Elementary ciphers in plain language
Hello, Habr!
We all quite often hear such words and phrases as “data encryption”, “secret ciphers”, “cryptographic protection”, “encryption”, but not everyone understands what exactly is meant. In this post we will understand what encryption is and consider elementary ciphers so that even people far from IT understand the essence of this phenomenon.
First of all, we will understand the terminology.
Encryption is a transformation of the original message that will not allow any bad people to read the data if they intercept this message. This transformation is done using special mathematical and logical algorithms, some of which we will consider below.
Original message- this, in fact, is what we want to encrypt. A classic example is text.
An encrypted message is a message that has passed the encryption process.
A cipher is the algorithm itself by which we convert the message.
A key is a component based on which encryption or decryption can be performed.
The alphabet is a list of all possible characters in the original and encrypted message. Including numbers, punctuation, spaces, separately lowercase and capital letters, etc.
Now that we speak more or less the same language, we will analyze simple ciphers.
The easiest cipher. Its essence is the upturn of the alphabet.
For example, we have an alphabet that is fully consistent with the usual Latin alphabet.
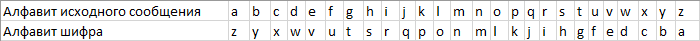
To implement the Atbash cipher, we simply invert it. “A” will become “Z”, “B” will turn into “Y” and vice versa. At the output, we get the following picture:
And now we write the desired
message in the original alphabet and cipher alphabet Original message: I love habr
Encrypted: r olev szyi
Here one more parameter is added - a primitive key in the form of a number from 1 to 25 (for the Latin alphabet). In practice, the key will be from 4 to 10.
Again, for clarity, we take the Latin alphabet
And now move each letter to the right or left by a key number of values.
For example, the key will be 4 and the shift to the right.
Original alphabet: abcdefghijklmnopqrstu vwxyz
Encrypted: wxyzabcdefghijklmnopq rstuv
Try to write a message:
We encrypt it and get the following incoherent text:
The simplest binary-based cipher that has absolute cryptographic strength. Without knowledge of the key, it is impossible to decrypt it (proved by Claude Shannon).
The original alphabet is still the same Latin.
The message is divided into separate characters and each character is presented in binary form.
Cryptography classics offer a five-digit bodo code for each letter. We will try to change this cipher for encoding at 8 bits / character using the example of an ASCII table. We represent each letter in the form of a binary code.

Now remember the electronics course and the XOR element, also known as XOR.
XOR receives signals (0 or 1 each), performs a logical operation on them and gives one signal based on the input values.
If all signals are equal (0-0 or 1-1 or 0-0-0, etc.), then the output is 0.
If the signals are not equal (0-1 or 1-0 or 1-0- 0, etc.), then the output is 1.
Now, to encrypt the message, enter the text itself for encryption and the key is the same length. We translate each letter into its binary code and execute the formula message XOR key
For example:
message: LONDON
key: SYSTEM
Translate them into binary code and execute XOR:
In this particular example, in place of the resulting characters, we will see only an empty place, because all the characters are in the first 32 service characters. However, if we translate the result into numbers, we get the following picture:
In appearance - a completely incoherent set of numbers, but we know something.
The encryption principle is about the same as Caesar’s cipher. Only in this case we shift the alphabet not by a certain number of positions, but by a code word.
For example, take the Cyrillic alphabet for a change.
We’ll come up with a code word. For example, Lukomorye. Remove all duplicate characters from it. At the output we get the word "Lukomrier".
Now we enter this word at the beginning of the alphabet, and leave the remaining characters unchanged.
And now we will record any message and encrypt it.
We get the following unreadable nonsense:
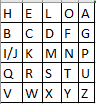
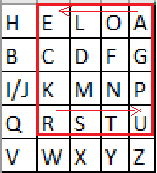
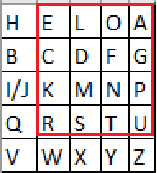
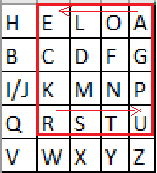
The classical Playfer cipher assumes a 5x5 matrix based on the Latin alphabet characters (i and j are written in one cell), a code word and further manipulation of them.
Let the code word be “HELLO”.
First, we act as with the previous cipher, i.e. remove the repetitions and write the word at the beginning of the alphabet.
Now take any message. For example, “I LOVE HABR AND GITHUB”.
We break it into bigrams, i.e. into pairs of characters, not including spaces.
If the message were from an odd number of characters, or if there were two identical characters (LL, for example) in the bigram, then the X character is put in place of the missing or repeated character.
Encryption is performed according to several simple rules:
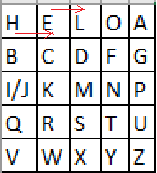
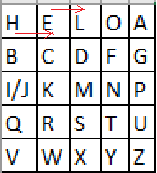
1) If the bigram characters are in the matrix on one line - we shift them to the right by one position. If the symbol was the last in a row - it becomes the first.
For example, EH becomes LE.
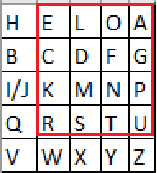
2) If the digram characters are in the same column, then they are shifted one position down. If the character was at the very bottom of the column, then it takes on the value of the topmost.
For example, if we had a LX bigram, then it would become DL.
3) If the characters are not on any row or column, then we build a rectangle, where our characters are the edges of the diagonal. And swap the corners.
For example, the bigram RA.
According to these rules, we encrypt the entire message.
If you remove the spaces, we get the following encrypted message:
Congratulations. After reading this article, you at least roughly understand what encryption is and you know how to use some primitive ciphers and you can begin to study some more complex cipher patterns, which we will talk about later.
Thanks for attention.
We all quite often hear such words and phrases as “data encryption”, “secret ciphers”, “cryptographic protection”, “encryption”, but not everyone understands what exactly is meant. In this post we will understand what encryption is and consider elementary ciphers so that even people far from IT understand the essence of this phenomenon.
First of all, we will understand the terminology.
Encryption is a transformation of the original message that will not allow any bad people to read the data if they intercept this message. This transformation is done using special mathematical and logical algorithms, some of which we will consider below.
Original message- this, in fact, is what we want to encrypt. A classic example is text.
An encrypted message is a message that has passed the encryption process.
A cipher is the algorithm itself by which we convert the message.
A key is a component based on which encryption or decryption can be performed.
The alphabet is a list of all possible characters in the original and encrypted message. Including numbers, punctuation, spaces, separately lowercase and capital letters, etc.
Now that we speak more or less the same language, we will analyze simple ciphers.
Atbash Cipher
The easiest cipher. Its essence is the upturn of the alphabet.
For example, we have an alphabet that is fully consistent with the usual Latin alphabet.
a b c d e f g h i j k l m n o p q r s t u v w x y zTo implement the Atbash cipher, we simply invert it. “A” will become “Z”, “B” will turn into “Y” and vice versa. At the output, we get the following picture:
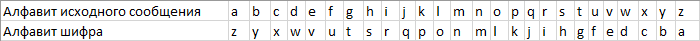
And now we write the desired
message in the original alphabet and cipher alphabet Original message: I love habr
Encrypted: r olev szyi
Caesar's code
Here one more parameter is added - a primitive key in the form of a number from 1 to 25 (for the Latin alphabet). In practice, the key will be from 4 to 10.
Again, for clarity, we take the Latin alphabet
a b c d e f g h i j k l m n o p q r s t u v w x y zAnd now move each letter to the right or left by a key number of values.
For example, the key will be 4 and the shift to the right.
Original alphabet: abcdefghijklmnopqrstu vwxyz
Encrypted: wxyzabcdefghijklmnopq rstuv
Try to write a message:
hello worldWe encrypt it and get the following incoherent text:
dahhk sknhzVernam cipher (XOR cipher)
The simplest binary-based cipher that has absolute cryptographic strength. Without knowledge of the key, it is impossible to decrypt it (proved by Claude Shannon).
The original alphabet is still the same Latin.
The message is divided into separate characters and each character is presented in binary form.
Cryptography classics offer a five-digit bodo code for each letter. We will try to change this cipher for encoding at 8 bits / character using the example of an ASCII table. We represent each letter in the form of a binary code.

Now remember the electronics course and the XOR element, also known as XOR.
XOR receives signals (0 or 1 each), performs a logical operation on them and gives one signal based on the input values.
If all signals are equal (0-0 or 1-1 or 0-0-0, etc.), then the output is 0.
If the signals are not equal (0-1 or 1-0 or 1-0- 0, etc.), then the output is 1.
Now, to encrypt the message, enter the text itself for encryption and the key is the same length. We translate each letter into its binary code and execute the formula message XOR key
For example:
message: LONDON
key: SYSTEM
Translate them into binary code and execute XOR:
01001100 01001111 01001110 01000100 01001111 01001110
01010011 01011001 01010011 01010100 01000101 01001101
_______________________________________________________
00011111 00010110 00011101 00010000 00001010 00000011In this particular example, in place of the resulting characters, we will see only an empty place, because all the characters are in the first 32 service characters. However, if we translate the result into numbers, we get the following picture:
31 22 29 16 10 3. In appearance - a completely incoherent set of numbers, but we know something.
Codeword Code
The encryption principle is about the same as Caesar’s cipher. Only in this case we shift the alphabet not by a certain number of positions, but by a code word.
For example, take the Cyrillic alphabet for a change.
абвгдеёжзийклмнопрстуфхцчшщъыьэюяWe’ll come up with a code word. For example, Lukomorye. Remove all duplicate characters from it. At the output we get the word "Lukomrier".
Now we enter this word at the beginning of the alphabet, and leave the remaining characters unchanged.
абвгдеёжзийклмнопрстуфхцчшщъыьэюя
лукомрьеабвгдёжзийнпстфхцчшщъыэюя
And now we will record any message and encrypt it.
"Златая цепь на дубе том"We get the following unreadable nonsense:
"Адлпля хриы жл мсур пиё"Playfer Code
The classical Playfer cipher assumes a 5x5 matrix based on the Latin alphabet characters (i and j are written in one cell), a code word and further manipulation of them.
Let the code word be “HELLO”.
First, we act as with the previous cipher, i.e. remove the repetitions and write the word at the beginning of the alphabet.
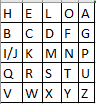
Now take any message. For example, “I LOVE HABR AND GITHUB”.
We break it into bigrams, i.e. into pairs of characters, not including spaces.
IL OV EH AB RA ND GI TH UB.If the message were from an odd number of characters, or if there were two identical characters (LL, for example) in the bigram, then the X character is put in place of the missing or repeated character.
Encryption is performed according to several simple rules:
1) If the bigram characters are in the matrix on one line - we shift them to the right by one position. If the symbol was the last in a row - it becomes the first.
For example, EH becomes LE.
2) If the digram characters are in the same column, then they are shifted one position down. If the character was at the very bottom of the column, then it takes on the value of the topmost.
For example, if we had a LX bigram, then it would become DL.
3) If the characters are not on any row or column, then we build a rectangle, where our characters are the edges of the diagonal. And swap the corners.
For example, the bigram RA.
According to these rules, we encrypt the entire message.
IL OV EH AB RA ND GI TH UB.
KO HY LE HG EU MF BP QO QGIf you remove the spaces, we get the following encrypted message:
KOHYLEHGEUMFBPQOQGCongratulations. After reading this article, you at least roughly understand what encryption is and you know how to use some primitive ciphers and you can begin to study some more complex cipher patterns, which we will talk about later.
Thanks for attention.
