CTB-Locker. We decided to pay
CTB Locker is a very well thought out and dangerous virus. I will not write about it - there is a lot of information about this virus on the Internet.
Over the past 3 months, some of our customers have caught this beast, despite warnings, updated corporate antiviruses and other protection solutions. Some suffered a separate work machine, while others had a terminal server. But backup tools saved everyone.
The last infection of one of the clients led to the loss of a large amount of data, as well as some backups. The responsibility for this lay with the client - financing for the expansion of the backup server could not be allocated half a year. But that's not the point. We were given the task of paying the creators of the virus (and here funding was sharply found).
I do not agitate community users to pay attackers (I am opposed to this), but perhaps this small manual will help someone.
Next, I will describe step by step how I paid bad people for decrypting client data.
1. So, we hit. The user's computer has become infected (as soon as we get infected, we’ll still find out; there is anti-spam, anti-virus, user rights have been cut). Over the network, the virus encrypted the file server, the disk of which was connected to the user as a network drive. The virus encrypted those folders on the server for which the user had write permissions. Local drives on the user's computer were also encrypted.
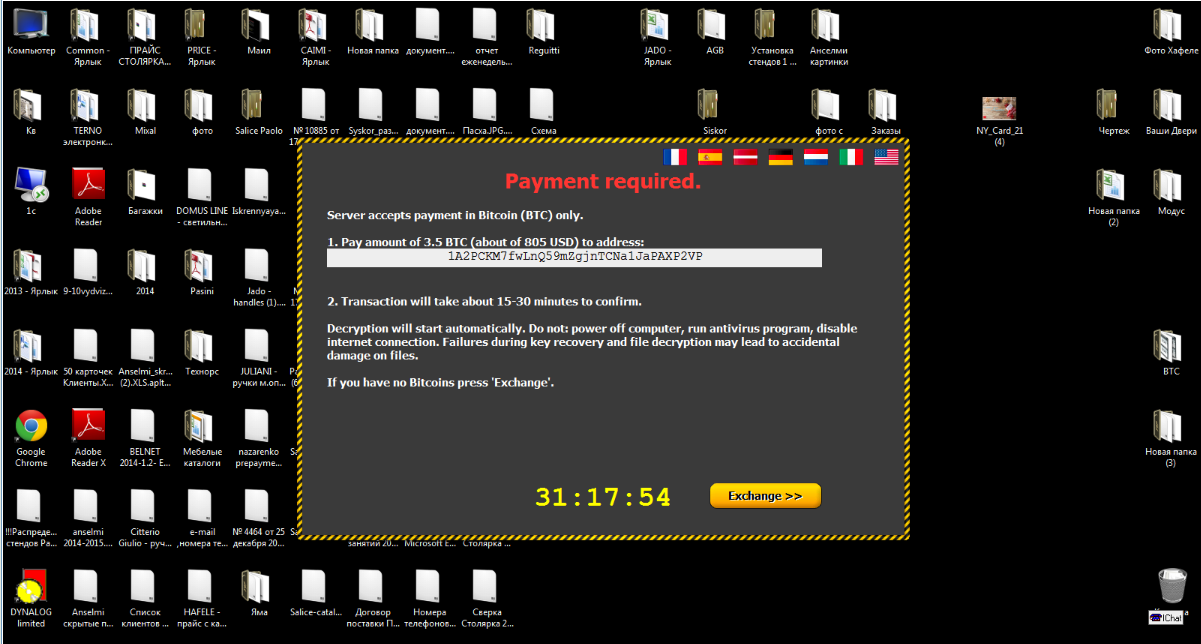
2. When the virus has finished encryption, it issued a banner to the user. We were asked to decrypt the data for 3.5 bitcoins, which is approximately $ 805. We were given 90 hours to make a decision.
3. On the local disk in the Documents folder instructions were found on how to proceed.
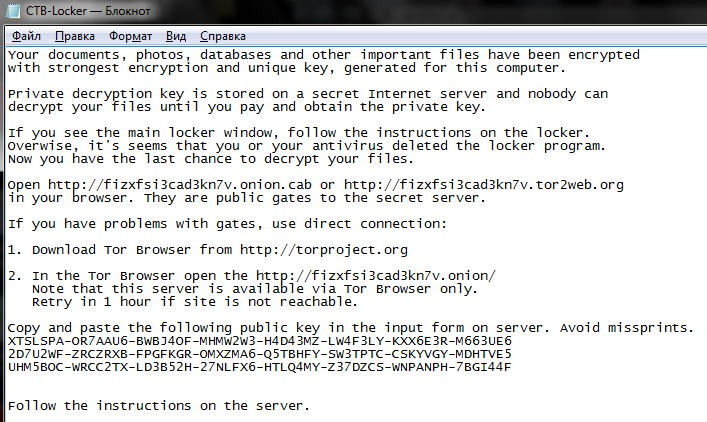
We were asked to go to the Tor network and enter the public key from this text file on the cybercriminals' website. Alas, I did not take a screenshot of the site, the site opens very rarely and I did not see anything new there. The site duplicated information from the banner on the user's desktop: information on the amount of the ransom, links to the site where you can buy bitcoins, wallet number where to transfer, etc., as well as a proposal to decrypt two files up to 1 megabyte each to prove the possibility of decryption .
4. Before starting all work, the infected user computer and file server were isolated on a separate network with a separate Internet connection. Checked the availability of a network drive. All OK. Getting started.
5. Search for bitcoins. I have not bought bitcoins before. Sites proposed by attackers to buy bitcoins did not suit us. We need to buy cryptocurrency with a payment card of a Ukrainian bank (created a virtual card). Went to look for ways to buy cryptocurrency. On the Internet, a Ukrainian site for buying and selling bitcoins was found.
a) register on the site (when registering, indicate your mobile - transaction confirmations will come to it), deposit UAH to the account.
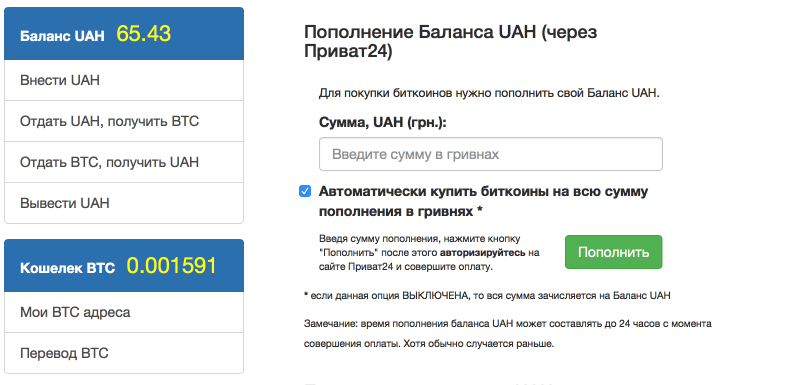
b) We buy bitcoins for hryvnia.
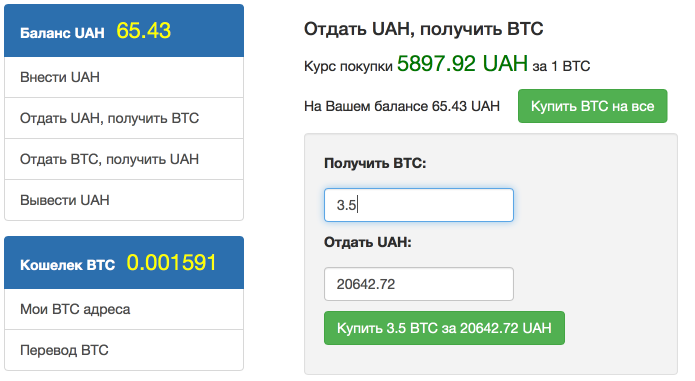
c) We transfer bitcoins to the wallet specified by the attackers. Pay attention to the commission of a bitcoin network.

We confirm the transaction via SMS from the phone specified during registration on the site. The transaction took about 10-15 minutes.
6. Waiting. So, we have fulfilled all the conditions of the attackers. What to do next? The Tor site is still not available. As it turned out, we were not deceived. The banner on the user's computer has changed from demanding money for information and that our information is now decrypted. Everything happened automatically.

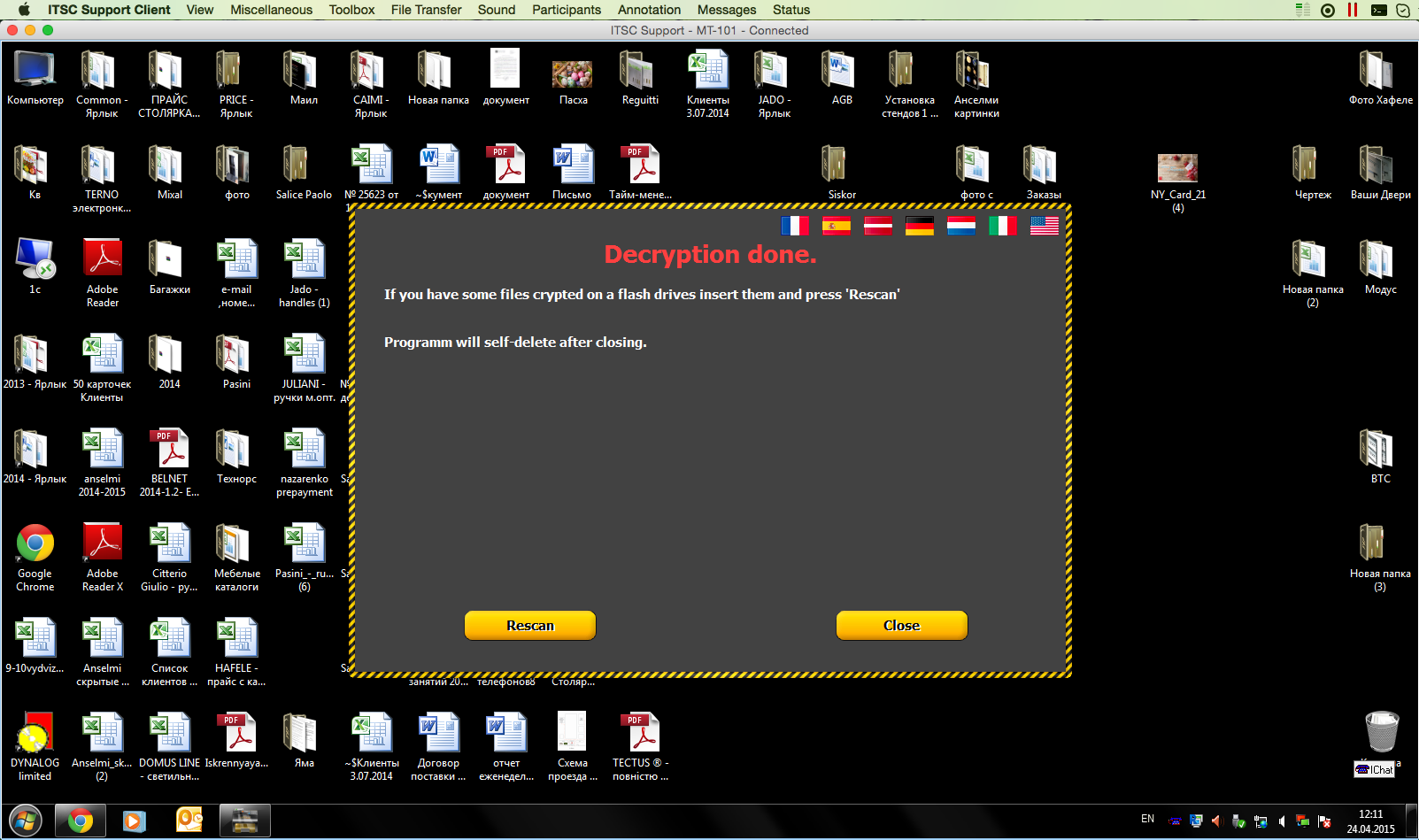
7. The decryption lasted about 2 hours. We check the file server - everything is in place, everything is perfectly decrypted. The banner offers us to make Rescan if we forgot to connect a network drive or insert a USB Flash / HDD, which was also previously encrypted, before decryption. Or click Close and it will delete itself from the computer.
8. We make a backup copy of the file server (again, funding was quickly found for expanding the space for backups).
9. Connect the file server back to the network to users. Format the user's computer, install Windows, etc.
10. We think about changing the antivirus.
I hope this publication helped someone. Or, at least, reminded about the importance of backup and fresh anti-virus databases.
