Malvar who reads memes
- Transfer
For a long time there were no articles about steganography. Here's an example of how hackers disguise their attacks as harmless traffic using social networks.
Each botnet needs to communicate with its control center to receive commands, instructions, updates and perform various tasks on infected devices. As security products scan network traffic to prevent communication with malicious IP addresses, attackers are increasingly using “legal” services in their attack infrastructures to make them more difficult to detect.
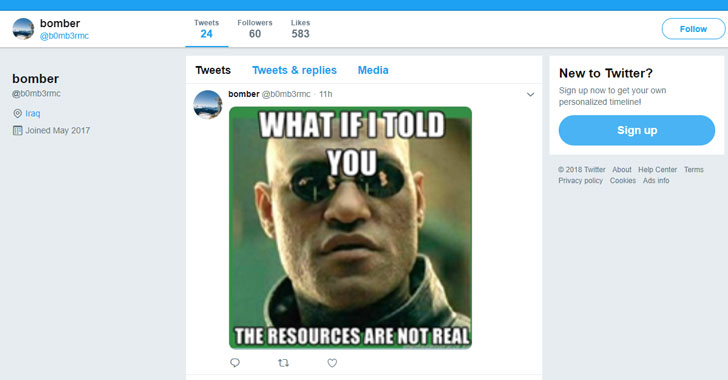
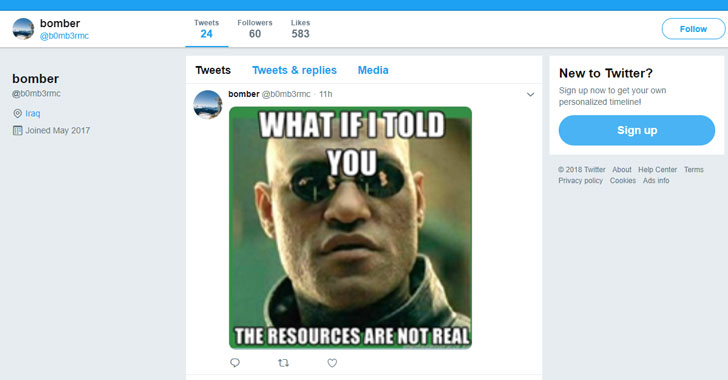
Trend Micro researchers have found an example of such a scheme: a new malware extracts commands from memes hosted on a Twitter account controlled by intruders. For us, the audience, this meme looks like a regular picture, but the file metadata contains commands available only to malware.
Here is a fragment of a malicious program that downloads pictures from an attacker on Twitter and searches for secret commands.

According to the researchers, the Twitter account in question was created in 2017 and contained only two memes containing commands for creating screenshots and sending them to the attacker's server, the program receives the address through pastebin service.
The researchers believe that the malware is in the early stages of its development, since Pastebin has a local IP address as the north, which may be a temporary stub.
It is worth noting that the malware was not downloaded from Twitter itself, and the researchers have not yet discovered what mechanism was used or could be used by attackers to deliver malware to the victims' computers.
At the moment, the Twitter account used to deliver malicious memes is disabled, but it is still unclear who is behind this malware and how the mysterious hacker distributed the malware.
Each botnet needs to communicate with its control center to receive commands, instructions, updates and perform various tasks on infected devices. As security products scan network traffic to prevent communication with malicious IP addresses, attackers are increasingly using “legal” services in their attack infrastructures to make them more difficult to detect.
Trend Micro researchers have found an example of such a scheme: a new malware extracts commands from memes hosted on a Twitter account controlled by intruders. For us, the audience, this meme looks like a regular picture, but the file metadata contains commands available only to malware.
Here is a fragment of a malicious program that downloads pictures from an attacker on Twitter and searches for secret commands.

According to the researchers, the Twitter account in question was created in 2017 and contained only two memes containing commands for creating screenshots and sending them to the attacker's server, the program receives the address through pastebin service.
Translator's note:In addition to sending screenshots, the malware can send lists of running processes, account names, retrieve lists of files from certain directories on an infected machine, and receive a dump from the user's clipboard.
The pastebin service allows users to exchange large amounts of textual information. Suppose you have written some code, sent it to pastebin, got a URL where other users can get your code. If you correct the code, then the users at the old URL will see the already corrected code. A kind githab, but only without a gita.
The researchers believe that the malware is in the early stages of its development, since Pastebin has a local IP address as the north, which may be a temporary stub.
It is worth noting that the malware was not downloaded from Twitter itself, and the researchers have not yet discovered what mechanism was used or could be used by attackers to deliver malware to the victims' computers.
At the moment, the Twitter account used to deliver malicious memes is disabled, but it is still unclear who is behind this malware and how the mysterious hacker distributed the malware.
