New Ransomvar asks for bitcoins
An animal called CryptoLocker surfaced on Reddit and in the news on Ars Technique .
The target audience of the beast - machines from XP to 7 64-bit. The malware spreads in email attachments and is not detected immediately by antiviruses (Reddit tested on MSE, Trend Micro WFBS, Eset, and Kaspersky). Victims of the Zeus botnet also received this virus through push.
Virustotal scan
The malware uses a public 2048-bit RSA key and takes a private key from the C&C server to encrypt documents in alphabetical order on the disk, as well as on all shared network folders where it has write access (for many network backups were encrypted). When activated, the virus creates encrypted files that fall under the mask: * .odt, * .ods, * .odp, * .odm, * .odc, * .odb, * .doc, * .docx, * .docm, * .wps, * .xls, * .xlsx, * .xlsm, * .xlsb, * .xlk, * .ppt, * .pptx, * .pptm, * .mdb, * .accdb, * .pst, * .dwg, *. dxf, * .dxg, * .wpd, * .rtf, * .wb2, * .mdf, * .dbf, * .psd, * .pdd, * .eps, * .ai, * .indd, * .cdr, ????????. jpg, ????????. jpe, img _ *. jpg, * .dng, * .3fr, * .arw, * .srf, * .sr2, * .bay , * .crw, * .cr2, * .dcr, * .kdc, * .erf, * .mef, * .mrw, * .nef, * .nrw, * .orf, * .raf, * .raw, * .rwl, * .rw2, * .r3d, * .ptx, * .pef, * .srw, * .x3f, * .der, * .cer, * .crt, * .pem, * .pfx, * .p12 , * .p7b, * .p7c, * .pdf, *.
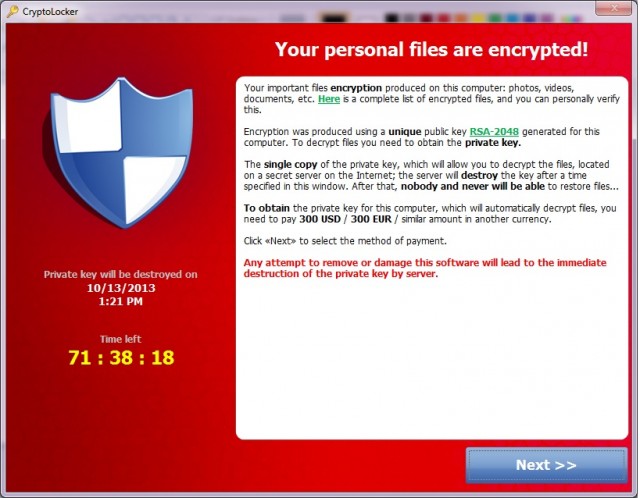
Having finished his dark business or disconnected from the Internet, CryptoLocker displays a window similar to what you see above and asks for $ 300 or 2BTC for a certain account, for decrypting the data. For everything about everything, the victim is given 72 hours (although the timer can be tricked through the BIOS), after which the malware disappears. Also, at the moment, many providers have already blocked the C&C server, and therefore some victims will not even be able to redeem their files.
From a translator: I want to say a lot of obscene things about the fact that the 21st century is in the yard and that it’s time to stop opening executables in attachments, but I won’t. Make cold backups, waving.
