LinkedIn started using salt
LinkedIn has published an addendum to the security rules on the corporate blog : now the password hashes on the server will be stored with the addition of salt. LinkedIn employs good IT security experts who have been preparing the system upgrade for a long time so that the hashes are stored with salt. By the time of the leak, an upgrade had already been made, now work is underway on additional security levels.
The director of LinkedIn also emphasizes that the email addresses of the users were not indicated in the leaked database , and the FBI is already engaged in the search for attackers.
Meanwhile, since the leak, more than half of the passwords from the published database have been selected. For example, SophosLabs managed to pick up 3.5 million passwords, i.e. 60% of all unique hashes from a published LinkedIn file (out of 6.5 million hashes, only 5.8 million are unique).
Programs like John the Ripper allow brute-force dictionary processing with word addition and character addition / replacement, so long passwords like linkedinpassword or p455w0rd can be decrypted quite easily. Moreover, the program allows you to replenish the dictionary with the passwords found in the process, so after seven passages there was such a password as m0c.nideknil (from dictionary linkedin).
Example
1 pass. pwdlink from pwlink with the rule "add d to the third position"
2. pwd4link from pwdlink with the rule "insert 4 to the fourth position"
3. pwd4linked from pwd4link with the rule "add ed"
4. pw4linked from pwd4linked with the rule "remove the 3rd character"
5. pw4linkedin from pw4linked with the rule "add in"
6. mpw4linkedin from pw4linkedin with the rule "add m to the beginning"
7. mw4linkedin from mpw4linkedin with the rule "remove the second character"
8. smw4linkedin from mw4linkedin with the rule "add s to the beginning"
9. sw4linkedin from smw4linkedin with the rule "remove the second character"
10. lsw4linkedin from sw4linkedin with the rule "add l to the beginning"
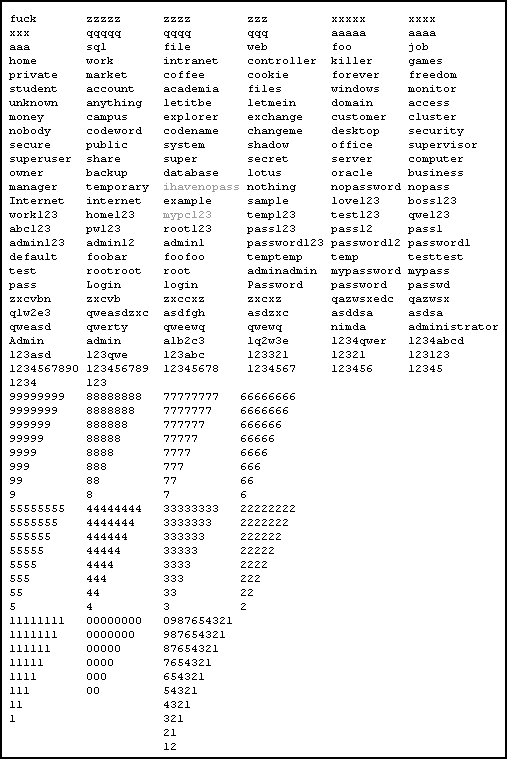
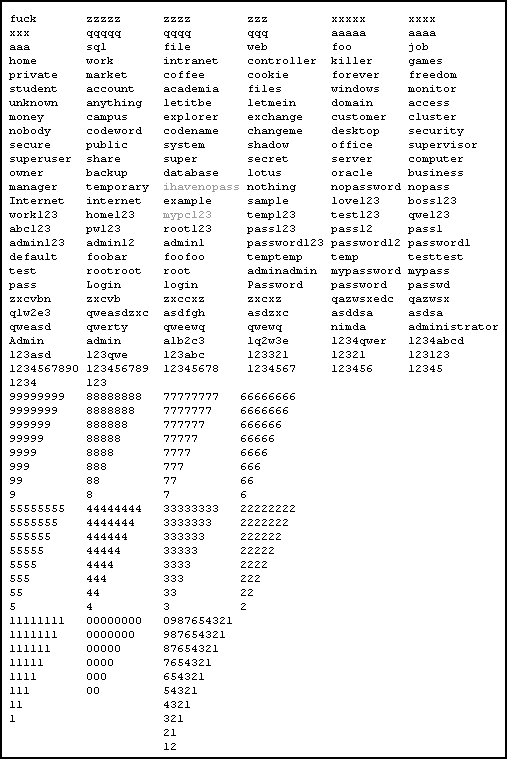
In SophosLabs, besides ordinary dictionaries, we also took a dictionary that used by the Conficker worm. Below is a list of passwords from the Conficker dictionary, all of them ended up in the LinkedIn database, except for two (mypc123 and ihavenopass).
See also the 30 most popular passwords stolen from LinkedIn .
The director of LinkedIn also emphasizes that the email addresses of the users were not indicated in the leaked database , and the FBI is already engaged in the search for attackers.
Meanwhile, since the leak, more than half of the passwords from the published database have been selected. For example, SophosLabs managed to pick up 3.5 million passwords, i.e. 60% of all unique hashes from a published LinkedIn file (out of 6.5 million hashes, only 5.8 million are unique).
Programs like John the Ripper allow brute-force dictionary processing with word addition and character addition / replacement, so long passwords like linkedinpassword or p455w0rd can be decrypted quite easily. Moreover, the program allows you to replenish the dictionary with the passwords found in the process, so after seven passages there was such a password as m0c.nideknil (from dictionary linkedin).
Example
1 pass. pwdlink from pwlink with the rule "add d to the third position"
2. pwd4link from pwdlink with the rule "insert 4 to the fourth position"
3. pwd4linked from pwd4link with the rule "add ed"
4. pw4linked from pwd4linked with the rule "remove the 3rd character"
5. pw4linkedin from pw4linked with the rule "add in"
6. mpw4linkedin from pw4linkedin with the rule "add m to the beginning"
7. mw4linkedin from mpw4linkedin with the rule "remove the second character"
8. smw4linkedin from mw4linkedin with the rule "add s to the beginning"
9. sw4linkedin from smw4linkedin with the rule "remove the second character"
10. lsw4linkedin from sw4linkedin with the rule "add l to the beginning"
In SophosLabs, besides ordinary dictionaries, we also took a dictionary that used by the Conficker worm. Below is a list of passwords from the Conficker dictionary, all of them ended up in the LinkedIn database, except for two (mypc123 and ihavenopass).
See also the 30 most popular passwords stolen from LinkedIn .
