Inside the secret lab of Ledger

Donjon is an information security laboratory of the French company Ledger. Ledger produces hardware wallets that store the private keys of cryptocurrency owners. Attackers prey on these keys, and the hardware wallet, respectively, protects the keys from leakage. How reliable? In the "Donjon" make every effort so that such a question does not even arise.

These people are doing everything for Ledger wallet owners to sleep peacefully.
For a long time, the existence of the laboratory was kept secret. It employs eight employees who prefer to remain anonymous. It is only known that they are “world-class experts” in cybersecurity and smart cards. These “white hackers” look for vulnerabilities in the software and in the hardware of Ledger, as well as in the products of competitors. The laboratory itself is located in the Paris office of the company. The workspace is protected by an alarm, and only Donjon personnel can enter it.
The laboratory is engaged in research of various types of attacks. Software attackswhich cryptocurrency wallets are exposed to usually consist of investigating the unusual behavior of systems and interfaces. A typical example of what Donjon is hunting for: a Heartbleed bug in the OpenSSL cryptographic library. This famous vulnerability spread in 2012 and consisted in the possibility of unauthorized reading of server memory, removing from it including the private key. They fixed it only in 2014, after which Google launched its Project Zero to prevent similar threats.

xkcd about what Heartbleed is
Donjon’s specialists apply standard techniques: reverse engineering, statistical analysis, cryptography and fuzzing. Fuzzing is the transfer of random or unexpected data to a program. Last October, with his help, hackers found two vulnerabilities in the crypto wallet code of the rival Trezor company.
These were buffer overflow errors. In both cases, the function specified the condition incorrectly; as often happens in such cases, the code worked, but not in the way its authors wanted. You can read more about this on the Trezor blog .
Both vulnerabilities allowed you to remotely disable the wallet by attacking it through the browser, without user intervention. They affected firmware versions 1.6.2 and 1.6.3, and fixed errors in the new version.
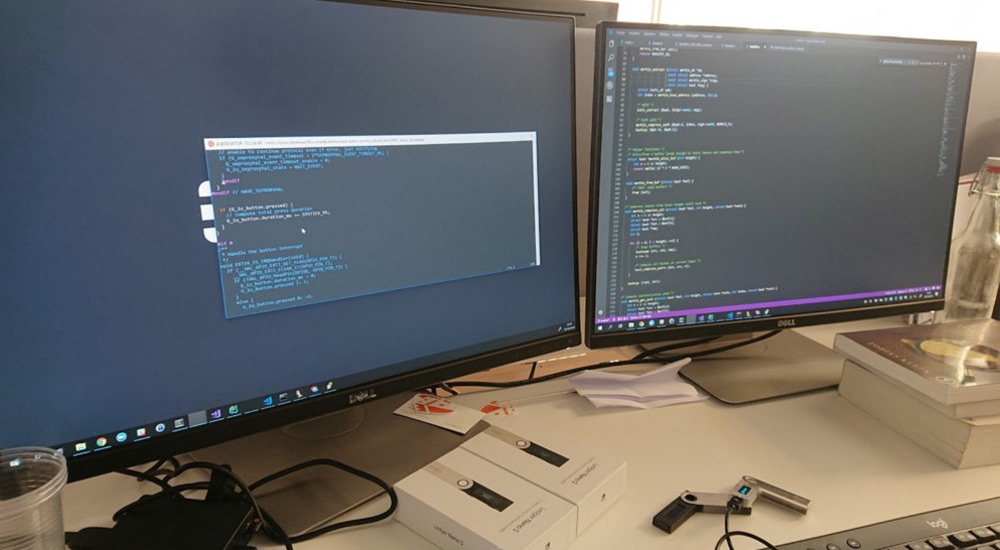
As honestly said the director of security at Ledger Charles Guillaume, the company only develops software from scratch. Chips and electronics are provided by third-party suppliers. Therefore, Donjon, like a medieval dungeon, is equipped with “torture” tools in order to methodically test wallets for physical vulnerabilities that could lead to data leakage. Attacks on third-party channels
look impressive and complex . Such attacks are aimed at the physical vulnerabilities of a working device. If an attacker stole or finds a lost crypto wallet, then he can measure the electromagnetic radiation and the change in the power consumption of the device during code execution. The hacker uses the received data to bypass the protection.

Attack on hardware wallet in progress
In practice, this idea allowed Ledger hackers to successfully crack the Trezor One wallet PIN. The PIN code was needed to access the device, and it gave a generous 15 attempts to enter the correct combination. "Donjon" learned to guess the PIN for five times.
The following happened: a wallet with a known PIN code was disassembled, and then sensors were installed on its flash memory to measure power consumption and electromagnetic field. Arbitrary numbers were entered into the wallet, and the oscilloscope wrote data from the probes. Data was marked as reactions to correct and incorrect input, and then “fed” to the algorithm for training.
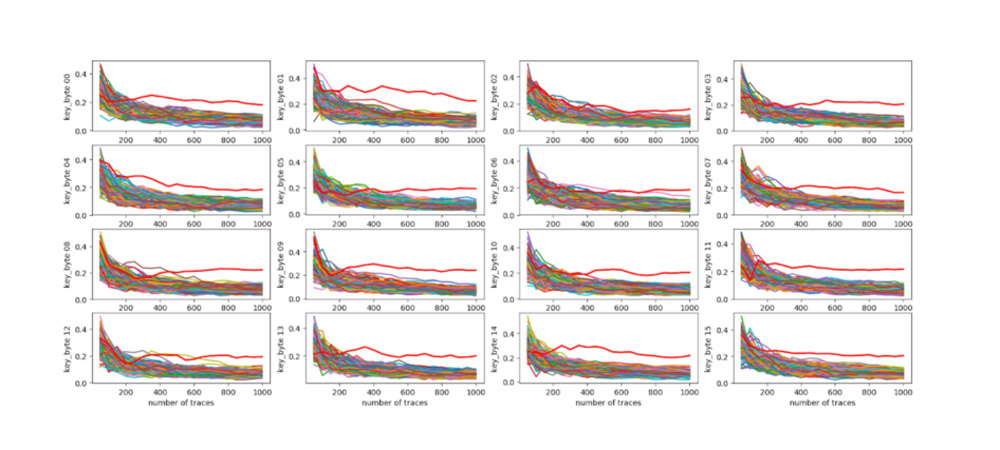
Attack Results. The future has come, so the robot will understand them
Having taught the algorithm to distinguish different reactions, the researchers put the sensors on the second device. It played the role of a potentially stolen wallet, and exactly the same data was written from it when entering the PIN code. The algorithm trained on the first wallet recognized which numbers were correct and which were not, and guessed the PIN entirely.
Since there is an additional delay before each new attempt to enter a PIN, such a hack is a long business. To sort through all 15 codes, it could take a whole day of work. If successful, the hacker gets unlimited access to other people's assets, so the game is worth the candle.
The experiment, Donjon again shared with competitors who took them very seriously and completely rewrote the PIN verification algorithm.
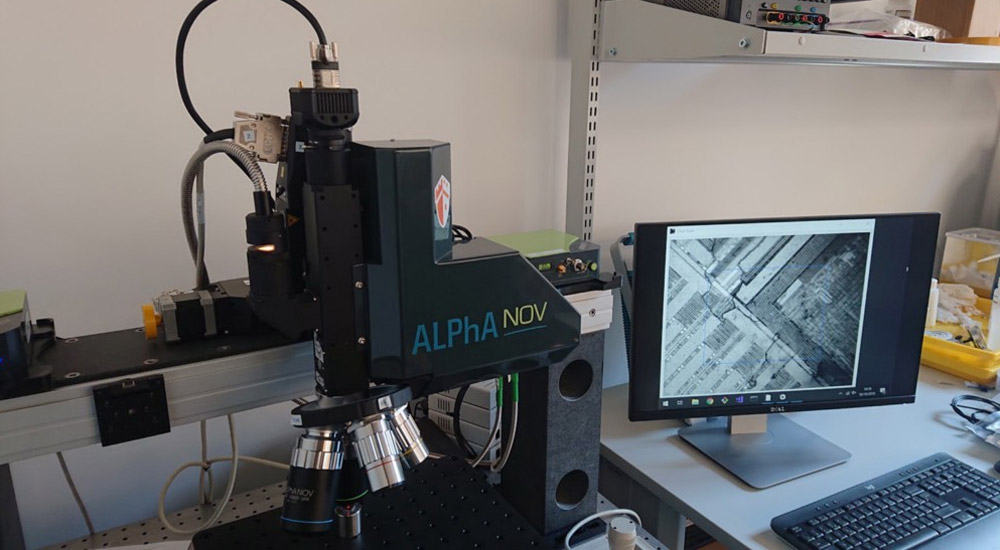
Installation for carrying out attacks on computational errors
Another favorite technique of Ledger hackers: attack on computational errors. This is a subtype of attack on third-party channels, which implies active intervention in the operation of the device: lowering and increasing the voltage in the circuit, increasing the clock frequency. A hardware wallet can be affected by ionizing radiation, a laser and an electromagnetic field. The attack allows you to bypass the input of the PIN code: increase the voltage, the device goes astray and skips checking the correctness of the entered numbers.
An experienced cracker will be able to extract other data that a hardware wallet should protect. For example, seed, a mnemonic phrase that opens access to all assets at once. This is a complicated but feasible procedure, and the Donjon team managed to do it with Keepkey, B Wallet, Trezor One and Trezor T wallets.

This donjon card is used to attack crypto-wallet chips
Unfortunately, the details of the last Donjon hack are not reveals. Hackers have a very strict “code of honor”: they first crack the device, then pass the details of the vulnerability to Ledger or competitors and wait for corrections. Only after this, the public is informed that the problem existed.
Hackers reported back in December 2018 that they could extract seed from their wallets. Vulnerability is still not fixed. According to Guillaume, in principle, nothing can be done with this defect, so the Donjon team will not tell how exactly the wallets were hacked.
To prevent attacks on calculation errors, Ledger crypto wallets use a separate Secure Element security chip. Such chips are put in credit cards, SIM-cards and biometric passports. He detects an attempted attack and actively responds to it. Secure Element also hides electromagnetic radiation and power consumption to prevent an attacker from “listening” to himself.
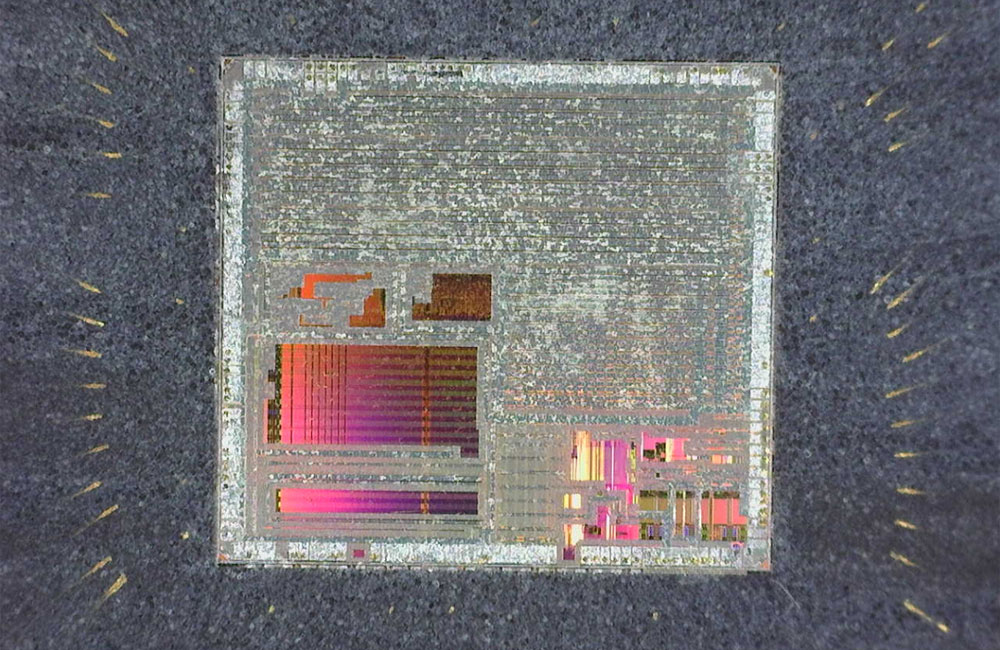
Chip Prepared for Attack
In many other cryptocurrency wallets, all calculations take place on a conventional microcontroller. Ledger considers this architecture unsafe, including because their own hackers “crack” simple chips like nuts. Competitors, including Trezor, counteract the claim that for such a hack it is necessary to have physical access to the device and expert knowledge in the field of cryptography. Most ethereum or bitcoin holders are much more worried about remote attacks, so manufacturers are focusing on software security.

xkcd about hacker everyday life
A pragmatic approach is paying off in the present. However, Ledger is looking into the future, which, as the company is sure, cryptocurrencies have. A pickpocket who pulled out a “flash drive” yesterday from a tourist’s pocket might not have realized that he had the key to wealth in his hands. In a year, he will know exactly who to sell the stolen hardware crypto wallets for someone else to crack into.
With the popularization of hardware wallets, there will inevitably be “markets” for reselling stolen devices. Exactly the same as existing for the resale of data of stolen credit cards. Ledger sledges are prepared in the summer and therefore they are already testing other crypto device manufacturers with complex hacking ideas (with lasers and neural networks).

Ledger Nano S wallet: certified, secure and fully secure (wrench protection not included)
According to Eric Larshevek, Ledger CEO, it’s not about looking for competitors, but about increasing the responsibility of the blockchain industry as a whole . Now the owner of any crypto wallet is his own bank and his own security system. Shifting responsibility onto the shoulders of the client is very convenient for companies that may not certify their goods at all.
Meanwhile, the Ledger Nano S wallet was the first on the market to successfully pass the certification of Agence Nationale de Sécurité des Systèmes d'Information, the French national cybersecurity agency. Ledger is not enough. “I believe the industry needs more security certification schemes,” says Guillaume. While there are no such schemes, Donjon makes every effort to ensure that Ledger hardware wallets are as safe as possible.
Written by Ledger. You can purchase hardware wallets from a French company in our online store.