The basics of biometrics
This article is to some extent a continuation of the past , and to some extent its prequel. Here I will talk about the basics of building any biometric system and about what remained behind the scenes of the last article, but was discussed in the comments. The emphasis is not on the biometric systems themselves, but on their principles and scope.
For those who have not read the article, or have already forgotten, I advise you to look at what FAR and FRR are, as these concepts will be used here.
Any authentication of a person is based on three traditional principles:
1) By property . Property may include a pass, a plastic card, a key or general civil documents.
2) By knowledge . Knowledge includes passwords, codes, or information (for example, mother’s maiden name).
3) According to biometric characteristics . I spoke in more detail about what biometric characteristics are in the previous article.
These three principles can be used individually or used in groups. This methodology gives rise to two main directions of biometrics.
Verification is the confirmation of a person’s identity through a biometric feature, where primary authentication was performed using one of the first two methods mentioned above. The simplest verifier is a border guard who verifies your face with your passport. Verification implies significantly greater system reliability. The probability that the system will miss an intruder that does not use the means of overcoming is equal to the FAR of the biometric method used. Even for the weakest biometric systems, this probability is negligible. The main disadvantages of verification are two points. First, a person needs to carry a document or remember the system password. There is always the problem of losing or forgetting information. Verification is also fundamentally impossible for stealth authentication.
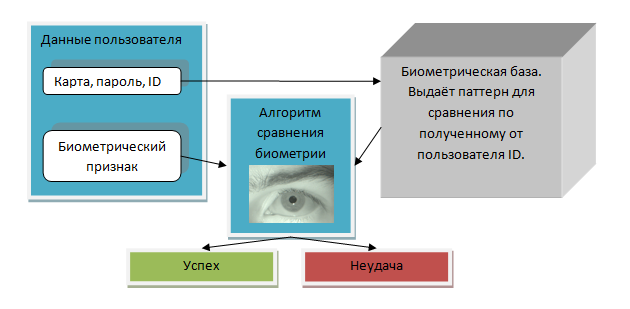
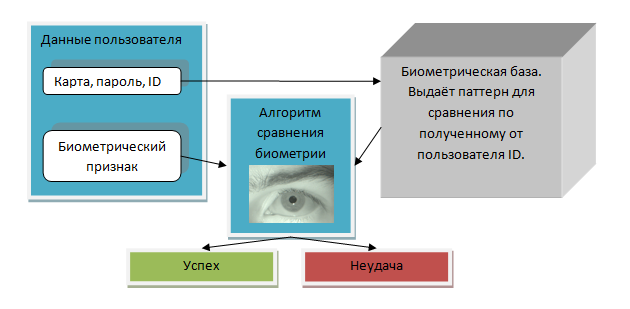
The operation of an access system based on biometric verification can be represented in the following way:
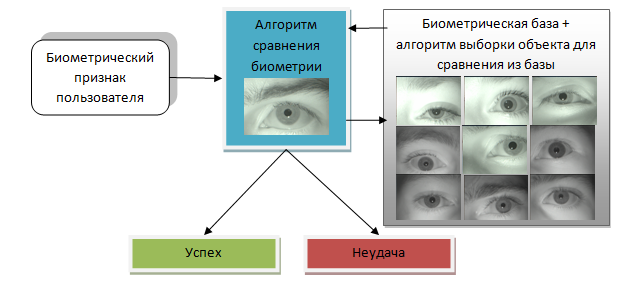
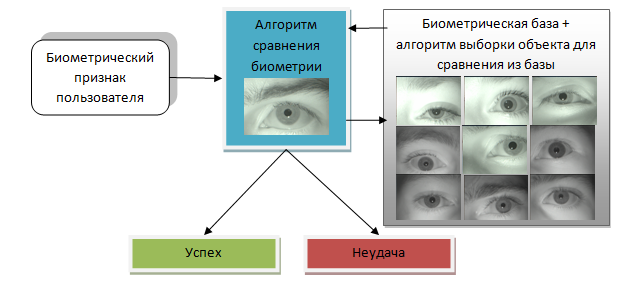
Biometric identification refers to the use of a biometric feature in which additional information is not required. Search for an object is carried out throughout the database and does not require a preliminary key. It is clear that the main disadvantage of this is that the more people in the database, the greater the likelihood of false access by an arbitrary person. In a previous article, assessments were made of the likelihood of such access in systems design. For example, fingerprint systems make it possible to contain a base of no more than 300 people, by the eyes no more than 3,000. Plus identification - all keys will always be with you, no passwords or cards are needed.
Unlike verification, identification can be secretive to humans. How is it possible and is it worth it to be afraid of? I’ll try to briefly describe the thoughts that exist among people involved in biometrics. In a previous article, this thought remained unfinished.
Consider technologies that can allow, at least in some cases, to covertly determine a person’s identity. Firstly, immediately it is necessary to discard all contact methods. Placing fingerprint scanners in door handles is not a good idea. They are noticeable, many do not touch pens, contact scanners get dirty, etc. Secondly, you can immediately discard methods where the maximum range is limited to 10-15 centimeters (for example, veins of the hands). Thirdly, all dynamic biometrics can be discarded, since FAR and FRR are too low there.
Only two technologies remain. These are technologies where cameras act as data scanners: face recognition (2D, 3D) and iris recognition.
The first of them, recognition by 2D faces, has already been repeatedly tried to implement (due to its simplicity), but all the time unsuccessfully. This is due to the low statistical parameters of the system. If the database of wanted persons contains only 100 people, then every 10 passers-by will be declared wanted. Even a policeman in the subway has much higher efficiency.
The following two technologies are very similar. For both, it is possible to use it far from a person, but both must have a sufficient amount of equipment. Both the 3D face scanner and the iris scanner can be placed in places where there are narrow passages. These are escalators, doors, stairs. An example of such a system is the system created by SRI International (now they have a dead site, but there is almost an analog from AOptix) I am not 100% sure that the system from SRI International is working, there are too many errors in the video, but there is a fundamental possibility of creation. The second system works, although the speed for the secretive system is too low there. 3D face scanners work approximately the same principle: detection in a narrow aisle. In the case of a 3D face and eye recognition, the reliability is quite high. If the base is 100 criminals, then only every 10,000 civilians will have to be checked, which is already quite effective.
A key feature of any hidden biometrics is that a person does not need to know about it. Insert lenses into the eyes, or change the shape of the face with several overlays can be imperceptible to others, but noticeable for the biometric system. For some reason, I have a suspicion that in the near future the demand for lenses that change the iris will increase significantly. In Britain, the demand for bandanas increased. And the events there are only the first signs of biometrics.
Any biometric system will consist of several elements. In some of the systems, individual elements are spliced, in some, they are spaced into different elements.

If the biometric system is used only on one passage, then it doesn’t matter whether the system is divided into parts or not. On the spot, you can add a person to the database and check it. If there are several walk-throughs, then it is irrational to store a separate database on each walk-through. Moreover, such a system is not dynamic: adding or removing users requires bypassing all scanners.
A biometric scanner is part of any biometric system without which it cannot exist. In some systems, a biometric scanner is just a video camera, and in some (for example, retinal scanners), it is a complex optical complex. The two main characteristics of a biometric scanner are its operating principle (contact, non-contact) and its speed (the number of people per minute that it can serve). For those biometric characteristics whose use has already become normal, the scanner can be purchased separately from the logical system. If the scanner is physically separated from the comparison algorithm and the base, then the scanner can perform initial processing of the obtained biometric characteristics (for example, for the eye, this is the selection of the iris). This action is performed in order so as not to overload the communication channel of the scanner and the main base. Also, in a scanner separate from the database, a data encryption system is usually built in to secure the transfer of biometric data.
These two parts of the biometric system usually live next door and often complement each other. For some biometric features, the comparison algorithm may perform optimized database searches (finger comparisons, face comparisons). And in some (eyes), for a complete comparison, in any case, he needs to go around the entire base.
The comparison algorithm has many characteristics. Its two main characteristics, FAR and FRR, largely determine the biometric system. It is also worth noting:
1) Speed. For some comparisons (eyes), the speed of operation can reach hundreds of thousands of comparisons per second on a regular computer. This speed is enough to meet any user needs without noticing the time delay. And for some systems (3D face), this is already a significant feature of the system, requiring a lot of computing power to maintain operating speed while increasing the base.
2) Convenience of work. In fact, the convenience of any system is largely determined by the ratio FAR, FRR. In the system, we can slightly change their value, so as to emphasize the side of speed or the side of reliability. Roughly speaking, we get something like this graph:
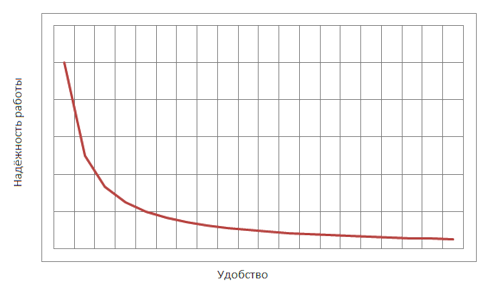
In case we want a high level of reliability, we choose a position in its left part. And if there are few users, then good indicators will be on the right side of the schedule, where there will be high characteristics of convenience, and hence high speed.
After comparison, the biometric system should give the results of the comparison to the governing bodies. Further it can be either the command “open the door” or the information “such-and-such-and-such came to work”. But what further to do with this information should be decided by the installers of the system. But here it’s not so simple, one must take into account the possibilities of attack:
Despite the fact that many biometric systems are equipped with algorithms that can determine the attack on them, this is not enough to be careless about security. The simplest attack on an identification system is multiple scanning. Suppose a situation: about a hundred people serve in the company. The attacker approaches the biometric pass system and is repeatedly scanned on it. Even for reliable systems, after a couple of thousand scans, it is possible to falsely identify and allow an attacker to enter an object. To avoid this, many systems track failed scans and block entry after 10-15 attempts. But in cases where the system cannot do this, this task rests with the user. Unfortunately, this is often forgotten.
The second way to attack a biometric system is to fake a scan object. If the system has anti-counterfeiting algorithms, it is important to respond to them correctly. Typically, these algorithms are also probabilistic and have their own FAR and FRR. So do not forget to keep track of the attack signals in time and send a guard.
In addition to attacking the system itself, it is possible to attack the system environment. Once we came across a funny situation in this country. Many integrators are not particularly worried about data transfer. For transmission, they use the standard Wiegand protocol . At the same time, they are not even encrypted in most cases, they do not even encrypt it. So it’s easier not to cheat the system, but to find the wire and send the key through it ...
I hope that my thoughts on what biometrics are and what they eat with them will help you someday. Or in order to put yourself such a system, or in order to deceive someone else's)
For those who have not read the article, or have already forgotten, I advise you to look at what FAR and FRR are, as these concepts will be used here.
General concepts
Any authentication of a person is based on three traditional principles:
1) By property . Property may include a pass, a plastic card, a key or general civil documents.
2) By knowledge . Knowledge includes passwords, codes, or information (for example, mother’s maiden name).
3) According to biometric characteristics . I spoke in more detail about what biometric characteristics are in the previous article.
These three principles can be used individually or used in groups. This methodology gives rise to two main directions of biometrics.
Verification
Verification is the confirmation of a person’s identity through a biometric feature, where primary authentication was performed using one of the first two methods mentioned above. The simplest verifier is a border guard who verifies your face with your passport. Verification implies significantly greater system reliability. The probability that the system will miss an intruder that does not use the means of overcoming is equal to the FAR of the biometric method used. Even for the weakest biometric systems, this probability is negligible. The main disadvantages of verification are two points. First, a person needs to carry a document or remember the system password. There is always the problem of losing or forgetting information. Verification is also fundamentally impossible for stealth authentication.
The operation of an access system based on biometric verification can be represented in the following way:
Identification
Biometric identification refers to the use of a biometric feature in which additional information is not required. Search for an object is carried out throughout the database and does not require a preliminary key. It is clear that the main disadvantage of this is that the more people in the database, the greater the likelihood of false access by an arbitrary person. In a previous article, assessments were made of the likelihood of such access in systems design. For example, fingerprint systems make it possible to contain a base of no more than 300 people, by the eyes no more than 3,000. Plus identification - all keys will always be with you, no passwords or cards are needed.
Secretive identification
Unlike verification, identification can be secretive to humans. How is it possible and is it worth it to be afraid of? I’ll try to briefly describe the thoughts that exist among people involved in biometrics. In a previous article, this thought remained unfinished.
Consider technologies that can allow, at least in some cases, to covertly determine a person’s identity. Firstly, immediately it is necessary to discard all contact methods. Placing fingerprint scanners in door handles is not a good idea. They are noticeable, many do not touch pens, contact scanners get dirty, etc. Secondly, you can immediately discard methods where the maximum range is limited to 10-15 centimeters (for example, veins of the hands). Thirdly, all dynamic biometrics can be discarded, since FAR and FRR are too low there.
Only two technologies remain. These are technologies where cameras act as data scanners: face recognition (2D, 3D) and iris recognition.
The first of them, recognition by 2D faces, has already been repeatedly tried to implement (due to its simplicity), but all the time unsuccessfully. This is due to the low statistical parameters of the system. If the database of wanted persons contains only 100 people, then every 10 passers-by will be declared wanted. Even a policeman in the subway has much higher efficiency.
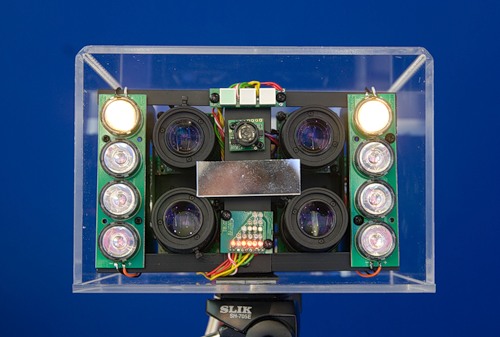
The following two technologies are very similar. For both, it is possible to use it far from a person, but both must have a sufficient amount of equipment. Both the 3D face scanner and the iris scanner can be placed in places where there are narrow passages. These are escalators, doors, stairs. An example of such a system is the system created by SRI International (now they have a dead site, but there is almost an analog from AOptix) I am not 100% sure that the system from SRI International is working, there are too many errors in the video, but there is a fundamental possibility of creation. The second system works, although the speed for the secretive system is too low there. 3D face scanners work approximately the same principle: detection in a narrow aisle. In the case of a 3D face and eye recognition, the reliability is quite high. If the base is 100 criminals, then only every 10,000 civilians will have to be checked, which is already quite effective.
A key feature of any hidden biometrics is that a person does not need to know about it. Insert lenses into the eyes, or change the shape of the face with several overlays can be imperceptible to others, but noticeable for the biometric system. For some reason, I have a suspicion that in the near future the demand for lenses that change the iris will increase significantly. In Britain, the demand for bandanas increased. And the events there are only the first signs of biometrics.
Model of a biometric access system and its parts
Any biometric system will consist of several elements. In some of the systems, individual elements are spliced, in some, they are spaced into different elements.

If the biometric system is used only on one passage, then it doesn’t matter whether the system is divided into parts or not. On the spot, you can add a person to the database and check it. If there are several walk-throughs, then it is irrational to store a separate database on each walk-through. Moreover, such a system is not dynamic: adding or removing users requires bypassing all scanners.
Biometric scanner
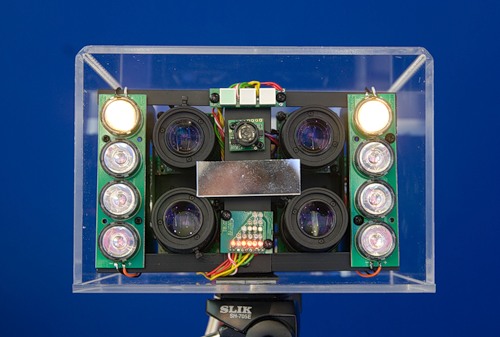
A biometric scanner is part of any biometric system without which it cannot exist. In some systems, a biometric scanner is just a video camera, and in some (for example, retinal scanners), it is a complex optical complex. The two main characteristics of a biometric scanner are its operating principle (contact, non-contact) and its speed (the number of people per minute that it can serve). For those biometric characteristics whose use has already become normal, the scanner can be purchased separately from the logical system. If the scanner is physically separated from the comparison algorithm and the base, then the scanner can perform initial processing of the obtained biometric characteristics (for example, for the eye, this is the selection of the iris). This action is performed in order so as not to overload the communication channel of the scanner and the main base. Also, in a scanner separate from the database, a data encryption system is usually built in to secure the transfer of biometric data.
Comparison Algorithm + Database
These two parts of the biometric system usually live next door and often complement each other. For some biometric features, the comparison algorithm may perform optimized database searches (finger comparisons, face comparisons). And in some (eyes), for a complete comparison, in any case, he needs to go around the entire base.
The comparison algorithm has many characteristics. Its two main characteristics, FAR and FRR, largely determine the biometric system. It is also worth noting:
1) Speed. For some comparisons (eyes), the speed of operation can reach hundreds of thousands of comparisons per second on a regular computer. This speed is enough to meet any user needs without noticing the time delay. And for some systems (3D face), this is already a significant feature of the system, requiring a lot of computing power to maintain operating speed while increasing the base.
2) Convenience of work. In fact, the convenience of any system is largely determined by the ratio FAR, FRR. In the system, we can slightly change their value, so as to emphasize the side of speed or the side of reliability. Roughly speaking, we get something like this graph:
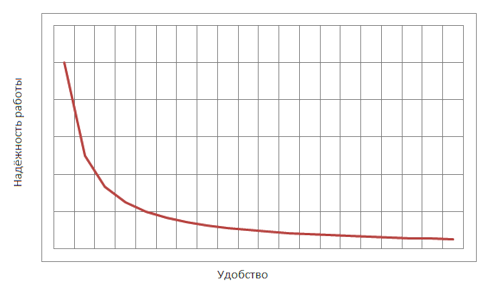
In case we want a high level of reliability, we choose a position in its left part. And if there are few users, then good indicators will be on the right side of the schedule, where there will be high characteristics of convenience, and hence high speed.
"Do something"
After comparison, the biometric system should give the results of the comparison to the governing bodies. Further it can be either the command “open the door” or the information “such-and-such-and-such came to work”. But what further to do with this information should be decided by the installers of the system. But here it’s not so simple, one must take into account the possibilities of attack:
Attack on a biometric system
Despite the fact that many biometric systems are equipped with algorithms that can determine the attack on them, this is not enough to be careless about security. The simplest attack on an identification system is multiple scanning. Suppose a situation: about a hundred people serve in the company. The attacker approaches the biometric pass system and is repeatedly scanned on it. Even for reliable systems, after a couple of thousand scans, it is possible to falsely identify and allow an attacker to enter an object. To avoid this, many systems track failed scans and block entry after 10-15 attempts. But in cases where the system cannot do this, this task rests with the user. Unfortunately, this is often forgotten.
The second way to attack a biometric system is to fake a scan object. If the system has anti-counterfeiting algorithms, it is important to respond to them correctly. Typically, these algorithms are also probabilistic and have their own FAR and FRR. So do not forget to keep track of the attack signals in time and send a guard.
In addition to attacking the system itself, it is possible to attack the system environment. Once we came across a funny situation in this country. Many integrators are not particularly worried about data transfer. For transmission, they use the standard Wiegand protocol . At the same time, they are not even encrypted in most cases, they do not even encrypt it. So it’s easier not to cheat the system, but to find the wire and send the key through it ...
I hope that my thoughts on what biometrics are and what they eat with them will help you someday. Or in order to put yourself such a system, or in order to deceive someone else's)
