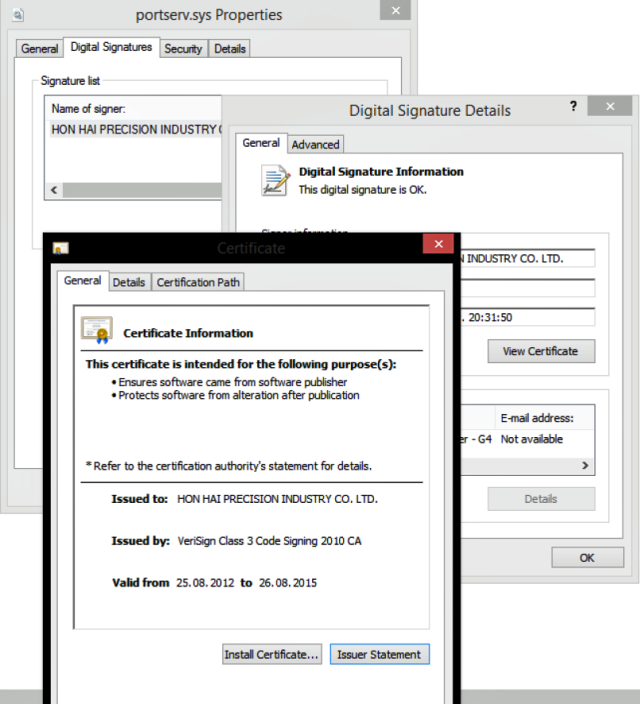
The attackers used stolen D-Link certificates in their password-stealing software

Recently it became known that a group of intruders took possession of valid certificates of D-Link, a well-known manufacturer of network equipment. In addition, certificates were stolen from another Taiwanese company. The obtained certificates were used to create software that steals the passwords of the victims ’accounts.
Certificates were needed in order for antivirus software to take malicious programs for quite legitimate software and not block them. And so it happened, because Microsoft Windows and MacOS, including many other operating systems, check the security of the software using the certificate with which it is signed. In the case of D-Link, the “trust level” of security software for such programs is quite high.
As for the intruders, they belong to the BlackTech faction. The second company, whose certificates have been taken away, is called Changing Information Technology. All this was told by an information security specialist from Eset. The attackers needed certificates to sign two elements of a single malware. One element is a remotely controlled backdoor, the second is “password transfer”.
Eset classifies malware as Plead. This software is used to conduct cyber spy actions in East Asia. Much has already been written about this malware. So, Japan Computer Emergency Response described Plead here , and Trend Micro here .
According to information security experts, the fact that the evil-minded people managed to steal certificates from two Taiwanese companies at once, and then create password-stealing software signed with legal certificates, testifies to the considerable experience of the hacker team that turned all this on.
Representatives of the company D-Link confirmed the existence of the problem. In an official postIt says that the certificates were stolen by “a very active group of cybercriminals.” The company also hurried to declare that its customers are not affected by theft. However, some of them may encounter problems - errors when trying to work with IP cameras using a browser. Now D-Link engineers are working on creating a firmware that solves the problem. Those users who work with mobile applications, do not face problems.
D-Link and Changing Information Technology have already revoked stolen certificates. However, until the update of the firmware of devices, browsers will report problem certificates and “legal” users, as mentioned above. In turn, attackers can create fake messages about problems with certificates, so that when a user clicks on an active button, they can transfer him to a phishing resource or invite him to download any “treatment” software. The company asks everyone to refrain from such proposals.
The technique used by the attackers is not at all new. Previously, many groups used it, but the most famous case can be called Stuxnet . For a long time, spyware remained unnoticed thanks to the use of RealTek and Jmicron certificates.
Theft of certificates to sign spyware is a more common technique for intruders than is commonly thought. The first case became known in 2003. Now there are even stores of certificates that someone leads, and someone buys. The goal is the same as that of the attackers from the BlackTech group - signing their software with a legitimate certificate.
One of these services has worked without problems since 2011. And if it became known about him, this does not mean at all that it will become known about other similar “commercial enterprises” in the near future. No, they will continue to work and will manifest themselves only by chance. And they are becoming more popular. The company Recorder Future has published a report, which states that the demand for stolen certificates of "white" security providersonly growing . In some cases, cybercriminals have access to accounts in companies that form certificates. And upon request they can create the necessary certificate “to order”.
