Reverse engineering applications after obfuscation
Introduction
This publication is aimed at studying some reverse engineering techniques. All materials are presented for informational purposes only and are not intended to be used for any personal gain.
Subject of study
As an example, we will study the Atomineer Pro Documentation code (hereinafter APD). This is a plug-in for Visual Studio designed to automatically generate comments in source codes. First, install this plugin and check its operation. The free version has a trial period and a number of usage restrictions during this time. So when adding comments to the file, the user is given a message stating that during the day you can process only 10 files
Message 1

When you try to process the entire project, the utility displays a dialog warning that this command is not available.
Message 2

Let's get started
First, look in the directory of the installed extension and find there only one dynamic library. We need it. The first thing we will do is upload it to the dotPeek decompiler from JetBrains.
dotPeek

As you can see on the screen, the library went through an obfuscator, the variables and methods were renamed and have names like a, b, c, d ... this is what we need. We were looking for just that. Let's see what can be done.
Part 1
The first thing that comes to mind is to find the line, but since the search functionality is not in dotPeek, let's go a different way. We decompile the library with the standard ildasm.exe from the Microsoft SDKs. The output will receive only one text file. In it, and look for the message text " Trial Mode. Please note that your ... "
text file

Found a method
.method family hidebysig static bool e () cil managedWhich belongs to the class CmdDocThisScope. Now back to dotPeek.
Spoiler heading

So what we have. We found a method that displays an APD trial message and, depending on the condition, returns true or false. We find all the places from which this method is called
call search

Only 2 call points were found and these are the methods CmdDocThisFile :: c and CmdDocThisScope :: c.
found

By the name of the classes and the constructor code, it is obvious that the classes are responsible for the menu items, and the virtuality of the “c” method indicates that this is the event handler for selecting the corresponding menu item by the user (This information will be useful to us further). It is easy to guess that if the method returns true, then the command will be executed even though it will show a dialog with a warning.
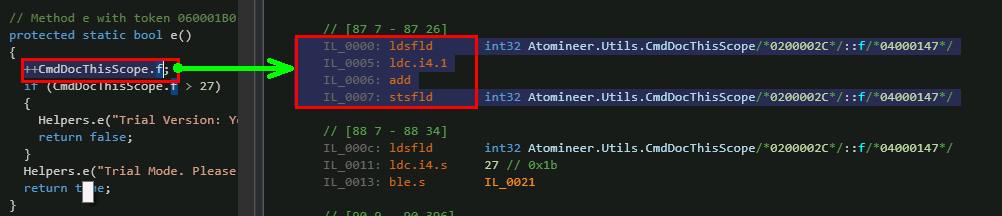
At the beginning of the CmdDocThisScope :: e method, the variable f is incremented. Open the “IL View” window and find the command code:
IL View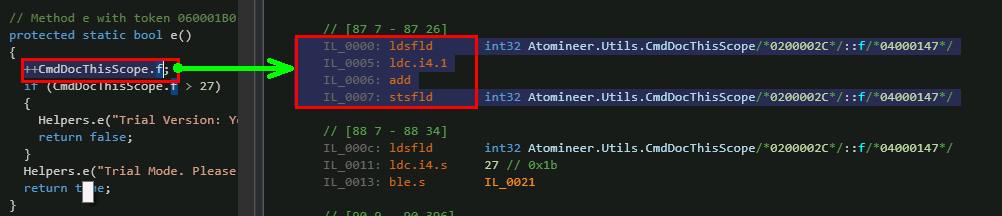
Wikipedia has an article describing these instructions .
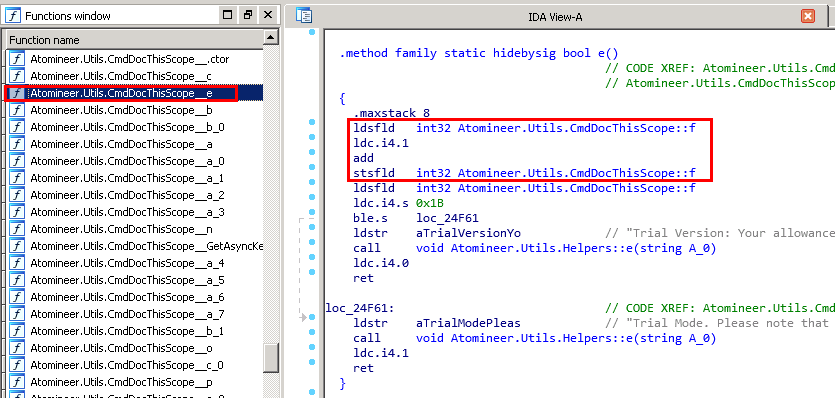
Next, find this method in the APD library file. We will do this using the IDA tool. In the window with the functions we will find our method, and we will see the already familiar code.
IDA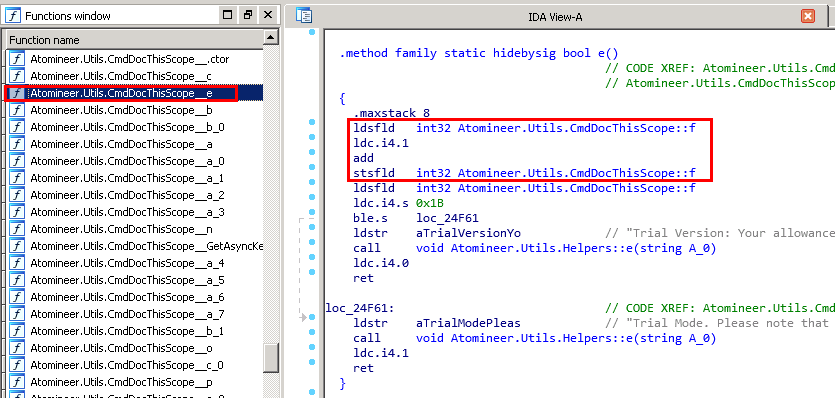
Having selected the ldsfld instruction, we find its binary representation in the Hex View window
Hex view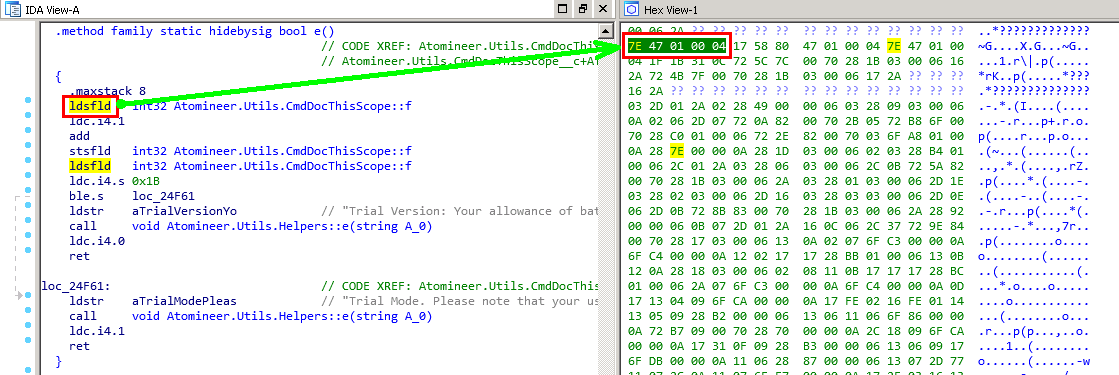
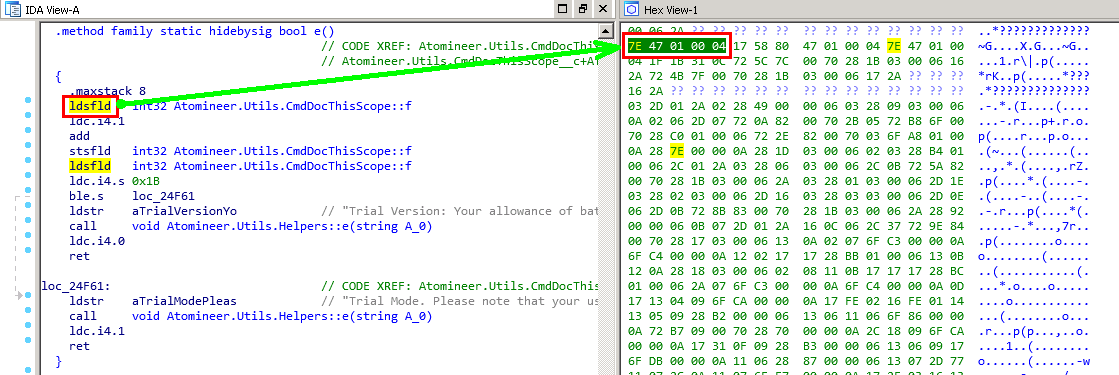
The description of the team confirms that we have found the right place.
Wiki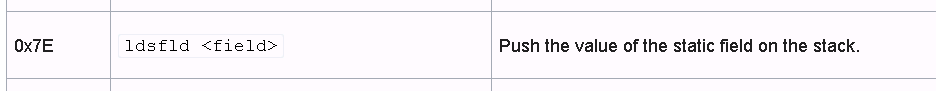
Further analysis of the code for this method and subsequent steps are beyond the scope of this article.
Part 2
Now, as already experienced researchers, we find a call to the dialogue with the message “ The 'Document all in Project' command is only available in the full version ... ”. Here is this method CmdDocThisProject :: c
CmdDocThisProject :: c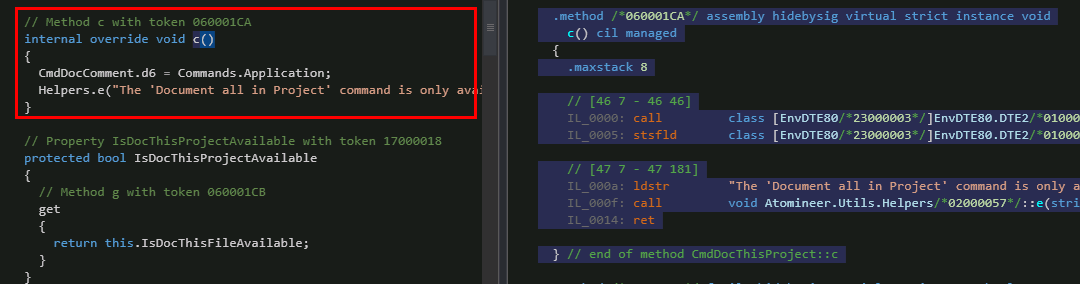
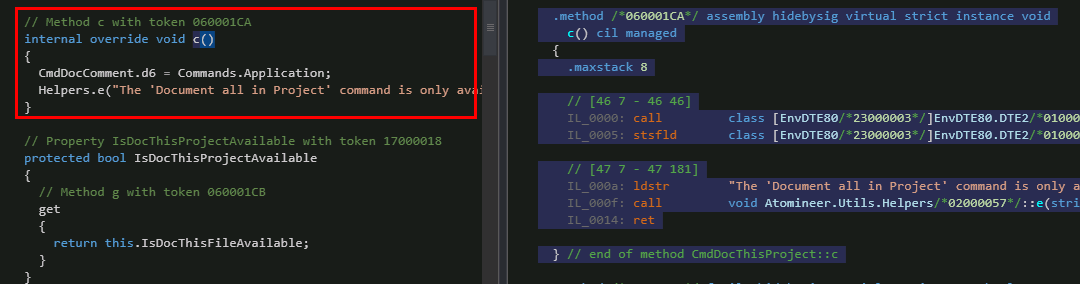
The CmdDocThisProject class is responsible for the “Process Project” command, the “c” method is virtual. And it contains only one thing - it is a call to a dialogue with a message. No conditions, no checks. Searching the source code leads us to the CmdDocThisProject :: i method, which has what we expect in CmdDocThisProject :: c. Now in IDA we can easily find the necessary methods and can learn CIL instructions
Conclusion
It remains to say that the article deliberately left white spots for their independent study.
