New ransomware options found for Android
Earlier, we wrote about a new version of the ransomware for Android, which encrypts user files and is called Simplocker. Now we have additional information about other variants of this malware. These detected modifications differ from each other in the following ways.

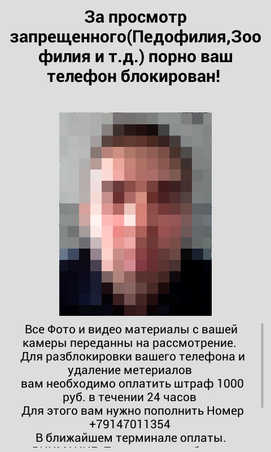
Fig. A screenshot of the ransom demand form in the case of Android / Simplocker.B , which depicts a portrait of the victim. The currency for the repurchase is indicated in Russian rubles.
A simplified approach to encryption using the AES algorithm and a hard-wired key is still present in most modifications of the malware that we discovered. In addition, some of these modifications do not contain the ability of an encryptor, that is, they do not encrypt files, but simply block access to the device.
As already mentioned in our previous posts, the threat is most widespread in Russia and Ukraine. When it gets to the user's device, Android / Simplocker really causes him considerable trouble, as the user loses access to his files.

Fig. Distribution geography of Android / Simplocker according to ESET LiveGrid cloud technology.
One of the most important issues in detecting a malicious program is its origin or infection vector, i.e., how it can get to the user's device. Our ESET LiveGrid telemetry system showed several Android / Simplocker infection vectors. For him, a typical distribution method is to disguise himself as an application related to pornography. In addition, the attackers also disguised the ransomware as games, for example, Grand Theft Auto: San Andreas.

Fig. A porn site that distributes Android / Simplocker.

Fig. Fake game icon Grand Theft Auto: San Andreas.
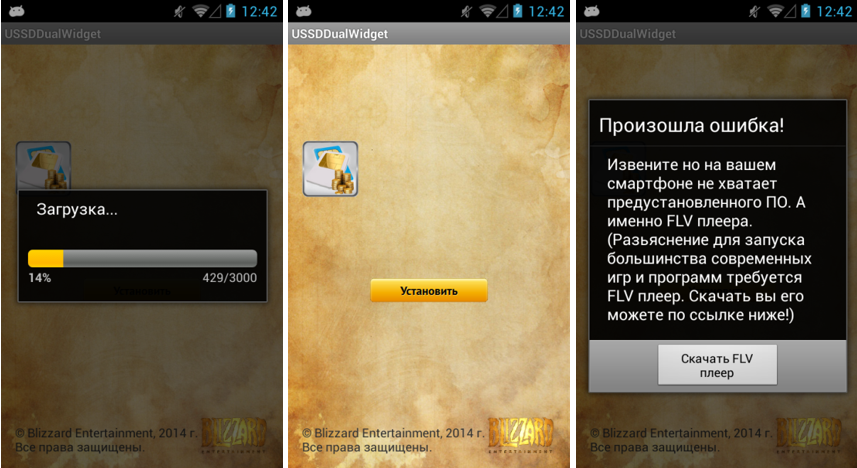
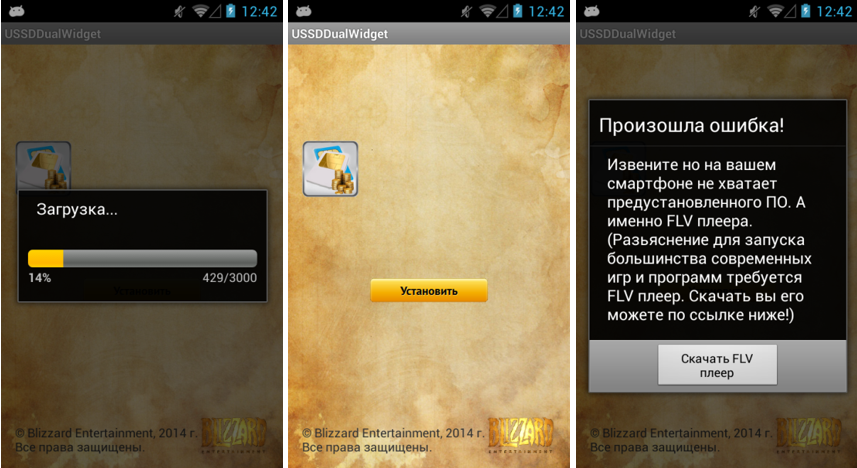
In the course of the investigation, we found that Android / Simplocker is spreading through another malicious program, the so-called a downloader or bootloader that remotely downloads the main Simplocker file. The use of such bootloaders is a common practice in the Windows world, but recently they have also been used for Android.
Downloaders are an additional malware distribution vector for Android. They complement traditional methods of social engineering, for example, the use of porn, as mentioned above. Another method of installing malicious code on a device is to exploit a vulnerability in software or OS.
Our sample of one of the downloaders is detected as Android / TrojanDownloader.FakeApp. He convinces the user to download a fake video player, which, in fact, is Android / Simplocker. An application such as a downloader has a much greater chance of avoiding the exposure of its malicious activity by Google Play security applications, for example, Bouncer, due to the following features:
In addition, in the sample we analyzed, the URL contained in the application does not indicate a malicious APK file from Simplocker directly. Instead, the trojan is downloaded to the device after being redirected to another server, which is under the control of intruders. This bootloader disguised itself in the application store as a legitimate application called USSDDualWidget.
- Using Tor. Some modifications use regular domains to communicate with C&C, others use .onion domains that belong to Tor .
- Various ways of transmitting the decrypt command, which signals the fact of a ransom being received by intruders.
- A different window interface with information about the repurchase, as well as various currencies for its payment (Ukrainian hryvnia and Russian ruble).
- Using camera snapshots. Some modifications of Simplocker add a photograph of the phone’s owner, which was made on the built-in camera, to the ransomware window interface.

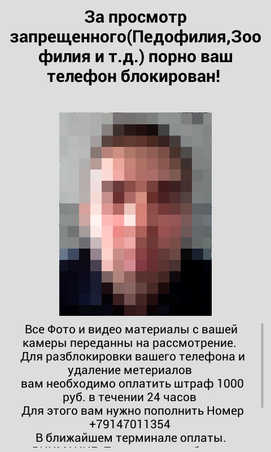
Fig. A screenshot of the ransom demand form in the case of Android / Simplocker.B , which depicts a portrait of the victim. The currency for the repurchase is indicated in Russian rubles.
A simplified approach to encryption using the AES algorithm and a hard-wired key is still present in most modifications of the malware that we discovered. In addition, some of these modifications do not contain the ability of an encryptor, that is, they do not encrypt files, but simply block access to the device.
As already mentioned in our previous posts, the threat is most widespread in Russia and Ukraine. When it gets to the user's device, Android / Simplocker really causes him considerable trouble, as the user loses access to his files.

Fig. Distribution geography of Android / Simplocker according to ESET LiveGrid cloud technology.
One of the most important issues in detecting a malicious program is its origin or infection vector, i.e., how it can get to the user's device. Our ESET LiveGrid telemetry system showed several Android / Simplocker infection vectors. For him, a typical distribution method is to disguise himself as an application related to pornography. In addition, the attackers also disguised the ransomware as games, for example, Grand Theft Auto: San Andreas.

Fig. A porn site that distributes Android / Simplocker.

Fig. Fake game icon Grand Theft Auto: San Andreas.
In the course of the investigation, we found that Android / Simplocker is spreading through another malicious program, the so-called a downloader or bootloader that remotely downloads the main Simplocker file. The use of such bootloaders is a common practice in the Windows world, but recently they have also been used for Android.
Downloaders are an additional malware distribution vector for Android. They complement traditional methods of social engineering, for example, the use of porn, as mentioned above. Another method of installing malicious code on a device is to exploit a vulnerability in software or OS.
Our sample of one of the downloaders is detected as Android / TrojanDownloader.FakeApp. He convinces the user to download a fake video player, which, in fact, is Android / Simplocker. An application such as a downloader has a much greater chance of avoiding the exposure of its malicious activity by Google Play security applications, for example, Bouncer, due to the following features:
- the fact that the application opens the URL (follows it) does not yet indicate its malicious activity;
- The bootloader itself does not require "potentially dangerous" permissions for its application.
In addition, in the sample we analyzed, the URL contained in the application does not indicate a malicious APK file from Simplocker directly. Instead, the trojan is downloaded to the device after being redirected to another server, which is under the control of intruders. This bootloader disguised itself in the application store as a legitimate application called USSDDualWidget.