Study: Intercepting Mobile Internet Traffic Through GTP and GRX

Most subscribers believe that working through a cellular network is quite safe, because a large telecom operator must have taken care of protection. Alas, in practice, there are many loopholes in the mobile Internet that provide great opportunities for attackers.
Positive Technologies researchers found vulnerabilities in the infrastructure of mobile communication networks that allow you to intercept GPRS traffic in the clear, replace data, block access to the Internet, and determine the location of the subscriber. Not only mobile phones, but also specialized devices connected to 2G / 3G / 4G networks via modems are at risk: ATMs and payment terminals, remote control systems for transport and industrial equipment, telemetry and monitoring tools, etc.
Mobile operators, as a rule, encrypt GPRS traffic between the mobile terminal (smartphone, modem) and the customer service node (SGSN) with GEA-1/2/3 algorithms, which complicates the interception and decryption of information. To circumvent this limitation, an attacker can penetrate the operator’s core network, where the data is not protected by authentication mechanisms. The Achilles heel are routing nodes (or gateway nodes) called GGSNs. They are easy to detect, in particular, with the help of the Shodan search engine. GTP ports are open on problem nodes, which allows an attacker to establish a connection and then encapsulate GTP control packets in the created tunnel. With the right choice of parameters, GGSN will perceive them as packets from legitimate devices of the operator’s network.
The GTP protocol described above should in no way be “visible” from the Internet. But in practice, this is not so: on the Internet there are more than 207 thousand devices around the globe with open GTP ports. More than five hundred of them are components of a cellular network and respond to a connection request.

Another possibility for attacks is related to the fact that GTP is far from the only control protocol on the found nodes. There are also Telnet, FTP, SSH, Web, etc. Using vulnerabilities in these interfaces (for example, standard passwords), an intruder can connect to the site of a mobile operator.
An experimental search on the Shodan site yields several vulnerable devices, including those with open Telnet and a disabled password. It is enough to connect to this device and make the necessary settings in it in order to be inside the operator’s network in the Central African Republic. At the same time, anyone who has gained access to the gateway node of any operator automatically gets access to the GRX network, which unites all mobile operators and is used to provide Internet access to subscribers in roaming. Using a single configuration error on one device, an attacker gets the opportunity to carry out various attacks on subscribers of any operator in the world.

Among the many options for using a compromised border node, the following should be noted: disconnecting subscribers from the Internet or blocking their access to it; Internet connection in the guise of another subscriber and at someone else’s expense; Interception of victim traffic and phishing. An attacker can also determine the subscriber identifier (IMSI) and track the location of the subscriber around the world until he changes his SIM card.
We describe some of the threats in more detail.
Internet at the expense of others
Purpose: exhaustion of the subscriber's account, use of the connection for illegal purposes.
Attack vector: the attacker acts through the GRX network or from the operator’s network.
The attack consists in sending “Create PDP context request” packets from the IMSI of a previously known subscriber, thus connecting to the network with its credentials. An unsuspecting subscriber will receive huge bills.
It is possible to connect a non-existent subscriber with IMSI, since subscriber authorization occurs at the stage of connecting to SGSN, and already “verified” connections reach GGSN. Since the SGSN is compromised in this case, no verification was carried out.
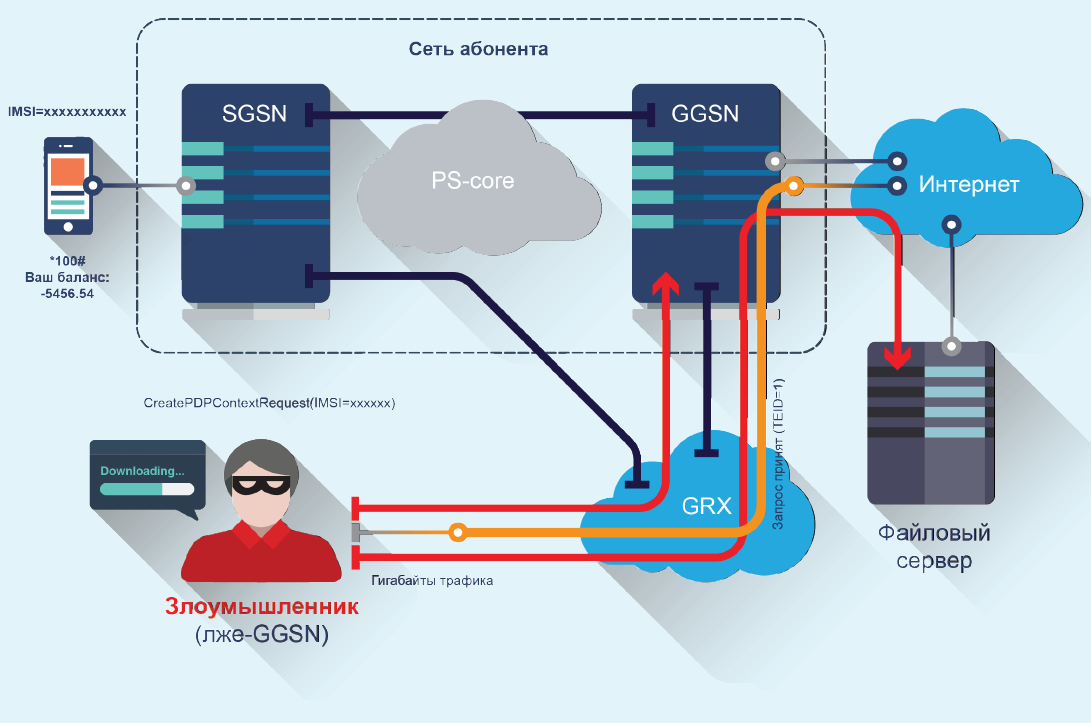
Result: Internet connection under the guise of a legitimate subscriber.
Data interception
Purpose: eavesdropping on victim traffic, phishing.
Attack vector: the attacker acts through the GRX network or from the operator’s network.
An attacker can intercept data transmitted between a subscriber device and the Internet by sending an “Update PDP Context Request” message with spoofed GSN addresses to the serving SGSN and GGSN. This attack is an analogue of the ARP Spoofing attack at the GTP protocol level.

Result: eavesdropping or substitution of the victim’s traffic, disclosure of confidential information.
DNS tunneling
Purpose: to get non-tariffed access to the Internet from the subscriber’s mobile station.
Attack vector: an attacker - a subscriber to a cellular network, acts through a mobile phone.
The long-known attack, rooted in the days of dial-up, lost its meaning when the cheap and fast dedicated Internet appeared. However, it is used in mobile networks, for example, in roaming, when the prices for mobile Internet are unreasonably high, and the data transfer speed is not so important (for example, for checking mail).
The essence of the attack is that some operators do not charge DNS-traffic, usually in order to redirect the subscriber to the operator’s page to replenish the account. This can be used - by sending specialized queries to the DNS server; also for this you need a specialized site on the Internet through which access will be carried out.

Result: obtaining non-tariffed access to the Internet at the expense of the mobile operator.
Replacing DNS with GGSN
Purpose: eavesdropping on victim traffic, phishing.
Attack vector: an attacker acts through the Internet.
In the case of gaining access to the GGSN (which, as we have already noted, it is quite possible), you can change the DNS address to your own, redirect all subscriber traffic through your site and thus "eavesdrop" on all mobile traffic.

Result: eavesdropping or spoofing the traffic of all subscribers, collecting confidential data, phishing
How to protect yourself
Some of these attacks would not have been possible with proper hardware setup. But the results of Positive Technologies research suggest that incorrect setup is by no means a rarity in the world of telecommunications companies. Often, device manufacturers also leave some services enabled, which should be disabled on this equipment, which gives attackers additional opportunities. Due to the large number of nodes, such control is recommended to be automated using specialized tools such as MaxPatrol.

In general, the security measures necessary to protect against such attacks include the proper configuration of equipment, the use of firewalls at the borders of the GRX network and the Internet, the use of 3GPP TS 33.210 recommendations for setting up security within the PS-Core network, monitoring perimeter security, and developing secure configuration standards equipment and periodic monitoring of compliance with these standards.
A number of experts pin their hopes on new communication standards, which include new security technologies. However, despite the emergence of such standards (3G, 4G), it will not be possible to completely abandon the networks of the old generation (2G). The reason for this is the implementation features of mobile networks, in particular, the fact that 2G base stations have better coverage, as well as the fact that 3G networks are also working on their infrastructure. The LTE standard still uses the GTP protocol, and therefore the necessary protection measures will be relevant in the foreseeable future.
The results of this study were obtained by Positive Technologies experts in 2013 and 2014 in the course of consulting work on the security analysis of several large mobile operators. Full report of Mobile Internet Vulnerabilities (GPRS)can be downloaded from our website: www.ptsecurity.ru/download/GPRS%20security.pdf
PS On February 19 at 2 p.m. one of the authors of the study, Pavel Novikov, will be able to tell more about these problems in the course of a free webinar. Registration for the webinar will begin on February 12 at: www.ptsecurity.ru/lab/webinars/#40018 .
