How Mitnik trolled the FBI. Articles on Habr from a camp for school students
“Mitnik, do you know how to handle phones?” The overseer asked.A couple of days ago, the idea occurred to me to instill in schoolchildren a taste for the beautiful and to familiarize them with
“Not really,” I replied, “but I can insert the plug into a power outlet.” You don’t worry, I’m learning fast. ”
For two days I installed and repaired prison phones. K. Mitnik “Ghost on the net”
The thing is happening right now, I am sitting in a camp in the robotics class (the camp is unusual, but with
Discussing topics of information security, hacking Wi-Fi networks, 3D printers, Arduino, brute force and asymmetric encryption, it turned out that many (schoolchildren, schoolgirls, counselors and teachers) actively read Habr and use it as a reference tool for their projects.
The idea of co-writing an article came to me when, when discussing the coolest articles, the guys recently referred to an article where “one acquaintance got into the Mitnik conference” . I had to admit that this was about my friend and, in developing the topic of ethical hacking, I suggested that young people try their hand at writing interesting posts.
The only time you can find all the camp participants is lunch (Hogwarts knew a lot about when to make speeches), and I announced the recruitment of volunteers. A few guys responded. On the same day, I posted announcements on the bulletin board to maintain interest.
Objectives:
- inciting interest in Habr, information security, social engineering;
- show how what used to be considered unreal becomes real (the nearest growth zone);
- inspire young authors to write articles on Habré;
- inspire / involve Habr veterans to help novice authors (Padawan Jedi).
For a smooth start, I decided to start with translations, then do some interviews with experts in the field (counselors / teachers), and then (already outside the camp) help the authors create independent content.
Work plan: the
first stage - co-writing an article on Habr, translating an article from Time and Mitnik ’s video “How to Troll the FBI” , as well as adding interesting points to the post from a book about the relationship between Mitnik and the FBI;
second stage- each describes one event for the second part of the article “History of hacking hacking information systems” (the first part is the History of hacking hacking information systems (1903-1971) ) the
third stage is the independent writing of your article under my supervision (sample topics: " Google Code Jam . Interview with the finalist - Roman Udovichenko (10th place) "," The Future of Robotics. Interviews with TRIC experts, "Forge of Belarusian Programmers, etc.)
UPD 08/28/2014 the first " Sauron " appeared.
The results of the first stage under the cut.
Cat ad
1. How to troll the FBI
Original text
Transcript - When the government was chasing me I wanted to get a sense of how close they were and to me this was a game. It was kind of like I was a little bit insane and I treated my fugitive status as a big video game. Unfortunately, it had real consequences and why I did this psychologically is I loved putting myself in dangerous situations and then trying to work my way out of them. I don't know why I liked doing this, but I did. So what I did is I hacked into the cellular provider in Los Angeles that serviced the FBI cell phone numbers of the agents that were chasing me, so to make a long story short I was able to get the cell phone numbers of the agents and then by hacking into the cellular provider I could monitor where they physically were, physically in Los Angeles. I could also monitor who they were calling and who was calling them.
So based on my traffic analysis and my location data I was able to find out if the feds ever got close and one time they did. I had an early warning system set up in 1992 when I was working as a private investigator in Los Angeles and when the warning system was tripped off I found out that the FBI was actually at my apartment and I was a mile away in Calabasas, but I just drove in from the apartment to work, so obviously they weren't there to arrest me and I didn't think if they were still near my apartment that it was to surveil me, so the only logical thing is that they were there to conduct a search and that means to get a search warrant. They didn't have a search warrant yet.
So in every criminal case when they have to get a search warrant from a judge they have to write down the precise description of the premises to be searched. It's the Fourth Amendment stuff and so I figured out that that was going on and so the very next day I cleaned up — well that evening I cleaned up everything from my apartment that the FBI may be interested in and then the very next day went out to Winchell's Donuts and got a big dozen assorted donuts and I labeled the box "FBI donuts" and I put it in the refrigerator. So when they were going to come search the only thing they would find is I had some donuts for them.
They searched the next day. They didn't 'find anything. I don't even know if they opened the refrigerator, but if they did they didn't help themselves to a donut for some reason.
So based on my traffic analysis and my location data I was able to find out if the feds ever got close and one time they did. I had an early warning system set up in 1992 when I was working as a private investigator in Los Angeles and when the warning system was tripped off I found out that the FBI was actually at my apartment and I was a mile away in Calabasas, but I just drove in from the apartment to work, so obviously they weren't there to arrest me and I didn't think if they were still near my apartment that it was to surveil me, so the only logical thing is that they were there to conduct a search and that means to get a search warrant. They didn't have a search warrant yet.
So in every criminal case when they have to get a search warrant from a judge they have to write down the precise description of the premises to be searched. It's the Fourth Amendment stuff and so I figured out that that was going on and so the very next day I cleaned up — well that evening I cleaned up everything from my apartment that the FBI may be interested in and then the very next day went out to Winchell's Donuts and got a big dozen assorted donuts and I labeled the box "FBI donuts" and I put it in the refrigerator. So when they were going to come search the only thing they would find is I had some donuts for them.
They searched the next day. They didn't 'find anything. I don't even know if they opened the refrigerator, but if they did they didn't help themselves to a donut for some reason.
When the government was persecuting me, I wanted to understand how close the FBI got to me and for me it was a kind of game. Unfortunately, the consequences were real, but I liked to find myself in difficult situations, and then find a way out of them. I don’t know why I liked to do it, but I continued to do it. I hacked into a Los Angeles-based mobile phone service provider serving the mobile phones of FBI agents chasing me. In short, I could track the location of the feds and control all incoming and outgoing calls on their phones.
Another paragraph translation option
When the government was stalking me, I wanted to know how close the FBI got to me and for me it was a game. It looked like I was a little crazy and rated my fugitive status as a great video game. Unfortunately, the consequences were real, but, psychologically, I liked to find myself in dangerous situations and then get out of them. I don’t know why I liked it, but I could not stop. So I hacked into a Los Angeles-based mobile phone service provider serving the FBI agents who were chasing me, and I was able to track the location of the feds within Los Angeles and control all incoming and outgoing calls on their phones.
Based on the location data I had and the analysis of (telephone) traffic, I tracked the movements of the feds. If they came close to me, I could find out. From the time when I happened to be in the role of a private detective, I had an early warning system installed, and on the way to work I received a signal from her that the FBI agents were in my apartment. It was obvious that they did not come to arrest me. The only logical explanation is to conduct a search for which they have not yet had a warrant.
During the official search, agents would be obliged to make an inventory of the premises, so I cleared my apartment in advance of everything that might interest them, then on a large box of sweets from Winchell's Donuts (Winchell Donuts) I wrote Donuts for the FBI and put in the fridge. So they could only find out that I have delicious donuts for them.
They searched my apartment the next day, but found nothing. I don’t know if they looked into the refrigerator at all, but they didn’t touch the donuts. I do not know why.
2. Ten Questions for Kevin Mitnick (New York Times)
Original
10 Questions for Kevin Mitnick
Could you hack into the New York Times best-seller list and change the ranking of your new book, Ghost in the Wires?
Probably. These days companies hire me to break into their systems to find their security vulnerabilities. I don't know if I could compromise the New York Times network, but I think it's likely. Of course, I would only do it with authorization.
Your first crime involved fake bus transfers. Do you think if somebody had cracked down on you earlier, your life might have gone a different way?
I think it goes back to my high school days. In computer class, the first assignment was to write a program to print the first 100 Fibonacci numbers. Instead, I wrote a program that would steal passwords of students. My teacher gave me an A.
What made you a good hacker was less the coding skills and more the social-engineering skills. What were they?
Social engineering is using deception, manipulation and influence to convince a human who has access to a computer system to do something, like click on an attachment in an e-mail. Most of the computer compromises that we hear about use a technique called spear phishing, which allows an attacker access to a key person's workstation. It's extremely difficult to defend against.
Has social networking changed hacking?
Made it easier. I can go into LinkedIn and search for network engineers and come up with a list of great spear-phishing targets because they usually have administrator rights over the network. Then I go onto Twitter or Facebook and trick them into doing something, and I have privileged access. If I know you love Angry Birds, maybe I would send you an e-mail purporting to be from Angry Birds with a new pro version. Once you download it, I could have complete access to everything on your phone.
How easy was it for those tabloid reporters to hack into celebrities' phones?
This kind of boggles my mind. A lot of the cellular operators would create a default PIN for people's voice mail as 1111 or 1234. It doesn't take a hacker to guess a PIN like that.
What is the perfect PIN then?
The perfect PIN is not four digits and not associated with your life, like an old telephone number. It's something easy for you to remember and hard for other people to guess.
What do you think of people like Julian Assange and the WikiLeaks crowd?
It's more Bradley Manning who was responsible for all of that. Here's an enlisted guy who's able to dump secret documents from SIPRNet to CDs. It is a huge security failure on the part of the US government - the worst that I know of.
Which of your hacks are you most proud of?
I think when I hacked into Pac Bell Cellular to do traffic analysis on the FBI agents who were tasked with capturing me - not for hacking into Pac Bell but for how I leveraged that information to stay one step ahead of the government.
You used Money's rankings of the 10 most livable cities to find places to hide. Should the FBI monitor that list?
No, it was just allowing Money to randomize my choice. If I had my own choice, somebody might have figured it out.
You served five years. How do hackers get treated in prison?
Could you hack into the New York Times best-seller list and change the ranking of your new book, Ghost in the Wires?
Probably. These days companies hire me to break into their systems to find their security vulnerabilities. I don't know if I could compromise the New York Times network, but I think it's likely. Of course, I would only do it with authorization.
Your first crime involved fake bus transfers. Do you think if somebody had cracked down on you earlier, your life might have gone a different way?
I think it goes back to my high school days. In computer class, the first assignment was to write a program to print the first 100 Fibonacci numbers. Instead, I wrote a program that would steal passwords of students. My teacher gave me an A.
What made you a good hacker was less the coding skills and more the social-engineering skills. What were they?
Social engineering is using deception, manipulation and influence to convince a human who has access to a computer system to do something, like click on an attachment in an e-mail. Most of the computer compromises that we hear about use a technique called spear phishing, which allows an attacker access to a key person's workstation. It's extremely difficult to defend against.
Has social networking changed hacking?
Made it easier. I can go into LinkedIn and search for network engineers and come up with a list of great spear-phishing targets because they usually have administrator rights over the network. Then I go onto Twitter or Facebook and trick them into doing something, and I have privileged access. If I know you love Angry Birds, maybe I would send you an e-mail purporting to be from Angry Birds with a new pro version. Once you download it, I could have complete access to everything on your phone.
How easy was it for those tabloid reporters to hack into celebrities' phones?
This kind of boggles my mind. A lot of the cellular operators would create a default PIN for people's voice mail as 1111 or 1234. It doesn't take a hacker to guess a PIN like that.
What is the perfect PIN then?
The perfect PIN is not four digits and not associated with your life, like an old telephone number. It's something easy for you to remember and hard for other people to guess.
What do you think of people like Julian Assange and the WikiLeaks crowd?
It's more Bradley Manning who was responsible for all of that. Here's an enlisted guy who's able to dump secret documents from SIPRNet to CDs. It is a huge security failure on the part of the US government - the worst that I know of.
Which of your hacks are you most proud of?
I think when I hacked into Pac Bell Cellular to do traffic analysis on the FBI agents who were tasked with capturing me - not for hacking into Pac Bell but for how I leveraged that information to stay one step ahead of the government.
You used Money's rankings of the 10 most livable cities to find places to hide. Should the FBI monitor that list?
No, it was just allowing Money to randomize my choice. If I had my own choice, somebody might have figured it out.
You served five years. How do hackers get treated in prison?

Could you hack the New York Times website and change the rating of your new book, Ghost on the Web?
Maybe. Large companies pay me good money for looking for vulnerabilities in their system. I don’t know if it’s possible for me to open the New York Times network, but, in principle, this does not seem impossible.
Your hacking career began with fake bus tickets. What do you think, if you were caught then, your fate would have changed a lot?
I think it all started back in school. Once, at a computer science lesson, we were given a task where it was necessary to display the first 100 Fibonacci numbers on a computer screen. Instead, I wrote a program that stole student passwords. My teacher put me a five.
What made you a good hacker? Tell us more about social engineering techniques, which ones do you use?
Social engineering is the manipulation of people, the influence on them, in order to convince them to do something. For example, click on the link in the email. Most of the computer hacks that we know about use spear fishing techniques to capture key computer computers. Protecting yourself from it is not easy.
How have social networks changed the hacking process?
They greatly simplified it. I can go to LinkedIN, look for system administrators and voila: I have a whole list of goals for phishing, because, as a rule, they have all the rights in the enterprise network. Then I go to Twitter or Facebook, I ask them to do a few manipulations and that’s all, I have full access. If you like Angry Birds, then maybe I will send you information about the new version of the game by mail. Once you download it once and I will have all access to your device.
How do yellow press reporters crack celebrity phones?
I think this is not a hack. Many mobile operators put 1111 or 1234 as the default PIN for voicemail. Agree, you do not need to be a hacker to pick up such a PIN.
What then is a “perfect” PIN?
An ideal PIN code certainly does not consist of four characters and should not be associated with your past, for example, it should not be an old phone number. This is something that only you and no one else should know.
What do you think of Julian Assange and WikiLeaks?
I think most of the responsibility lies with Bradley Manning. This is a soldier who could really declassify information from SIPRNet. There were serious leaks in the US government, this is not much that I know.
What was your most amazing hack?
I think when I monitored the Pac Bell Cellular traffic to listen to the FBI agents who were hunting me at that moment. I stood on the edge of a knife, but always kept half a step ahead of the government.
You used the Money.com rating of the most livable cities to hide. FBI monitors this list?
Not. I just used this list to randomize my selection. If I made a choice on my own, someone could figure me out.
You got 5 years. How are hackers treated in prison?
Not bad at all. The Colombian drug dealer offered me 5 million for hacking the Prison Agency network to arrange for his early release, to which I replied: “Let's discuss it.”
3. Mitnik and the FBI (based on materials from the book “Ghost on the Net”)
Mitnik annoyed the FBI so much that they soldered him 460 years in prison and a fine of 300 million dollars. What else besides donuts did Mitnik do with the FBI?
Below are some life hacks and examples of using social engineering from Kevin Mitnik.
In the process of his own investigation of who his "new friend" Eric Heinz is, Mitnick stumbled upon Mike Martinez's profile. How to find out who this person is?
Traffic analysis
Intelligence officers themselves merge all personal data about themselvesThe process begins with the fact that you study the detailed call records (CDR) of the person whose phone number you have identified, and learn from these records the necessary information. Who does he call often? Who is calling him? Does it happen that he calls a certain person several times in a row at short intervals or, on the contrary, receives a series of such calls? Are there any people he calls mostly in the morning? In the evenings? Are there any numbers for which calls are particularly long? Especially short? Etc.
Then you conduct a similar analysis of the people whom this person calls most often.
Next, you ask the question: who are these people calling?
You are already starting to imagine the situation. The amount of work was monstrous, this process was to take a significant part of free time, several hours a day. I needed to find out. There was no workaround: this is a matter of paramount importance, regardless of the degree of risk.
Then you conduct a similar analysis of the people whom this person calls most often.
Next, you ask the question: who are these people calling?
You are already starting to imagine the situation. The amount of work was monstrous, this process was to take a significant part of free time, several hours a day. I needed to find out. There was no workaround: this is a matter of paramount importance, regardless of the degree of risk.
Receiving all data from the calling civil servants
Kevin Mitnik built an early warning system that would sound an alarm if the feds appeared around.I gained control of all DMV (vehicle registration service) phone numbers in Sacramento.
From my computer, I checked whether the freshly obtained number was used for calls from law enforcement agencies, and found that there were 20 lines in the search group for this number, that is, when the number given to the cops was busy, the call was automatically forwarded to the next available number from 20 The switch was just looking for an idle line.
I decided to select the 18th number for myself from the list, since from the number closer to the end of the table I will receive calls only when the line is heavily loaded, otherwise I will probably be constantly bothered by calls. I entered commands for the switch to add call forwarding, and then forward the calls that come to this line so that they are redirected to my disguised cell phone instead.
I think in those days I allowed myself exceptional arrogance. I got calls from the Secret Service, the Bureau of Land Management, the Drug Enforcement Administration, and the Bureau of Alcohol, Tobacco, and Firearms.
How is it for you: I even received calls from FBI agents - guys who had the right to handcuff me and put me back in jail.
Each time one of these guys called, believing that he was talking with a DMV employee, I requested all the necessary login information: name, organization, requesting code, driver’s license number, date of birth, etc. I don’t risked, since none of them would ever have guessed that the guy on the other end of the wire was not really working in the DMV.
From my computer, I checked whether the freshly obtained number was used for calls from law enforcement agencies, and found that there were 20 lines in the search group for this number, that is, when the number given to the cops was busy, the call was automatically forwarded to the next available number from 20 The switch was just looking for an idle line.
I decided to select the 18th number for myself from the list, since from the number closer to the end of the table I will receive calls only when the line is heavily loaded, otherwise I will probably be constantly bothered by calls. I entered commands for the switch to add call forwarding, and then forward the calls that come to this line so that they are redirected to my disguised cell phone instead.
I think in those days I allowed myself exceptional arrogance. I got calls from the Secret Service, the Bureau of Land Management, the Drug Enforcement Administration, and the Bureau of Alcohol, Tobacco, and Firearms.
How is it for you: I even received calls from FBI agents - guys who had the right to handcuff me and put me back in jail.
Each time one of these guys called, believing that he was talking with a DMV employee, I requested all the necessary login information: name, organization, requesting code, driver’s license number, date of birth, etc. I don’t risked, since none of them would ever have guessed that the guy on the other end of the wire was not really working in the DMV.
Early warning system
From time to time, Mitnik listened to the conversations of the security manager of the telephone company, and one day he heard the mention of his nameI bought a radio frequency scanner at the RadioShack store. Through it, you could listen to the cellular range (the US Federal Communications Commission has already begun to put pressure on the manufacturers of radio devices and demand to exclude the possibility of interception of cellular communications). I also bought a device called DDI, which meant "digital data interpreter." It was such a box that could decode information signals that were transmitted over a cellular network. The signals from the listening device were sent to a DDI connected to my computer.
The mobile phone is identified by the nearest cell tower and establishes communication with it. Therefore, when they call you, the system knows which cell tower has forwarded the call to the telephone you are talking on. Without such a mechanism, the mobile operator simply could not have directed the call coming to you. I programmed my radio frequency scanner to the frequency of the cell tower closest to Telec, and could thus receive information from it. So I found out which cell phone was connected to this tower, even when the subscriber simply passed in the coverage area of this tower.
My scanner constantly sent a data stream to DDI, and the interpreter converted them into separate information fragments of the following kind:
618-1000 (213) Registration
610-2902 (714) Paging call
400-8172 (818)
Paging 701-1223 (310) Registration
Each such line shows the status of a cell phone located in the coverage area of the listening tower. The first group of numbers in a line is the mobile phone number. Paging means that the tower has received a call for a specific cell phone and signals that a connection needs to be established. Registration indicates that a particular phone is in the coverage area of the tower, that it is ready to make or receive calls.
I configured the DDI software package on the work computer so that it will give an alarm if the DDI detects any of the programmed numbers. I filled in the program with the phone numbers of all those FBI agents who, according to my information, had contacted Eric by telephone. The program constantly checked the phone numbers, which, like in a chain, went to the tower - to the scanner - to the interpreter - to the computer. If the FBI agents' cell phones started working in the Teltec area, my device would warn me.
I set up a trap for the FBI and one step ahead of them. If they came for me, I would know about this in advance.
The mobile phone is identified by the nearest cell tower and establishes communication with it. Therefore, when they call you, the system knows which cell tower has forwarded the call to the telephone you are talking on. Without such a mechanism, the mobile operator simply could not have directed the call coming to you. I programmed my radio frequency scanner to the frequency of the cell tower closest to Telec, and could thus receive information from it. So I found out which cell phone was connected to this tower, even when the subscriber simply passed in the coverage area of this tower.
My scanner constantly sent a data stream to DDI, and the interpreter converted them into separate information fragments of the following kind:
618-1000 (213) Registration
610-2902 (714) Paging call
400-8172 (818)
Paging 701-1223 (310) Registration
Each such line shows the status of a cell phone located in the coverage area of the listening tower. The first group of numbers in a line is the mobile phone number. Paging means that the tower has received a call for a specific cell phone and signals that a connection needs to be established. Registration indicates that a particular phone is in the coverage area of the tower, that it is ready to make or receive calls.
I configured the DDI software package on the work computer so that it will give an alarm if the DDI detects any of the programmed numbers. I filled in the program with the phone numbers of all those FBI agents who, according to my information, had contacted Eric by telephone. The program constantly checked the phone numbers, which, like in a chain, went to the tower - to the scanner - to the interpreter - to the computer. If the FBI agents' cell phones started working in the Teltec area, my device would warn me.
I set up a trap for the FBI and one step ahead of them. If they came for me, I would know about this in advance.
Overheard conversation
When Kevin was asked to “expedite” the release on bail of an acquaintance, Kevin readily agreed: “No problem. Let me know when you pay. One has only to make a deposit, and I will get it out of there in 15 minutes. ”I was instantly wary when one of them said: “Mitnik”. The conversation was fascinating, informative and encouraging. It turned out that these guys had absolutely no idea how I was dealing with all their systems and traps, and this was noticeably unnerving to them.
They talked about the need for fresh ideas on how to lure me into a trap, talked about something that would give them clear evidence against me that they could present to the FBI. They wondered what I could do the next time, to somehow prepare for this and eventually take me in the act.
Someone suggested a plan to catch me, which seemed completely idiotic to me. To my death, I wanted to intervene in their conversation and say: “I don’t think it will work. This Mitnik is smart enough. “You never can say for sure, or maybe he is listening to us right now!”
Yes, I happened to do things as arrogant and reckless as this, but this time I managed to resist the temptation.
They talked about the need for fresh ideas on how to lure me into a trap, talked about something that would give them clear evidence against me that they could present to the FBI. They wondered what I could do the next time, to somehow prepare for this and eventually take me in the act.
Someone suggested a plan to catch me, which seemed completely idiotic to me. To my death, I wanted to intervene in their conversation and say: “I don’t think it will work. This Mitnik is smart enough. “You never can say for sure, or maybe he is listening to us right now!”
Yes, I happened to do things as arrogant and reckless as this, but this time I managed to resist the temptation.
Social Engineering for Parole
Mitnik and Lewis used a scanner to track the activity of the FBI negotiations in their immediate vicinity.Knowing how respectful people in uniform are for their ranks, I just called another prison in upstate Los Angeles, Wayside, and asked, “What kind of lieutenant is on duty this afternoon?” They called me his name. Then I called the Central Men's Prison, where they held Grant. I already knew the direct dial extension number in the pledge department. When the woman picked up the phone, I asked her for the extension number of the reception and release department. For a person like me, in such a situation, it came in handy that I myself had once gone through the prison system. I said that I was such and such a lieutenant (he named the name that he had learned before) on Wayside. “You have a prisoner there, for whom they should have paid a deposit. He, as an informant, helps in one case. I need him to leave immediately, ”I called her Grant.
I heard a knock of keys. “We have just received the order, but have not yet entered it.”
Then I said that I want to talk with her sergeant. When he went to the phone, I fed him the same fable and added: “Sergeant, you will not do me a favor?”
“Yes, sir,” he said. - What you need?"
“Since the security deposit has already been made, could you personally control his procedures and release them as soon as possible?”
He replied: “No problem, sir.”
After 20 minutes, Michael Grant called me and informed me that his father was free.
I heard a knock of keys. “We have just received the order, but have not yet entered it.”
Then I said that I want to talk with her sergeant. When he went to the phone, I fed him the same fable and added: “Sergeant, you will not do me a favor?”
“Yes, sir,” he said. - What you need?"
“Since the security deposit has already been made, could you personally control his procedures and release them as soon as possible?”
He replied: “No problem, sir.”
After 20 minutes, Michael Grant called me and informed me that his father was free.
RF scanner
Finding activity on the air is half the battle; how do you know the content of the negotiations? Mitnik gracefully solves this problem.Lewis and I met in the parking lot about half an hour before the appointed time. When I got into his car, he carefully listened to the scanner of the radio wave range. I could not ask what exactly he was listening to: the scanner was programmed to track all the frequencies used by the FBI, intelligence and counterintelligence, as well as bailiffs. In addition, when the feds knew that they were dealing with someone who could understand their technology, they often tricked and switched to the frequency of another agency, such as the Prison Bureau, the Drug Enforcement Administration, and even the Postal Service Inspectorate. Therefore, Lewis programmed tracking of these frequencies.
The scanner did not pick up distant signals, but only those whose source was nearby, and those that were strong enough. At that time, almost all federal law enforcement services were already quite skilled and encrypted their traffic. However, we just needed to check if they were talking somewhere nearby. If the frequencies of law enforcement began to hum more than usual, we hastily retreated from this place.
The scanner did not pick up distant signals, but only those whose source was nearby, and those that were strong enough. At that time, almost all federal law enforcement services were already quite skilled and encrypted their traffic. However, we just needed to check if they were talking somewhere nearby. If the frequencies of law enforcement began to hum more than usual, we hastily retreated from this place.
We go around the encrypted radio system
Even during the search and arrest, Mitnik didn’t stop subtly trolling the special services:I armed myself with my faithful early warning system - amateur radio, which was slightly modified and allowed me to transmit and receive signals at all frequencies that were used by various federal agencies.
I was terribly furious that all the traffic of these organizations was encrypted. Of course, I knew when one of these agents turned out to be nearby, but had absolutely no idea whether there was a conversation about me or someone else.
How can I crack the FBI code? I thought a little and came up with a plan B.
To allow agents to communicate over long distances, special transmitters were installed at elevated locations, transmitting a signal from each other. The radios of the agents transmitted a signal at one frequency, and received at another. On the repeaters, an input frequency was set to receive messages from agents, and an output frequency on which agents listened to messages. Wanting to find out if there is an agent nearby, I simply tracked the signal strength at the input frequency of the repeater.
Such a system allowed me to play a little. Hearing any noise that could mean messaging, I clicked the "Transfer" button. My device began to generate a radio signal at the same frequency, and the signal from the agent was jammed by interference.
In this case, one agent could not understand what it was trying to transfer to another. After two or three attempts, the agents got tired of this fuss with the walkie-talkie. I very vividly imagined one of them saying: “Some kind of nonsense with a walkie-talkie. Come on the usual connection. "
They switched the radio from encrypted to normal mode - and I could hear two interlocutors! Even today, it’s funny for me to recall how easy it was to bypass this encryption and not even crack any code.
I was terribly furious that all the traffic of these organizations was encrypted. Of course, I knew when one of these agents turned out to be nearby, but had absolutely no idea whether there was a conversation about me or someone else.
How can I crack the FBI code? I thought a little and came up with a plan B.
To allow agents to communicate over long distances, special transmitters were installed at elevated locations, transmitting a signal from each other. The radios of the agents transmitted a signal at one frequency, and received at another. On the repeaters, an input frequency was set to receive messages from agents, and an output frequency on which agents listened to messages. Wanting to find out if there is an agent nearby, I simply tracked the signal strength at the input frequency of the repeater.
Such a system allowed me to play a little. Hearing any noise that could mean messaging, I clicked the "Transfer" button. My device began to generate a radio signal at the same frequency, and the signal from the agent was jammed by interference.
In this case, one agent could not understand what it was trying to transfer to another. After two or three attempts, the agents got tired of this fuss with the walkie-talkie. I very vividly imagined one of them saying: “Some kind of nonsense with a walkie-talkie. Come on the usual connection. "
They switched the radio from encrypted to normal mode - and I could hear two interlocutors! Even today, it’s funny for me to recall how easy it was to bypass this encryption and not even crack any code.
Arrest
After half an hour, about half past one in the night, there was a knock on the door. Not realizing how late it was, I mechanically shouted: “Who is it?”
"FBI".
I was numb. They knocked again. I shouted: “Who are you looking for?”
“Kevin Mitnik. Are you Kevin Mitnick? ”
"Not! - I answered, trying to portray irritation. “You can check my inbox.”
Silent. I thought, maybe they really sent someone to the mailboxes or decided that there would be a sign saying “MITNIK” on the door of my apartment?
Shitty! I greatly underestimated the speed of the federals; they too quickly came to me. I was looking for a retreat. He went out onto the balcony and saw that no one was on duty behind the building. I looked around again, wondering if I could quickly tie a rope out of something. Sheets? Not. Twist them too long. In addition, they may try to shoot me when they see me crawling along the rope.
They knocked again.
I called mom home. There is no time to turn the usual scheme "mom, go to the casino." “I'm in Railay, North Carolina,” I say. “Outside the door of the FBI.” I don’t know where they can take me. ” We talked for a few minutes, trying to cheer each other up. Mom was completely out of her mind, heartbroken, inconsolable. She understood that I would go to jail again. I said how I love her and my grandmother, and in order to feel stronger, I added that we will survive this.
Without stopping talking on the phone, I rushed about in a cramped room, trying to hide everything that might arouse suspicion. Turned off the computer and unplugged the cord from the network. No time to erase everything from the hard drive. The laptop is still warm - you can see that they recently worked with it. I put one cell phone under the bed, the other in the gym bag. Mom told me to contact Aunt Chicky and consult with her.
Chicky gave me the home number of John Isurdiagi, the lawyer who worked with me since the time of the Calabasas affair.
They knocked on the door with renewed vigor and demanded to immediately open the door.
I shouted: “Yes, I sleep. What do you want?"
A voice answered: “We have a few questions for you.”
Trying to portray extreme indignation, I yelled: “Come in the morning when I get enough sleep!”
They were not going to leave. Is there any chance of convincing them that I'm not the one they are looking for?
A few minutes later I called my mother again and said: “Mom, I open the door. Hang on the phone, please. "
I opened a little. The man who tried to shout at me turned out to be black, with a graying beard and at the age of under 40.
It was deep night in the yard, and he was wearing a suit. I thought he was probably from the FBI. It turned out to be Levord Burns, the employee who manages the operation. I repeat, I opened the door just a little, but he put his foot in the slot so that I could no longer close. Several other young men pushed behind, and the whole company burst into the room by force.
“Are you Kevin Mitnick?”
"I already told you that no."
Another agent, Daniel Glasgow, undertook to process me. He was a little older than Burns, awkward, with a graying head. “Hang up,” he said.
I whispered to my mother: "That's it, then we'll talk."
Several agents began to search.
I ask: “Do you have a search warrant?”
Burns replies: “If you are Kevin Mitnik, then we have a warrant for your arrest.”
I replied: "I need to talk with a lawyer."
Agents did not try to stop me.
I called Izurdiaga and said: “Good night, John, this is Thomas Case. I'm in Railay, North Carolina right now. Guests from the FBI came to me. They think that I am a certain Mitnik, and they are looking for something in the apartment, but they have not presented a search warrant. Could you talk to them? ”
...
I handed the phone to an agent who was standing nearby. He picked up the phone and immediately demanded that John introduce himself.
I handed the phone to an agent who was standing nearby. It was Glasgow. He picked up the phone and immediately demanded that John introduce himself. I thought that Izurdiaga would not want to admit it, he knows that I am acting under an assumed name, and this may be fraught with ethical problems for him.
Glasgow handed the phone to Burns. Now there is no doubt who is in charge here.
I heard Izurdiaga say: "You can conduct a search only if you present a valid warrant to my client."
Then Burns hung up, and the whole detachment shook the apartment.
Burns asked me for identification, I pulled out a wallet and presented him with a driver's license in the name of J. Thomas Cayce.
Suddenly one of the agents stumbled upon a cell phone thrown under a bed. He showed it to Burns.
Burns, meanwhile, rummaged through my gym bag and found a second cell phone. In those years, a minute of mobile communication cost about a buck, and the fact that I had, it turns out, two cell phones, could not but arouse suspicion.
Burns asked what the cell number is. I did not say anything - I hoped that he would turn on the phone. I put a fuse there in case of such an emergency: if you turn on the phone and do not enter a secret activation code for a minute, then all the phone’s memory, as well as the programmed and electronic serial numbers will be erased. Zilch! And no evidence.
Heck, he just handed the phone to another agent without even turning it on.
I again demanded: “Present your search warrant!”
Burns opened the folder and handed me the document.
I looked and said: “This order is not valid. The address is not indicated here. ” No wonder I read so many books on law: under the US Constitution, a general search was not allowed. An order is valid only if it specifically and accurately indicates the address at which the search should be conducted.
They set about searching again. As an actor, I tried to imagine myself in the role of a person whose rights are infringed, and loudly declared: “You have no right to be here. Get out of my apartment! You do not have a search warrant. Get out of here, IMMEDIATELY! ”
Several agents took me into the ring. One showed me a piece of paper and asked: “Do you know who this is?”
I could not help smiling. Wow, the US Marshals Service concocted the Wanted poster on me. Unbelievable!
It says: WANTED FOR VIOLATION OF EARLY RELEASE CONDITIONS The
photo there was the same one that was taken more than six years ago in the Los Angeles branch of the FBI, the one that hit the New York Times. In those days, I was much thicker and looked very untidy, since I didn’t wash or shave for three days.
I told the agent: "Yes, he doesn’t look like me at all."
He himself thought: “They hesitate. Maybe you can get out. "
Burns came out, and the two guys set to search again. Two more stood and watched what was happening. When I asked where they were from, one answered that they were serving in the local police, in the task force to search for fugitive criminals in the area of Reilly and Durham. Did the feds think that the three of them could not bind one unarmed hacker?
Suddenly, agent Glasgow noticed my briefcase. It was full of documents, or rather, my many false identities, blank birth certificates and the like. In other words, it was a ticket to jail. He puts the diplomat on the dining table and opens it.
I shout: "Hey!" For a second, he looked up at me, in the meantime I slammed the lid, snapped the code lock, twisted the wheels with numbers - that's it, the briefcase is closed.
He shouted at me: “You, open in a good way!”
I have zero attention. He went into the kitchen and found there a large carving knife.
His face was crimson.
As soon as he was about to stick the knife into the briefcase, another agent Lazell Thomas grabbed his arm. Everyone in the room understood that if a diplomat opened Glasgow by force without a valid search warrant, then whatever it was, it could no longer be attached to the case.
Agent Burns was absent for about half an hour. Then he returned and handed me another warrant, which, by all rules, was printed and signed by a federal judge, only now my address was written down manually. By that time, two agents had been illegally searched for more than two hours.
Agent Thomas began to search my closet. I shouted that he did not meddle there, but he did not listen to me and opened the door. After a while, he again went into the room with my wallet.
“So what have we got here?” He asked with a sharp southern accent.
One by one, I pulled out of my wallet a driver’s license, which I used to use. Everyone else stopped the search and began to monitor him.
“Who is Eric Weiss? - he asked. “Who is Michael Stanfill?”
I wanted to tear all this out of his hands, but I understood: such an action could pass for an attack on a policeman. This is not a good idea in a room stuffed with armed men.
Now they knew that I was not an ordinary hard worker, whose everything was purely in my soul. However, they did come to arrest Kevin Mitnik, and I have nothing in my wallet that would connect me with this person.
Obviously, I played the role extremely convincingly: a private person, a man indignant at the fact that he was unjustly attacked. They even started talking about the need to take me to the city with the whole outfit, take my fingerprints and check whether I really am Mitnik, or just trying to fool them.
I said: “Well, you can drive up. What time can I go to your site in the morning? ”
They ignored me and set about searching again.
My luck did not change me.
It still happens. Thomas shook all the clothes in the closet, reached my old ski suit. He pulled a piece of paper from a zipped inside pocket.
“The receipt of payment,” he said, “was written out in the name of Kevin Mitnik.”
Agent Thomas yelled: “You are arrested!”
Not like in any movie: no one even tried to read my rights to me.
I was so careful, and now the receipt from the company where I worked shortly after leaving Beit Tshuva, the receipt, hidden for many years in a forgotten sportswear pocket, decided my fate.
I have a bile taste in my mouth, I could not even go to the sink and spit. He told the agents that I need to take a cure for reflux disease. They looked at the label on the vial, made sure that the medicine was prescribed by the doctor, but they did not give me the pill.
Incredible. I held out against them for more than three and a half hours, and before that I walked right in front of them for almost three years while the FBI, the US Marshals Service and other secret services were looking for me.
Now it's over.
Agent Thomas stared at me and said: “That's it, Mitnik, played out!”
"FBI".
I was numb. They knocked again. I shouted: “Who are you looking for?”
“Kevin Mitnik. Are you Kevin Mitnick? ”
"Not! - I answered, trying to portray irritation. “You can check my inbox.”
Silent. I thought, maybe they really sent someone to the mailboxes or decided that there would be a sign saying “MITNIK” on the door of my apartment?
Shitty! I greatly underestimated the speed of the federals; they too quickly came to me. I was looking for a retreat. He went out onto the balcony and saw that no one was on duty behind the building. I looked around again, wondering if I could quickly tie a rope out of something. Sheets? Not. Twist them too long. In addition, they may try to shoot me when they see me crawling along the rope.
They knocked again.
I called mom home. There is no time to turn the usual scheme "mom, go to the casino." “I'm in Railay, North Carolina,” I say. “Outside the door of the FBI.” I don’t know where they can take me. ” We talked for a few minutes, trying to cheer each other up. Mom was completely out of her mind, heartbroken, inconsolable. She understood that I would go to jail again. I said how I love her and my grandmother, and in order to feel stronger, I added that we will survive this.
Without stopping talking on the phone, I rushed about in a cramped room, trying to hide everything that might arouse suspicion. Turned off the computer and unplugged the cord from the network. No time to erase everything from the hard drive. The laptop is still warm - you can see that they recently worked with it. I put one cell phone under the bed, the other in the gym bag. Mom told me to contact Aunt Chicky and consult with her.
Chicky gave me the home number of John Isurdiagi, the lawyer who worked with me since the time of the Calabasas affair.
They knocked on the door with renewed vigor and demanded to immediately open the door.
I shouted: “Yes, I sleep. What do you want?"
A voice answered: “We have a few questions for you.”
Trying to portray extreme indignation, I yelled: “Come in the morning when I get enough sleep!”
They were not going to leave. Is there any chance of convincing them that I'm not the one they are looking for?
A few minutes later I called my mother again and said: “Mom, I open the door. Hang on the phone, please. "
I opened a little. The man who tried to shout at me turned out to be black, with a graying beard and at the age of under 40.
It was deep night in the yard, and he was wearing a suit. I thought he was probably from the FBI. It turned out to be Levord Burns, the employee who manages the operation. I repeat, I opened the door just a little, but he put his foot in the slot so that I could no longer close. Several other young men pushed behind, and the whole company burst into the room by force.
“Are you Kevin Mitnick?”
"I already told you that no."
Another agent, Daniel Glasgow, undertook to process me. He was a little older than Burns, awkward, with a graying head. “Hang up,” he said.
I whispered to my mother: "That's it, then we'll talk."
Several agents began to search.
I ask: “Do you have a search warrant?”
Burns replies: “If you are Kevin Mitnik, then we have a warrant for your arrest.”
I replied: "I need to talk with a lawyer."
Agents did not try to stop me.
I called Izurdiaga and said: “Good night, John, this is Thomas Case. I'm in Railay, North Carolina right now. Guests from the FBI came to me. They think that I am a certain Mitnik, and they are looking for something in the apartment, but they have not presented a search warrant. Could you talk to them? ”
...
I handed the phone to an agent who was standing nearby. He picked up the phone and immediately demanded that John introduce himself.
I handed the phone to an agent who was standing nearby. It was Glasgow. He picked up the phone and immediately demanded that John introduce himself. I thought that Izurdiaga would not want to admit it, he knows that I am acting under an assumed name, and this may be fraught with ethical problems for him.
Glasgow handed the phone to Burns. Now there is no doubt who is in charge here.
I heard Izurdiaga say: "You can conduct a search only if you present a valid warrant to my client."
Then Burns hung up, and the whole detachment shook the apartment.
Burns asked me for identification, I pulled out a wallet and presented him with a driver's license in the name of J. Thomas Cayce.
Suddenly one of the agents stumbled upon a cell phone thrown under a bed. He showed it to Burns.
Burns, meanwhile, rummaged through my gym bag and found a second cell phone. In those years, a minute of mobile communication cost about a buck, and the fact that I had, it turns out, two cell phones, could not but arouse suspicion.
Burns asked what the cell number is. I did not say anything - I hoped that he would turn on the phone. I put a fuse there in case of such an emergency: if you turn on the phone and do not enter a secret activation code for a minute, then all the phone’s memory, as well as the programmed and electronic serial numbers will be erased. Zilch! And no evidence.
Heck, he just handed the phone to another agent without even turning it on.
I again demanded: “Present your search warrant!”
Burns opened the folder and handed me the document.
I looked and said: “This order is not valid. The address is not indicated here. ” No wonder I read so many books on law: under the US Constitution, a general search was not allowed. An order is valid only if it specifically and accurately indicates the address at which the search should be conducted.
They set about searching again. As an actor, I tried to imagine myself in the role of a person whose rights are infringed, and loudly declared: “You have no right to be here. Get out of my apartment! You do not have a search warrant. Get out of here, IMMEDIATELY! ”
Several agents took me into the ring. One showed me a piece of paper and asked: “Do you know who this is?”
I could not help smiling. Wow, the US Marshals Service concocted the Wanted poster on me. Unbelievable!
It says: WANTED FOR VIOLATION OF EARLY RELEASE CONDITIONS The
photo there was the same one that was taken more than six years ago in the Los Angeles branch of the FBI, the one that hit the New York Times. In those days, I was much thicker and looked very untidy, since I didn’t wash or shave for three days.
I told the agent: "Yes, he doesn’t look like me at all."
He himself thought: “They hesitate. Maybe you can get out. "
Burns came out, and the two guys set to search again. Two more stood and watched what was happening. When I asked where they were from, one answered that they were serving in the local police, in the task force to search for fugitive criminals in the area of Reilly and Durham. Did the feds think that the three of them could not bind one unarmed hacker?
Suddenly, agent Glasgow noticed my briefcase. It was full of documents, or rather, my many false identities, blank birth certificates and the like. In other words, it was a ticket to jail. He puts the diplomat on the dining table and opens it.
I shout: "Hey!" For a second, he looked up at me, in the meantime I slammed the lid, snapped the code lock, twisted the wheels with numbers - that's it, the briefcase is closed.
He shouted at me: “You, open in a good way!”
I have zero attention. He went into the kitchen and found there a large carving knife.
His face was crimson.
As soon as he was about to stick the knife into the briefcase, another agent Lazell Thomas grabbed his arm. Everyone in the room understood that if a diplomat opened Glasgow by force without a valid search warrant, then whatever it was, it could no longer be attached to the case.
Agent Burns was absent for about half an hour. Then he returned and handed me another warrant, which, by all rules, was printed and signed by a federal judge, only now my address was written down manually. By that time, two agents had been illegally searched for more than two hours.
Agent Thomas began to search my closet. I shouted that he did not meddle there, but he did not listen to me and opened the door. After a while, he again went into the room with my wallet.
“So what have we got here?” He asked with a sharp southern accent.
One by one, I pulled out of my wallet a driver’s license, which I used to use. Everyone else stopped the search and began to monitor him.
“Who is Eric Weiss? - he asked. “Who is Michael Stanfill?”
I wanted to tear all this out of his hands, but I understood: such an action could pass for an attack on a policeman. This is not a good idea in a room stuffed with armed men.
Now they knew that I was not an ordinary hard worker, whose everything was purely in my soul. However, they did come to arrest Kevin Mitnik, and I have nothing in my wallet that would connect me with this person.
Obviously, I played the role extremely convincingly: a private person, a man indignant at the fact that he was unjustly attacked. They even started talking about the need to take me to the city with the whole outfit, take my fingerprints and check whether I really am Mitnik, or just trying to fool them.
I said: “Well, you can drive up. What time can I go to your site in the morning? ”
They ignored me and set about searching again.
My luck did not change me.
It still happens. Thomas shook all the clothes in the closet, reached my old ski suit. He pulled a piece of paper from a zipped inside pocket.
“The receipt of payment,” he said, “was written out in the name of Kevin Mitnik.”
Agent Thomas yelled: “You are arrested!”
Not like in any movie: no one even tried to read my rights to me.
I was so careful, and now the receipt from the company where I worked shortly after leaving Beit Tshuva, the receipt, hidden for many years in a forgotten sportswear pocket, decided my fate.
I have a bile taste in my mouth, I could not even go to the sink and spit. He told the agents that I need to take a cure for reflux disease. They looked at the label on the vial, made sure that the medicine was prescribed by the doctor, but they did not give me the pill.
Incredible. I held out against them for more than three and a half hours, and before that I walked right in front of them for almost three years while the FBI, the US Marshals Service and other secret services were looking for me.
Now it's over.
Agent Thomas stared at me and said: “That's it, Mitnik, played out!”
My intervention and editing was minimal, I would like novice authors to receive feedback not only from me, but also from the habr community.
Text translation - securityqq (Sasha), ottenok_leshi (Lesha), Raccooner (Dima), DDragones (Oleg)
Information search in Mitnik ’s book “The Ghost on the Web” - ottenok_leshi (Lesha), Bio_Wolf (Pasha)
Record holder for finding errors in the text - Trephs (Lesha)
Development of a 3d model of
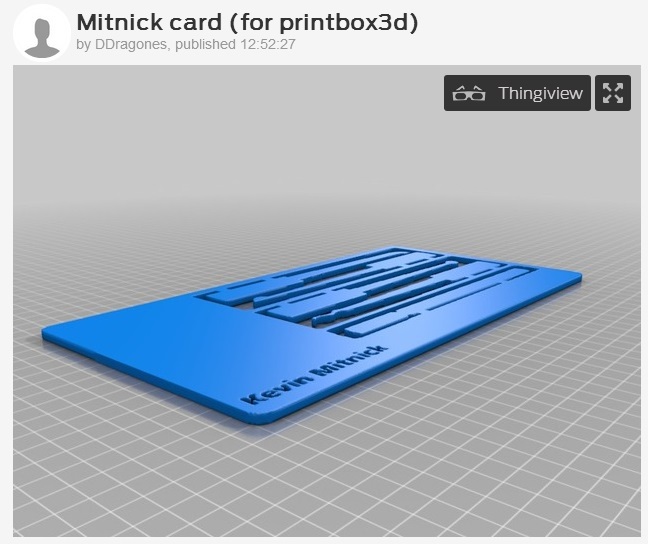
http://www.thingiverse.com/thing:434534


Why Mitnik and not Schneier (Poulsen, Lamo, Koch, Tenenbaum, Assange, Schwartz)?
I was guided by the following considerations when choosing Mitnik as an example for research.
First: Mitnik has a halo of adventure and romance (secrets, penetrations, mnogohodovki, prosecution, searches, impudent behavior with the FBI and security guards). He was both a hacker and a hacker catcher.
Second: He did no harm (did not use stolen credit cards, did not publish the source of the received programs, etc.). His story with a happy ending - entering a socially acceptable position. (Plus Mitnik is out of politics, unlike Assange and Schwartz).
Third:The range of topics covered in the book about Mitnik and other publications is very wide: telephony (wired and cellular), computers, programs, and his hobby is social engineering. This allows us to talk about information security through numerous real-life examples, constantly supporting the attention and interest of a young audience (this is a small stone in the garden of Natalia's lecturer).
Fourth: There are three books and one film in Russian for further study and inspiration to improve your skills. Schneier is good, but academic and has no “adventure component." Poulsen has several books, it seems that they are excellent, but, alas, there are no translations into Russian (can organize habrperep?).
Fifth:Mitnik is a cool man and a pleasant conversationalist. He eagerly responded to the invitation to talk with the Hackspace members (I hope that next time he will be able to arrange a meeting with schoolchildren / students).
I invite the habr community to give feedback to beginning authors and take part in the discussion of the IB educational process (how to inspire young children to study the subject area, how to organize a fun process, on which examples to teach, what books to read, how to explain Torrent , Tor and Bitcoin, etc.).
