Access Certification: Reduce Risks with Armed Data
Internal policies and company rules require managers to constantly monitor the relevance of employee access levels. For healthcare organizations, government departments, financial institutions, any joint-stock companies and enterprises that accept credit cards for payment, this is a task of key importance. Incorrect organization of the process of certification of access rights can be very expensive for the company. The consequences can be different: from "just" a deterioration in the image to a fall in stocks, fines, or even civil and criminal lawsuits. Let's look at the difficulties associated with access certification and how to solve them.
Certification
In most organizations, access certification is boring mechanical work. To determine whether an employee still works in the company and if he needs the access rights that he has, IT managers have to look through long lists in spreadsheets. Most often, they have no idea what information is available to each specific employee, and can only make assumptions: since the person is still working in the company, then access can be confirmed. The situation is aggravated by the presence in such check-box lists of “mark everything”, which saves managers time: just select this option and it's done.
But is blind certification a threat when managers give out access rights without knowing their relevance? Well, really, what bad can happen? In reality, this approach is fraught with serious trouble. Here's an example: in October 2010, former Societe Generale trader Jerome Kerviel was sentenced to three years in prison and paid 4.9 billion euros. As it turned out, Cervier made risky stock exchange operations without management control and used passwords that he retained from his previous positions in the company.
Something similar can happen in any organization if managers blindly leave access rights for employees on the grounds that they are still working in the company. How, for example, to be with an employee who was recently transferred from another department? Leave him access to the files that were necessary for his previous work, or is it still not worth doing this?
Source of the Problem
Often, certification problems have three reasons:
Lack of information
Too often, managers whose job it is to review access rights does not have a complete picture of what actually needs to be reviewed. They can make sure that all employees still work in their departments or in the company as a whole, but usually they do not have details about the access level of each individual person. Accordingly, there is no way to reliably find out whether the employee needs to retain the access rights it has. Instead, you have to blindly leave everything as it is.
Some organizations delegate certification to application developers, but they usually also do not have information about the current role of employees and the relevance of access levels. For example, if a developer several years ago granted access to an employee in response to a request by e-mail, now he can only find the name of this employee in the list of the company's personnel department and make sure that the person is still working in this organization. Most likely, he does not have data on the current duties of this employee, nor does he have information on whether the same level of access is needed to perform these duties. What if a person was recently promoted or transferred to another department?
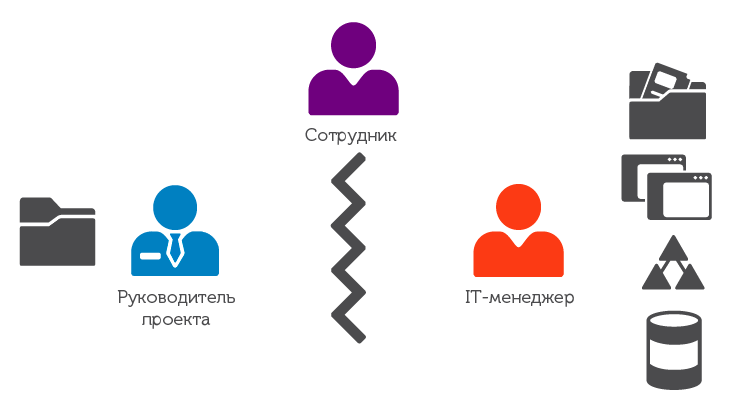
Fig. 1. Usually, the project manager sees that an employee is part of his team and performs certain duties, but does not know which access rights he has. On the other hand, the IT manager sees which systems and applications are available to the employee, but he does not know either the duties of the employee or the need to access certain applications.
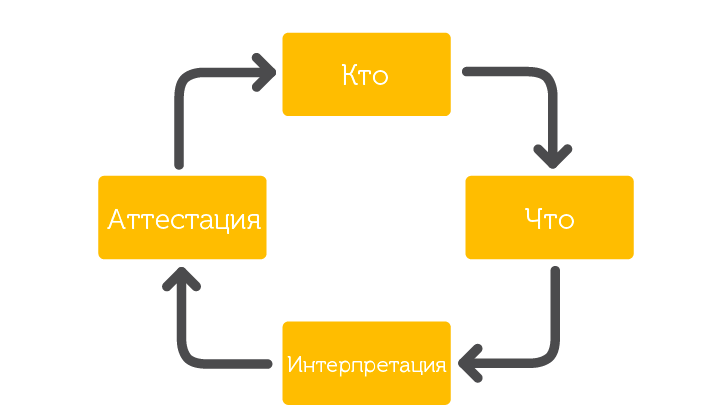
Fig. 2. Parts of the solution to the problem of access certification.
It does not matter who is involved in access certification, the project manager or application developer, in such situations, problems arise precisely due to lack of information.
Misunderstanding
In other organizations, managers are provided with lists of all access rights of each specific employee (it is likely generated by a self-made program). But these lists are not always easy to understand. Here is an example: the project manager sees that Vasily Pupkin has access to \\ DC7 \ C $ \, but will he understand what this means? Most likely, he will not know which server or shared folder we are talking about, whether Vasily has access to all the data on this server, and so on. Agree, the situation is ambiguous.

Fig. 3. The manager control panel displays the number of employees and their responsibilities. Charts in the form of traffic lights report the presence of unsolved problems or problems encountered.
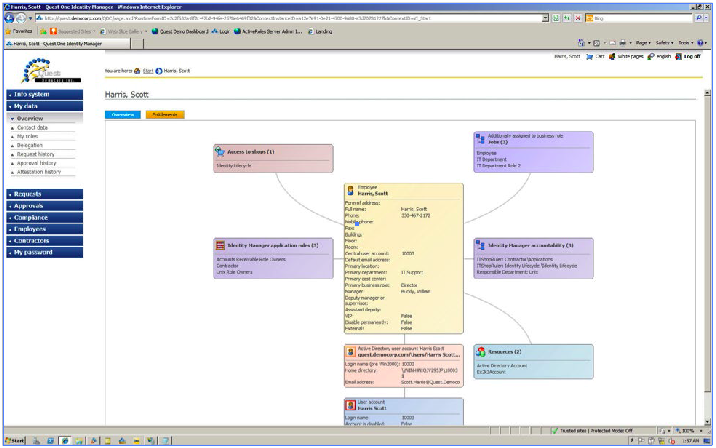
Fig. 4. The Entitlements tab displays all the network elements that the employee has access to.
From the side of the IT manager, there is also a misunderstanding, but exactly the opposite. It’s just quite clear to him what \\ DC7 \ C $ \ is, but he does not know what Vasily Pupkin is specifically doing, and whether he really needs access to \\ DC7 \ C $ \.
Lack of a clearly established certification process
In many organizations, the challenges of access certification are shifting to automated systems. It is believed that if there is a well-established algorithm that automatically issues access rights and revokes them when the employee is fired, the need for regular certification disappears. But in practice this does not work. Users are constantly provided with access to new programs and applications, and at the same time, it is not always canceled on time. A classic example is the transfer of an employee within the company, as is the case with the Societe Generale trader. Often, after changing the position or duties, the employee has the old access simply because no one took care to close it. A person is still working in a company, what is the problem?
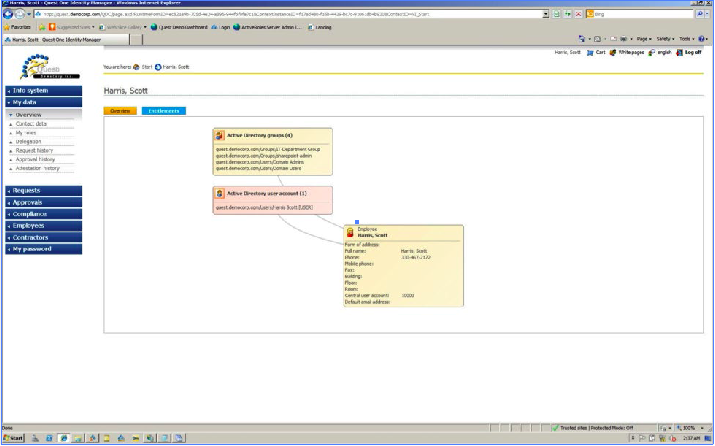
Fig. 5. Details about access for employee Scott Harris: he is a member of the IT group, is a SharePoint administrator, administrator and domain user.
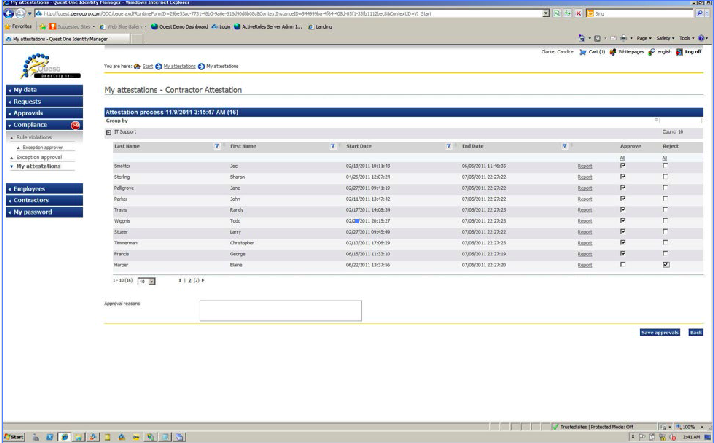
Fig. 6a. This example shows how manager Candice Clark excludes Elaine Harper from the contractor team.
There is a lack of clear interaction between IT managers who see what access rights each individual employee has and project managers who understand the current responsibilities of their employees.
The Best Approach to Access Certification
Issues Each problem will have a solution if it is broken into small parts, and access certification is no exception. The process can be divided into the following components:
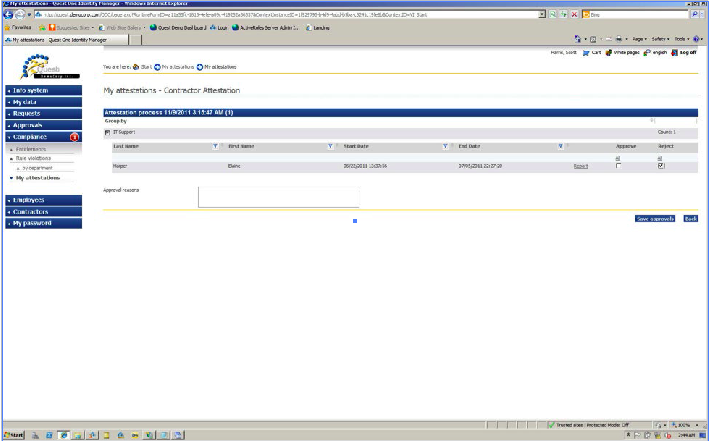
Fig. 6b. As soon as Candice Clark removed Elaine Harper from the list of employees, administrator Scott Harris receives a notification with the option to confirm. As soon as Scott confirms the exception, Elaine’s immediate revocation process begins.

Fig. 7. You can set a schedule for regular certification of employee access rights.
Who: determine the number of employees
First of all, you need to make sure your list of employees is up to date. You need to rely on the list made up by the personnel department, because if a person no longer works in the company, they definitely know about it. Also, personnel officers should clarify the structure of departments in order to attract project managers to the certification process. You can’t do without their participation, because it is they who know the responsibilities of their employees and the level of access that they need.
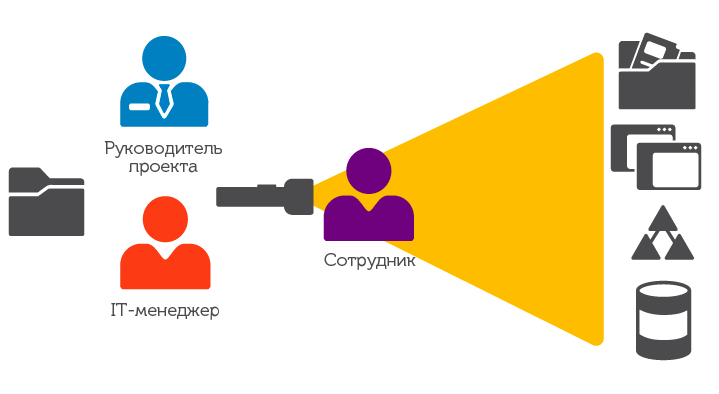
Fig. 8. Using suitable tools, both project managers and IT managers can clearly see which network resources each employee has access to. This will allow them to make informed decisions about access certification.
What: determine what access is required to
The next step will be to identify all potential levels of tolerance and a detailed review, which of them are already available for each individual employee. For many, this item may turn out to be the most time-consuming, since you will have to get the list of users from the administrators responsible for each application, the “shared” folder, etc. If you already have a similar list sorted by department or job title, this should also be taken into account.
Interpretation: “translate” the names of all network elements into an understandable language
To prevent blind grading, this step is critical. As already mentioned, the project manager can see that the employee has access to the server, but do not understand the code by which he is designated. The project manager must clearly understand what exactly he provides access to, and not "blindly" assume that everything is in order.
Certification: Determine if the user needs access.
All the previous steps have created the basis for the correct certification of access. A clear vision of who is granted access, what current rights the employee has, as well as the understandable names of each permit (and not just the code in the table) help determine whether the requested access level is required to fulfill the current duties of the employee.
Conclusion
Access certification in many organizations creates difficulties due to lack of information, misunderstanding and lack of a well-established process. Project managers understand the responsibilities of their team, but not their access rights, but IT managers, on the contrary, see the access rights of employees, but do not know their current responsibilities. In addition, it is simply impossible to replace the interaction between IT and project managers with an automated process. Because blind certification typically exposes an organization to serious risks, a new look at the difficulties associated with access certification is needed.
Dell One Identity provides a clear, comprehensive view of employees and their level of access in an easy-to-understand format. A clear organization of the process and appropriate certification tools allow companies to save time and provide better protection for the network and its compliance with the needs of the organization.
Detailed information about the Dell One Identity can be found here .
Certification
In most organizations, access certification is boring mechanical work. To determine whether an employee still works in the company and if he needs the access rights that he has, IT managers have to look through long lists in spreadsheets. Most often, they have no idea what information is available to each specific employee, and can only make assumptions: since the person is still working in the company, then access can be confirmed. The situation is aggravated by the presence in such check-box lists of “mark everything”, which saves managers time: just select this option and it's done.
But is blind certification a threat when managers give out access rights without knowing their relevance? Well, really, what bad can happen? In reality, this approach is fraught with serious trouble. Here's an example: in October 2010, former Societe Generale trader Jerome Kerviel was sentenced to three years in prison and paid 4.9 billion euros. As it turned out, Cervier made risky stock exchange operations without management control and used passwords that he retained from his previous positions in the company.
Something similar can happen in any organization if managers blindly leave access rights for employees on the grounds that they are still working in the company. How, for example, to be with an employee who was recently transferred from another department? Leave him access to the files that were necessary for his previous work, or is it still not worth doing this?
Source of the Problem
Often, certification problems have three reasons:
- Lack of information.
- Misunderstanding of the information that you have to deal with.
- Lack of a clearly defined access certification process.
Lack of information
Too often, managers whose job it is to review access rights does not have a complete picture of what actually needs to be reviewed. They can make sure that all employees still work in their departments or in the company as a whole, but usually they do not have details about the access level of each individual person. Accordingly, there is no way to reliably find out whether the employee needs to retain the access rights it has. Instead, you have to blindly leave everything as it is.
Some organizations delegate certification to application developers, but they usually also do not have information about the current role of employees and the relevance of access levels. For example, if a developer several years ago granted access to an employee in response to a request by e-mail, now he can only find the name of this employee in the list of the company's personnel department and make sure that the person is still working in this organization. Most likely, he does not have data on the current duties of this employee, nor does he have information on whether the same level of access is needed to perform these duties. What if a person was recently promoted or transferred to another department?
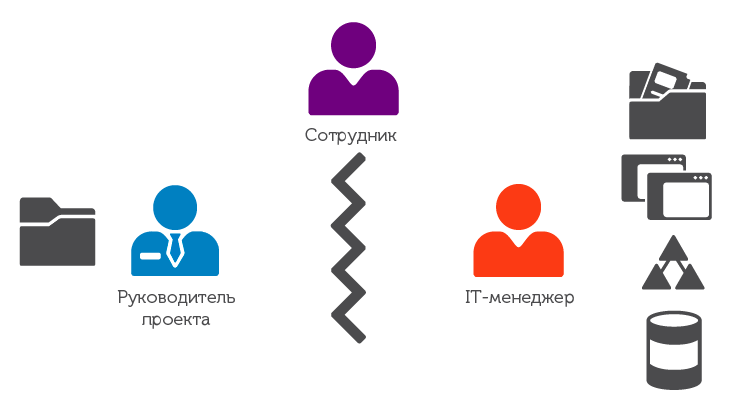
Fig. 1. Usually, the project manager sees that an employee is part of his team and performs certain duties, but does not know which access rights he has. On the other hand, the IT manager sees which systems and applications are available to the employee, but he does not know either the duties of the employee or the need to access certain applications.
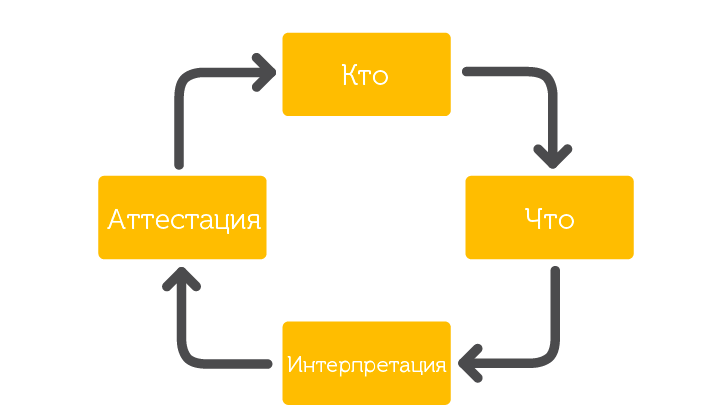
Fig. 2. Parts of the solution to the problem of access certification.
It does not matter who is involved in access certification, the project manager or application developer, in such situations, problems arise precisely due to lack of information.
Misunderstanding
In other organizations, managers are provided with lists of all access rights of each specific employee (it is likely generated by a self-made program). But these lists are not always easy to understand. Here is an example: the project manager sees that Vasily Pupkin has access to \\ DC7 \ C $ \, but will he understand what this means? Most likely, he will not know which server or shared folder we are talking about, whether Vasily has access to all the data on this server, and so on. Agree, the situation is ambiguous.

Fig. 3. The manager control panel displays the number of employees and their responsibilities. Charts in the form of traffic lights report the presence of unsolved problems or problems encountered.
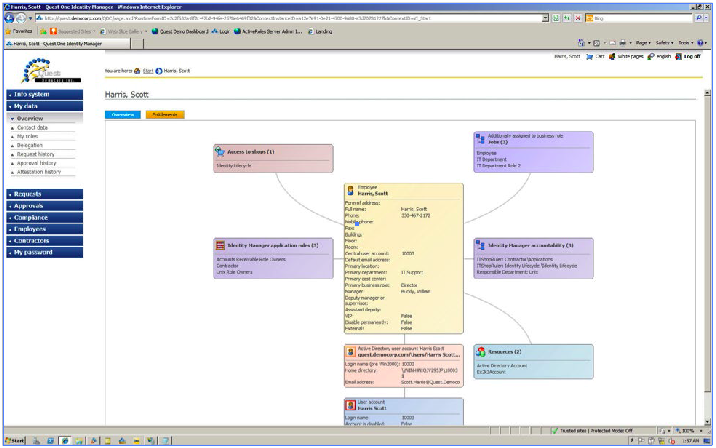
Fig. 4. The Entitlements tab displays all the network elements that the employee has access to.
From the side of the IT manager, there is also a misunderstanding, but exactly the opposite. It’s just quite clear to him what \\ DC7 \ C $ \ is, but he does not know what Vasily Pupkin is specifically doing, and whether he really needs access to \\ DC7 \ C $ \.
Lack of a clearly established certification process
In many organizations, the challenges of access certification are shifting to automated systems. It is believed that if there is a well-established algorithm that automatically issues access rights and revokes them when the employee is fired, the need for regular certification disappears. But in practice this does not work. Users are constantly provided with access to new programs and applications, and at the same time, it is not always canceled on time. A classic example is the transfer of an employee within the company, as is the case with the Societe Generale trader. Often, after changing the position or duties, the employee has the old access simply because no one took care to close it. A person is still working in a company, what is the problem?
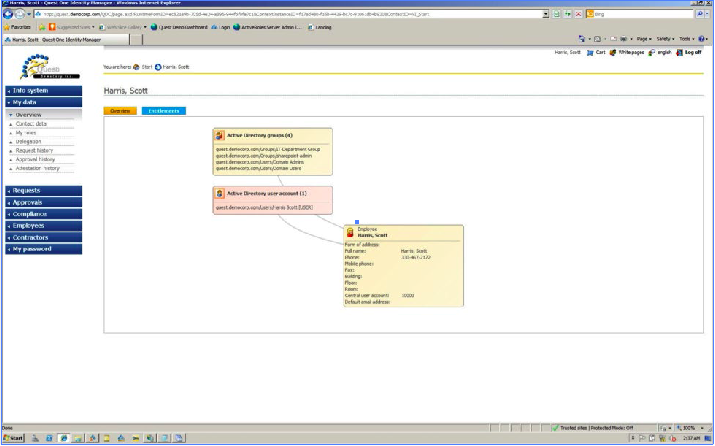
Fig. 5. Details about access for employee Scott Harris: he is a member of the IT group, is a SharePoint administrator, administrator and domain user.
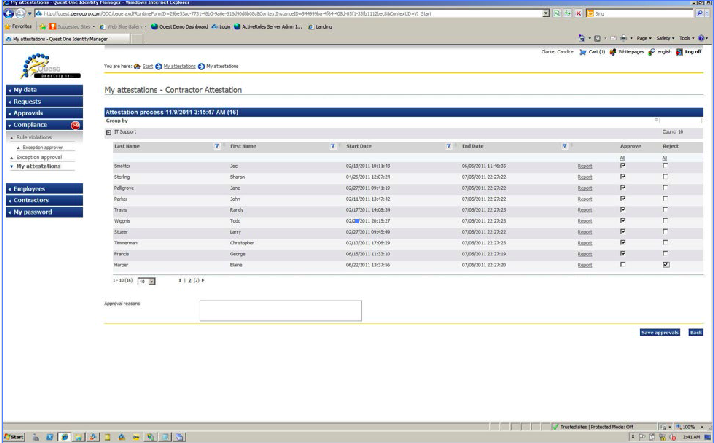
Fig. 6a. This example shows how manager Candice Clark excludes Elaine Harper from the contractor team.
There is a lack of clear interaction between IT managers who see what access rights each individual employee has and project managers who understand the current responsibilities of their employees.
The Best Approach to Access Certification
Issues Each problem will have a solution if it is broken into small parts, and access certification is no exception. The process can be divided into the following components:
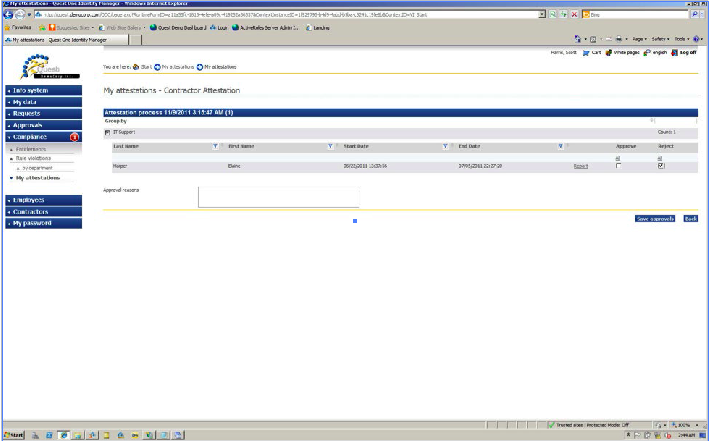
Fig. 6b. As soon as Candice Clark removed Elaine Harper from the list of employees, administrator Scott Harris receives a notification with the option to confirm. As soon as Scott confirms the exception, Elaine’s immediate revocation process begins.

Fig. 7. You can set a schedule for regular certification of employee access rights.
Who: determine the number of employees
First of all, you need to make sure your list of employees is up to date. You need to rely on the list made up by the personnel department, because if a person no longer works in the company, they definitely know about it. Also, personnel officers should clarify the structure of departments in order to attract project managers to the certification process. You can’t do without their participation, because it is they who know the responsibilities of their employees and the level of access that they need.
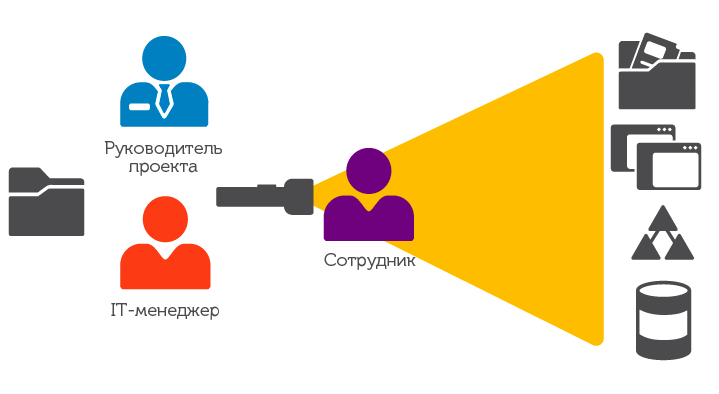
Fig. 8. Using suitable tools, both project managers and IT managers can clearly see which network resources each employee has access to. This will allow them to make informed decisions about access certification.
What: determine what access is required to
The next step will be to identify all potential levels of tolerance and a detailed review, which of them are already available for each individual employee. For many, this item may turn out to be the most time-consuming, since you will have to get the list of users from the administrators responsible for each application, the “shared” folder, etc. If you already have a similar list sorted by department or job title, this should also be taken into account.
Interpretation: “translate” the names of all network elements into an understandable language
To prevent blind grading, this step is critical. As already mentioned, the project manager can see that the employee has access to the server, but do not understand the code by which he is designated. The project manager must clearly understand what exactly he provides access to, and not "blindly" assume that everything is in order.
Certification: Determine if the user needs access.
All the previous steps have created the basis for the correct certification of access. A clear vision of who is granted access, what current rights the employee has, as well as the understandable names of each permit (and not just the code in the table) help determine whether the requested access level is required to fulfill the current duties of the employee.
Conclusion
Access certification in many organizations creates difficulties due to lack of information, misunderstanding and lack of a well-established process. Project managers understand the responsibilities of their team, but not their access rights, but IT managers, on the contrary, see the access rights of employees, but do not know their current responsibilities. In addition, it is simply impossible to replace the interaction between IT and project managers with an automated process. Because blind certification typically exposes an organization to serious risks, a new look at the difficulties associated with access certification is needed.
Dell One Identity provides a clear, comprehensive view of employees and their level of access in an easy-to-understand format. A clear organization of the process and appropriate certification tools allow companies to save time and provide better protection for the network and its compliance with the needs of the organization.
Detailed information about the Dell One Identity can be found here .
