not obvious to everyone, but the answer “ Only for receiving notifications ” threatens privacy even more than SMS correspondence with someone who does not have instant messengers. Congratulating a relative on holidays, you think about what you write. Who sends notifications - no.
The sample is modest, but in large numbers the difference will be insignificant.
Threat # 1: Unauthorized expenses
Regularly there are stories about automatic subscriptions to paid services. Last month, on Habr, they spoke about Megafon :

A year ago about MTS on Medusa :

To understand the scale of the problem:
Threat # 2: Account Security
You lose a SIM card, apply with a passport to the salon of a mobile operator, an employee issues a new card with your number in a minute. The usual scenario? He can do the same thing of his own free will, without your knowledge, if the benefit exceeds the consequences and the likelihood of punishment.
But the re-issuance of SIM cards by fake proxy is noticeably more popular . Aware of the problem, mobile operators offer to protect themselves by prohibition of actions on behalf of the subscriber by proxy. Although they could solve the problem globally by setting a default ban.

Having fallen into the wrong hands, your number becomes the key to mail, instant messengers, and many payment instruments. That is wherever access recovery or verification via SMS is used.
The relatively good news is that most modern banks can track the fact of a SIM card change, which means they will not be allowed into the Internet bank and they will not send a confirmation code for online payment. At least until you confirm the change of card in the department or by phone. But do not forget that the entries on the “Spring Package” are kept by the operator for six months, and there, among other things, there are your answers to the “secret questions”.
The law enforcement agencies can also gain control over your SMS, as we already mentioned earlier. Without re-issuance of a SIM-card and completely invisible to the subscriber
Threat 3: Privacy
Here is the fun part.
Notifications from companies : online services, restaurants, clubs, clinics, shops, delivery services, car sharing. Many sign their messages, which means that you can immediately determine what services the client uses. How much personal information is contained in such messages, you can imagine for yourself.
Notifications from banks . From such messages you can get information:
• about account balances;
• about withdrawals and replenishment in which ATMs;
• about your total turnover for any period;
• about deposits: amount, term, interest paid;
• About approved loans, payments on them and debts;
• on issued cards, on a part of their numbers, and sometimes a part or a whole pin-code;
• about all transactions of the user, his purchases;
• about paying bills;
• about transfers to other people, including their names and account numbers.
And what the operator saves is not protected by any “banking secrecy”.
The information collected allows you to create a thorough and personalized customer profile. Analytics do not require a lot of resources: textual information on templates, keywords, and the type of destination is easily processed by algorithms.
Such a profile provides almost unlimited opportunities for the operator and anyone else who has received unauthorized access, including a database leak.

About information leaks on @dataleak
Open your SMS and see what information you share with the operator in the clear.
How many SMS archives are stored? According to the Mobile-Review investigation - 3 years, according to Maxim Katz - at least 2 years.
Get off the needle SMS - it will not be easy
Financial operations
We switch to using Push notifications instead of SMS.
Sample scenario from Alfa Bank:

A similar procedure is available in most other banks with mobile applications.
Service Login Confirmations
We use verification applications in the smartphone (Google Authenticator and analogues), smart cards, tokens, or at least confirmation by e-mail of a reliable mail service.
Communication
Everyone with whom you communicate via SMS can be transferred to safe or relatively safe messengers of foreign manufacture. Show them personally that using instant messengers is not scary and not painful.
Two more radical options
For discussion.
Using a foreign SIM card
Several doubts about the reliability of this option:
- Are these SMS available in clear text to the local operator who services a foreign number while roaming?
- Keeps and should he keep them legally?
- Is it obligated to provide information about messages to such numbers upon request?
If someone wants to talk about the “inner kitchen” of these issues, but is not ready to do this in public comments, you can anonymously write in our telegram bot marked “for Habr.” By your permission, we will add anonymized information to the article.
Complete rejection of SMS
It’s hard to imagine how to live with it. But in our vote, this option gained 13% ...

Can you completely refuse SMS?
