Ransomware for Android encrypts files on the device
Last week, our anti-virus lab discovered an interesting sample of malicious code for Android. It is a ransomware for Android devices that encrypts user files and then requires a ransom for decrypting them. This type of ransomware is widespread in the Windows world. Attackers encrypt user files and then block the desktop with a ransom request.

A malicious program has been added to our databases as Android / Simplocker . After infecting the device, it checks the memory card for the presence of certain types of files there, then encrypts them and blocks access to the device with a ransom message. Simplocker performs its operations in the same way as ransomware for Windows does.
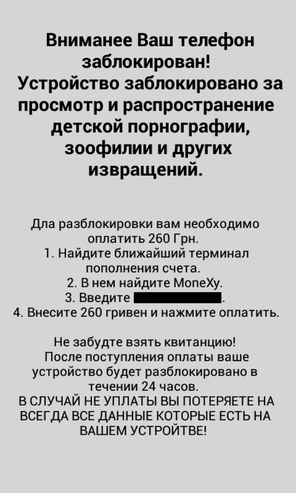
Fig. A message that a malicious program displays when a device is blocked.
As you can see in the screenshot above, the message about the blocking is written in Russian and requires a ransom payment in Ukrainian hryvnias, which suggests that the ransomware is focused on Ukraine. Note that the very first Android SMS Trojans ( including Android / Fakeplayer ), which appeared in 2010, also have Russian and Ukrainian origin.
Attackers send the victim to pay the ransom using the MoneyXy service, since the clients of this service are not so easy to track, unlike the customers of ordinary payment systems that work with credit cards.
After infecting the device, the malicious code is Android / Simplocker.Awill check the file system of the memory card for the presence of pictures, documents or videos, i.e. files with the following extensions: jpeg, jpg, png, bmp, gif, pdf, doc, docx, txt, avi, mkv, 3gp, mp4 . Once these files are discovered, each of them will be encrypted using the AES symmetric encryption algorithm.
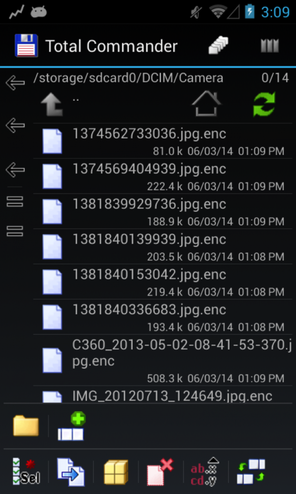
Fig. Encrypted Android / Simplocker.A files. A new .enc extension has been added for each file.
The ransomware interacts with its remote C&C server and sends it some identification information about the device, for example, the IMEI identifier . It is interesting to note that the URL of the C&C server itself is hosted on the .onion domain, which belongs to the anonymous TOR network. This allows attackers to provide the proper level of anonymity.
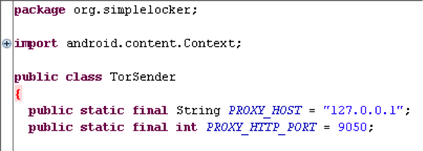
Fig. Part of the Android / Simplocker.A code for connecting to the TOR network.
As you can see in the screenshot of the lock screen above, the message does not contain a special field for entering a code confirming receipt of a ransom by intruders. This code entry field is widespread in the case of Windows ransomware. Instead, Android / Simplocker.A constantly listens for connections to the C&C server to receive a confirmation message that the funds were successfully transferred to attackers.
The Android / Simplocker.A sample we analyzed was distributed as an application called “Sex xionix”. It has not been detected on Google Play and we believe that it has a fairly low prevalence rate today.
Our analysis of this threat showed that in the case of Simplocker, attackers managed to get closer to implementing the concept of the notorious ransomware Cryptolocker, which made a lot of noise in the Windows world. Despite the fact that Android / Simplocker.A contains code for decrypting encrypted files on the device, we strongly do not recommend users to follow the lines of attackers. There is no guarantee that after payment of the required amount the files will be decrypted or you will not fall into the bait of attackers again.
We recommend that users protect themselves from this type of threat through prevention and protective proactive measures. To do this, you can use the ESET Mobile Security app for Android, which will keep your device safe. When working with Android, do not install applications obtained from unreliable sources on your device, this will significantly reduce the risk of compromising the device with malware. Back up data on your device in a timely manner, this is one of the best ways to protect against ransomware ransomware, as it will allow you to quickly restore your data from a backup source.

A malicious program has been added to our databases as Android / Simplocker . After infecting the device, it checks the memory card for the presence of certain types of files there, then encrypts them and blocks access to the device with a ransom message. Simplocker performs its operations in the same way as ransomware for Windows does.
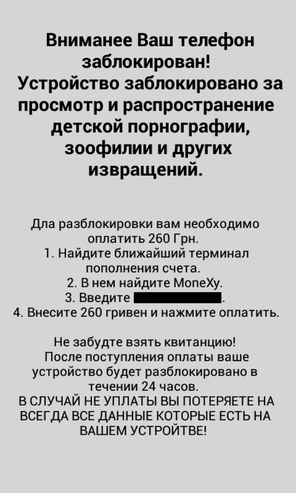
Fig. A message that a malicious program displays when a device is blocked.
As you can see in the screenshot above, the message about the blocking is written in Russian and requires a ransom payment in Ukrainian hryvnias, which suggests that the ransomware is focused on Ukraine. Note that the very first Android SMS Trojans ( including Android / Fakeplayer ), which appeared in 2010, also have Russian and Ukrainian origin.
Attackers send the victim to pay the ransom using the MoneyXy service, since the clients of this service are not so easy to track, unlike the customers of ordinary payment systems that work with credit cards.
After infecting the device, the malicious code is Android / Simplocker.Awill check the file system of the memory card for the presence of pictures, documents or videos, i.e. files with the following extensions: jpeg, jpg, png, bmp, gif, pdf, doc, docx, txt, avi, mkv, 3gp, mp4 . Once these files are discovered, each of them will be encrypted using the AES symmetric encryption algorithm.
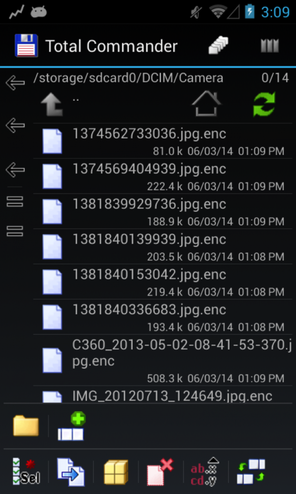
Fig. Encrypted Android / Simplocker.A files. A new .enc extension has been added for each file.
The ransomware interacts with its remote C&C server and sends it some identification information about the device, for example, the IMEI identifier . It is interesting to note that the URL of the C&C server itself is hosted on the .onion domain, which belongs to the anonymous TOR network. This allows attackers to provide the proper level of anonymity.
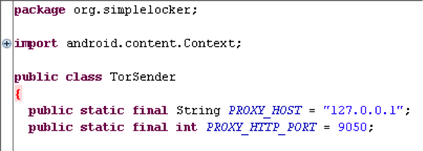
Fig. Part of the Android / Simplocker.A code for connecting to the TOR network.
As you can see in the screenshot of the lock screen above, the message does not contain a special field for entering a code confirming receipt of a ransom by intruders. This code entry field is widespread in the case of Windows ransomware. Instead, Android / Simplocker.A constantly listens for connections to the C&C server to receive a confirmation message that the funds were successfully transferred to attackers.
The Android / Simplocker.A sample we analyzed was distributed as an application called “Sex xionix”. It has not been detected on Google Play and we believe that it has a fairly low prevalence rate today.
Our analysis of this threat showed that in the case of Simplocker, attackers managed to get closer to implementing the concept of the notorious ransomware Cryptolocker, which made a lot of noise in the Windows world. Despite the fact that Android / Simplocker.A contains code for decrypting encrypted files on the device, we strongly do not recommend users to follow the lines of attackers. There is no guarantee that after payment of the required amount the files will be decrypted or you will not fall into the bait of attackers again.
We recommend that users protect themselves from this type of threat through prevention and protective proactive measures. To do this, you can use the ESET Mobile Security app for Android, which will keep your device safe. When working with Android, do not install applications obtained from unreliable sources on your device, this will significantly reduce the risk of compromising the device with malware. Back up data on your device in a timely manner, this is one of the best ways to protect against ransomware ransomware, as it will allow you to quickly restore your data from a backup source.
