Practical aspects of using DHCP relay + option82
In this article, I would like to highlight the practical aspects of using DHCP relay + option82 as an authorization option (in the future, this bundle will be meant) , as well as provide examples of configuration of the Dlink DES-3200-10 switch and isc-dhcp-server. In almost all articles, dhcp relay is interpreted as follows: "you can move a dhcp server outside the broadcast domain." However, for some reason they do not mention or almost never mention that this is a good opportunity to get rid of broadcast requests within the same broadcast domain. And most importantly, what I focus on, we can be sure, thanks to option82, that the request came from the switch with the given poppy and from the port with the specified number, and therefore - this way you can "authorize" the user.
I’ll go a little further and recall how DHCP relay works. It will intercept the broadcast request (the VLAN it is configured to), wrap it in L3 and send it to the specified DHCP server unicast. Well, it’s not superfluous to recall what option82 does. It adds two additional parameters to the DHCP packet:
I also want to talk about the methods of implementing this option in the package. There are two ways in Dlink equipment:
A little deviate from the topic. The fact is that I found the dhcp_local_relay construct only in Dlink hardware. I wondered why other manufacturers did not implement such a wonderful option? It turns out, implemented, and for a long time. It is called DHCP Snooping.
Perhaps someone will ask a question: “why should we get rid of broadcast traffic”? The fact is that in practice I very often encountered such a phenomenon that when a switch fails, for example, as a result of a thunderstorm, loops occur, which leads to a broadcast storm. Of course, as you may have guessed, we still can’t get rid of one broadcast traffic in IPv4 - this is ARP traffic. He is responsible for building MAC-IP tables. Of course, you can disable this and fill out the tables manually. But, I'm afraid that the inconvenience caused by this will negate all the charms of static ARP tables.
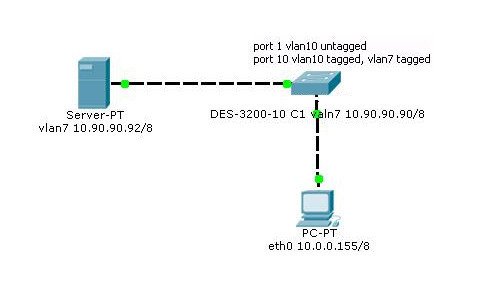
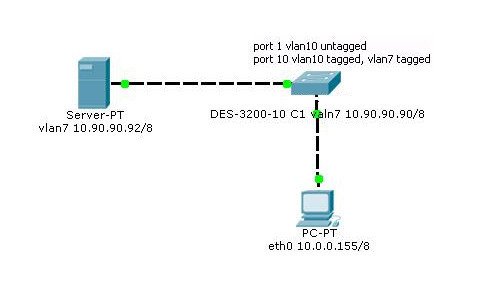
All articles indicate that the DHCP client and the DHCP server can (should) be on different subnets - this is not true. Here is our diagram:
Next I will give an example of configurations:
DLINK DES-3200
Now the config isc-dhcp-server (isc-dhcpd-4.2.4) on
Linux big-A75F-M2 3.13.0-24-generic # 47-Ubuntu SMP Fri May 2 23:30:00 UTC 2014 x86_64 x86_64 x86_64 GNU / Linux:
Of course, this is only a stand-alone config, but the most important thing for us to figure out is how it works. Still, looking ahead I can say that I have a billing system with option82 and the dhcp_local_relay (dhcp snooping) construct, and freeradius2 is used as a server with perl-selection of IP addresses from the postgres database. But this is already beyond the scope of this article.
On the machine with the server, run:
And if we saw something like:
That is, there are no broadcasts, which means that everything is going well and it is time to launch our DHCP server.
For the first time, I recommend starting it by simply typing in the line:
Then you will immediately see all the errors, if any, and there must be a record of the form:
Just in case, you can check after a few seconds:
Should return the UID of the process, if nothing comes out, check the configuration.
Why is such a check necessary? I remember cases when the server started, hung in memory for several seconds and crashed. And I tried in vain to get an IP address.
If everything went well, in the logs we will find something like:
Now one very important thing, it has not been written about anywhere, but I reached it experimentally. The IP address of the switch must be on the same subnet as the addresses issued to subscribers . Under no other combinations did I manage to get the Dlink DES-3200 bundle working (Boot PROM Version: Build 4.00.002 Firmware Version: Build 4.04.004 Hardware Version: C1) and isc-dhcp-server 4.2.4.
And there’s not a big bonus, how not to die from Broadcasts. Config for Dlink DES-3200 C1:
This article is not a clone or attempt to rewrite other people's articles in your own words. Below is a list of similar publications and differences from them. In my article, I focused on the use of this design as an authorization method, rather than trying to take a DHCP server out of the network.
- xgu.ru/wiki/%D0%9E%D0%BF%D1%86%D0%B8%D1%8F_82_DHCP - there is an error here, I spent a lot of time to find it. I wrote about it above (the switch’s IP address must be on the same subnet as the addresses given to subscribers. Under no other combinations did I manage to get the Dlink DES-3200 bundle working (Boot PROM Version: Build 4.00.002 Firmware Version : Build 4.04.004 Hardware Version: C1) and isc-dhcp-server 4.2.4.) ;
habrahabr.ru/post/143846- here dhcp is moved outside the network;
www.dlink.ru/ru/faq/62/228.html - here also dhcp is moved outside the network.
I’ll go a little further and recall how DHCP relay works. It will intercept the broadcast request (the VLAN it is configured to), wrap it in L3 and send it to the specified DHCP server unicast. Well, it’s not superfluous to recall what option82 does. It adds two additional parameters to the DHCP packet:
DHCP-Relay-Circuit-Id - port number from which the request came.
DHCP-Relay-Remote-Id - (by default) the switch mac address from which the request came.
I also want to talk about the methods of implementing this option in the package. There are two ways in Dlink equipment:
dhcp_relay - adds Option82 and, as described above, wraps it in L3 and sends it unicast to the specified DHCP server
dhcp_local_relay (DHCP Snooping) - only adds Option82 and forwards the broadcast packet further.
A little deviate from the topic. The fact is that I found the dhcp_local_relay construct only in Dlink hardware. I wondered why other manufacturers did not implement such a wonderful option? It turns out, implemented, and for a long time. It is called DHCP Snooping.
Perhaps someone will ask a question: “why should we get rid of broadcast traffic”? The fact is that in practice I very often encountered such a phenomenon that when a switch fails, for example, as a result of a thunderstorm, loops occur, which leads to a broadcast storm. Of course, as you may have guessed, we still can’t get rid of one broadcast traffic in IPv4 - this is ARP traffic. He is responsible for building MAC-IP tables. Of course, you can disable this and fill out the tables manually. But, I'm afraid that the inconvenience caused by this will negate all the charms of static ARP tables.
All articles indicate that the DHCP client and the DHCP server can (should) be on different subnets - this is not true. Here is our diagram:
Next I will give an example of configurations:
DLINK DES-3200
config vlan default delete 1-10 # Remove all ports from the default VLAN create vlan VLAN7 tag 7 # Create the VLAN where our DHCP server is located config vlan VLAN7 add tagged 9-10 # Add tagged ports 9 and 10 there (look towards the provider) create vlan VLAN10 tag 10 # We create VLAN 10 in which we have subscribers config vlan VLAN10 add tagged 9 -10 # Add tagged ports 9 and 10 there config vlan VLAN10 add untagged 1-8 # Add untagged ports 1-8 there (subscriber ports) config ipif System ipaddress 10.90.90.90/8 # Set the IP address of the switch config ipif System vlan VLAN7 # We hang it on VLAN7 enable dhcp_relay # Activate the option config dhcp_relay option_82 policy replace # We say that if the information in the package is already there, then replace config dhcp_relay option_82 remote_id default # Just save the default settings (poppy) config dhcp_relay option_82 circuit_id default # Just save the default settings (port number) config dhcp_relay add vlanid 10 10.90.90.92 # We say that all traffic with VLAN10 is intercepted and sent to a DHCP server with the address 10.90.90.92 create iproute default 10.90.90.92 # We create a default route, in this example I’m not sure what is needed at all, but Feng Shui
Now the config isc-dhcp-server (isc-dhcpd-4.2.4) on
Linux big-A75F-M2 3.13.0-24-generic # 47-Ubuntu SMP Fri May 2 23:30:00 UTC 2014 x86_64 x86_64 x86_64 GNU / Linux:
$ sudo apt-get install vlan-tools isc-dhcp-server
$ sudo vconfig add eth0 7
$ sudo ifconfig eth0.7 10.90.90.92/8
# Create VLAN7 and assign the address 10.90.90.92/8 on which we will have the DHCP server
local-address 10.90.90.92;
# Theoretically, this should indicate where the socket will be created for wiretapping, but in practice I realized that this option is a rudiment, I tried to change it and comment nothing has changed, but as they say by Feng Shui it should be :). In general, I must say that the server will "spit" on all your instructions and will automatically hang up on the IP interfaces that fall into the subnet described in the subnet section!
if exists agent.circuit-id
{
log (info, concat ("Lease for", binary-to-ascii (10, 8, ".", leased-address) ,.
"raw option-82 info is CID:", binary-to-ascii (10, 8, ".", option agent.circuit-id), "AID:",
binary-to-ascii (16, 8, ".", option agent.remote-id)));
}
# This simply outputs entries to our log file if option 82 is detected
subnet 10.0.0.0 netmask 255.0.0.0 {
pool {
range 10.0.0.155;
}
}
# Set the subnet and pool
Of course, this is only a stand-alone config, but the most important thing for us to figure out is how it works. Still, looking ahead I can say that I have a billing system with option82 and the dhcp_local_relay (dhcp snooping) construct, and freeradius2 is used as a server with perl-selection of IP addresses from the postgres database. But this is already beyond the scope of this article.
On the machine with the server, run:
$ sudo tcpdump -i eth0.7 -e -n -t
And if we saw something like:
c0: a0: bb: 48: e5: b0> 00: 15: 17: db: e3: e0 , ethertype IPv4 (0x0800), length 345: 10.90.90.90.68> 10.90.90.92.67 : BOOTP / DHCP, Request from 48: 5b: 39: 43: 78: e5, length 303
That is, there are no broadcasts, which means that everything is going well and it is time to launch our DHCP server.
For the first time, I recommend starting it by simply typing in the line:
$ sudo dhcpd
Then you will immediately see all the errors, if any, and there must be a record of the form:
Listening on LPF / eth0.7 / 00: 15: 17: db: e3: e0 / 10.0.0.0 / 8
Sending on LPF / eth0.7 / 00: 15: 17: db: e3: e0 / 10.0.0.0 / 8
Just in case, you can check after a few seconds:
$ pgrep dhcpd
Should return the UID of the process, if nothing comes out, check the configuration.
Why is such a check necessary? I remember cases when the server started, hung in memory for several seconds and crashed. And I tried in vain to get an IP address.
If everything went well, in the logs we will find something like:
Dec 2 20:36:17 big-A75F-M2 dhcpd: DHCPREQUEST for 10.0.0.155 from 48: 5b: 39: 43: 78: e5 (big-1001PX) via 10.90.90.90
Dec 2 20:36:17 big-A75F -M2 dhcpd: DHCPACK on 10.0.0.155 to 48: 5b: 39: 43: 78: e5 (big-1001PX) via 10.90.90.90
Dec 2 20:38:06 big-A75F-M2 dhcpd: Lease for 10.0.0.155 raw option-82 info is CID: 0.4.0.10.0.3 AID: 0.6.c0.a0.bb.48.e5.b0
Now one very important thing, it has not been written about anywhere, but I reached it experimentally. The IP address of the switch must be on the same subnet as the addresses issued to subscribers . Under no other combinations did I manage to get the Dlink DES-3200 bundle working (Boot PROM Version: Build 4.00.002 Firmware Version: Build 4.04.004 Hardware Version: C1) and isc-dhcp-server 4.2.4.
And there’s not a big bonus, how not to die from Broadcasts. Config for Dlink DES-3200 C1:
config safeguard_engine state enable config safeguard_engine utilization rising 90 falling 30 state enable # This is processor overload protection config traffic control 1-8 broadcast enable multicast enable unicast disable action drop threshol d 64 countdown 5 time_interval 5 # This will save you from multiple Broadcasts generated by customers enable loopdetect config loopdetect ports 1-8 state enable config loopdetect recover_timer 1200 interval 10 mode port-based # And this will save from loops if they are already formed
This article is not a clone or attempt to rewrite other people's articles in your own words. Below is a list of similar publications and differences from them. In my article, I focused on the use of this design as an authorization method, rather than trying to take a DHCP server out of the network.
- xgu.ru/wiki/%D0%9E%D0%BF%D1%86%D0%B8%D1%8F_82_DHCP - there is an error here, I spent a lot of time to find it. I wrote about it above (the switch’s IP address must be on the same subnet as the addresses given to subscribers. Under no other combinations did I manage to get the Dlink DES-3200 bundle working (Boot PROM Version: Build 4.00.002 Firmware Version : Build 4.04.004 Hardware Version: C1) and isc-dhcp-server 4.2.4.) ;
habrahabr.ru/post/143846- here dhcp is moved outside the network;
www.dlink.ru/ru/faq/62/228.html - here also dhcp is moved outside the network.
