Why expose a management interface or attack on Cisco Smart Install on the Internet
Recently, Cisco found out about some hacking groups that target Cisco switches as their target, using the problem of protocol misuse in the Cisco Smart Install Client. Several incidents in different countries, including some related to critical infrastructure, have been associated with the improper use of the Smart Install protocol. Some experts believe that a number of these attacks are associated with hackers in the service of the state. As a result, we take an active position and urge customers, again, to assess risks and apply the available methods of risk neutralization.
On February 14, 2017 (yes, there’s no mistake, it's about 2017), the Cisco Product Security Incident Response Team (PSIRT) published a newsletter describing the results of an active scan related to Cisco Smart Install Clients. The Cisco Smart Install Client software is an outdated utility designed to remotely configure new Cisco equipment, in particular Cisco switches. Continuing, Cisco Talos posted a blog post and released an open source tool that scans devices using the Cisco Smart Install protocol. In addition to the described, a signature was released for the Snort attack detection system (SID: 41722-41725), which allows detecting any attempts to use this technology.
Cisco Smart Install can be abused to change the configuration of the TFTP server, export configuration files via TFTP, change configuration files, replace the image of the IOS network operating system, and set up accounts that enable IOS commands. Although this is not a vulnerability in the classical sense, misuse of this protocol can serve as an attack vector that should be immediately neutralized. During the end of 2017 and the beginning of 2018, Talos observed how attackers tried to scan clients using this vulnerability. Recent information has increased the relevance of this problem and we decided to return to it again.
Although we only observed attacks related to the problem of improper use of the Cisco Smart Install protocol, it was recently disclosed andAnother vulnerability in the Cisco Smart Install Client has been fixed . This vulnerability was discussed publicly, and code was issued proving the possibility of exploitation of the vulnerability (PoC). To resolve the problem of improper use of the protocol, clients should also eliminate this vulnerability by installing the appropriate update.
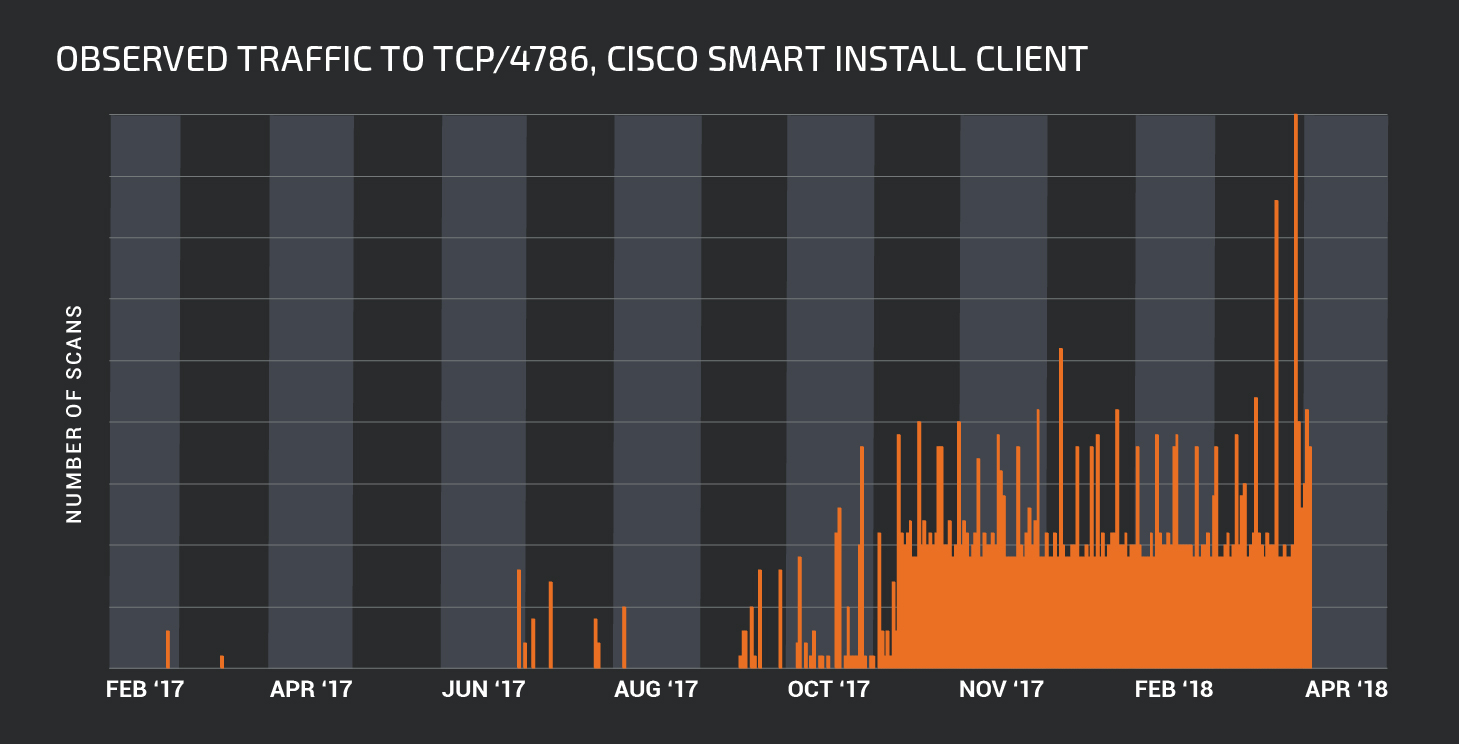
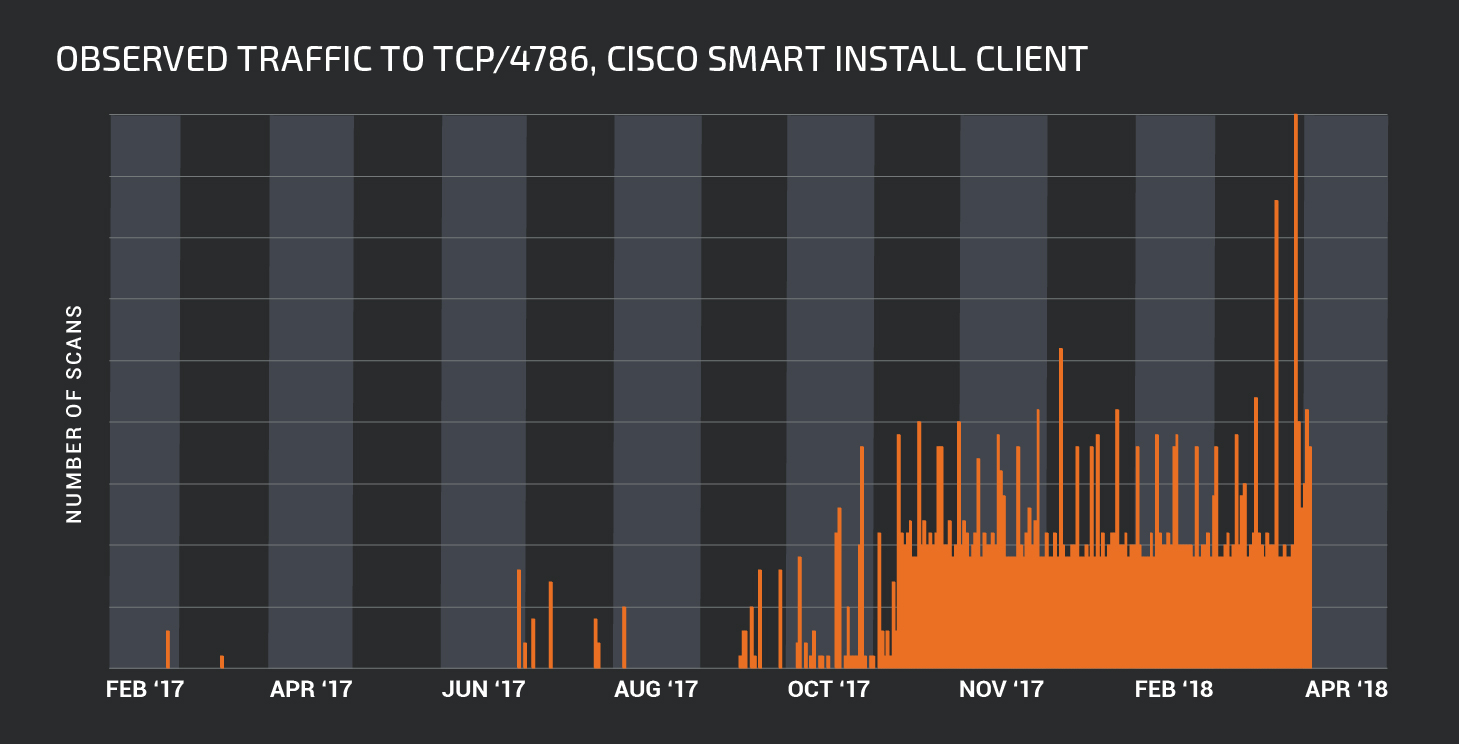
As part of the Cisco Talos study, we began to examine how many devices are potentially vulnerable to this attack. The results were extremely alarming. Using Shodan, Talos was able to determine that more than 168,000 systems could potentially be discovered through the “open to the Internet” Cisco Smart Install Client. This is better than the results of 2016, when a Tenable employee reported 251,000 vulnerable Cisco Smart Install Client clients that were “visible” from the Internet. There may be differences in the scanning methodology of Cisco Talos and Tenable, but we expect a significant reduction in the number of devices available for attack. In addition, although there has been a decrease in scan volumes since our initial newsletter, Talos has seen a sharp increase in scan attempts for the Cisco Smart Install Client around November 9, 2017.
You can determine if you have a device “up” on the Cisco Smart Install Client software switch. Running the show vstack config command will let you determine if Smart Install Client is active. The following is an example of such a command with a response to it:
Additional symptoms of an active Cisco Smart Install Client may be present if Level 6 (informational) or higher registration is enabled. These event logs may include, but are not limited to, TFTP write operations, command execution, and device reboots.
The easiest way to neutralize this problem is to run the no vstack command on the vulnerable device. If for some reason this option is not available to the client, the best option would be to restrict access through the access control list (ACL) for the interface, an example of which is shown below:
This type of ACL allows only the nodes shown above access to the Smart Install Client, which greatly limits the ability to implement the attack. In addition to this, there are signatures in our Intrusion Prevention System (IPS) that allow us to determine whether the Smart Install Client is affected or not.
For this and other issues, it’s important to remember Cisco’s commitment to supporting affected customers. All customers, regardless of the status of the support contract, receive free incident response assistance, as well as assistance offered to contract customers for any incident involving known or reasonably suspicious security vulnerabilities in the Cisco product. If you encounter an incident with a Cisco product, contact the Cisco Technical Assistance Center (TAC):
For more information, see Cisco Vulnerability Security Policy .
To ensure security and perimeter control, network administrators need to be especially vigilant. It’s easy to “install and forget” network devices because they are usually very stable and rarely change. It’s enough to recall the results of our last year’s annual report on cybersecurity, in which we demonstrated the results of our study, which proves that the average time to eliminate clientsvulnerabilities in network and server hardware and software is on average about five years. Combine this with the advantages that an attacker has when gaining access and taking control of a network device and you will realize that routers and switches become very attractive targets for attackers. Especially when it comes to devices standing on the perimeter of the organization or telecom operator.
Observing the active use of this vector by cybercriminals, Cisco strongly recommends that all customers review their architecture, use Talos tools to scan their network and remove the Cisco Smart Install Client from all devices where it is not used.
On February 14, 2017 (yes, there’s no mistake, it's about 2017), the Cisco Product Security Incident Response Team (PSIRT) published a newsletter describing the results of an active scan related to Cisco Smart Install Clients. The Cisco Smart Install Client software is an outdated utility designed to remotely configure new Cisco equipment, in particular Cisco switches. Continuing, Cisco Talos posted a blog post and released an open source tool that scans devices using the Cisco Smart Install protocol. In addition to the described, a signature was released for the Snort attack detection system (SID: 41722-41725), which allows detecting any attempts to use this technology.
Cisco Smart Install can be abused to change the configuration of the TFTP server, export configuration files via TFTP, change configuration files, replace the image of the IOS network operating system, and set up accounts that enable IOS commands. Although this is not a vulnerability in the classical sense, misuse of this protocol can serve as an attack vector that should be immediately neutralized. During the end of 2017 and the beginning of 2018, Talos observed how attackers tried to scan clients using this vulnerability. Recent information has increased the relevance of this problem and we decided to return to it again.
Although we only observed attacks related to the problem of improper use of the Cisco Smart Install protocol, it was recently disclosed andAnother vulnerability in the Cisco Smart Install Client has been fixed . This vulnerability was discussed publicly, and code was issued proving the possibility of exploitation of the vulnerability (PoC). To resolve the problem of improper use of the protocol, clients should also eliminate this vulnerability by installing the appropriate update.
Scope
As part of the Cisco Talos study, we began to examine how many devices are potentially vulnerable to this attack. The results were extremely alarming. Using Shodan, Talos was able to determine that more than 168,000 systems could potentially be discovered through the “open to the Internet” Cisco Smart Install Client. This is better than the results of 2016, when a Tenable employee reported 251,000 vulnerable Cisco Smart Install Client clients that were “visible” from the Internet. There may be differences in the scanning methodology of Cisco Talos and Tenable, but we expect a significant reduction in the number of devices available for attack. In addition, although there has been a decrease in scan volumes since our initial newsletter, Talos has seen a sharp increase in scan attempts for the Cisco Smart Install Client around November 9, 2017.
Neutralization
You can determine if you have a device “up” on the Cisco Smart Install Client software switch. Running the show vstack config command will let you determine if Smart Install Client is active. The following is an example of such a command with a response to it:
switch # show vstack config | inc Role
Role: Client (SmartInstall enabled)
Additional symptoms of an active Cisco Smart Install Client may be present if Level 6 (informational) or higher registration is enabled. These event logs may include, but are not limited to, TFTP write operations, command execution, and device reboots.
The easiest way to neutralize this problem is to run the no vstack command on the vulnerable device. If for some reason this option is not available to the client, the best option would be to restrict access through the access control list (ACL) for the interface, an example of which is shown below:
ip access-list extended SMI_HARDENING_LIST
permit tcp host 10.10.10.1 host 10.10.10.200 eq 4786
deny tcp any any eq 4786
permit ip any anyThis type of ACL allows only the nodes shown above access to the Smart Install Client, which greatly limits the ability to implement the attack. In addition to this, there are signatures in our Intrusion Prevention System (IPS) that allow us to determine whether the Smart Install Client is affected or not.
Support
For this and other issues, it’s important to remember Cisco’s commitment to supporting affected customers. All customers, regardless of the status of the support contract, receive free incident response assistance, as well as assistance offered to contract customers for any incident involving known or reasonably suspicious security vulnerabilities in the Cisco product. If you encounter an incident with a Cisco product, contact the Cisco Technical Assistance Center (TAC):
- In Moscow: +7 495 961 13 82
- In St. Petersburg: +7 812 363-3328
- Free call in Russia: 8 800 700 05 22
- In Armenia: 800-721-7549
- In Belarus: 8 800 101, then 800 721 7549
- In Ukraine (main): 0800 301 2090 (toll free)
- In Ukraine (alternative): +380 44 390 2400
- In Azerbaijan: 088 9999999
- In Kazakhstan: 8 ^ 800-121-4321 (dial 8, wait for the 2nd signal and then dial the remaining digits). Then dial PIN, 800-721-7549
- In Tajikistan: + 992 44 600 60 40
- In Uzbekistan: 800-721-7549
For more information, see Cisco Vulnerability Security Policy .
conclusions
To ensure security and perimeter control, network administrators need to be especially vigilant. It’s easy to “install and forget” network devices because they are usually very stable and rarely change. It’s enough to recall the results of our last year’s annual report on cybersecurity, in which we demonstrated the results of our study, which proves that the average time to eliminate clientsvulnerabilities in network and server hardware and software is on average about five years. Combine this with the advantages that an attacker has when gaining access and taking control of a network device and you will realize that routers and switches become very attractive targets for attackers. Especially when it comes to devices standing on the perimeter of the organization or telecom operator.
Observing the active use of this vector by cybercriminals, Cisco strongly recommends that all customers review their architecture, use Talos tools to scan their network and remove the Cisco Smart Install Client from all devices where it is not used.
Additional Information
- Cisco Bulletin Misuse of the Cisco Smart Install Protocol
- Cisco RCE Smart Install Vulnerability Bulletin
- Cisco DDoS Smart Install Vulnerability Bulletin
- Note on Cisco Talos Blog on Misuse of Smart Install
- Smart Install Client Scanner Developed by Cisco Talos
- This original article in Talos blog
- Cisco Guidelines for Enhancing Security for Cisco IOS and IOS XE Devices
