How to protect data on mobile employees
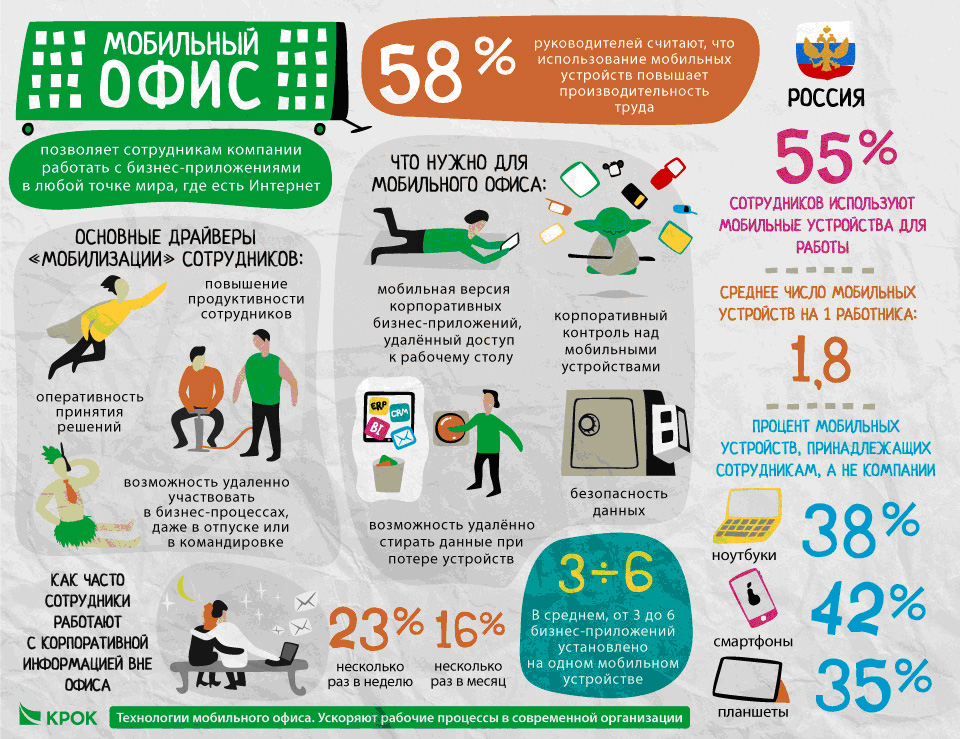
Mobile office is cool. You can access working applications and documents from your tablet or smartphone. For those who work on the road or on business trips, this saves time, who often "in the field" is simply necessary, and those who are in the office are more than convenient.
True, from the point of view of security, every smartphone or tablet is a hole in an information security device the size of a mining truck. Therefore, for all this to work, you need to build a process for managing mobile devices of employees. Both personal and secured at the corporate level. And there are solutions for this, including “out of the box”.
After we say that it is possible, for example, to set a policy for disconnecting a smartphone’s camera in a protected area, many people simply start to be happy.
How does it all start?
Most often, the customer has some basic things such as separation of corporate mail and personal, your server and certificates, for example. Sometimes there are their own applications such as viewing cameras on objects (for employees) or a secure browser with access to the internal network of the enterprise, regardless of the location of the device, and so on. But all this is fragmented and not integrated into the system. In the West, MDM solutions ( Mobile Device Management ) have been developed for a long time and are well known to everyone, but we have full implementations if several dozens across the country are good. And few people understand exactly what is needed: the most common case is when the security guards say "it is necessary", and the rest try to find a solution that will also be convenient.
What can be done at all?
MDM - Mobile Device Management - is the management, directly, of the device itself, that is, the parameters of the hardware. Here you can set Wi-Fi settings, prohibit the use of the camera, receive data on the location of the device, configure VPN, deliver certificates and so on. The employee changed the piece of iron - they rolled the same settings, and he continues to work pleased, because spared from frequent visits to the "sysadmin den" in order to make the new piece of iron work.
There is software - MAM - Mobile Application Management. This is the next level, because settings are already set at the application level (implied - corporate). Here, for example, you can open corporate mail, copy text. And you can’t insert it into an unincorporated application. And the attachment can only be opened in the application authorized for this. And you can’t take screenshots. There are almost no pure MDMs in practice, there is always at least a partial MAM functionality.
In order to implement the management of corporate applications, containers are made to separate corporate data from user data. For example, in order to simply take and make the corporate part a frozen certificate revocation upon dismissal. The main question is whether there will be a media platform that will act as a gateway. If you just need control, there are dozens of solutions. If you need a system that will provide data exchange between heterogeneous hardware and the OS, you need a single platform that will prepare data and channels for each specific device.
All together is an EMM system (Enterprise Mobility Management). There are only a few on the Russian market.
How is this being implemented?
Most often - from security. Let me quote from the latest project for the Aviadvigatel design bureau (they make engines for airplanes, gas turbine units for energy and gas pumping, and supply gas turbine power plants). In general, a large important facility. The state employs 2,500 people. The cost of information from such organizations is higher than the cost of protecting it. The task was quite simple - the emphasis was on ensuring that employees did not take out the data. The solution is minimalistic, without a media platform or complex policies. Simple management and control. And a remote wipe. Plus VPN, remote updates, data protection in open communication channels. Here:
“CROC specialists used a comprehensive solution for implementing BYOD security policy in our Aviadvigatel OJSC: an MDM system that allows you to centrally manage mobile devices, and Check Point's SSL VPN subsystem - provides secure access to the company's internal information resources.
“Thanks to the integration of the two solutions in Aviadvigatel, the access rights of users to various information resources of the enterprise are differentiated and data confidentiality is ensured when they are transmitted over open communication channels,” says Anton Razumov, head of the group of security consultants at Check Point Software Technologies. “It is important that as a result of the introduction of the system, it was possible to ensure the safety of information on mobile devices and introduce a centralized distribution of software and updates.”
If something more complicated were needed, it would be worth looking in the direction of Citrix's XenMobile. This is a complete EMM solution - remote control of devices, and geolocation, setting access policies when moving an employee from one branch to another, the ability to isolate applications from each other at a logical level, auto-configurators, and so on. We are now implementing this thing at another facility, but so far at the testing stage in the department of 250 people.
And one more question that may be interesting - how do corporate applications end up on employees' mobile and tablets? It's simple - they take them from the store, as they used to. Just not having a corporate account you can’t get access to them.
This is how the applications look in the corporate store:

And this is the launch pad of corporate applications for their aggregation in one place:

At the same time, for example, you can’t force the application to be delivered to the user; in any case, he must click the OK button. But everything is going to reduce the dependence on the user's decision. For example, innovations for device management and data control in the corporate segment in IOS 7 - policies have already appeared for restricting access to data within corporate and personal applications, secure tunnels to the enterprise network at the application level, and not at the device level. EMM vendors actively support such initiatives and quickly integrate new functionality into their solutions, often expanding it.
The most common tasks
If not to concern safety - then these are documents , BPM and PPM. The application allows you to work together on documents, send them in a chain, sign directly from the phone.
In the workflow, push notifications about documents that need to be signed, or payments that need to be agreed, look especially beautiful. The speed of bookkeeping increases in places by an order of magnitude.

Here, for example, is a screenshot of a cashless payment order form that comes in charge of approval at our CROC. It can be seen that you can confirm or reject the application in one click.
You can set tasks remotely. Application versions of PPM (Project Portfolio Management) are popular - managers set tasks outside the office, and executors report remotely. Another situation is insurance, which get access to knowledge bases directly from tablets when talking with a specific client. Logisticians are also very fond of keeping abreast of online deliveries, it is also important for them to make the right corporate applications, which means that there is a need for MDM.
Sometimes MRO systems (Maintenance and Repair) are used, and, for example, when going around the equipment, all important information will be immediately entered into the system. Here, however, there is a nuance - we need special mobile devices, an ordinary iPad in the workshop will live for two or three days, no more.
Mentality features
In the West, customers tend to make the most of the built-in capabilities of the system. At our place, people are simply not ready to put up with what they need, to seriously adjust their business to the platform, and they are redoing it. The result - a ready-made mobile client for CRM, for example, is no longer suitable, it has to be finished. The second great feature is that sometimes it’s easier to pick up phones at the entrance than to set security policies. But this is not a question for us.
All. Ready to answer your questions. If you suddenly need something in a personal type of pricing for a specific project - write to KShogenov@croc.ru .
