Social Engineering in Practice: “Physical Access” to Kevin Mitnik’s Closed Conference
“Physical access is penetration into the building of the company you are interested in. I never liked that. Too risky. I am writing about this - and cold sweat is already breaking through me. ” Kevin Mitnick, “The Ghost on the Web. Memoirs of the greatest hacker "
Even in my student days, when Olympiads and conferences on information security were held, I was enraged that methods and work, including social engineering (SI) , were not accepted . How so! After all, the legendary already in those days Mitnik says that 99% of hacking occurs using SI.
I can’t tell you what my joy was when I found out last September that Mitnik was coming to Moscow, but I was even more happy with the “story of one of my acquaintances” who came to a closed conference for a business audience. I don’t know, maybe he made it up, but still I’ll publish the “text of the translation of his letter”, which he sent me from the “anonymous mailbox”.
Under the cut, an excerpt from Mitnik’s book about physical access and a story about penetrating Mitnik’s conference in Moscow 2013.
An excerpt from the first chapter of the book contains many useful tricks that my acquaintance successfully used.
to read
Somehow I happened to experience what physical access is. An incredible feeling encompasses when on a warm spring evening you hide in the dark parking lot of a company that rolls billions of dollars and choose the right moment. The week before, I visited the building in broad daylight. He came under the pretext that you need to leave a letter for one employee. In fact, upon entering the building, I was able to find out how a pass-identifier looks in this company. So, a close-up photograph of the employee is located in the upper left corner. Right below it is the name and surname, first comes the last one in large block letters. At the bottom of the card is the name of the company in large red letters.
I went to an online club and looked at the company's website. On it it was possible to download and copy the image of the logo of this company. After working for about 20 minutes in Photoshop with a logo and a scanned photo on documents, I made a very convincing facsimile of the identification card. I carefully inserted the result of the creation into a penny badge. Another false pass he made for a friend who agreed to help if his help was needed.
It turned out that one could do without this disguise. In 99% of cases, they almost never look at the pass. If the main elements of the card are located correctly and look something like they should look, then you will calmly get inside. However, some overly zealous guard or employee who decided to play Cerberus may ask you to bring the card closer. And if you live like me, then such a danger can never be discounted.
I can’t see me in the parking lot. I look at the lights of cigarettes of that series of people who go out to smoke. Finally, I notice a group of five to six people returning to the building. The back door is one of those that opens only when one of the employees brings the card to the reader. I seize the moment and attach myself to a similar group last. The guy in front of me crosses the threshold, notices that someone is following him, glances around at me, sees that I have a badge, like all employees, and holds the door so that I enter. I nod gratefully.
This technique is called a “train”.
Inside, I immediately notice a poster, which is located so that every visitor will definitely see it. This poster, posted for added security, warns you that you can’t keep the door in front of someone following you: everyone needs to enter the building one at a time, bringing the ID card to the reader. However, the usual courtesy, the very minimal courtesy that you render every day to a fellow colleague, makes employees with enviable constancy ignore the warning poster.
So I'm inside. I go forward along long corridors with a wide stride of a man who is running to solve an important task. This is actually a research trip and I am looking for an office of an information technology (IT) department. I find him in about ten minutes in another part of the building. I am well prepared for the visit and I know the name of one system administrator for this company. I believe that he has the widest access rights to the corporate network.
Hell! When I find his workplace, it turns out that this is not an ordinary fenced-in cabin like “come in who wants”, but a separate office where the door is locked. However, this problem is instantly resolved. The suspended ceiling is lined with white soundproof squares. Above it is often left the technical floor for pipes, wiring, ventilation, etc.
I call a comrade, say that his help is needed, and return to the back door to let in an accomplice. He, thin and tall, will be able to do what I could not. We return to the department of information technology, and my accomplice climbs onto the table. I grab his legs and lift him high enough. He manages to raise the soundproof plate. I strain, raise it even higher - he grabs the pipe and pulls himself up. Not a minute passes, and I hear that he is already in the office. The door handle turns - and a friend launches me into the office. He is covered in dust, but his smile stretched to the ears.
I go in and quietly close the door. Now we are safer, and the possibility that they will notice us is very small. The office is dark. It is dangerous to turn on the light, but it is not needed either: I have enough of a monitor to see everything I need. In addition, the risk is much less. I quickly examine the table, check what lies in the upper drawer and under the keyboard - suddenly the administrator left the cheat sheet on which he wrote down the password for the computer. Have not found. Sorry, but this is not a problem at all.
I take a bootable CD-ROM with the Linux operating system from my bag, which also contains hacker tools, and insert it into the drive. One of the tools allows you to change the local administrator password. I am changing the password to the one I know, with which I can log in. Then I remove the disk and restart the computer. This time I am logging in with administrator rights through a local account.
I work as quickly as possible. I install a remote access trojan - a special virus that gives me full access to the system - and now I can keep track of all keystrokes, collect encrypted values (hashes) of passwords and even order a webcam to take pictures of a person who is working at a computer. The Trojan that I installed on the machine will be connected via the Internet to another system every few minutes. I have full control over this connection and now I can do whatever I want in the affected system.
I’m doing the last operation: I go into the computer registry and specify as the last user who logged in (last logged in user) the login of an unsuspecting engineer. So I erase all traces of what entered the system through the local administrator account. In the morning the engineer will come to work and notice that for some reason he has logged out of the system. It's okay: as soon as he enters it again, everything will look exactly as it should.
It's time to go back. My friend has already replaced the soundproof tile. Leaving, I close the door to the castle.
The next day at 08:30 the system administrator turns on the computer and connects to my laptop. Since the trojan runs under his account, I have all administrator rights in this domain. In just a few seconds, I find a domain controller that contains passwords for all the accounts of employees of this company. The hacker tool fgdump allows me to collect hashed, that is, encrypted, passwords from each user in a separate file.
In a few hours, I run the list of hashes through the “rainbow tables” - a huge database that contains pre-computed password hashes - and recover the passwords of most employees of this company. In the end, I find an internal server that processes user transactions, but I understand that the credit card numbers are encrypted. However, this is not a problem at all. It turns out that the key used to encrypt the numbers is hidden in a stored procedure inside the database on the SQL server computer. Access to this computer is open to any database administrator.
Several million credit card numbers. I can buy whatever I want, use a different card every time, and most importantly - they will never end.
Believe me, I'm not going to buy anything. This true story is not another hacking attempt, because of which I have made a lot of trouble. I was hired to complete this infiltration.
I went to an online club and looked at the company's website. On it it was possible to download and copy the image of the logo of this company. After working for about 20 minutes in Photoshop with a logo and a scanned photo on documents, I made a very convincing facsimile of the identification card. I carefully inserted the result of the creation into a penny badge. Another false pass he made for a friend who agreed to help if his help was needed.
It turned out that one could do without this disguise. In 99% of cases, they almost never look at the pass. If the main elements of the card are located correctly and look something like they should look, then you will calmly get inside. However, some overly zealous guard or employee who decided to play Cerberus may ask you to bring the card closer. And if you live like me, then such a danger can never be discounted.
I can’t see me in the parking lot. I look at the lights of cigarettes of that series of people who go out to smoke. Finally, I notice a group of five to six people returning to the building. The back door is one of those that opens only when one of the employees brings the card to the reader. I seize the moment and attach myself to a similar group last. The guy in front of me crosses the threshold, notices that someone is following him, glances around at me, sees that I have a badge, like all employees, and holds the door so that I enter. I nod gratefully.
This technique is called a “train”.
Inside, I immediately notice a poster, which is located so that every visitor will definitely see it. This poster, posted for added security, warns you that you can’t keep the door in front of someone following you: everyone needs to enter the building one at a time, bringing the ID card to the reader. However, the usual courtesy, the very minimal courtesy that you render every day to a fellow colleague, makes employees with enviable constancy ignore the warning poster.
So I'm inside. I go forward along long corridors with a wide stride of a man who is running to solve an important task. This is actually a research trip and I am looking for an office of an information technology (IT) department. I find him in about ten minutes in another part of the building. I am well prepared for the visit and I know the name of one system administrator for this company. I believe that he has the widest access rights to the corporate network.
Hell! When I find his workplace, it turns out that this is not an ordinary fenced-in cabin like “come in who wants”, but a separate office where the door is locked. However, this problem is instantly resolved. The suspended ceiling is lined with white soundproof squares. Above it is often left the technical floor for pipes, wiring, ventilation, etc.
I call a comrade, say that his help is needed, and return to the back door to let in an accomplice. He, thin and tall, will be able to do what I could not. We return to the department of information technology, and my accomplice climbs onto the table. I grab his legs and lift him high enough. He manages to raise the soundproof plate. I strain, raise it even higher - he grabs the pipe and pulls himself up. Not a minute passes, and I hear that he is already in the office. The door handle turns - and a friend launches me into the office. He is covered in dust, but his smile stretched to the ears.
I go in and quietly close the door. Now we are safer, and the possibility that they will notice us is very small. The office is dark. It is dangerous to turn on the light, but it is not needed either: I have enough of a monitor to see everything I need. In addition, the risk is much less. I quickly examine the table, check what lies in the upper drawer and under the keyboard - suddenly the administrator left the cheat sheet on which he wrote down the password for the computer. Have not found. Sorry, but this is not a problem at all.
I take a bootable CD-ROM with the Linux operating system from my bag, which also contains hacker tools, and insert it into the drive. One of the tools allows you to change the local administrator password. I am changing the password to the one I know, with which I can log in. Then I remove the disk and restart the computer. This time I am logging in with administrator rights through a local account.
I work as quickly as possible. I install a remote access trojan - a special virus that gives me full access to the system - and now I can keep track of all keystrokes, collect encrypted values (hashes) of passwords and even order a webcam to take pictures of a person who is working at a computer. The Trojan that I installed on the machine will be connected via the Internet to another system every few minutes. I have full control over this connection and now I can do whatever I want in the affected system.
I’m doing the last operation: I go into the computer registry and specify as the last user who logged in (last logged in user) the login of an unsuspecting engineer. So I erase all traces of what entered the system through the local administrator account. In the morning the engineer will come to work and notice that for some reason he has logged out of the system. It's okay: as soon as he enters it again, everything will look exactly as it should.
It's time to go back. My friend has already replaced the soundproof tile. Leaving, I close the door to the castle.
The next day at 08:30 the system administrator turns on the computer and connects to my laptop. Since the trojan runs under his account, I have all administrator rights in this domain. In just a few seconds, I find a domain controller that contains passwords for all the accounts of employees of this company. The hacker tool fgdump allows me to collect hashed, that is, encrypted, passwords from each user in a separate file.
In a few hours, I run the list of hashes through the “rainbow tables” - a huge database that contains pre-computed password hashes - and recover the passwords of most employees of this company. In the end, I find an internal server that processes user transactions, but I understand that the credit card numbers are encrypted. However, this is not a problem at all. It turns out that the key used to encrypt the numbers is hidden in a stored procedure inside the database on the SQL server computer. Access to this computer is open to any database administrator.
Several million credit card numbers. I can buy whatever I want, use a different card every time, and most importantly - they will never end.
Believe me, I'm not going to buy anything. This true story is not another hacking attempt, because of which I have made a lot of trouble. I was hired to complete this infiltration.
Text of the letter
(The letter was in English, so my translation is a little crooked, I redrawn the picture too).
“I learned about the arrival of Mitnik in a couple of days. After searching the Internet for information, I found only the contacts of the organizers. I sent out several requests on behalf of the Information Security Department of a technical university. Sorry, but the organizers did not answer the letter. Well, I decided to go the other way. I found out where the meeting will take place. I arrived at the specified address with the intention of sorting out on the spot. It was a nook on the promenade. It was easily found by signs and banners with the name of the event.
How it looked outside:

It was a narrow dead end. On the street in front of the building’s entrance there was a smoking room, coffee-break tables and a reception, where passes were issued. The entrance was strictly by passes, 2 security guards followed, 90% of them were alone, sometimes one left, but the second always remained at the post.
I settled in a purple dot and pretended to be waiting for someone. Periodically, I took out the phone and said to it that I was already in place and how many fools still had to wait. It was always one and a half to two meters from the entrance, so I heard everything the guards were saying, and they heard what I was saying. So an hour passed, and I gathered quite a lot of information. What color is the badge of anyone, how exactly is the badge checked, is there anyone who passes without badges, how are the waiters, are there any service entrance, etc. During this time, there was a change of guards, which pleased me.
During the time that I stood, I noticed that for the media they sometimes give out badges without a full name and they differed in color. It was also noticed that already several media teams managed to come in and out, that is, they made a report and left.
I'm waiting. I'm watching. I see that another media team is coming out with the intention of leaving permanently. These were a couple of female journalists and a couple of cameramen.
I attract the attention of girls, stand next to the guards, look behind all the tenacious eyes of the special agent. I try to make eye contact.
So they leave, I slowly follow him. Around a bunch of people scurry around - participants, organizers, security guards. So let's move on. Green dots indicate the path of the media. Without leaving the alley, I watched the media cross the road and put cameras in the car. And here I am speeding up, running across the road, running to the car, one girl has not yet got inside, making a slightly alarmed face and saying: “Sorry, I’m from the organizers, you saw me at the entrance, we help the security service. By our mistake, we accidentally released you with badges, and this is prohibited by the rules, otherwise someone can use it and unauthorized access to the building. Please hand over your badges. “And they handed over. And they asked for forgiveness. Bingo!
Badges are on hand, but they are with female names. It is good that the badge was plastic, and the names were printed on self-adhesive and glued to the badge. It was easy to pick them up, although the handles shook.
Since I knew that some media were simply allowed to get their badges without a full name, I did not bother and did not look for the nearest express printing house, but got insolence and moved on to the second stage.
I returned to the entrance, stood for about 5 minutes, took out the phone, went closer to the guards to be heard, and said into the pipe: “Ale. Have you arrived yet? And the pass with you? I’m already going, I’m tortured to wait so much for you. “
Then I turned around the corner, put on a badge, turned his back just in case (I saw that the guards let him in this situation too), returned to the entrance and came in through the door with a confident and confident look protection.
First of all, I went to the banquet hall and ate as much meat and cakes as I could. Feel better. And just announce the beginning of the performance of Kevin Mitnik. Heading to the conference room on the second floor. A wide staircase leads to the second floor, I take a step to the first step and I hear a firm but very polite voice: “Young man, can you wait a minute.”
Pam. I turn around, on the sides of the stairs are two security guards in more prestigious suits than those on the street.
“Turn over, please, your badge.” I turn it over
. “Everything is fine, you can go through.”
What thoughts were in my head as I climbed the stairs, I will leave this to the discretion of your imagination.
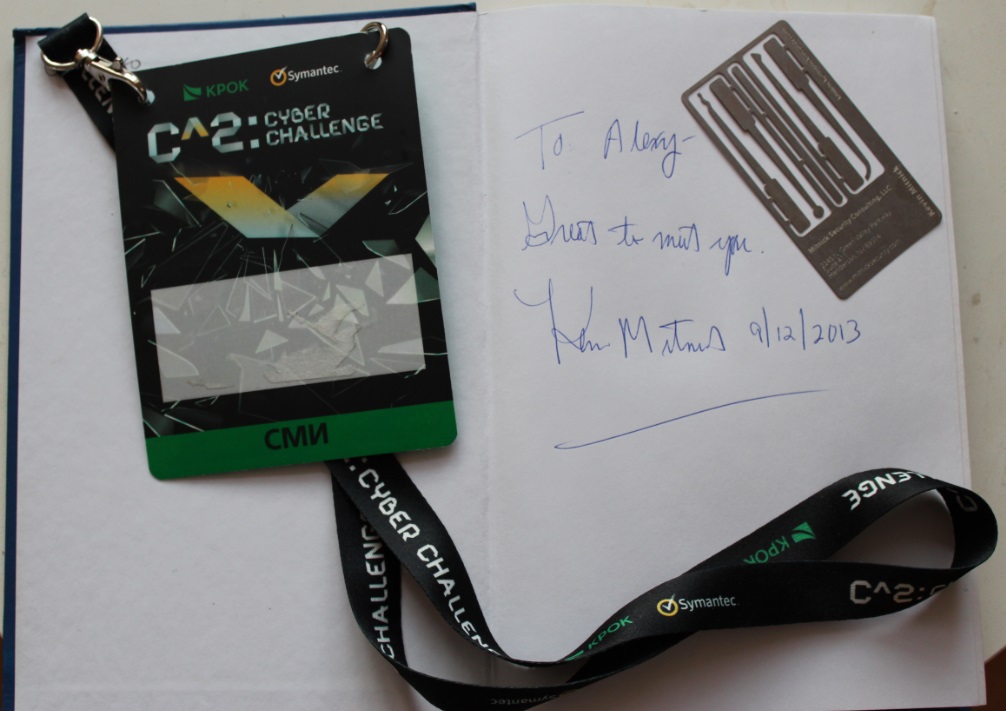
But in the form of a trophy I have a book with the signature of Mitnik, his legendary business card and Nouneymsky badge. "
End of story
Such stories happen and I am very curious to get acquainted with such stories (and it’s even more interesting to be a participant).
If anyone is familiar with interesting examples of social engineering, share these examples in the comments.
UPD (Aug 6) Happy Birthday, Kevin Mitnik!
