Configure software restriction group policies in Windows 7
After reading the article Windows-based computer without antiviruses , I got excited about this idea of security and decided to try to do it myself.
Since I have Windows 7 Professional, the first idea was to use AppLocker, but it quickly became clear that he did not want to work in my edition of Windows and required Ultimate or Enterprise. Due to the licensing of my Windows and the emptiness of my wallet, the option with AppLocker has disappeared.
The next attempt was to configure group policies for limited use of programs. Since AppLocker is a “pumped-up” version of this mechanism, it’s logical to try policies, especially since they are free for Windows users :)
Go to the settings:
gpedit.msc -> Computer Configuration -> Windows Configuration -> Security Settings -> Software Restricted Policies
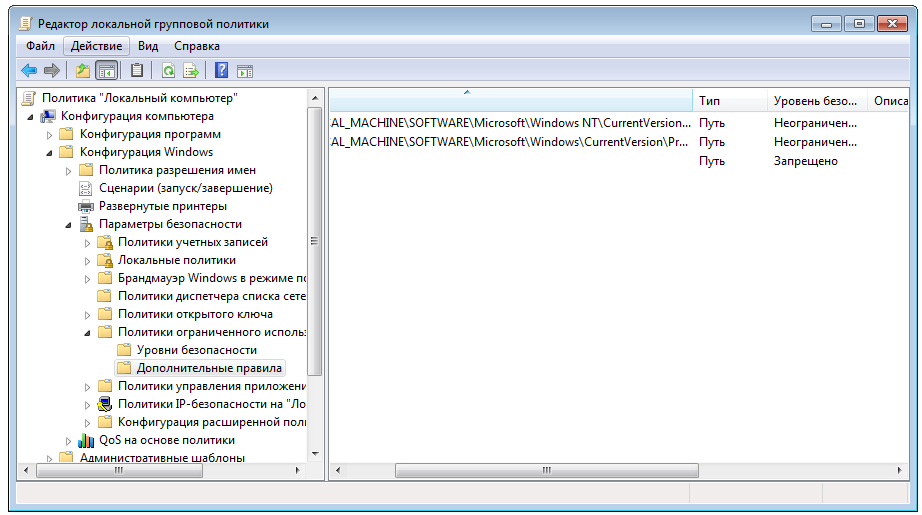
If there are no rules, the system will offer to generate automatic rules that allow programs to be launched from the Windows folder and Program Files. Also add a deny rule for the path * (any path). As a result, we want to be able to run programs only from protected system folders. And what?
Yes, this is what we will get, but that's just a little bad luck - shortcuts and http links do not work. Links can still be scored, but without shortcuts to live a little bad.
If you allow the launch of files by the * .lnk mask, we will get the opportunity to create a shortcut for any executable file, and to launch it using the shortcut, even if it is not in the system folder. Lousy.
A Google request leads to the following solutions: either allow the launch of shortcuts from the user folder, or use third-party bars with shortcuts. No other way. Personally, I do not like this option.
As a result, we are faced with the situation that * .lnk is, from the Windows point of view, not a link to an executable file, but an executable file. It’s crazy, but what can I do ... I would like Windows to check not the location of the shortcut, but the location of the file to which it refers.
And then I accidentally stumbled upon the settings of the list of extensions that are executable from the Windows point of view (gpedit.msc -> Computer Configuration -> Windows Configuration -> Security Settings -> Assigned File Types). We remove LNK from there and at the same time HTTP and log in. We get fully working shortcuts and checking the location of the executable file.
There was a doubt whether it would be possible to pass parameters through shortcuts - it is possible, so everything is ok.

As a result, we got an implementation of the idea described in the article “Windows-based computer without antiviruses” without any inconvenience for the user.
Also, for fans to shoot themselves in the foot, you can create a folder in Program Files and drop a shortcut for it on your desktop, calling it, for example, “Sandbox”. This will allow you to run programs from there without disabling policies using secure storage (protection via UAC).
I hope the method described turns out to be useful and new for someone. At least I haven’t heard of such a thing from anyone and haven’t seen it anywhere.
