Secretive Fiber Connection: Techniques and Precautions
- Transfer
Articles on listening to optical fiber are quite rare due to the specific nature of this kind of communication. As the cost of equipment and the cost of organizing communication channels based on fiber optics become cheaper, they have long been used in commercial practice. IT security professionals who are responsible for communication security issues should be aware of the main sources of threats and countermeasures. This article is a translation of a scientific paper published in the materials of the conference HONET (High Capacity Optical Networks and Enabling Technologies) in 2012. It was possible to find a full-text author's preprint on the network dated in the fall of 2011, which, although it contains some errors (the authors are not original native English speakers), nevertheless describe the problems quite well.
M. Zafar Iqbal, Habib Fathalla, Nezih Belhaj
MZ IQBAL, H FATHALLAH, N BELHADJ. 2011. Optical Fiber Tapping: Methods and Precautions. High Capacity Optical Networks and Enabling Technologies (HONET).
Communication using optical fiber is far from being as secure as is commonly believed. There are a number of well-known methods used to extract or insert information into the optical channel and avoid connecting detection. Several incidents were previously reported in which a successful connection was difficult to detect. In this paper, we consider a number of well-known methods of connecting to optical fiber, present a report on the simulation of the optical characteristics of the fiber to which the connection is made by the bend method, and also a proof of concept in the form of a physical experiment. Diagrams of various scenarios are also presented, where an attacker with the necessary resources and using existing technologies can compromise the security of the optical communication channel.
This article is based on work supported by the Royal Air Force of the Kingdom of Saudi Arabia.
M. Zafar Iqbal works at the Prince Sultan Advanced Technology Research Institute (ziqbal@ksu.edu.sa)
Habib Fathalla - Assistant Professor (Assistant Professor) King Saud University (hfathallah@ksu.edi.sa)
Nezih Belhaj - Postdoctoral Researcher Univeriteta Liverwave nbelhadj@gel.ulaval.ca)
In contrast to the general idea, the optical fiber essentially does not have protection against third-party connections and listening. Currently, a huge amount of critical and sensitive information is transmitted through optical communication channels, and there is a risk that it can fall into the hands of certain people who have the necessary resources and equipment.
Fiber tapping is a process in which the security of an optical channel is compromised by the insertion or extraction of light information. Fiber connection can be intrusive or non-intrusive. The first method requires cutting the fiber and connecting it to an intermediate device to retrieve information, while using the second method, the connection is performed without disrupting the data flow and interrupting the service. Non-intrusive technologies and this article will be devoted.
Currently, only a few recorded cases of connection to the optical fiber are reported. This is associated with great difficulties in finding the connection point, while the actual connection is quite simple. Here is a list of the main incidents:
In the following sections, we will provide a brief overview of unauthorized connection methods [4]. Then we will present a numerical representation of the signal loss during fiber bending, accompanied by a report on the physical demonstration of a prototype device for connecting to an optical fiber developed in our laboratory. Here we will explain the prototype device, the hardware and software used for this. We will also discuss possible connection scenarios in real conditions and discuss what resources are needed to achieve these goals. As a result, we will offer several methods for protecting optical channels against connections.
With this connection method, the cable is disassembled to fiber. This method is based on the principle of the propagation of light through a fiber through total internal reflection. To achieve this method, the angle of incidence of light on the transition between the actual core of the fiber and its cladding should be greater than the critical angle of total internal reflection .
Otherwise, part of the light will be emitted through the shell of the nucleus. The critical angle value is a function of the reflection indices of the core and its shell and is represented by the following expression:
θ c = cos -1 (μ cladding / μ core ), and μ cladding <μ core ;
Where θc is the critical angle, μ cladding is the refractive index of the shell, μ core is the refractive index of the core
When the fiber is bent, it bends so that the reflection angle becomes less than critical, and light begins to penetrate the shell. There are
obviously two types of bends:
The application of external force leads to a sharp, but at the same time microscopic curvature of the surface, leading to axial displacements of several microns and spatial displacement of the wavelength by several millimeters (Fig. 1). Light penetrates through the defect, and it can be used to read information.
Figure 1: Microbend
For each type of fiber there is a minimum allowable bending radius. This property can also be used to retrieve information. If the fiber is bent with a smaller radius, then a light transmission is possible (Fig. 2), sufficient for information retrieval. Typically, the minimum bending radius of a single-mode fiber is 6.5-7.5 cm, with the exception of a special type of fiber. Multimode fiber can be bent up to 3.8 cm.
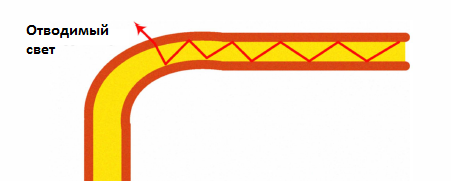
Figure 2. Macrobending
The optical fiber is inserted into the splitter, which diverts part of the optical signal. This method is intrusive because it requires cutting the fiber, which will trigger an alarm. However, an undetected connection of this type can work for years.
This method is used to intercept the signal from the source fiber to the receiver fiber by carefully polishing the shells to the surface of the core and then combining them. This allows some of the signal to penetrate into the second fiber. This method is difficult to perform in the field.
A V-shaped cut is a special recess in the fiber sheath close to the core, made in such a way that the angle between the light propagating in the fiber and the projection of the V-cut is more than critical. This causes a total internal reflection, in which part of the light will leave the main fiber through the shell and the V-shaped notch.
A Bragg grating is created on the fiber core, with its help reflection of a part of the signal from the fiber is achieved. This is achieved by superposition and interference of UV rays created by a laser with UV excitation.
To accurately estimate the loss in bending of an SMF-28 type optical fiber, the Maxwell full-vector frequency solver is used, based on the high-order finite element method and allowing the adaptation of boundary conditions — a stretching perfectly matched layer. Vector calculations of propagation constants and electric fields of modes in curved waveguides are obtained. Bending loss is calculated based on the imaginary part of the propagation constant of the fundamental mode. The total loss is obtained by adding the loss of the orthogonal and base mode. The results obtained by this method are quite accurate and were verified in [5].
For SMF-28 fiber, core radius and refractive index are respectively.
r c = 4.15 μm and n c = 1.4493
In the shell, they are respectively equal:
r cl = 62.25 μm and n cl = 1.444.
The refractive index of air is 1.
The bending radius ρ is taken along the x axis, the mode is polarized along the y axis, and the propagation is along the z axis, as shown in Figure 3.
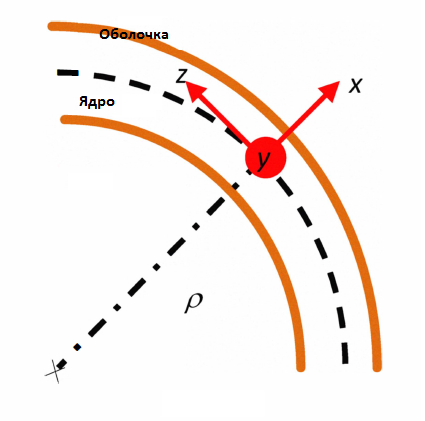
Figure 3
Figure 4 represents the bending loss expressed in numbers as a function of the bending radius of a meter-long fiber. A logarithmic dependence of the losses with respect to the bending radius is observed. For small bending radii (ρ <10 mm), the loss exceeds 40 dB / m. For ordinary bending radii (ρ> 15 mm), losses are less than 1 dB / m.

Figure 4. Numerical estimation of bending loss as a function of bending radius.
The full listening operation can be implemented using the following steps:
The experiment involved transmitting a digital video signal via optical Ethernet from one computer to another. The connected fiber was cut to the sheath and placed in an optical coupler, where the fiber bends, causing a certain amount of light to emit, which violates the principle of total internal reflection. This device directs the captured light to a unidirectional Ethernet converter. Further, Ethernet frames are processed and the video stream on the third PC is reconstructed from them. For stream transfer and playback, a VLC player was used. The WireShark protocol analyzer was used to capture packets, and Chaosreader software was used to reconstruct the video from the captured packets.
The software and hardware are connected as in Figure 5. The cut fiber passes from the video source to the receiver through the clamp of the maker. A part of the light is diverted in the clip and enters a unidirectional media converter that reads Ethernet frames, which are then transmitted to the third PC on which WireShark is installed. The protocol analyzer converts Ethernet frames and extracts information such as the MAC address of the source and receiver. It also processes the contents of the frames and extracts IP packets from it. Information received from packets includes IP addresses, signaling protocol messages, and overhead bits.

Figure 5. Experimental design for bending to a fiber.
Packets collected in this way are saved in the pcap (packet capture) file format. The file is then processed by Chaosreader software, which reconstructs the original files and creates an index of the reconstructed files. To detect our captured video, we look in the directory and look for * .DAT files of large size. Then this file opens in the VLC player and shows the intercepted part of the video stream.
In addition to playing video, the experimental system described here can be used to perform a number of tasks for intercepting information, such as information for attacking IP addresses, stealing passwords, listening to VoIP conversations, reconstructing email messages using free, commercial or homemade software.
The experiment described here was performed using Ethernet components, due to their greatest availability. However, some scenarios that are possible in real life may well look like this:
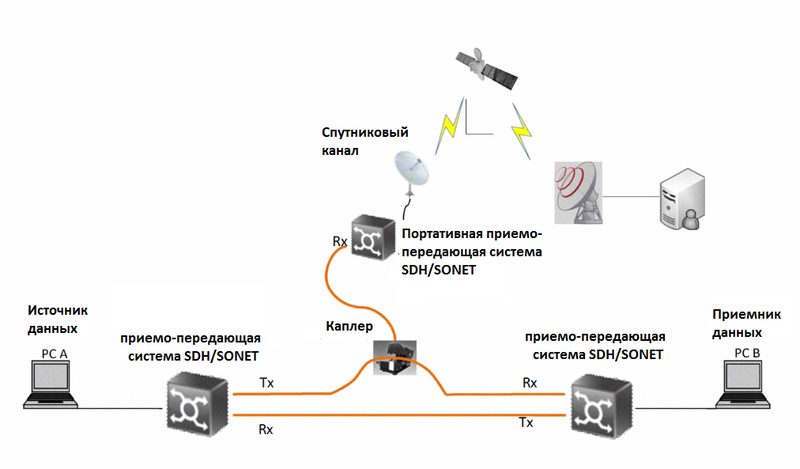
Figure 6 Connection scenario with remote processing.
Valuable information can be obtained from data transmission networks such as SDH and SONET, the two main standards for transmitting data over fiber through trunk communication channels and metro networks.
Information from high-speed networks is quite difficult to store and process, but high-tech SDH protocol analyzers are available on the market that can be used to obtain low-level source signals [6]. This partly simplifies the possible difficulties associated with the data transfer rate. Such devices can subsequently be modified to receive various types of traffic passing through the network. For example, you can retrieve an ethernet stream that is mapped to some stream of a VC4 container.
There are two important incentives for remote processing:
Using imagination, you can easily complete all the necessary scenarios for working with remote data. For example:
1) Using wireless internet. When using Wi-Fi, the listening computer may be in another room or van, outside the building where the connection is established. An expert can work in relative safety with the ability to access all resources.
2) Use of a micro-frequency or satellite channel. Our experimental scheme was modified and Ethernet traffic was redirected to the directional satellite channel (Fig. 6).
3) Insertion of the signal. Using the scattering method described earlier, it is theoretically possible to create a device that can transmit the signal inside the fiber using modified coupling
technology. You can develop technologies for interfering with the fiber without breaking the connection or even introducing malicious information .
There are three main categories of methods that prevent or minimize the impact of extraneous connections:
Production of optical fiber with additional fibers, through which a special monitoring signal is transmitted. Using this method will increase the cost of the cable, but any attempt to bend the cable causes a loss of the monitoring signal, and triggers an alarm [7].
Another method is to integrate the electrical conductors into the cable, and if the cable sheath is broken, the capacitance between the electrical conductors changes and this can be used to trigger an alarm.
This method is applicable to a multimode fiber in which attenuation is a function of the mode in which light propagates. The connection affects certain modes, but also affects other modes. This leads to a redistribution of energy from conducting modes to non-conducting, which changes the ratio of energy in the fiber core and its sheath. A change in the energy in the modes can be detected on the receiving side by an appropriate measurement, which will be the information for deciding whether there is a connection to the cable or not [8].
The fiber can monitor the level of optically significant power. In the event that it differs from the set value, an alarm is triggered. However, this requires appropriate coding of the signal, so that a constant signal level is present in the fiber, independent of the presence of the transmitted information [8].
Since the fiber connection takes part of the optical signal, optical reflectometers can be used to detect connections. With their help, you can set the distance along the path at which a drop in the signal level is detected (Fig. 7) [8]

Figure 7. Search for connections on the optical path using an optical reflectometer
Pilot tones pass through the fiber as well as communication data. They are used to detect transmission interruptions. Pilot tones can be used to detect attacks associated with jamming, but if the carrier wave frequencies of the pilot tones are not affected, then this method is not effective in detecting such attacks. The presence of a connection can only be judged by the significant degradation of the signal level of the pilot tone [8]
These types of fiber, commonly referred to as low loss fiber and strong bend radius, protect the data network by limiting the high loss that occurs when a fiber is punctured or bent. In addition, factors such as stretching, twisting and other physical manipulations of the fiber become less damaging to the light flux. There are also other types of fiber based on other production technologies [9].
Although encryption does not interfere with the connection to the fiber, it makes the stolen information of little use for attackers. Encryption is usually classified into levels 2 and 3.
An example of third-level encryption is IPSec. It is implemented on the user side, so this causes certain delays in processing. The protocol rises at the beginning of the session and the overall implementation can be very difficult if a large number of network elements are involved. Consider, for example, the development of multimedia subsystems. At initial development, the connection between the various nodes and elements is insecure. Much later, IPSec was built into the original design, since lower-level technologies did not offer any encryption at all.
Second level encryption frees third level elements from any burden of information encryption. One of the possible sources of second level encryption is optical CDMA, which is considered relatively safe [10-12]. This assumption is mainly based on brute force decryption methods and overlooks more advanced methods. The likelihood of successfully intercepting data is a function of several parameters, including the signal-to-noise ratio, and fractionation of the available system capacity. It is pointed out in [12] that increasing the code complexity can increase the signal-to-noise ratio required for an attacker to “break” the encoding by only a few dB, while processing less than 100 bits from an attacker can reduce the signal-to-noise ratio by 12 dB
The authors thank the Prince Sultan Advanced Technology Research Institute for providing its resources and performing the experimental part of the work.
Connecting to fiber is a very tangible threat to national security interests, financial institutions, as well as personal privacy and freedoms. After connecting, the information obtained can be used in many ways, depending on the motivation of the attacker and his technical capabilities. In this paper, we presented the concept both in the form of a simulation and in the form of a physical experiment, using the connection through the 'bend connection' and also demonstrated the possibility of the existence of different scenarios that can be performed using available technologies. In addition to obtaining information from optical fiber, there are a number of methods that allow you to insert information into it, as in the case of separation on inhomogeneous waves and achieve jamming or throwing in incorrect information.
Secretive Fiber Connection: Techniques and Precautions
M. Zafar Iqbal, Habib Fathalla, Nezih Belhaj
MZ IQBAL, H FATHALLAH, N BELHADJ. 2011. Optical Fiber Tapping: Methods and Precautions. High Capacity Optical Networks and Enabling Technologies (HONET).
annotation
Communication using optical fiber is far from being as secure as is commonly believed. There are a number of well-known methods used to extract or insert information into the optical channel and avoid connecting detection. Several incidents were previously reported in which a successful connection was difficult to detect. In this paper, we consider a number of well-known methods of connecting to optical fiber, present a report on the simulation of the optical characteristics of the fiber to which the connection is made by the bend method, and also a proof of concept in the form of a physical experiment. Diagrams of various scenarios are also presented, where an attacker with the necessary resources and using existing technologies can compromise the security of the optical communication channel.
This article is based on work supported by the Royal Air Force of the Kingdom of Saudi Arabia.
M. Zafar Iqbal works at the Prince Sultan Advanced Technology Research Institute (ziqbal@ksu.edu.sa)
Habib Fathalla - Assistant Professor (Assistant Professor) King Saud University (hfathallah@ksu.edi.sa)
Nezih Belhaj - Postdoctoral Researcher Univeriteta Liverwave nbelhadj@gel.ulaval.ca)
I. INTRODUCTION
In contrast to the general idea, the optical fiber essentially does not have protection against third-party connections and listening. Currently, a huge amount of critical and sensitive information is transmitted through optical communication channels, and there is a risk that it can fall into the hands of certain people who have the necessary resources and equipment.
Fiber tapping is a process in which the security of an optical channel is compromised by the insertion or extraction of light information. Fiber connection can be intrusive or non-intrusive. The first method requires cutting the fiber and connecting it to an intermediate device to retrieve information, while using the second method, the connection is performed without disrupting the data flow and interrupting the service. Non-intrusive technologies and this article will be devoted.
Currently, only a few recorded cases of connection to the optical fiber are reported. This is associated with great difficulties in finding the connection point, while the actual connection is quite simple. Here is a list of the main incidents:
- 2000, At Frankfurt Airport, Germany, a connection was found to the three main lines of Deutsche Telekom [1].
- 2003, a wiretap was discovered on a Verizone optical network [1].
- 2005, the USS Jimmy Carter submarine was specially upgraded to install unauthorized connections to submarine cables [2], [3] ( Separate post on the hub - USS Jimmy Carter submarine, its special tasks and submarine optical cables ).
In the following sections, we will provide a brief overview of unauthorized connection methods [4]. Then we will present a numerical representation of the signal loss during fiber bending, accompanied by a report on the physical demonstration of a prototype device for connecting to an optical fiber developed in our laboratory. Here we will explain the prototype device, the hardware and software used for this. We will also discuss possible connection scenarios in real conditions and discuss what resources are needed to achieve these goals. As a result, we will offer several methods for protecting optical channels against connections.
II. FIBER OPTIC CONNECTION METHODS
A. Fiber bending
With this connection method, the cable is disassembled to fiber. This method is based on the principle of the propagation of light through a fiber through total internal reflection. To achieve this method, the angle of incidence of light on the transition between the actual core of the fiber and its cladding should be greater than the critical angle of total internal reflection .
Otherwise, part of the light will be emitted through the shell of the nucleus. The critical angle value is a function of the reflection indices of the core and its shell and is represented by the following expression:
θ c = cos -1 (μ cladding / μ core ), and μ cladding <μ core ;
Where θc is the critical angle, μ cladding is the refractive index of the shell, μ core is the refractive index of the core
When the fiber is bent, it bends so that the reflection angle becomes less than critical, and light begins to penetrate the shell. There are
obviously two types of bends:
1) Microbend
The application of external force leads to a sharp, but at the same time microscopic curvature of the surface, leading to axial displacements of several microns and spatial displacement of the wavelength by several millimeters (Fig. 1). Light penetrates through the defect, and it can be used to read information.
Figure 1: Microbend
2) macrobend
For each type of fiber there is a minimum allowable bending radius. This property can also be used to retrieve information. If the fiber is bent with a smaller radius, then a light transmission is possible (Fig. 2), sufficient for information retrieval. Typically, the minimum bending radius of a single-mode fiber is 6.5-7.5 cm, with the exception of a special type of fiber. Multimode fiber can be bent up to 3.8 cm.
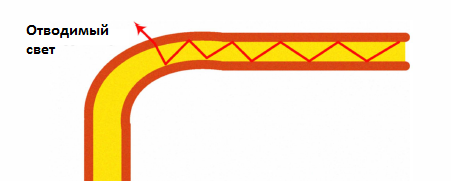
Figure 2. Macrobending
B. Optical Fission
The optical fiber is inserted into the splitter, which diverts part of the optical signal. This method is intrusive because it requires cutting the fiber, which will trigger an alarm. However, an undetected connection of this type can work for years.
C. Use of Inhomogeneous Waves (Evanescent Coupling)
This method is used to intercept the signal from the source fiber to the receiver fiber by carefully polishing the shells to the surface of the core and then combining them. This allows some of the signal to penetrate into the second fiber. This method is difficult to perform in the field.
D. V Groove Cut
A V-shaped cut is a special recess in the fiber sheath close to the core, made in such a way that the angle between the light propagating in the fiber and the projection of the V-cut is more than critical. This causes a total internal reflection, in which part of the light will leave the main fiber through the shell and the V-shaped notch.
E. Scattering
A Bragg grating is created on the fiber core, with its help reflection of a part of the signal from the fiber is achieved. This is achieved by superposition and interference of UV rays created by a laser with UV excitation.
III. MODELING
A. Methodology
To accurately estimate the loss in bending of an SMF-28 type optical fiber, the Maxwell full-vector frequency solver is used, based on the high-order finite element method and allowing the adaptation of boundary conditions — a stretching perfectly matched layer. Vector calculations of propagation constants and electric fields of modes in curved waveguides are obtained. Bending loss is calculated based on the imaginary part of the propagation constant of the fundamental mode. The total loss is obtained by adding the loss of the orthogonal and base mode. The results obtained by this method are quite accurate and were verified in [5].
B. Data for modeling.
For SMF-28 fiber, core radius and refractive index are respectively.
r c = 4.15 μm and n c = 1.4493
In the shell, they are respectively equal:
r cl = 62.25 μm and n cl = 1.444.
The refractive index of air is 1.
C. Calculation of power loss.
The bending radius ρ is taken along the x axis, the mode is polarized along the y axis, and the propagation is along the z axis, as shown in Figure 3.
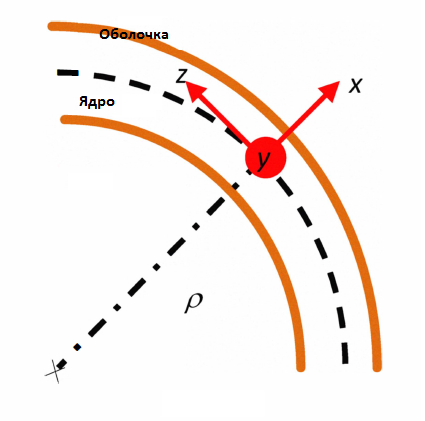
Figure 3
Figure 4 represents the bending loss expressed in numbers as a function of the bending radius of a meter-long fiber. A logarithmic dependence of the losses with respect to the bending radius is observed. For small bending radii (ρ <10 mm), the loss exceeds 40 dB / m. For ordinary bending radii (ρ> 15 mm), losses are less than 1 dB / m.

Figure 4. Numerical estimation of bending loss as a function of bending radius.
IV. FIBER OPERATION EXPERIMENT
A. Procedure for connecting to optical fiber.
The full listening operation can be implemented using the following steps:
- Receiving an optical signal from a fiber
- Signal detection.
- Transmission mechanism detection (protocol decoding)
- Software processing for detecting frames / packets and extracting the necessary data from them.
The experiment involved transmitting a digital video signal via optical Ethernet from one computer to another. The connected fiber was cut to the sheath and placed in an optical coupler, where the fiber bends, causing a certain amount of light to emit, which violates the principle of total internal reflection. This device directs the captured light to a unidirectional Ethernet converter. Further, Ethernet frames are processed and the video stream on the third PC is reconstructed from them. For stream transfer and playback, a VLC player was used. The WireShark protocol analyzer was used to capture packets, and Chaosreader software was used to reconstruct the video from the captured packets.
B. Procedure
The software and hardware are connected as in Figure 5. The cut fiber passes from the video source to the receiver through the clamp of the maker. A part of the light is diverted in the clip and enters a unidirectional media converter that reads Ethernet frames, which are then transmitted to the third PC on which WireShark is installed. The protocol analyzer converts Ethernet frames and extracts information such as the MAC address of the source and receiver. It also processes the contents of the frames and extracts IP packets from it. Information received from packets includes IP addresses, signaling protocol messages, and overhead bits.

Figure 5. Experimental design for bending to a fiber.
Packets collected in this way are saved in the pcap (packet capture) file format. The file is then processed by Chaosreader software, which reconstructs the original files and creates an index of the reconstructed files. To detect our captured video, we look in the directory and look for * .DAT files of large size. Then this file opens in the VLC player and shows the intercepted part of the video stream.
C. Possible actions when listening
In addition to playing video, the experimental system described here can be used to perform a number of tasks for intercepting information, such as information for attacking IP addresses, stealing passwords, listening to VoIP conversations, reconstructing email messages using free, commercial or homemade software.
V. FURTHER CONNECTION SCENARIOS.
The experiment described here was performed using Ethernet components, due to their greatest availability. However, some scenarios that are possible in real life may well look like this:
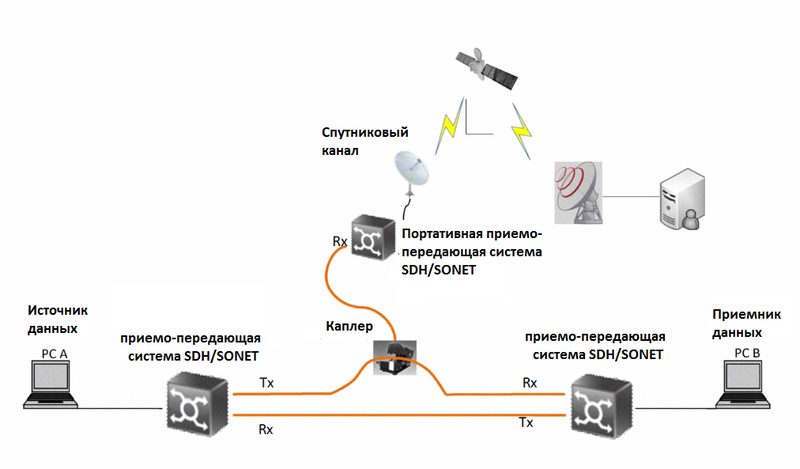
Figure 6 Connection scenario with remote processing.
A. Connection to a data network
.Valuable information can be obtained from data transmission networks such as SDH and SONET, the two main standards for transmitting data over fiber through trunk communication channels and metro networks.
Information from high-speed networks is quite difficult to store and process, but high-tech SDH protocol analyzers are available on the market that can be used to obtain low-level source signals [6]. This partly simplifies the possible difficulties associated with the data transfer rate. Such devices can subsequently be modified to receive various types of traffic passing through the network. For example, you can retrieve an ethernet stream that is mapped to some stream of a VC4 container.
Remote Processing Connection
There are two important incentives for remote processing:
- When connected to long-distance high-speed (several Gbit / s) communication channels, the role of storage becomes extremely important. Captured packets fill the disk extremely quickly.
- Engaging network experts to work in the field can be very costly. It is more convenient to organize their work in a remote processing center where there is any necessary equipment that is difficult to endure in the field.
Using imagination, you can easily complete all the necessary scenarios for working with remote data. For example:
1) Using wireless internet. When using Wi-Fi, the listening computer may be in another room or van, outside the building where the connection is established. An expert can work in relative safety with the ability to access all resources.
2) Use of a micro-frequency or satellite channel. Our experimental scheme was modified and Ethernet traffic was redirected to the directional satellite channel (Fig. 6).
3) Insertion of the signal. Using the scattering method described earlier, it is theoretically possible to create a device that can transmit the signal inside the fiber using modified coupling
technology. You can develop technologies for interfering with the fiber without breaking the connection or even introducing malicious information .
VI. PROTECTION AGAINST CONNECTIONS.
There are three main categories of methods that prevent or minimize the impact of extraneous connections:
A. Cable surveillance and monitoring.
1. Monitoring signals near the fiber.
Production of optical fiber with additional fibers, through which a special monitoring signal is transmitted. Using this method will increase the cost of the cable, but any attempt to bend the cable causes a loss of the monitoring signal, and triggers an alarm [7].
2) Electrical conductors
Another method is to integrate the electrical conductors into the cable, and if the cable sheath is broken, the capacitance between the electrical conductors changes and this can be used to trigger an alarm.
3) Power monitoring mod.
This method is applicable to a multimode fiber in which attenuation is a function of the mode in which light propagates. The connection affects certain modes, but also affects other modes. This leads to a redistribution of energy from conducting modes to non-conducting, which changes the ratio of energy in the fiber core and its sheath. A change in the energy in the modes can be detected on the receiving side by an appropriate measurement, which will be the information for deciding whether there is a connection to the cable or not [8].
4) Measurement of optically significant power
The fiber can monitor the level of optically significant power. In the event that it differs from the set value, an alarm is triggered. However, this requires appropriate coding of the signal, so that a constant signal level is present in the fiber, independent of the presence of the transmitted information [8].
5) Optical reflectometers
Since the fiber connection takes part of the optical signal, optical reflectometers can be used to detect connections. With their help, you can set the distance along the path at which a drop in the signal level is detected (Fig. 7) [8]

Figure 7. Search for connections on the optical path using an optical reflectometer
6) Methods using pilot tone:
Pilot tones pass through the fiber as well as communication data. They are used to detect transmission interruptions. Pilot tones can be used to detect attacks associated with jamming, but if the carrier wave frequencies of the pilot tones are not affected, then this method is not effective in detecting such attacks. The presence of a connection can only be judged by the significant degradation of the signal level of the pilot tone [8]
B. Strongly bending fiber.
These types of fiber, commonly referred to as low loss fiber and strong bend radius, protect the data network by limiting the high loss that occurs when a fiber is punctured or bent. In addition, factors such as stretching, twisting and other physical manipulations of the fiber become less damaging to the light flux. There are also other types of fiber based on other production technologies [9].
C. Encryption
Although encryption does not interfere with the connection to the fiber, it makes the stolen information of little use for attackers. Encryption is usually classified into levels 2 and 3.
1) Third level encryption
An example of third-level encryption is IPSec. It is implemented on the user side, so this causes certain delays in processing. The protocol rises at the beginning of the session and the overall implementation can be very difficult if a large number of network elements are involved. Consider, for example, the development of multimedia subsystems. At initial development, the connection between the various nodes and elements is insecure. Much later, IPSec was built into the original design, since lower-level technologies did not offer any encryption at all.
2) Second level encryption.
Second level encryption frees third level elements from any burden of information encryption. One of the possible sources of second level encryption is optical CDMA, which is considered relatively safe [10-12]. This assumption is mainly based on brute force decryption methods and overlooks more advanced methods. The likelihood of successfully intercepting data is a function of several parameters, including the signal-to-noise ratio, and fractionation of the available system capacity. It is pointed out in [12] that increasing the code complexity can increase the signal-to-noise ratio required for an attacker to “break” the encoding by only a few dB, while processing less than 100 bits from an attacker can reduce the signal-to-noise ratio by 12 dB
THANKS
The authors thank the Prince Sultan Advanced Technology Research Institute for providing its resources and performing the experimental part of the work.
VII. CONCLUSION
Connecting to fiber is a very tangible threat to national security interests, financial institutions, as well as personal privacy and freedoms. After connecting, the information obtained can be used in many ways, depending on the motivation of the attacker and his technical capabilities. In this paper, we presented the concept both in the form of a simulation and in the form of a physical experiment, using the connection through the 'bend connection' and also demonstrated the possibility of the existence of different scenarios that can be performed using available technologies. In addition to obtaining information from optical fiber, there are a number of methods that allow you to insert information into it, as in the case of separation on inhomogeneous waves and achieve jamming or throwing in incorrect information.
ССЫЛКИ
- Sandra Kay Miller, «Hacking at the Speed of Light », Security Solutions Magazine, April 2006
- Davis, USN, RADM John P.«USS Jimmy Carter (SSN-23): Expanding Future SSN Missions». Undersea Waifare, Fall 1999 Vol.2, No. I
- Optical Illusion by: Sandra Kay Miller Information security Issue: Nov 2006.
- Optical Network Security: Technical Analysis of Fiber Tapping Mechanisms and Methods for detection and Prevention, Keith Shaneman & Dr. Stuart Gray, IEEE Military Communications Conference 2004.
- R. Jedidi and R. Pierre, High-Order Finite-Element Methods for the Computation of Bending Loss in Optical Waveguides, lLT, Vol. 25, No. 9, pp. 2618-30, SEP 2007.
- FTB-8140 Transport Blazer — 40143 Gigabit SONETISDH Test Module, EXFO
- «Optical Fiber Design for Secure Tap Proof transmission», US Patent No. 6801700 B2, Oct. 5,2004.
- All Optical Networks (A ON), National Communication System, NCS TIB 00-7, August 2000
- DrakaElite, BendBright-Elite Fiber for Patch Cord, Draka Communications, July, 2010
- W. Ford, Computer Communications Security, Upper Saddle River, NJ: Prentice-Hall, 1994.
- DR Stinson, "Cryptography", Boca Raton, FL: CRC, 1995.
- N. Ferguson and 8. Schneier, Practical Cryptography, Indianapolis, IN: Wiley, 2003.
