What tasks do IAM systems solve?
What tasks do IAM systems solve?
Terminology
Most often we come across the term Identity Management (IdM), which means managing user accounts or electronic representations of users. Typically, an IdM system is required to manage not only accounts, but also access to systems. Therefore, usually speaking of IdM, they mean Identity and Access Management.
Identity and Access Management (IAM) refers to a set of technologies and software products that meet the challenges of managing the life cycle of accounts and controlling access to various systems in a company. Analytical agencies (Gartner, Forrester, KuppingerCole) and IAM system developers identify at least two areas within IAM: User Administration and Provisioning (UAP) and Identity and Access governance (IAG). A modern IAM solution should provide functionality in both areas.
UAP solutions appeared in the late 1990s as a means of automating work with directory services. UAP solves the problems of automating the creation, modification and deletion of accounts in the organization’s information systems, and also provides access to the applications and resources that the user needs to work.
Typical IAM Tasks
UAP Tasks
Imagine the process of organizing access to IT resources (applications, data, services) in a company without automation. The employee at the time of hiring the personnel department contributes to 1C. Then information about him gets into the IT department. The IT department creates an account in the Active Directory directory service. A new employee receives access to folders, applications, mailings by contacting the system administrator or the support service by e-mail, in some cases, the consent of the manager or owner of the resource is required. Moreover, an employee never asks to “select access” and over the years of work in a company can “grow” access to various systems.
If the organization of access in a small company is decided by direct communication and a newcomer can get access to everything that is required for work during the day, then in a geographically distributed company with more than 500 people it can take days.
Employees can change positions, phone numbers, last names, and these changes should be reflected in information systems. Some companies have contract workers or seasonal workers. Upon termination of the contract or change of position, access to resources must be terminated.
If the company has several information systems, for example, a document management system, an accounting system, an external portal, the task of managing passwords appears. Each system is controlled by different people. The password in each system is created separately (i.e., personal passwords are assigned). It is difficult for the user to remember several passwords, and this leads to the fact that they are stored on paper. If you need to change the password, you need to find the owner of the application, which may be on vacation, and access is necessary now.
Imagine a situation when an employee on a business trip decided to connect access to mail on a mobile phone and made a mistake when entering the password. His account will be blocked during repeated attempts to enter incorrect data, and he will not be able to access mail on his own.
When an employee is fired, it is necessary to block his access to all company systems, sometimes it is important to do this within a minute.
Such a process on the scale of a large organization takes a lot of time from the IT department, inevitably leads to errors and, as a result, financial losses.
Quite often on the Internet you can read about legal cases related to the fact that the dismissed employee has access to the enterprise systems, for example:
www.kuzbass85.ru/2012/04/11/uvolennyiy-sistemnyiy-administrator-udalil-chetyirehletniy-arhiv- buhucheta-byivshego-predpriyatiya
The court found that in July 2011 Prikhodko, being at home in the city of Kemerovo, made unauthorized access to the mail server of the enterprise where he had previously worked. Then he removed the program “1C Enterprise” for the period from 2007 to 2011. As a result, the accounting data on the servers of three holding company companies located in Prokopyevsk were destroyed.
We will not find out about many such cases, as banks or insurance companies prefer not to advertise such incidents.
Now let's see what the automated process looks like.
After the appearance of an account in the personnel system, the UAP solution automatically creates accounts in the connected systems, and gives access based on user attributes (for example, position and department) and groups. UAP-system allows you to check the values of attributes for compliance with the rules and prohibit the creation of "incorrect records", in particular, with an empty post. When changes are enough to make them in one place - and they will automatically be reflected in all connected systems. So, for example, the user, changing the password in AD, automatically receives the same password on all systems. When transferring or dismissing an employee, the system selects access to all systems almost instantly.
It is important to note that UAP was initially aimed more at solving the routine tasks of IT departments for user and resource administration. However, such solutions were not intended for organizing access control to systems and were not intended for non-IT users. That is, UAP-systems automatically granted access and selected it, but could not give an answer to the question of what resources the user has access to now. It was also important to give users the opportunity to independently request access to resources (applications, data, services), and their managers (or resource owners) to confirm the eligibility of access when requesting, to organize certification for checking who has access to a particular resource.
At first, these needs were covered by a set of extended functionality of UAP products, but it was clear that such tasks require new solutions.
IAG Tasks
In the mid-2000s, specialized IAG proposals began to appear. The IAG system solves the tasks of requesting, confirming, certifying and auditing access to applications, data and services, and also provides control and business intelligence for the processes of creating accounts, managing these records and how these records were used for access. Unlike UAP, where rights in systems were tied directly to accounts, IAG solutions operate with roles that are associated with the organizational structure of the enterprise. We can say that in the UAP solutions, the IT department was responsible for issuing access, and the IAG systems returned the reins of access control to business users.
Let's look at specific examples of the use of IAG solutions. Suppose you want to use Adobe Photoshop on a work computer. First, the user sends a request to the technical support service. Its employees are waiting for the confirmation of the head, who is added to the correspondence. As a result, the user receives the installed application, spending a couple of days on it. It happens that several people participate in the coordination (so in order to get a new laptop, you need confirmation from the head and director).
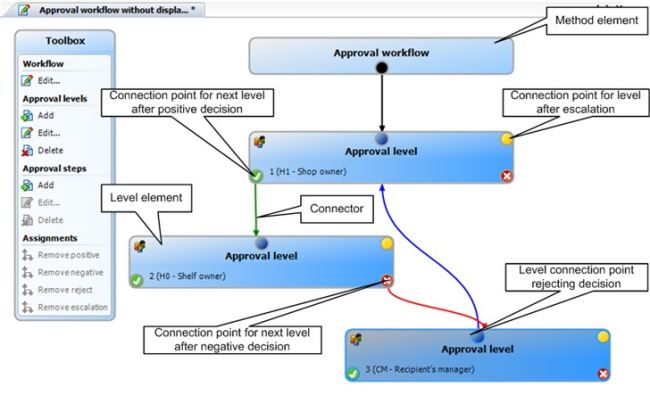
IAG solutions offer the automation of such processes using a web portal where you can request a resource, then a “invisible” process will be launched, which, if necessary, will request the confirmation of the head and after receiving it will automatically make the necessary changes.
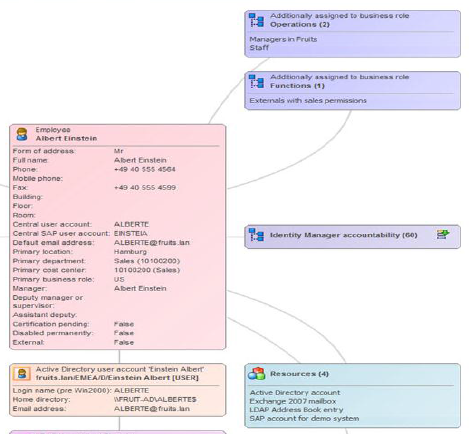
The IAG system allows the supervisor or security officer to see which systems the user has access to and also manage this access.
Access can also be granted on the basis of “calculated” rules, that is, if an employee is assigned to work on a specific project and he has the appropriate role, he will automatically gain access to the required documentation, which will avoid “manual approvals”.
If the user has extra rights (for example, the Active Directory administrator added the user to the group) that do not correspond to his role, the security service will receive a notification about this and may confirm the exception or take measures to eliminate it.
An important part of the role management process is Separation of Duties (SoD) policies or separation of powers. These policies prohibit the combination of certain roles. For example, the employee creating the order should not participate in financial transactions.
Some areas of IAM development
IAM solutions are developing rapidly, covering new areas, such as content-based data management, mobile device management, risk-based authorization, and many others.
As we can see, existing IAM solutions make it possible to control access to centralized resources. However, modern companies have huge amounts of unstructured data stored on users' computers in network folders. The user can easily copy valuable data to his computer and then distribute it uncontrollably.
To solve this problem, modules appear in IAM products that allow you to classify data according to the contents and attributes of a document and provide access based on a comparison of data provided by the user (who the user is and what device he uses) and classification data of the document (what data the document contains).
Another promising area is the management and interaction with mobile devices. In modern companies, users use not only desktop computers, but also smartphones and tablets. In many cases, these are not corporate devices, but personal ones. The BYOD policy (Bring your own device, or bring your device) is gaining popularity by reducing the company's costs of supporting infrastructure, purchasing devices. With the popularization of this policy, new challenges are emerging. How to protect company data stored on the device, but at the same time respect the integrity of the employee’s private information?
The technology of using login and password to access company resources has been criticized for a long time, however, no one could offer a worthy replacement. Two-factor authentication methods (for example, a combination of the traditional method and SMS) are not widely used. Now, IAM solution providers are moving towards authentication based on contextual data about the user, device, application, where the request came from. These data are analyzed and a decision is made on the identity of the user. Such an algorithm of work exists in some social networks. So, when entering a login from another country, you can get an offer to specify additional data (phone number, for example).
How to choose the right IAM system
IAM Solutions Market
The IAM market is actively developing, mergers and acquisitions are taking place. The complexity of IAM systems increases significantly every year. Evaluation of modern IAM-proposals requires serious expertise not only in the field of information technology, but also in the field of business analytics.
There are several analytical agencies specializing in research and comparison of IAM solutions: Forrester, KuppingerCole, Gartner. They, as a rule, issue an annual report on the IAM-solutions market, as well as separate documents on industry trends, questionnaires to help you choose the most suitable system. If annual reports can be found on the websites of solution providers, then specialized documentation, as a rule, costs from hundreds to tens of thousands of dollars.
For annual reports, each agency has its own methodology of comparisons and visual presentation of the results.
So, for example, Gartner evaluates IAM suppliers on the Vision scale (a vision of how the market is developing and developing, the ability to innovate) and “Implementation ability” (the ability to occupy market share and sell the system).

There are several diagrams in the KuppingerCole report where IAM solution providers are ranked on a single scale (overall product rating in the screenshot below).
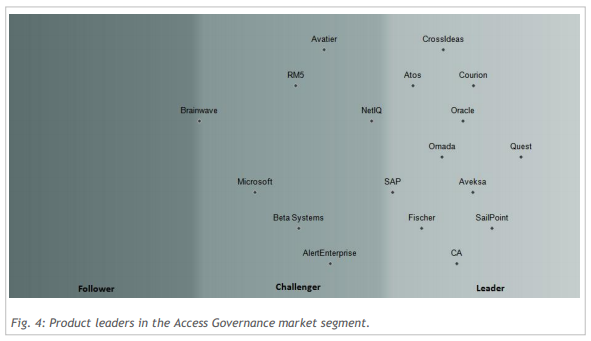
Such reports provide an understanding of the subject area, market trends and a general idea of major players in the IAM market.
It is important to understand that many systems are not represented at all on the Russian market. There may also be local solutions that are quite successful in the Russian market, but which are not widespread in the world.
System Selection Criteria
As there are no two identical enterprises with the same set of applications and business processes, so there are no universal and the best IAM systems. Each IAM-system has a unique set of functionality, connectors to target systems, frameworks for expanding functionality.
You can start your choice with formal requirements, such as the cost of ownership (the cost of licenses, implementation and support for several years), licensing policy, the presence of successfully completed projects in similar companies / industries, the availability of implementation and support specialists in Russia.
Technical requirements can also help: the presence of connectors to common systems used in the enterprise, a web interface for business users, automation of business processes (for example, approvals), a certification mechanism, requirements for open expansion of functionality (when the system can be expanded without a manufacturer) .
After selecting some of the most suitable suppliers, you can see how the system works with the main and most important scenarios that need to be automated.
Usually these are scenarios of an employee’s life cycle: hiring, transferring to another department or office, vacation, dismissal. A set of access control scenarios is also important: issuing temporary and permanent access to systems upon request, automatically or by agreement based on roles in the company or project, access control according to a schedule (certification) and request.
When working with account data, it is important to verify their correctness (for example, the format of the phone number), as well as convert the data during synchronization, in particular, transliterate names when synchronizing the personnel system and Active Directory.
As a rule, connectors are used to automate the life cycle of users in target systems. These are dedicated IAM modules that interact with an external system, create, modify, delete accounts and provide access by transferring roles in the IAM system to a set of rights that is understandable for the target system, for example, a group. Connectors often change due to changes in the target system. Will IAM support the new version of 1C or SalesForce? How expensive is the completion of the connector?
It is important to understand that the IAM system is not a boxed product and in most projects the cost of services can be several times higher than the cost of licenses. IAM projects never end (except for unsuccessful ones), since the target systems under the control of IAM offerings are constantly changing and require reconfiguration, updating or revision. Therefore, system extensibility is a very important selection criterion. Will it be necessary to attract supplier specialists for each change, or can administrators and business users of the customer deal with this?
Sample scenarios for evaluating an IAM system
Hiring
Scenario: After the human resources department creates an account for a new employee in the personnel system (for example, 1C), the employee must receive accounts and sets of rights in all systems according to his role no later than n minutes later.
Result:
An employee can use all systems within the scope of his role.
Request for access to a resource
Scenario: After an employee requests a resource through a web portal, he should receive a response within n hours. Temporary access to the resource is regulated by manual coordination. That is, the request is received by the owner of the resource and / or his deputy. If the request remains unanswered for a specified time, an escalation occurs.
Result:
a) The employee gains access to the resource;
b) The employee is refused.
Certification
Scenario: Once a month, the owner of the resource certifies the list of those who have access to the resource. For each member of the list, he prolongs or terminates access.
Result: Certification has been carried out, only employees confirmed by the owner have access to the resource.
Vacation
Scenario: Access for an employee on vacation should be automatically terminated during his absence. Terminating access does not require manual action.
Result: An employee does not have access to company systems during the holidays.
Dismissal
Scenario: The employee must have canceled access to all systems of the enterprise no later than n minutes after the initiation of the process by the manager on the web portal.
Результат: Сотрудник не имеет доступ к системам компании.
Разделение полномочий
Сценарий: Руководитель назначает сотруднику роль, которая не совместима с уже имеющимися ролями. Сотрудник не может совмещать взаимоисключающие роли.
Результат: Система отказывает в изменении и фиксирует нарушение политики.
Сброс пароля
Сценарий: Сотрудник забыл пароль.
Он заходит на веб-сайт, где, ответив на вопросы системы, инициирует сброс пароля и получает новый пароль в виде СМС. Новый пароль автоматически должен быть синхронизирован в подключенные системы.
Результат: Сотрудник получает новый пароль, которым может пользоваться во всех системах, где у него есть доступ.
Это первая часть статьи, будет продолжение...
Автор: Александр Цветков, инженер Dell Software
