LockerGoga: what exactly happened with Norsk Hydro

Photo, source - www.msspalert.com
On the night of Monday to Tuesday (approximately 23:00 UTC 03/18/2019), Norsk Hydro specialistsnoticed failures in the functioning of the network and a number of systems. It soon became clear that the failures were caused by a massive infection of the systems with an encryptor, which spread very quickly across infrastructure facilities. After identifying the threat, the security service began the isolation process, but the malware managed to spread so deeply over the infrastructure that it was necessary to transfer part of the production to manual control mode (“rollback” to the procedures adopted before computerization of production processes). Investigation of the attack required the involvement of local authorities and law enforcement agencies (National Security Authority / NorCERT, Norwegian Police Security Service, National Criminal Investigation Service), as well as a number of commercial companies. Restoring infrastructure has not yet been completed and individual production facilities (e.g.
Despite the fact that the investigation of the incident is not completed and it is still difficult to predict the timing of its completion, by the available facts you can understand the mechanism of action of the attackers and analyze what Norsk Hydro did right and what not, and how else the defense could be improved.
The state of the company after the attack
Norsk Hydro is a fairly large company: its facilities are located in 40 countries, and the total number of employees exceeds 35,000 people. The volume of information systems and computers that are affected by the attack is also large. From information from company representatives voiced at a joint press conference with the authorities , and daily news on the progress of the investigation and recovery on the website (update dated 03/22/2019), it follows that:
- local industrial incidents and human injuries did not occur;
- as a result, all plants were successfully isolated, the processes were transferred to manual control where possible (at the aluminum extrusion plants, only 50% efficiency was achieved);
- mobile devices and some PCs are functioning normally, cloud mail is functioning correctly;
- there is no complete picture of the number of failed PCs and servers, there is a different degree of damage to infrastructure facilities;
- there is no access to systems containing data on orders, however there is the necessary amount of information that is required for order production;
- there are no assumptions about the attackers; the most likely hypothesis about the malware used for the attack is LockerGoga ransomware;
- The company has a well-established backup process, and rollback to previously made backups is the main recovery strategy;
- the company has cyber risk insurance, which they plan to use to cover damage from an attack.
It is important to note how Norsk Hydro behaved during the attack. The company acted as openly as possible: at the time of problems with the main site, it launched a temporary one, informed the public through a Facebook account, notified the securities market about its situation and held a press conference on the first day of the attack.
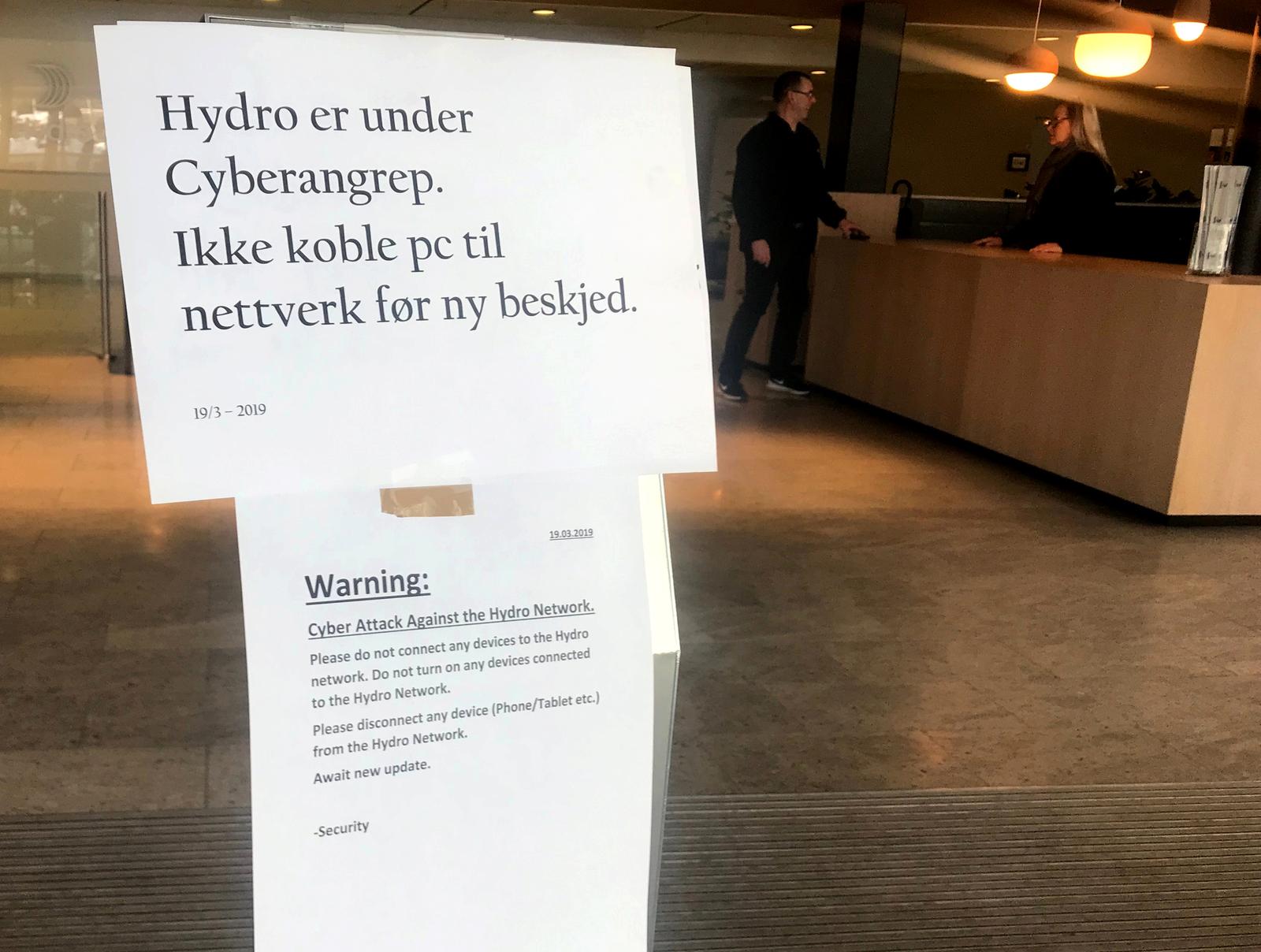
A warning to Norsk Hydro employees that you should not connect any devices to the network due to a cyber attack. Photo, source - www.reuters.com
What is LockerGoga malware?
For the first time, the general public learned about attacks using LockerGoga at the end of January 2019.Then the consulting company Altran suffered from it, but there were very few technical details of the attack. Norsk Hydro was attacked with several versions of the malware, which, by the mechanics of their action, are similar (with the exception of individual "features") to the samples used in the January attack.
The malicious executable files are signed with the same certificate issued by Sectigo (formerly Comodo CA) as the samples used in the attack on Altran (probably a shell company ALISA LTD with 2 owners and 2 shares of 1 GBP each). At the moment, the certificate has been revoked, but during the attack it was valid.
Apparently, each malicious specimen was generated uniquely for the attacked company, which is noted in the analysis of the samples by the researchers .
All identified samples do not have the ability to self-replicate (unlike WannaCry and NotPetya) and must be run on the attacked node. The most likely hypothesis of malware spreading over the Norsk Hydro network is the use of AD group policies to create tasks or services with malicious content. With high probability, this means that at the penetration stage another malware was used, with the help of which it was possible to obtain administrative privileges in the domain. One of the possible mechanisms could be phishing, followed by theft of Kerberos passwords or tickets from the memory of a compromised node.
During the infection process, the malicious executable file is copied to the directory %TEMP%and launched with elevated privileges. After that, it starts a large number of child processes, distributing file encryption to them according to the assembled list. Judging by the behavior of the existing samples, not only files with extensions of office documents, databases and other working files ( doc, dot, wbk, docx, dotx, docb, xlm, xlsx, xltx, xlsb, xlw, ppt, pot, pps, pptx, potx, ppsx, sldx, pdf) are encrypted , but also other files on the C: \ drive (for example, dll libraries) with variations depending on the sample. The child process generates a key / iv pair using RNG, then uses the AES algorithm to overwrite the file with encrypted data, encrypts the key / iv pair with a public key, add the encrypted key pair to the file, and rename the file by adding.LOCKEDto expand. This behavior allows you to more utilize the processor of the infected computer with encryption tasks and make the whole process faster.
The parent process also creates a text file on the desktop with a ransom request (README_LOCKED.txt with variations in the name), changes the passwords of local users (this behavior probably depends on the version of the sample, i.e. only the passwords of local administrators can be encrypted) and commits forced exit from user session. In some versions, the ability to disable the network interface of the computer was revealed.
Thus, in some cases, an infected PC may simply not boot (if critical components of the OS kernel are encrypted) or the user will not be able to log in to view the ransom requirements, which is more common for vipers.
The ransom request (an example is given below) does not contain wallet addresses or the ransom amount, but only postal addresses for interacting with intruders. Different versions of malicious samples have different email addresses in the request.
Greetings!
There was a significant flaw in the security system of your company.
You should be thankful that the flaw was exploited by serious people and not some rookies.
They would have damaged all of your data by mistake or for fun.
Your files are encrypted with the strongest military algorithms RSA4096 and AES-256.
Without our special decoder it is impossible to restore the data.
Attempts to restore your data with third party software as Photorec, RannohDecryptor etc.
will lead to irreversible destruction of your data.
To confirm our honest intentions.
Send us 2-3 different random files and you will get them decrypted.
It can be from different computers on your network to be sure that our decoder decrypts everything.
Sample files we unlock for free (files should not be related to any kind of backups).
We exclusively have decryption software for your situation
DO NOT RESET OR SHUTDOWN – files may be damaged.
DO NOT RENAME the encrypted files.
DO NOT MOVE the encrypted files.
This may lead to the impossibility of recovery of the certain files.
To get information on the price of the decoder contact us at:
AbbsChevis@protonmail.com
IjuqodiSunovib98@o2.pl
The payment has to be made in Bitcoins.
The final price depends on how fast you contact us.
As soon as we receive the payment you will get the decryption tool and
instructions on how to improve your systems securityThe malware does not use any C&C infrastructure, the only communication channel with the attacker is email. Also, the malware does not try to hide the traces of its activities. In connection with a similar implementation of the ransom mechanism, as well as the actual incapacitation of encrypted PCs, it can be assumed that the goal of LockerGoga is similar to the WannaCry and NotPetya malware. However, whether it is true or not, it cannot be said at the moment.
What was done right and what wasn’t
After disclosing information about high-profile cyber attacks, you can often see articles and various materials telling about what the victims of the attack did wrong. In the case of Norsk Hydro, the situation is different; the company did not show noticeable failures in the organization of infrastructure (production did not stop) and conducts the response process to the attack well, namely:
- The company is as open as possible with investors and the public in informing about the progress in eliminating the attack. An indirect indicator of a positive reaction may be the stock price of the stock exchange: despite a slight drop (3.6%) of shares on 23.03, there are prerequisites for their further stable growth.
- It was possible to isolate production facilities quickly enough so that production on them would not be affected.
- There are well-established processes that allow production facilities to function in manual control mode (at least for the majority of production).
- The backup process has been established, which will greatly facilitate the recovery of infrastructure nodes after the incident.
- There are backup communication channels (cloud mail) that allow employees to interact even in case of problems on the main infrastructure.
- The company uses cyber risk insurance, which will help compensate part of the damage from the attack.
At the same time, Norsk Hydro relied too much on the anti-virus solution installed in it. According to the researchers, at the beginning of March, some malware samples were not detected by any anti-virus solution, at the time the attack began, the number of solutions that determined the samples as malicious was also small. In addition, the certification center revoked the malicious certificate too late - after the start of the attack. Also, for some objects, the segmentation of industrial infrastructure from office was probably insufficiently performed.
Detecting an attack in the early stages would help continuous monitoring:
- privileged account activity;
- Group Policy Changes
- creating new services and tasks of the scheduler;
- password change events for privileged accounts, incl. and local administrators;
- activity similar to Pass-the-Hash and Pass-the-Ticket attacks;
Such control should be carried out by an internal monitoring service (using SIEM-like solutions and behavioral analysis systems) and / or an external SOC / CSIRT.
Indeed, early detection will help in saving significant funds to eliminate the consequences of the attack.
Upd. 03/26/2019
Alert Logic researchers have discovered a bug in malware. The attackers did not provide for exception handling when, when collecting a list of files for encryption, the malware stumbles upon a link (* .lnk) that contains errors (incorrect network path or lack of association with the RPC endpoint according to the study). This can happen when collecting files from the Recent Items folder. In this case, the main process is terminated by the operating system and it does not even reach encryption. Perhaps this can partially explain the uneven degree of damage to the company's nodes.
References
- https://www.bleepingcomputer.com/news/security/new-lockergoga-ransomware-allegedly-used-in-altran-attack/
- https://www.nrk.no/norge/skreddersydd-dobbeltangrep-mot-hydro-1.14480202
- http://webtv.hegnar.no/presentation.php?webcastId=97819442
- https://www.hydro.com/
- https://twitter.com/GossiTheDog/status/1107986706089811968
- https://twitter.com/malwrhunterteam/status/1104082562216062978
- https://twitter.com/_qaz_qaz/status/1108441356836503553
- https://www.bleepingcomputer.com/news/security/lockergoga-ransomware-sends-norsk-hydro-into-manual-mode/
- https://www.bloomberg.com/news/articles/2019-03-19/hydro-says-victim-of-extensive-cyber-attack-impacting-operations-jtfgz6td
- https://blog.talosintelligence.com/2019/03/lockergoga.html
- https://www.nozominetworks.com/blog/breaking-research-lockergoga-ransomware-impacts-norsk-hydro/
- https://www.joesecurity.org/blog/2995389471535835488
- https://doublepulsar.com/how-lockergoga-took-down-hydro-ransomware-used-in-targeted-attacks-aimed-at-big-business-c666551f5880
- https://securityaffairs.co/wordpress/82684/malware/lockergoga-ransomware-spreads.html
- https://www.bbc.com/news/technology-47624207
- https://uk.globaldatabase.com/company/alisa-ltd
- https://blog.alertlogic.com/halting-the-lockergoga-ransomware/
